Pass Your Amazon AWS Certified Solutions Architect - Professional Exam Easy!
Amazon AWS Certified Solutions Architect - Professional Exam Questions & Answers, Accurate & Verified By IT Experts
Instant Download, Free Fast Updates, 99.6% Pass Rate
Amazon AWS Certified Solutions Architect - Professional Practice Test Questions, Exam Dumps
Amazon AWS Certified Solutions Architect - Professional (AWS Certified Solutions Architect - Professional (SAP-C01)) exam dumps vce, practice test questions, study guide & video training course to study and pass quickly and easily. Amazon AWS Certified Solutions Architect - Professional AWS Certified Solutions Architect - Professional (SAP-C01) exam dumps & practice test questions and answers. You need avanset vce exam simulator in order to study the Amazon AWS Certified Solutions Architect - Professional certification exam dumps & Amazon AWS Certified Solutions Architect - Professional practice test questions in vce format.
Mastering the Amazon AWS Certified Solutions Architect - Professional Exam: Foundations and Strategic Value
Embarking on the path to achieve the AWS Certified Solutions Architect - Professional certification is a significant step in any cloud professional's career. This advanced credential is not merely a test of knowledge but a validation of your expertise in designing complex, fault-tolerant, and scalable solutions on the Amazon Web Services platform. It signifies a deep understanding of architectural principles and the ability to apply them to solve real-world business problems. This series is designed to guide you through the multifaceted preparation required for this challenging examination.
This first part will lay the groundwork for your studies. We will explore the strategic value this certification brings to your career, providing a compelling reason for the commitment required. We will deconstruct the exam blueprint, giving you a clear picture of the domains you need to master. Furthermore, we will define the ideal candidate profile, helping you assess your readiness. Most importantly, we will discuss the critical shift in mindset required to think like a professional-level architect and introduce the foundational AWS Well-Architected Framework, which underpins the entire exam.
The Strategic Importance of the AWS Certified Solutions Architect - Professional Certification
Achieving the AWS Certified Solutions Architect - Professional certification is a powerful career accelerator. It places you in an elite group of cloud professionals who have demonstrated their ability to design and deploy dynamically scalable, highly available, fault-tolerant, and reliable applications on AWS. This credential goes far beyond foundational knowledge, proving your capacity to evaluate cloud application requirements and make architectural recommendations for implementation, deployment, and provisioning. It is a clear signal to employers and clients that you possess the advanced technical skills and experience needed to handle complex projects.
This certification often translates into significant career opportunities and increased earning potential. Companies actively seek out professionals who can lead cloud initiatives and ensure that solutions are not only functional but also cost-effective, secure, and performant. Holding this certificate validates your ability to navigate the intricate trade-offs involved in high-level architectural decisions. It builds credibility and empowers you to lead technical discussions, guide implementation teams, and align technology solutions with overarching business goals, making you an invaluable asset to any organization leveraging the AWS cloud.
The distinction between the Associate and Professional levels is substantial. While the Associate certification confirms your ability to design and deploy using AWS services, the Professional certification challenges you to do so at scale, within complex organizational structures, and across multiple projects. It focuses on your ability to manage multi-account environments, implement sophisticated hybrid connectivity, and strategize large-scale data migrations. The exam scenarios are designed to mimic the intricate and often ambiguous challenges faced by senior architects, demanding a thought process that balances numerous competing requirements.
This advanced certification is about more than just knowing individual services; it is about orchestrating them into a cohesive, robust, and efficient architecture. It validates your ability to think strategically about long-term goals, continuous improvement, and modernization of existing workloads. By preparing for and passing this exam, you are not just learning facts; you are developing and refining the critical thinking skills that define a top-tier solutions architect in the competitive cloud computing landscape.
Deconstructing the SAP-C02 Exam Blueprint
To succeed in the AWS Certified Solutions Architect - Professional exam, you must have a thorough understanding of its structure and content domains. The official exam guide for the SAP-C02 version outlines four main domains, each with a specific weighting that indicates its importance on the test. These domains reflect the core responsibilities of a senior solutions architect and should be the focus of your study plan. Understanding this blueprint is the first step in structuring your preparation for maximum effectiveness.
The first domain, Design for Organizational Complexity, accounts for a significant portion of the exam. This area tests your ability to architect solutions for multi-account AWS environments, including strategies for governance, security, and networking across an enterprise. The second domain is Design for New Solutions, which focuses on your skills in gathering requirements and designing architectures for new products or services that are secure, reliable, scalable, and cost-effective. This involves selecting the appropriate AWS services and designing resilient and performant systems from the ground up.
The third domain, Continuous Improvement for Existing Solutions, assesses your ability to analyze and enhance current architectures. This includes identifying opportunities for performance optimization, cost reduction, improved security, and increased reliability. The final domain, Accelerate Workload Migration and Modernization, covers the intricate processes of moving existing on-premises or cloud workloads to AWS and modernizing them to leverage cloud-native features. This domain requires knowledge of migration tools, methodologies, and strategies for refactoring applications for the cloud.
