Pass Your Isaca CISM Certification Easy!
Isaca CISM Certification Exams Questions & Answers, Accurate & Verified By IT Experts
Instant Download, Free Fast Updates, 99.6% Pass Rate.

$69.99
Download Free CISM Practice Test Questions VCE Files
| Exam | Title | Files |
|---|---|---|
Exam CISM |
Title Certified Information Security Manager |
Files 28 |
Isaca CISM Certification Exam Dumps & Practice Test Questions
Prepare with top-notch Isaca CISM certification practice test questions and answers, vce exam dumps, study guide, video training course from ExamCollection. All Isaca CISM certification exam dumps & practice test questions and answers are uploaded by users who have passed the exam themselves and formatted them into vce file format.
Understanding ISACA CISM Certification: A Complete Guide to Information Security Leadership
In today’s rapidly evolving digital world, information security is no longer a support function but a strategic necessity. Organizations across industries face complex cybersecurity threats, regulatory pressures, and an ever-growing need to protect sensitive information. In this context, the Certified Information Security Manager (CISM) certification offered by ISACA has emerged as a key credential for professionals who aim to bridge the gap between technical security operations and business management.
The CISM certification is designed to equip professionals with the knowledge and skills required to manage, oversee, and develop enterprise information security programs. Unlike technical certifications that focus primarily on hands-on skills, CISM emphasizes governance, risk management, and program management—key areas that enable professionals to align security strategies with organizational objectives.
The Purpose of CISM Certification
The primary goal of the CISM certification is to validate expertise in information security management. It demonstrates a professional’s ability to design and manage enterprise-wide security programs that support business goals while mitigating risks. Organizations value CISM-certified professionals for their ability to make strategic decisions, assess threats, and manage security initiatives efficiently.
One distinguishing factor of CISM is its focus on managerial responsibilities. While technical knowledge is essential, the certification emphasizes decision-making, strategic planning, and leadership in information security. This makes it particularly suitable for professionals looking to move from technical roles into management or executive positions in cybersecurity.
Key Domains of CISM
The CISM certification is structured around four core domains, each representing an essential aspect of information security management:
Information Security Governance
Governance is the foundation of any effective information security program. This domain focuses on creating and maintaining a security framework that aligns with business objectives, compliance requirements, and stakeholder expectations. Professionals are trained to develop policies, standards, and procedures that guide the organization’s security posture.
This domain emphasizes leadership, communication, and strategic alignment. Security leaders must communicate risks and strategies effectively to executives and boards of directors. The ability to link security initiatives to business objectives ensures that the organization invests in programs that provide measurable value.
Information Risk Management
Risk management is a critical function in ensuring that security programs protect organizational assets while supporting business operations. This domain teaches professionals how to identify, assess, and prioritize risks to information assets. Candidates learn to implement mitigation strategies, monitor risk environments, and maintain a balance between security measures and business objectives.
Risk management also involves understanding threats from both internal and external sources. Professionals must evaluate vulnerabilities, assess the potential impact of incidents, and ensure that security controls are cost-effective and aligned with the organization’s risk tolerance.
Information Security Program Development and Management
Designing and managing security programs is another essential responsibility of a CISM-certified professional. This domain focuses on the lifecycle of security initiatives, from planning and implementation to monitoring and continuous improvement. Candidates are taught to develop programs that address organizational needs, comply with regulatory requirements, and ensure effective resource allocation.
Program development requires an understanding of organizational culture, business processes, and technology infrastructure. Security managers must coordinate teams, define roles and responsibilities, and ensure that programs remain adaptable to emerging threats and evolving business requirements.
Information Security Incident Management
No organization is immune to security incidents, making incident management a vital domain for CISM professionals. This area covers the development and execution of processes for detecting, responding to, and recovering from security breaches. It emphasizes preparation, response planning, and post-incident analysis to minimize damage and enhance organizational resilience.
Effective incident management requires collaboration across multiple departments, including IT, legal, communications, and executive leadership. Professionals must develop and test response plans, conduct root cause analyses, and implement lessons learned to prevent future incidents.
Who Should Pursue CISM Certification
CISM is best suited for professionals who are moving into managerial and leadership roles in information security. Candidates often include:
IT managers responsible for security programs
Security consultants providing strategic guidance
Risk and compliance officers
Security auditors overseeing governance processes
Professionals aspiring to executive roles such as Chief Information Security Officer (CISO)
While technical knowledge remains important, the certification is designed for individuals who are expected to make strategic decisions, influence organizational policies, and communicate effectively with stakeholders.
Requirements for Certification
To earn CISM certification, candidates must meet several prerequisites. The most significant requirement is professional experience. Candidates must have at least five years of work experience in information security, with a minimum of three years in information security management. Some experience waivers may apply based on education, certifications, or other qualifications.