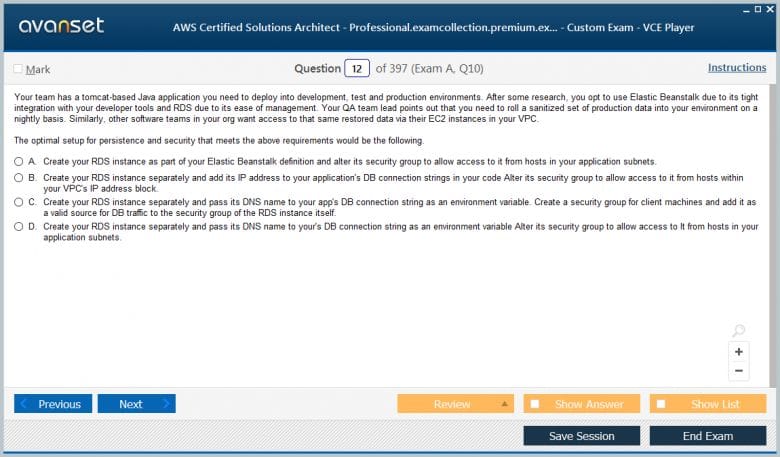
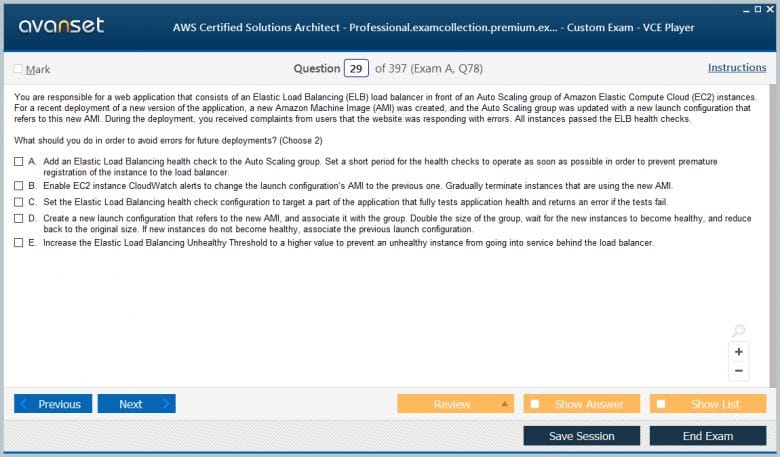
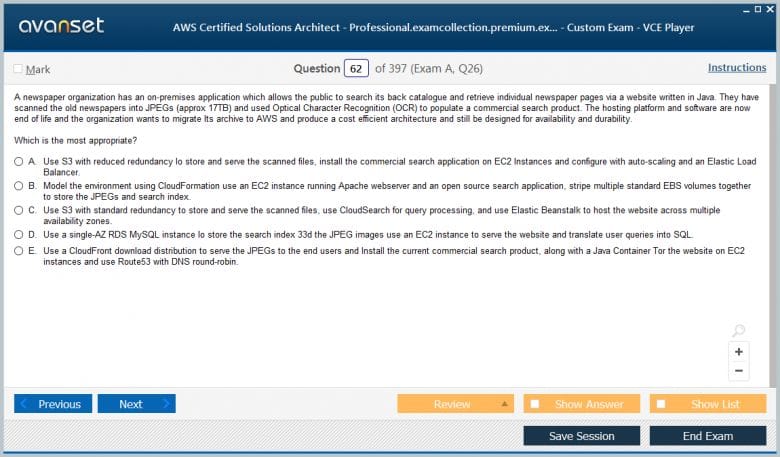
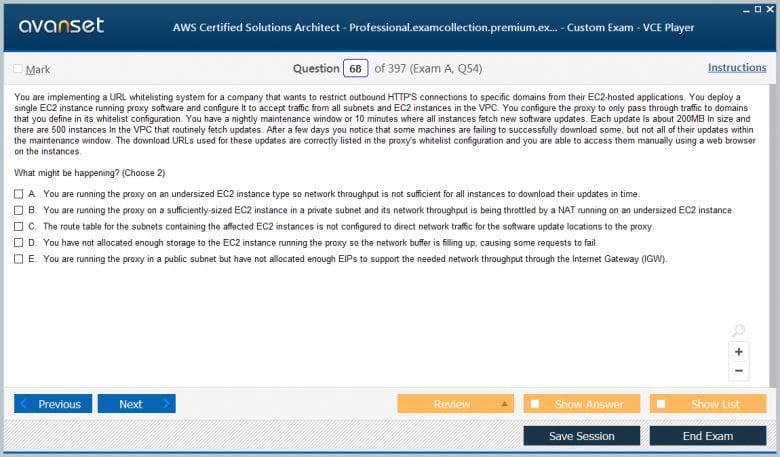
The exam itself consists of 75 multiple-choice and multiple-response questions, which you must complete within a 180-minute timeframe. The questions are famously long and scenario-based, often presenting you with a wall of text describing a complex business problem. Your task is to dissect the scenario, identify the key constraints and requirements, and select the best possible solution from the given options. Effective time management and the ability to quickly parse dense information are just as critical as your technical knowledge.
Who is the Ideal Candidate for This Certification?