In addition to experience, candidates must pass the CISM examination, which tests knowledge across the four domains. The exam is scenario-based, requiring an understanding of real-world applications rather than rote memorization. This ensures that certified professionals can apply their skills effectively in practical settings.
Candidates must also adhere to ISACA’s Code of Professional Ethics. This commitment ensures that certified professionals act with integrity, objectivity, and responsibility in all aspects of their work. Finally, maintaining certification requires ongoing professional development through continuing education, keeping skills relevant in a rapidly changing cybersecurity landscape.
Benefits of CISM Certification
Earning CISM certification provides numerous advantages for both professionals and organizations.
Career Advancement
CISM-certified professionals often qualify for higher-level positions, including managerial and executive roles in cybersecurity. The certification demonstrates leadership ability, strategic thinking, and expertise in governance, making candidates attractive to employers seeking to strengthen their security programs.
Credibility and Recognition
CISM is recognized globally as a leading credential for information security management. Certified professionals gain credibility among peers, executives, and clients. The certification signals that the individual possesses not only technical knowledge but also the ability to manage complex security initiatives and align them with business goals.
Enhanced Skills and Knowledge
The certification process equips professionals with comprehensive knowledge of governance, risk management, program development, and incident management. This combination of skills ensures that certified individuals can make informed decisions, prioritize resources effectively, and anticipate potential security challenges.
Global Opportunities
Given its international recognition, CISM certification opens doors to career opportunities around the world. Professionals may work in multinational corporations, consulting firms, or government agencies, taking on leadership roles that influence organizational security strategies at a global level.
Preparing for the CISM Exam
Effective preparation is essential for success in the CISM examination. Candidates should focus on understanding core concepts, applying knowledge to real-world scenarios, and developing a strategic mindset. Recommended preparation strategies include:
Studying official CISM guides and reference materials
Participating in structured training programs or workshops
Practicing with scenario-based questions to enhance problem-solving skills
Gaining hands-on experience in security management and governance
Successful candidates combine theoretical understanding with practical experience, ensuring that they can navigate complex organizational challenges and contribute meaningfully to information security programs.
CISM and Career Pathways
The CISM certification serves as a stepping stone to various career paths in information security management. Common roles for certified professionals include:
Chief Information Security Officer (CISO)
Information Security Manager
IT Risk and Compliance Manager
Security Consultant
Governance, Risk, and Compliance (GRC) Analyst
Each of these roles requires a blend of technical knowledge, strategic thinking, and leadership ability—qualities that CISM-certified professionals develop through the certification process.
The Strategic Advantage of CISM
One of the most significant benefits of CISM is its emphasis on aligning security with business objectives. Organizations increasingly recognize that effective security programs contribute to business success by protecting assets, ensuring regulatory compliance, and enabling innovation. CISM-certified professionals are uniquely positioned to bridge the gap between technical teams and executive leadership, making strategic decisions that balance security needs with organizational priorities.
The certification also equips professionals to anticipate and respond to emerging threats. By understanding risk management principles and governance frameworks, certified individuals can proactively address vulnerabilities, implement effective controls, and foster a culture of security awareness throughout the organization.
Continuing Professional Development
CISM certification is not a one-time achievement but an ongoing commitment to professional growth. Maintaining certification requires earning continuing professional education (CPE) hours annually. This ensures that professionals stay current with evolving technologies, regulatory changes, and emerging threats. Continuing education may include training programs, conferences, webinars, and industry research.
By actively engaging in professional development, CISM-certified individuals remain competitive in the job market and continue to provide value to their organizations. It also reinforces their role as leaders who guide security strategy, mentor teams, and drive continuous improvement in information security management.
The ISACA CISM certification is a prestigious and valuable credential for professionals aspiring to leadership roles in information security. By focusing on governance, risk management, program development, and incident management, CISM prepares individuals to manage enterprise security programs effectively. The certification enhances career opportunities, builds credibility, and equips professionals with the strategic skills necessary to navigate complex organizational challenges.
As organizations face increasingly sophisticated cyber threats, the demand for skilled security managers will continue to grow. CISM-certified professionals are uniquely positioned to meet this demand, providing leadership, strategic insight, and a comprehensive understanding of information security management. Earning CISM is not just an investment in certification—it is an investment in a long-term career in cybersecurity leadership.
Preparing for the CISM Certification Exam: Strategies and Insights
Successfully earning the Certified Information Security Manager (CISM) certification requires more than familiarity with security concepts—it demands a strategic approach to learning, practical experience, and an understanding of organizational security management. The CISM exam evaluates knowledge across four critical domains: governance, risk management, program development, and incident management. This article explores effective strategies, preparation techniques, and tips to help candidates confidently approach the exam and maximize their chances of success.