The AWS Certified Solutions Architect - Professional certification is not intended for beginners in the cloud computing field. It is specifically designed for individuals who have substantial hands-on experience in architecting and deploying systems on AWS. The ideal candidate typically has two or more years of practical experience in a solutions architect role, where they have been responsible for designing complex, multi-service solutions that meet a wide range of business requirements. This experience is crucial because the exam scenarios are crafted to test practical application rather than rote memorization of service features.
A strong candidate should possess a deep familiarity with a broad range of AWS services, understanding not just what each service does but also its limitations, integration patterns, and optimal use cases. This knowledge must extend to core areas such as networking, security, storage, compute, databases, and application integration. Furthermore, proficiency with the AWS Command Line Interface (CLI), AWS APIs, and Infrastructure as Code tools like AWS CloudFormation is expected. A solid understanding of scripting in a language such as Python or Bash is also highly beneficial for automating and managing cloud environments.
The certification is particularly well-suited for experienced IT professionals, such as solutions architects, senior developers, and system administrators, who are looking to validate their expertise and advance their careers in cloud architecture. It is for those who are tasked with making high-level design decisions that impact an entire organization. This includes designing hybrid architectures that connect on-premises data centers with the AWS cloud, leveraging services like AWS Direct Connect or VPN solutions, and implementing robust continuous integration and continuous deployment (CI/CD) pipelines.
Ultimately, the successful candidate is someone who can bridge the gap between business objectives and technical implementation. They must be capable of translating business requirements into a technical vision and then architecting a solution that is secure, resilient, high-performing, and cost-efficient. If you have a proven track record of designing and implementing sophisticated AWS solutions and want to have your skills formally recognized at an expert level, then the AWS Certified Solutions Architect - Professional certification is the right goal for you.
The Architect's Mindset: Thinking Beyond Individual Services
Passing the AWS Certified Solutions Architect - Professional exam requires a fundamental shift in mindset compared to associate-level certifications. It is no longer sufficient to simply know the definition and primary function of an AWS service. Instead, you must think holistically, understanding how services integrate to form comprehensive solutions. The exam evaluates your ability to make design decisions based on a complex set of competing priorities, such as cost, performance, security, reliability, and operational excellence. This requires a deep appreciation for the trade-offs inherent in any architectural choice.
Consider a common scenario: choosing a database. An associate-level question might test your knowledge of the difference between Amazon RDS and Amazon DynamoDB. A professional-level question, however, will present a detailed business case with specific requirements for latency, consistency, scalability, and budget. You will need to weigh the benefits of a managed relational database against a NoSQL offering, and perhaps even consider options like Amazon Aurora for its specific features or self-hosting a database on Amazon EC2 for maximum control. The correct answer depends entirely on a nuanced understanding of the context provided.
This exam constantly forces you to think about the "why" behind a design choice, not just the "what." Why choose a Network Load Balancer over an Application Load Balancer for a specific TCP-based workload? Why use Amazon S3 Transfer Acceleration instead of AWS Direct Connect for a one-time large data transfer from a remote office? The best architects understand that there is rarely a single, perfect solution. Instead, there is an optimal solution for a given set of circumstances, and your job is to identify it by carefully balancing all the relevant factors.
This mindset extends to understanding the broader implications of your design. How will your architecture scale over time? How can it be monitored and managed effectively? What is the security posture, and how does it comply with industry regulations? The AWS Certified Solutions Architect - Professional exam is a test of your judgment as an architect. It challenges you to think critically, anticipate future needs, and build solutions that are not just technically sound but also strategically aligned with business goals. Cultivating this way of thinking is the most important aspect of your preparation.
Introduction to the AWS Well-Architected Framework
The AWS Well-Architected Framework is the conceptual foundation upon which the AWS Certified Solutions Architect - Professional exam is built. It is not a specific service but a set of best practices and guiding principles developed by AWS to help cloud architects build secure, high-performing, resilient, and efficient infrastructure for their applications. A deep and practical understanding of this framework is absolutely essential for success on the exam, as its principles are woven into the fabric of nearly every scenario-based question you will encounter.
The framework is organized into six distinct pillars. The first is Operational Excellence, which focuses on the ability to run and monitor systems to deliver business value and to continually improve supporting processes and procedures. The second pillar is Security, which involves protecting information, systems, and assets while delivering business value through risk assessments and mitigation strategies. This pillar covers topics like data protection, identity and access management, and infrastructure protection. The third pillar, Reliability, is centered on the ability of a workload to perform its intended function correctly and consistently.
The fourth pillar is Performance Efficiency, which focuses on using computing resources efficiently to meet system requirements and to maintain that efficiency as demand changes and technologies evolve. The fifth pillar, Cost Optimization, is about running systems to deliver business value at the lowest price point. It involves understanding and controlling where money is being spent, selecting the most appropriate and cost-effective resources, and scaling to meet business needs without overspending. The final and newest pillar is Sustainability, which focuses on minimizing the environmental impacts of running cloud workloads.
For the AWS Certified Solutions Architect - Professional exam, you must move beyond simply memorizing the names of the pillars. You need to internalize their principles and apply them to complex architectural design choices. When a question presents a scenario, you should instinctively evaluate the options through the lens of the Well-Architected Framework. Which option offers the best balance of reliability and cost? Which one provides the strongest security posture while still meeting performance goals? Thinking in this structured way will help you navigate the complexity of the exam questions and select the most appropriate answer.
Architecting for the Enterprise
Welcome to the second part of our series on preparing for the AWS Certified Solutions Architect - Professional exam. In Part 1, we established the foundational concepts, the exam structure, and the mindset required for success. Now, we transition from the "why" to the "how," beginning a deep dive into the technical domains. This part focuses exclusively on the first and most heavily weighted domain of the exam: Design for Organizational Complexity. This is where the "Professional" distinction truly comes to life, moving beyond single-account architectures into the realm of enterprise-scale cloud management.
Organizations rarely operate within a single AWS account. As they grow, they adopt a multi-account strategy to isolate workloads, manage billing, and enforce security boundaries. This introduces significant complexity in governance, networking, and identity management. The AWS Certified Solutions Architect - Professional exam will extensively test your ability to design solutions that address these challenges effectively. We will explore the core services and strategies you must master, including AWS Organizations, advanced identity and access management patterns, and sophisticated multi-account networking architectures.
Mastering AWS Organizations and Account Strategy
At the heart of managing enterprise-scale AWS environments is AWS Organizations. This service is fundamental to the Design for Organizational Complexity domain, and you must understand it intimately. AWS Organizations allows you to centrally manage and govern your environment as you grow and scale your workloads on AWS. It provides policy-based management for multiple AWS accounts, enabling you to create groups of accounts, called Organizational Units (OUs), and attach policies to them for governance. This hierarchical structure is a powerful tool for applying controls consistently across your enterprise.
A critical feature you must master is Service Control Policies (SCPs). SCPs are a type of policy that you can use to manage permissions in your organization. They offer central control over the maximum available permissions for all accounts in your organization, allowing you to ensure your accounts stay within your organization’s access control guidelines. It is crucial to remember that SCPs do not grant permissions. Instead, they specify the maximum permissions for an OU or an individual account. Permissions must still be granted to users and roles using standard IAM policies.
The exam will present scenarios where you need to design an effective OU structure. A common best practice is to structure OUs based on function, compliance requirements, or environment lifecycle (e.g., Development, Testing, Production). For instance, you might have a "Security" OU containing accounts for logging and security tooling, a "Workloads" OU with sub-OUs for different business units, and a "Sandbox" OU for experimentation. Your ability to reason about the trade-offs of different OU structures to meet specific governance and operational needs will be tested.
Furthermore, you need to understand how AWS Organizations integrates with other AWS services to provide a complete governance framework. This includes enabling services like AWS GuardDuty, AWS Config, or AWS Security Hub across all accounts from a central management account. The exam will expect you to know how to use features like delegated administrator to allow specific member accounts to manage these services on behalf of the organization. A deep understanding of these integration patterns is key to designing a robust and scalable landing zone for any large enterprise.
Advanced Identity and Access Management (IAM)
While IAM is a foundational AWS service, the AWS Certified Solutions Architect - Professional exam tests your knowledge of its advanced features and patterns within a complex, multi-account context. You must move beyond simple user and policy creation and understand how to establish a scalable and secure identity federation strategy for an enterprise. This often involves integrating an existing corporate identity provider (IdP), such as Active Directory or an Okta, with AWS.
You need to be an expert in IAM Roles and the Security Token Service (STS). The concept of assuming a role is central to cross-account access and identity federation. You should understand the mechanics of the AssumeRole API call and the difference between identity-based policies and resource-based policies. For instance, a common pattern tested is using an IAM role in a central "identity" account that users from a corporate directory can assume. From there, they can assume other roles in various "resource" accounts to access specific applications or services, a technique known as role chaining.
The exam will present scenarios that require you to design a permissions model that adheres to the principle of least privilege at scale. This involves a deep understanding of policy evaluation logic, including explicit denies, permission boundaries, and conditions. Permission boundaries are a particularly important advanced feature. They allow you to set the maximum permissions that an identity-based policy can grant to an IAM entity. This is a powerful tool for delegating permissions management to developers while maintaining central control over security boundaries.
Another key area is understanding how to grant cross-account access to resources securely. You need to know when to use resource-based policies (e.g., on an S3 bucket or an KMS key) versus when to use IAM roles. A common scenario involves a central logging account that needs to collect logs from dozens of other application accounts. You should be able to design a solution using a resource-based policy on the destination S3 bucket, allowing other accounts to write to it without needing complex cross-account roles.
Designing a Scalable and Secure Multi-Account Network
Networking in a multi-account environment is one of the most challenging and frequently tested topics on the AWS Certified Solutions Architect - Professional exam. As an organization scales, connecting the Virtual Private Clouds (VPCs) across dozens or hundreds of accounts becomes a significant architectural challenge. You must understand the various options for inter-VPC connectivity and their respective trade-offs in terms of scalability, cost, and management overhead.
The traditional approach of VPC Peering does not scale well. While effective for connecting a small number of VPCs, it creates a complex mesh of connections that becomes difficult to manage as the number of VPCs grows. You must understand its limitations, such as the lack of transitive routing. If VPC A is peered with VPC B, and VPC B is peered with VPC C, VPC A cannot communicate with VPC C through VPC B. This is a critical point that often appears in exam questions.