Understanding the Structure of the CISM Exam
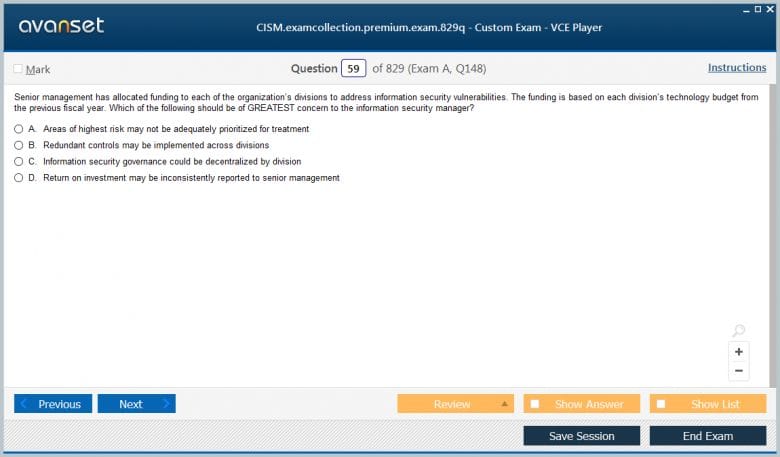
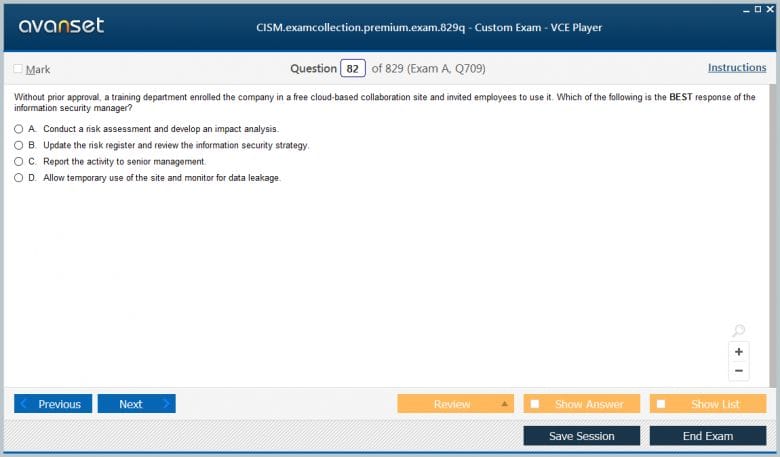
Before beginning exam preparation, it is essential to understand its structure and focus areas. The CISM exam is designed to test not only knowledge but also the application of security management principles in real-world scenarios. It consists of multiple-choice questions that assess the candidate’s ability to:
Analyze complex situations
Make informed decisions aligned with business objectives
Prioritize actions based on risk and organizational needs
Communicate effectively with stakeholders
The four domains of the exam carry varying weight, reflecting the emphasis on governance, risk management, program development, and incident management. Understanding these weightings helps candidates allocate study time effectively:
Information Security Governance: 24%
Information Risk Management: 30%
Information Security Program Development and Management: 27%
Information Security Incident Management: 19%
Focusing on the domains with higher weight ensures candidates are well-prepared for the areas most heavily tested.
Setting a Study Plan
Creating a structured study plan is crucial for success. The following steps provide a roadmap for exam preparation:
Assess Your Knowledge: Begin by evaluating your current understanding of the four CISM domains. Identify areas of strength and weakness to focus your efforts.
Set a Timeline: Allocate sufficient time for study based on your experience and knowledge level. Typically, candidates dedicate three to six months of consistent preparation.
Divide Study Materials: Break down the exam content into manageable sections. Focus on one domain at a time before integrating knowledge across domains.
Schedule Practice Exams: Regularly test your understanding with practice questions and scenario-based exercises. This helps reinforce concepts and identify gaps.
Review and Adjust: Periodically review progress and adjust your study plan as needed. Concentrate on areas where improvement is required and refine your strategies.
A well-structured plan ensures consistent progress, reduces stress, and builds confidence as the exam date approaches.
Effective Study Resources
CISM candidates have access to a variety of study resources designed to support comprehensive exam preparation. These include:
Official ISACA Study Guides: These guides provide in-depth explanations of concepts, frameworks, and best practices across all four domains.
Practice Exams: Scenario-based practice questions help candidates develop critical thinking skills and apply knowledge to real-world situations.
Training Workshops: Instructor-led training sessions provide interactive learning opportunities, clarify complex topics, and allow candidates to engage with experienced professionals.
Online Study Groups: Collaborating with peers provides new perspectives, reinforces understanding, and encourages discussion of practical scenarios.