To address the scalability limitations of VPC Peering, AWS introduced AWS Transit Gateway. This service acts as a cloud router and a regional hub for connecting your VPCs and on-premises networks. You must have a deep understanding of how Transit Gateway works, including its route tables, attachments, and policy-based routing capabilities. A common enterprise pattern is to deploy a central Transit Gateway in a dedicated "Network" account. This hub-and-spoke model simplifies connectivity, as each new VPC only needs to connect to the central hub rather than peering with every other VPC.
Beyond inter-VPC connectivity, you must master hybrid connectivity solutions. This means having expert-level knowledge of AWS Direct Connect and AWS Site-to-Site VPN. You should be able to design highly available connections using multiple Direct Connect connections, Link Aggregation Groups (LAGs), and Bidirectional Forwarding Detection (BFD). You will also be tested on complex routing scenarios involving Border Gateway Protocol (BGP), route propagation, and how to control traffic paths between your on-premises data centers and your multi-account AWS environment through the Transit Gateway.
Centralized Governance and Security Services
A core tenet of designing for organizational complexity is centralizing key governance and security functions. The AWS Certified Solutions Architect - Professional exam expects you to design architectures where security monitoring, logging, and compliance are managed from a set of dedicated accounts, providing a single pane of glass for the entire organization. This approach enhances security posture and simplifies operations by consolidating critical data and tooling.
You should be proficient in designing a centralized logging solution. A typical pattern involves creating a dedicated "Log Archive" account with a central Amazon S3 bucket. This bucket is configured with a resource-based policy that allows other accounts in the organization to ship their logs to it. You would then use services like AWS CloudTrail, AWS Config, and VPC Flow Logs in each member account and configure them to deliver their logs to this central bucket. This ensures that all audit and log data is securely stored and immutable.
Similarly, you must understand how to centralize security monitoring. AWS Security Hub is a key service here. It provides a comprehensive view of your security alerts and security posture across your AWS accounts. The exam will test your ability to implement Security Hub in a multi-account environment, using AWS Organizations to automatically enable it on member accounts and aggregate all findings into a single, delegated administrator account. This allows a central security team to monitor for threats and misconfigurations across the entire enterprise from one place.
Other critical services in this domain include AWS Control Tower, AWS Config, and Amazon GuardDuty. AWS Control Tower automates the setup of a secure, multi-account AWS environment, or landing zone, based on AWS best practices. AWS Config is used for assessing, auditing, and evaluating the configurations of your AWS resources, and it can be used to enforce compliance rules across the organization. Amazon GuardDuty is an intelligent threat detection service that continuously monitors for malicious activity and unauthorized behavior. You must be able to architect solutions that integrate these services seamlessly across a multi-account structure.
Implementing a Multi-Region Strategy
For global organizations, designing for complexity often extends beyond a single AWS region. The AWS Certified Solutions Architect - Professional exam will test your ability to architect solutions that are resilient, performant, and compliant across multiple geographic locations. This requires a deep understanding of data residency requirements, disaster recovery strategies, and the services that facilitate multi-region deployments. Your designs must account for factors like latency for global users and the need for business continuity in the event of a regional outage.
A key challenge in multi-region architectures is data replication. You need to be familiar with the native replication capabilities of various AWS services. For example, Amazon S3 Cross-Region Replication (CRR) can be used to automatically copy objects to a bucket in another region for disaster recovery or to reduce latency for users in different geographic locations. For databases, you should understand services like Amazon Aurora Global Database, which allows a single database to span multiple AWS regions with low-latency reads and fast disaster recovery failover.
Networking across regions also introduces complexity. While a Transit Gateway is a regional service, you can peer Transit Gateways in different regions to enable inter-region VPC communication. You should understand how to set up this peering and how data transfer costs are affected. For delivering content to a global user base with low latency, you must be an expert in Amazon CloudFront. The exam will present scenarios where you need to design a complex CloudFront distribution with multiple origins, custom behaviors, and security features like AWS WAF.
Disaster recovery (DR) is a major focus of multi-region architecture questions. You need to be intimately familiar with different DR strategies, such as Backup and Restore, Pilot Light, Warm Standby, and Multi-Site Active-Active. The exam will provide a scenario with specific Recovery Time Objective (RTO) and Recovery Point Objective (RPO) requirements, and you will have to select the most cost-effective architecture that meets those goals. This could involve using AWS Elastic Disaster Recovery (DRS) or crafting a custom solution using services like Route 53 for DNS failover and CloudFormation for infrastructure provisioning.
Architecting the Future State
Welcome to the third installment of our comprehensive guide to the AWS Certified Solutions Architect - Professional certification. In the previous part, we focused on building a robust and scalable enterprise foundation using a multi-account strategy. Now, we turn our attention to the dynamic processes of building new solutions and transforming existing ones. This part covers two closely related exam domains: Design for New Solutions and Accelerate Workload Migration and Modernization. These areas test your ability to act as a forward-thinking architect who can both create cloud-native applications and strategically move legacy systems to the cloud.
The AWS Certified Solutions Architect - Professional exam heavily emphasizes your ability to translate ambiguous business requirements into concrete, well-architected technical designs. It also requires you to be a master of migration strategy, understanding that moving to the cloud is not just a "lift and shift" operation but an opportunity for modernization and optimization. In this section, we will explore the methodologies for planning migrations, the various strategies for transforming workloads, and the key AWS services that facilitate this journey from legacy infrastructure to a cloud-native future.