Using a combination of these resources ensures a well-rounded preparation approach that covers both theoretical knowledge and practical application.
Focus on Real-World Application
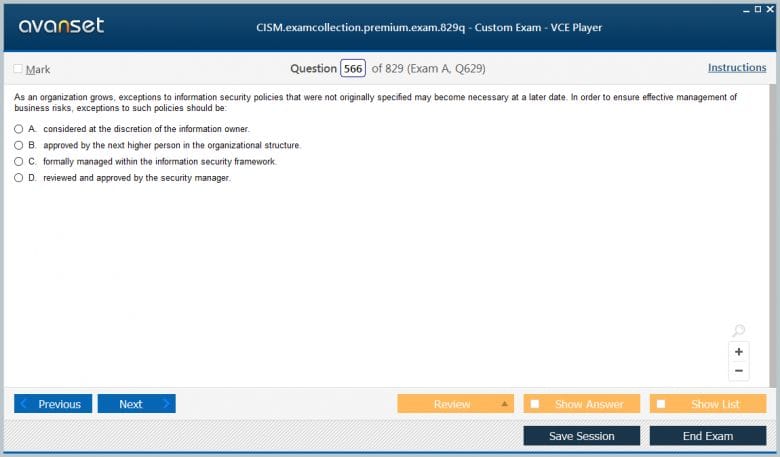
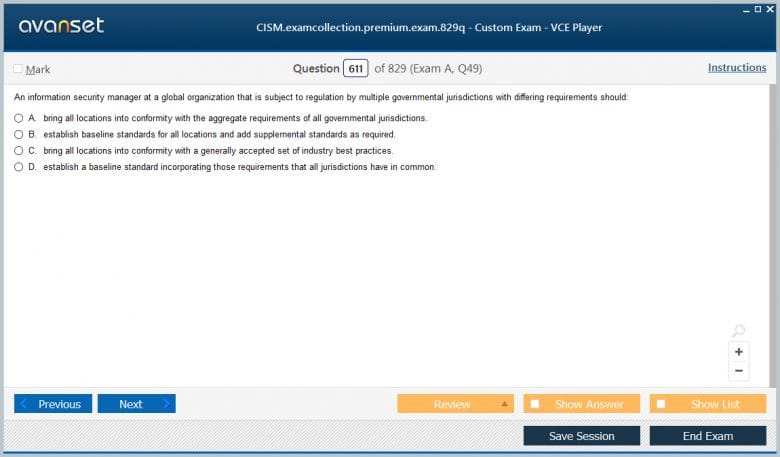
One of the distinguishing features of the CISM exam is its emphasis on real-world application. Candidates are expected to demonstrate the ability to manage security programs and make strategic decisions rather than simply recalling facts. This requires:
Understanding organizational objectives and aligning security initiatives with business goals
Applying risk management principles to prioritize actions and resources
Developing and monitoring security programs to ensure compliance and effectiveness
Responding effectively to security incidents and minimizing organizational impact
Engaging with practical scenarios through simulations, case studies, or workplace experience helps candidates build the judgment and decision-making skills necessary for success.
Key Exam Preparation Strategies
Successful CISM candidates employ targeted strategies to enhance understanding and retention of exam material. Some recommended approaches include:
Active Learning
Active learning techniques, such as summarizing concepts in your own words, creating diagrams, or teaching topics to others, reinforce understanding. Passive reading is insufficient for CISM preparation, as the exam requires analysis and application.
Scenario-Based Practice
Since the exam emphasizes real-world decision-making, practicing with scenario-based questions is essential. Evaluate each scenario critically, consider potential risks, and choose actions aligned with governance principles and organizational objectives.
Time Management
Effective time management during both preparation and the exam is critical. Allocate time for each domain based on its weight in the exam and ensure balanced coverage. During the exam, read questions carefully, eliminate clearly incorrect options, and prioritize scenarios that require detailed analysis.
Focus on Core Principles
While the exam may include detailed scenarios, core principles remain central. Understanding governance frameworks, risk assessment methodologies, program management processes, and incident response best practices provides a foundation for analyzing complex situations.
Continuous Review
Regularly revisiting material helps reinforce retention. Create a review schedule that revisits key topics weekly, consolidates learning, and addresses areas where understanding is weakest.
The Role of Professional Experience
Hands-on experience in information security management significantly enhances exam readiness. Practical experience allows candidates to:
Apply theoretical concepts to real-world organizational challenges
Understand how policies, frameworks, and procedures function in practice
Develop strategic thinking skills necessary for governance and decision-making
Build confidence in responding to security incidents and risk scenarios
Even for experienced professionals, reviewing prior experiences in the context of the CISM domains helps solidify understanding and enables better application during the exam.