Understanding the Migration Process
A successful cloud migration is a well-planned journey, not a single event. The AWS Certified Solutions Architect - Professional exam expects you to be familiar with the established phases of a large-scale migration, often referred to as the Migration Acceleration Program (MAP) phases: Assess, Mobilize, and Migrate & Modernize. Understanding the activities and goals of each phase is crucial for answering scenario-based questions that ask you to recommend the next step or identify a missing component in a migration plan.
The Assess phase is the starting point. Here, the goal is to build a strong business case for migration. This involves discovering the existing inventory of servers and applications, understanding their dependencies, and performing a Total Cost of Ownership (TCO) analysis to compare the cost of running on-premises versus on AWS. AWS provides tools like the AWS Application Discovery Service and AWS Migration Hub to aid in this process. You should know the purpose of these tools and how they contribute to building a data-driven migration strategy.
The Mobilize phase is about preparing the organization and the environment for migration. This involves addressing the gaps identified in the assess phase. Key activities include creating a landing zone, which is the secure, multi-account AWS environment we discussed in Part 2. It also involves training teams, refining the migration plan, and performing pilot migrations with a small number of non-critical applications. This phase is critical for building momentum and ensuring that the foundational elements are in place before the full-scale migration begins.
Finally, the Migrate & Modernize phase is where the execution happens. This is an iterative process where applications are moved to the cloud in waves. It is not just about moving virtual machines; it is also about modernizing them to take advantage of cloud-native capabilities. This phase relies on a deep understanding of various migration strategies and the specific AWS services that support them. Your ability to choose the right strategy for a given application based on its characteristics and the business goals will be heavily tested.
The 7 R's: Migration Strategies
At the core of any migration plan is the selection of the right strategy for each application in the portfolio. The AWS Certified Solutions Architect - Professional exam requires you to be an expert on the seven common migration strategies, often called the "7 R's." These are Rehost, Replatform, Refactor/Re-architect, Repurchase, Retain, Retire, and the newer addition, Relocate. You will be presented with scenarios describing an application and its business context and asked to choose the most appropriate migration path.
Rehost, also known as "lift and shift," is the process of moving an application to the cloud with minimal changes. This is often done using tools like AWS Application Migration Service (MGN) to replicate servers from an on-premises environment to Amazon EC2 instances. This strategy offers a fast migration path but may not fully leverage cloud benefits. Replatform, or "lift and reshape," involves making some optimizations to the application to take advantage of the cloud, such as moving from a self-managed database to a managed service like Amazon RDS.
Refactor or Re-architect is the most transformative strategy. It involves fundamentally changing the application's architecture to be cloud-native, often moving from a monolithic design to a microservices architecture using services like AWS Lambda, Amazon ECS, or Amazon EKS. While this approach yields the greatest benefits in terms of scalability and agility, it also requires the most effort. Repurchase involves moving to a different product, typically a SaaS solution, such as migrating from a self-hosted CRM to Salesforce.
The remaining strategies are simpler. Relocate involves moving workloads, specifically a VMware environment, to the cloud using VMware Cloud on AWS, with minimal disruption. Retain means keeping certain applications on-premises, usually because they are not ready for migration or are subject to specific residency requirements. Finally, Retire is the process of decommissioning applications that are no longer needed in the portfolio. A successful enterprise migration involves a mix of all these strategies, and your role as an architect is to recommend the right one for each workload.
Database and Data Migration Strategies
Migrating databases and large volumes of data presents a unique set of challenges that are a major focus of the AWS Certified Solutions Architect - Professional exam. You must be proficient in the tools and techniques for moving data from on-premises data centers to AWS securely and efficiently. This includes both online migrations, where the source database remains operational during the transfer, and offline migrations for very large datasets where downtime is acceptable.
For heterogeneous database migrations, such as moving from an Oracle or SQL Server database to a cloud-native option like Amazon Aurora, the AWS Schema Conversion Tool (SCT) and AWS Database Migration Service (DMS) are essential. SCT is used to analyze and convert the source database schema to a format compatible with the target database. DMS is the workhorse that handles the actual data replication. You must understand how to configure a DMS task for both a one-time full load and ongoing replication using Change Data Capture (CDC) to minimize downtime.
For large-scale offline data transfers, you need to understand the AWS Snow Family of services. This includes AWS Snowcone, AWS Snowball Edge, and AWS Snowmobile. You will be tested on your ability to choose the correct Snow device based on the amount of data to be transferred and the required compute capabilities at the edge. The exam will often present scenarios where network bandwidth is limited, making an online transfer impractical, and you must calculate the most efficient way to use the Snow Family to move petabytes of data into Amazon S3.
You also need to be familiar with options for migrating file shares and other unstructured data. AWS DataSync is a key service for this purpose. It is an online data transfer service that simplifies, automates, and accelerates moving data between on-premises storage systems and AWS Storage services like Amazon S3 or Amazon EFS. You should understand its features, such as built-in encryption and data integrity validation, and when to use it over other methods like the AWS Transfer Family for SFTP-based transfers.