Overcoming Common Challenges
CISM candidates often face several common challenges during preparation:
Complex Terminology: Information security management involves specialized language. Using flashcards or glossaries can aid retention.
Scenario Analysis: Some candidates struggle to translate concepts into practical decisions. Practice with real-world examples and case studies is key.
Time Pressure: Balancing study with professional responsibilities can be challenging. A disciplined schedule and incremental progress help maintain consistency.
Application vs. Memorization: The exam tests judgment and strategic thinking rather than rote memorization. Emphasizing understanding over memorization ensures better performance.
Acknowledging these challenges early and employing targeted strategies can reduce stress and improve exam outcomes.
Maintaining a Balanced Approach
While preparation is critical, maintaining balance is equally important. Candidates should ensure adequate rest, nutrition, and stress management during the study period. Short breaks, exercise, and mindfulness practices enhance focus and retention. A balanced approach also reduces burnout, allowing candidates to maintain sustained motivation throughout preparation.
Exam Day Tips
On exam day, several practical strategies can enhance performance:
Arrive early to allow time for orientation and relaxation
Read each question carefully and focus on scenario context
Manage time effectively, allocating sufficient time to complex questions
Trust your preparation and avoid second-guessing initial judgments
Stay calm and maintain focus throughout the exam
Confidence, combined with thorough preparation, greatly improves the likelihood of passing the exam on the first attempt.
Career Advantages After Certification
Successfully earning CISM certification positions professionals for significant career growth. Key benefits include:
Eligibility for managerial and executive roles in cybersecurity
Enhanced credibility with peers, executives, and clients
Opportunities to influence organizational security strategy
Access to global career opportunities and professional networks
Recognition as a strategic decision-maker in information security
The certification’s emphasis on governance, risk management, and strategic leadership sets CISM-certified professionals apart, preparing them for long-term success in information security management.
Leveraging CISM for Long-Term Growth
CISM is not just an exam credential—it is a tool for professional development. Certified professionals often leverage their skills to:
Lead enterprise security initiatives
Develop governance frameworks aligned with business objectives
Mentor teams and build organizational security culture
Implement best practices for risk assessment and incident response
Drive continuous improvement in security programs
By integrating knowledge and experience, CISM-certified individuals become strategic assets within their organizations.
Preparing for Future Challenges
The field of information security is dynamic, with evolving threats, technologies, and regulations. CISM certification equips professionals to:
Anticipate emerging risks and adapt strategies proactively
Implement flexible governance frameworks capable of responding to change
Communicate security priorities effectively to stakeholders
Influence policy decisions that enhance organizational resilience
CISM prepares professionals not just for today’s challenges but also for the complex security landscape of the future.
Preparing for the CISM certification exam requires a structured approach, practical experience, and a focus on real-world application. By understanding the exam structure, developing a detailed study plan, leveraging multiple resources, and practicing scenario-based analysis, candidates can maximize their chances of success. Beyond passing the exam, preparation provides valuable insights and skills applicable to strategic information security management roles.
CISM certification is a career-defining achievement, positioning professionals for leadership, global opportunities, and recognition as strategic decision-makers in information security. By approaching preparation thoughtfully and systematically, candidates not only succeed in the exam but also strengthen their ability to lead, influence, and innovate in the field of cybersecurity.
Advanced Governance Frameworks and Strategies for CISM Professionals
In the modern business environment, organizations face an increasingly complex landscape of cybersecurity threats, regulatory requirements, and evolving technology. Certified Information Security Manager (CISM) professionals play a critical role in bridging the gap between technical security measures and strategic business objectives. Beyond passing the CISM exam, mastering advanced governance frameworks, risk management methodologies, and security program strategies is essential for professionals seeking leadership roles in information security.
Understanding Information Security Governance
Information security governance is the foundation of any effective cybersecurity strategy. It provides a structured framework for aligning security initiatives with organizational objectives, regulatory requirements, and stakeholder expectations. Governance encompasses policies, standards, procedures, and processes that guide decision-making and resource allocation across the enterprise.
Effective governance ensures that security is not treated as a reactive or isolated function but as an integral part of organizational strategy. This involves setting clear objectives, defining accountability, and regularly measuring performance against established goals.
Key Governance Frameworks
Several governance frameworks are widely recognized for guiding CISM professionals in developing robust security programs. Familiarity with these frameworks helps ensure that governance practices are consistent, scalable, and aligned with global best practices.
COBIT (Control Objectives for Information and Related Technologies)
COBIT is a comprehensive framework for managing and governing enterprise IT. It provides principles, practices, and metrics for aligning IT operations with business goals. CISM professionals use COBIT to establish clear accountability, measure performance, and manage risk across information systems. The framework emphasizes continuous improvement and supports decision-making at both operational and strategic levels.
ISO/IEC 27001
ISO/IEC 27001 is an international standard for information security management systems (ISMS). It provides a systematic approach to managing sensitive information, ensuring confidentiality, integrity, and availability. CISM professionals leverage ISO/IEC 27001 to implement security controls, assess risks, and maintain compliance with global regulatory requirements. The framework promotes a culture of security awareness and continuous monitoring.
NIST Cybersecurity Framework
The National Institute of Standards and Technology (NIST) Cybersecurity Framework offers a flexible approach to managing and mitigating cybersecurity risks. It consists of five core functions: Identify, Protect, Detect, Respond, and Recover. CISM professionals utilize the NIST framework to design programs that address organizational risk, ensure regulatory compliance, and enhance incident response capabilities.
Risk Management Frameworks
Integrating risk management frameworks with governance strategies is critical for informed decision-making. Frameworks such as FAIR (Factor Analysis of Information Risk) and OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation) provide structured methods for quantifying risk and prioritizing mitigation efforts. CISM professionals use these frameworks to ensure that security initiatives are cost-effective, aligned with business objectives, and capable of addressing both current and emerging threats.
Information Risk Management Strategies
Risk management is a central responsibility of CISM-certified professionals. Effective risk management involves identifying potential threats, assessing vulnerabilities, evaluating the impact of incidents, and implementing controls to reduce risk to an acceptable level.
Identifying Risks
Risk identification involves understanding the organization’s assets, processes, and technology infrastructure. CISM professionals conduct thorough assessments to identify potential threats, including cyberattacks, insider threats, natural disasters, and operational failures. Accurate risk identification requires collaboration with stakeholders across the organization and continuous monitoring of the threat landscape.
Risk Assessment and Analysis
Once risks are identified, professionals evaluate their likelihood and potential impact. Quantitative and qualitative methods are used to prioritize risks based on business objectives, regulatory requirements, and organizational tolerance. Risk assessment frameworks help professionals determine which risks require immediate attention and which can be monitored over time.
Implementing Risk Mitigation Controls
Mitigation strategies include technical controls, such as firewalls and encryption, as well as administrative and procedural measures like policies, training, and audits. CISM professionals ensure that controls are appropriate for the organization’s risk profile, cost-effective, and adaptable to evolving threats.
Continuous Risk Monitoring
Risk management is not a one-time activity but an ongoing process. Continuous monitoring allows organizations to respond promptly to emerging threats, evaluate the effectiveness of existing controls, and adjust strategies as needed. CISM professionals establish metrics and reporting mechanisms to track risk performance and communicate findings to executive leadership.
Developing and Managing Security Programs
A critical aspect of CISM responsibilities involves developing and managing enterprise-wide security programs. These programs integrate governance and risk management principles to protect information assets and support business objectives.
Program Design and Planning
Program design begins with understanding organizational priorities and risk appetite. CISM professionals identify critical assets, define program objectives, allocate resources, and establish timelines. Effective planning ensures that security initiatives address the most significant threats while aligning with broader business strategies.
Resource Allocation and Management
Managing a security program requires effective allocation of personnel, technology, and budget. CISM professionals must ensure that teams have the necessary skills and tools to implement security measures efficiently. Balancing limited resources against organizational priorities is a key component of program management.
Program Monitoring and Evaluation
Ongoing monitoring allows professionals to evaluate program effectiveness, measure performance against objectives, and identify areas for improvement. Metrics such as incident response times, policy compliance, and risk reduction outcomes provide actionable insights for program refinement.
Program Communication and Reporting
Communication is essential for program success. CISM professionals regularly report to executive leadership, stakeholders, and boards on security posture, risks, and progress. Clear communication ensures transparency, facilitates informed decision-making, and demonstrates the value of security initiatives.
Incident Management and Response
Despite preventive measures, security incidents can still occur. CISM professionals play a pivotal role in preparing for, responding to, and recovering from security breaches.
Developing Incident Response Plans
A comprehensive incident response plan outlines roles, responsibilities, and procedures for addressing security events. Plans cover detection, containment, eradication, recovery, and post-incident analysis. CISM professionals ensure that plans are tested, updated regularly, and integrated with broader organizational policies.
Coordinating Response Efforts
Effective incident response requires coordination among IT teams, legal departments, communications, and executive leadership. CISM professionals lead response efforts, ensuring that actions are timely, effective, and aligned with organizational objectives. Coordination also involves engaging with external partners, regulators, or law enforcement as needed.
Post-Incident Analysis and Improvement
After an incident, organizations must conduct a thorough review to identify root causes, assess the effectiveness of the response, and implement corrective actions. CISM professionals use lessons learned to strengthen security programs, update policies, and enhance risk management strategies.