Modernizing Applications for the Cloud
The ultimate goal of many migrations is not just to move to the cloud but to modernize applications to become more agile, scalable, and resilient. The AWS Certified Solutions Architect - Professional exam will test your ability to design modern, cloud-native architectures. This often involves decomposing monolithic applications into smaller, independent microservices. A deep understanding of containerization and serverless computing is therefore mandatory.
Containerization using Docker has become a standard for modern application deployment. You must be an expert in the AWS container orchestration services: Amazon Elastic Container Service (ECS) and Amazon Elastic Kubernetes Service (EKS). The exam will not ask you to write Kubernetes manifests, but it will present complex scenarios where you need to choose between ECS and EKS based on a company's existing skillset, need for control, and operational preferences. You should also be proficient in AWS Fargate, the serverless compute engine for containers that removes the need to manage the underlying EC2 instances.
Serverless computing with AWS Lambda is another cornerstone of application modernization. You should be able to design event-driven architectures where Lambda functions are triggered by events from various sources, such as API calls via Amazon API Gateway, file uploads to Amazon S3, or messages in an Amazon SQS queue. Understanding how to manage Lambda function concurrency, memory allocation, and integration with other services is critical. The exam will test your ability to build highly scalable and cost-effective solutions by leveraging the serverless paradigm.
Decoupling is a key principle in modern architecture design. You must be an expert in using services like Amazon Simple Queue Service (SQS) for asynchronous messaging between microservices and Amazon Simple Notification Service (SNS) for publish/subscribe patterns. This decoupling improves the fault tolerance and scalability of the application, as a failure in one component does not cascade and bring down the entire system. Your ability to identify opportunities to introduce queues and topics to break down dependencies in a legacy application is a key skill for a professional architect.
Designing for New Solutions
While migration and modernization are about transforming the old, the AWS Certified Solutions Architect - Professional exam also tests your ability to create the new. The Design for New Solutions domain focuses on your ability to take a set of business and technical requirements and architect a greenfield application on AWS from scratch. This requires a broad and deep knowledge of the AWS service portfolio and the ability to select the right tool for the job.
A typical scenario will provide you with requirements related to performance, durability, cost, and security. You will then need to design a multi-tiered architecture. For the web and application tiers, you might consider auto-scaling groups of EC2 instances, containers managed by ECS or EKS, or a serverless approach with AWS Lambda and API Gateway. You must be able to justify your choice based on the specific needs outlined in the scenario, such as the expected traffic patterns or the development team's expertise.
For the data tier, you will need to choose the appropriate database or storage solution. This is a critical decision point. Is the data structured, requiring a relational database like Amazon RDS or Aurora? Or is it unstructured, better suited for a NoSQL database like Amazon DynamoDB? Perhaps the solution requires a data warehouse like Amazon Redshift or a search service like Amazon OpenSearch Service. The exam will test your ability to analyze the data access patterns and consistency requirements to make the optimal choice.
Finally, your design must be secure and well-architected from the start. This means incorporating security at every layer, from network controls using VPC security groups and NACLs to data protection using encryption with AWS Key Management Service (KMS). You should also design for high availability and disaster recovery, for example, by deploying across multiple Availability Zones or even multiple regions. Your solution should reflect the principles of the AWS Well-Architected Framework, demonstrating a holistic approach to building robust and reliable systems.
Architecting for Value and Efficiency
Welcome to the fourth part of our in-depth series preparing you for the AWS Certified Solutions Architect - Professional exam. Having covered enterprise foundations, migration, and modernization, we now focus on two pillars of the AWS Well-Architected Framework that are critical for success at the professional level: Performance Efficiency and Cost Optimization. These domains are intrinsically linked; a well-performing architecture is often an efficient one, and an efficient architecture is typically cost-effective. The exam will challenge you to design solutions that meet stringent performance requirements while adhering to strict budgetary constraints.
The AWS Certified Solutions Architect - Professional is expected to be more than just a technical designer; they must also be a financial steward of their organization's cloud resources. This means making architectural choices that deliver business value at the lowest possible price point without sacrificing performance or reliability. This part will delve into the strategies, services, and design patterns you need to master to build highly performant and cost-optimized solutions on AWS. We will cover everything from selecting the right compute resources to implementing sophisticated caching and data management strategies.
Strategies for Cost Optimization
Cost optimization on AWS is a continuous process, not a one-time task. The AWS Certified Solutions Architect - Professional exam requires you to understand the strategic, ongoing practices that enable an organization to control and reduce its cloud spend. This goes beyond simply choosing the cheapest option and involves a deep understanding of pricing models, monitoring tools, and architectural patterns that promote financial efficiency. You must be able to analyze an existing architecture, identify areas of waste, and recommend specific changes to lower costs.
A foundational aspect of cost optimization is right-sizing. This is the process of matching instance types and sizes to your workload’s performance and capacity requirements at the lowest possible cost. The exam will present scenarios with underutilized or over-provisioned resources, and you will need to recommend a more appropriate instance type from the vast EC2 family. You should be familiar with tools like AWS Compute Optimizer and the Trusted Advisor, which provide recommendations for right-sizing based on historical utilization metrics from Amazon CloudWatch.