Leveraging Metrics for Security Effectiveness
Measuring and demonstrating the effectiveness of security programs is essential for governance and decision-making. CISM professionals use metrics to track performance, justify investments, and identify areas for improvement.
Key Performance Indicators
Metrics may include incident response times, policy compliance rates, risk reduction statistics, and employee security awareness levels. Establishing meaningful KPIs enables organizations to evaluate program effectiveness objectively.
Reporting to Leadership
Transparent reporting helps executives understand the security landscape, make informed decisions, and allocate resources effectively. CISM professionals present data in a clear, actionable manner, highlighting successes, challenges, and strategic recommendations.
Continuous Improvement
Security programs are dynamic and must evolve alongside organizational needs and emerging threats. CISM professionals foster a culture of continuous improvement, regularly reviewing metrics, adjusting strategies, and implementing best practices to enhance overall security posture.
The Strategic Role of CISM Professionals
CISM certification positions professionals as strategic leaders within their organizations. Beyond technical expertise, CISM professionals:
Influence policy decisions and governance frameworks
Align security initiatives with business objectives
Lead risk assessment and mitigation efforts
Drive organizational resilience and preparedness
Mentor teams and foster a culture of security awareness
By taking a strategic approach, CISM-certified professionals contribute not only to risk reduction but also to organizational growth and long-term sustainability.
Global Implications and Opportunities
CISM certification is recognized worldwide, offering professionals opportunities to work across industries and geographies. Certified individuals are sought after for roles in multinational corporations, government agencies, and consulting firms, where governance, risk management, and program leadership are highly valued. The global recognition of CISM ensures that professionals can leverage their skills in diverse organizational contexts, influencing security strategy on an international scale.
Preparing for Emerging Threats
The cybersecurity landscape is constantly evolving, with new threats, technologies, and regulatory challenges emerging regularly. CISM professionals must stay informed about trends such as:
Advanced persistent threats and cybercrime tactics
Cloud security and virtualization risks
Regulatory changes and compliance requirements
Emerging technologies such as AI and IoT
By anticipating changes and adapting governance, risk, and program strategies, CISM professionals ensure that organizations remain resilient and secure in an unpredictable environment.
Mastering advanced governance frameworks, risk management strategies, and security program management is critical for CISM-certified professionals. By leveraging recognized frameworks, implementing structured risk management, developing comprehensive programs, and effectively managing incidents, CISM professionals position themselves as strategic leaders in information security.
The certification is not only a testament to knowledge but also a pathway to practical expertise in aligning security initiatives with organizational goals. CISM professionals play a pivotal role in shaping the cybersecurity posture of organizations, driving strategic decisions, and preparing for future challenges in an increasingly complex digital landscape.
Advanced Governance Frameworks and Strategies for CISM Professionals
In the modern business environment, organizations face an increasingly complex landscape of cybersecurity threats, regulatory requirements, and evolving technology. Certified Information Security Manager (CISM) professionals play a critical role in bridging the gap between technical security measures and strategic business objectives. Beyond passing the CISM exam, mastering advanced governance frameworks, risk management methodologies, and security program strategies is essential for professionals seeking leadership roles in information security.
Understanding Information Security Governance
Information security governance is the foundation of any effective cybersecurity strategy. It provides a structured framework for aligning security initiatives with organizational objectives, regulatory requirements, and stakeholder expectations. Governance encompasses policies, standards, procedures, and processes that guide decision-making and resource allocation across the enterprise.
Effective governance ensures that security is not treated as a reactive or isolated function but as an integral part of organizational strategy. This involves setting clear objectives, defining accountability, and regularly measuring performance against established goals.
Key Governance Frameworks
Several governance frameworks are widely recognized for guiding CISM professionals in developing robust security programs. Familiarity with these frameworks helps ensure that governance practices are consistent, scalable, and aligned with global best practices.
COBIT (Control Objectives for Information and Related Technologies)
COBIT is a comprehensive framework for managing and governing enterprise IT. It provides principles, practices, and metrics for aligning IT operations with business goals. CISM professionals use COBIT to establish clear accountability, measure performance, and manage risk across information systems. The framework emphasizes continuous improvement and supports decision-making at both operational and strategic levels.
ISO/IEC 27001
ISO/IEC 27001 is an international standard for information security management systems (ISMS). It provides a systematic approach to managing sensitive information, ensuring confidentiality, integrity, and availability. CISM professionals leverage ISO/IEC 27001 to implement security controls, assess risks, and maintain compliance with global regulatory requirements. The framework promotes a culture of security awareness and continuous monitoring.
NIST Cybersecurity Framework
The National Institute of Standards and Technology (NIST) Cybersecurity Framework offers a flexible approach to managing and mitigating cybersecurity risks. It consists of five core functions: Identify, Protect, Detect, Respond, and Recover. CISM professionals utilize the NIST framework to design programs that address organizational risk, ensure regulatory compliance, and enhance incident response capabilities.