Understanding AWS purchasing options is absolutely mandatory. You must be an expert on the differences between On-Demand Instances, Savings Plans, and Reserved Instances (RIs). You should know when to recommend a Compute Savings Plan for maximum flexibility versus a Standard RI for maximum savings on a specific, stable workload. The exam will test your ability to analyze usage patterns and recommend the optimal purchasing strategy to maximize discounts for an organization's predictable, long-term compute needs.
Furthermore, you need to design architectures that are inherently cost-aware. This often means leveraging serverless technologies like AWS Lambda and AWS Fargate, where you pay only for the compute time you consume, eliminating the cost of idle resources. It also involves implementing data lifecycle management, for example, by using Amazon S3 Lifecycle policies to automatically move infrequently accessed data from the S3 Standard storage class to more cost-effective tiers like S3 Infrequent Access or S3 Glacier.
Mastering Performance Efficiency
Performance efficiency is about using computing resources effectively to meet system requirements and maintaining that efficiency as demand changes and technology evolves. The AWS Certified Solutions Architect - Professional exam will test your ability to select and configure services to achieve the best possible performance for a given workload. This involves making informed decisions about compute, storage, databases, and networking to minimize latency and maximize throughput.
When it comes to compute, your choice of Amazon EC2 instance type has a massive impact on performance. You should be familiar with the different instance families (e.g., General Purpose, Compute Optimized, Memory Optimized, Storage Optimized) and their ideal use cases. For high-performance computing (HPC) workloads, you need to understand advanced features like Elastic Fabric Adapter (EFA) for low-latency, high-bandwidth inter-instance communication, and how to deploy instances in a placement group to control their physical locality.
Storage performance is another critical area. You must have a deep understanding of the different Amazon EBS volume types, such as gp3, io2 Block Express, and st1, and their respective performance characteristics (IOPS and throughput). The exam will present scenarios with I/O-intensive applications, and you will need to select the EBS volume type and configuration that meets the required performance goals without over-provisioning and incurring unnecessary costs. For file storage, you should know the different performance modes of Amazon EFS and when to use them.
Database performance is a frequent topic of complex scenario questions. You should be able to design solutions to address database bottlenecks. This might involve implementing a read replica strategy for Amazon RDS to offload read traffic from the primary instance, or using Amazon DynamoDB Accelerator (DAX) to provide a fully managed, in-memory cache for DynamoDB that can reduce response times from milliseconds to microseconds. Understanding these performance-enhancing patterns is key to designing scalable and responsive applications.
Conclusion
Our five-part journey through the world of the AWS Certified Solutions Architect - Professional exam is now complete. We have covered the strategic foundations, the complexities of enterprise-scale architecture, the nuances of migration and modernization, the critical balance of performance and cost, and finally, the pillars of security and reliability. This comprehensive path has aimed to equip you not just with the knowledge to pass an exam, but with the mindset and skills of a true professional architect.
The path to this certification is a marathon that demands dedication and a deep passion for technology. It pushes you to think beyond individual services and to see the bigger picture of how to build systems that are robust, secure, scalable, and aligned with business goals. By mastering these concepts, you are not just preparing for a test; you are preparing to be a leader in the field of cloud architecture. We wish you the very best of luck on your certification exam and in your continued journey as a cloud professional.
Go to testing centre with ease on our mind when you use Amazon AWS Certified Solutions Architect - Professional vce exam dumps, practice test questions and answers. Amazon AWS Certified Solutions Architect - Professional AWS Certified Solutions Architect - Professional (SAP-C01) certification practice test questions and answers, study guide, exam dumps and video training course in vce format to help you study with ease. Prepare with confidence and study using Amazon AWS Certified Solutions Architect - Professional exam dumps & practice test questions and answers vce from ExamCollection.
Amazon AWS Certified Solutions Architect - Professional Video Course
Top Amazon Certification Exams
- AWS Certified Generative AI Developer - Professional AIP-C01
- AWS Certified Solutions Architect - Associate SAA-C03
- AWS Certified Solutions Architect - Professional SAP-C02
- AWS Certified AI Practitioner AIF-C01
- AWS Certified Cloud Practitioner CLF-C02
- AWS Certified Machine Learning Engineer - Associate MLA-C01
- AWS Certified Security - Specialty SCS-C03
- AWS Certified DevOps Engineer - Professional DOP-C02
- AWS Certified Data Engineer - Associate DEA-C01
- AWS Certified Advanced Networking - Specialty ANS-C01
- AWS Certified CloudOps Engineer - Associate SOA-C03
- AWS Certified Developer - Associate DVA-C02
- AWS Certified Machine Learning - Specialty
- AWS Certified Security - Specialty SCS-C02
- AWS Certified SysOps Administrator - Associate
Site Search:




















Is the premimum dump still valid ? (1st March 2022)
@Kevo, congrats. You only used the premium file to study for the exam? Does anyone know if Amazon offers the opportunity to take a proctor exam rather than at a centre because of the pandemic of COVID-19?
Passed today premium dump 100% valid all questions came from premium dump
Did anyone passes with this exam dump
Any recent success story with the premium file please?
Hi, anyone got this exam recently?
Hey, is this dump valid? Has anyone got this exam?
NO one has any feedback?
Is this valid for the 2019 refresh?
Is the dump uploaded on Dec 25 still valid?
Is the premium file ok?