Risk Management Frameworks
Integrating risk management frameworks with governance strategies is critical for informed decision-making. Frameworks such as FAIR (Factor Analysis of Information Risk) and OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation) provide structured methods for quantifying risk and prioritizing mitigation efforts. CISM professionals use these frameworks to ensure that security initiatives are cost-effective, aligned with business objectives, and capable of addressing both current and emerging threats.
Information Risk Management Strategies
Risk management is a central responsibility of CISM-certified professionals. Effective risk management involves identifying potential threats, assessing vulnerabilities, evaluating the impact of incidents, and implementing controls to reduce risk to an acceptable level.
Identifying Risks
Risk identification involves understanding the organization’s assets, processes, and technology infrastructure. CISM professionals conduct thorough assessments to identify potential threats, including cyberattacks, insider threats, natural disasters, and operational failures. Accurate risk identification requires collaboration with stakeholders across the organization and continuous monitoring of the threat landscape.
Risk Assessment and Analysis
Once risks are identified, professionals evaluate their likelihood and potential impact. Quantitative and qualitative methods are used to prioritize risks based on business objectives, regulatory requirements, and organizational tolerance. Risk assessment frameworks help professionals determine which risks require immediate attention and which can be monitored over time.
Implementing Risk Mitigation Controls
Mitigation strategies include technical controls, such as firewalls and encryption, as well as administrative and procedural measures like policies, training, and audits. CISM professionals ensure that controls are appropriate for the organization’s risk profile, cost-effective, and adaptable to evolving threats.
Continuous Risk Monitoring
Risk management is not a one-time activity but an ongoing process. Continuous monitoring allows organizations to respond promptly to emerging threats, evaluate the effectiveness of existing controls, and adjust strategies as needed. CISM professionals establish metrics and reporting mechanisms to track risk performance and communicate findings to executive leadership.
Developing and Managing Security Programs
A critical aspect of CISM responsibilities involves developing and managing enterprise-wide security programs. These programs integrate governance and risk management principles to protect information assets and support business objectives.
Program Design and Planning
Program design begins with understanding organizational priorities and risk appetite. CISM professionals identify critical assets, define program objectives, allocate resources, and establish timelines. Effective planning ensures that security initiatives address the most significant threats while aligning with broader business strategies.
Resource Allocation and Management
Managing a security program requires effective allocation of personnel, technology, and budget. CISM professionals must ensure that teams have the necessary skills and tools to implement security measures efficiently. Balancing limited resources against organizational priorities is a key component of program management.
Program Monitoring and Evaluation
Ongoing monitoring allows professionals to evaluate program effectiveness, measure performance against objectives, and identify areas for improvement. Metrics such as incident response times, policy compliance, and risk reduction outcomes provide actionable insights for program refinement.
Program Communication and Reporting
Communication is essential for program success. CISM professionals regularly report to executive leadership, stakeholders, and boards on security posture, risks, and progress. Clear communication ensures transparency, facilitates informed decision-making, and demonstrates the value of security initiatives.
Incident Management and Response
Despite preventive measures, security incidents can still occur. CISM professionals play a pivotal role in preparing for, responding to, and recovering from security breaches.
Developing Incident Response Plans
A comprehensive incident response plan outlines roles, responsibilities, and procedures for addressing security events. Plans cover detection, containment, eradication, recovery, and post-incident analysis. CISM professionals ensure that plans are tested, updated regularly, and integrated with broader organizational policies.
Coordinating Response Efforts
Effective incident response requires coordination among IT teams, legal departments, communications, and executive leadership. CISM professionals lead response efforts, ensuring that actions are timely, effective, and aligned with organizational objectives. Coordination also involves engaging with external partners, regulators, or law enforcement as needed.
Post-Incident Analysis and Improvement
After an incident, organizations must conduct a thorough review to identify root causes, assess the effectiveness of the response, and implement corrective actions. CISM professionals use lessons learned to strengthen security programs, update policies, and enhance risk management strategies.
Leveraging Metrics for Security Effectiveness
Measuring and demonstrating the effectiveness of security programs is essential for governance and decision-making. CISM professionals use metrics to track performance, justify investments, and identify areas for improvement.
Key Performance Indicators
Metrics may include incident response times, policy compliance rates, risk reduction statistics, and employee security awareness levels. Establishing meaningful KPIs enables organizations to evaluate program effectiveness objectively.
Reporting to Leadership
Transparent reporting helps executives understand the security landscape, make informed decisions, and allocate resources effectively. CISM professionals present data in a clear, actionable manner, highlighting successes, challenges, and strategic recommendations.
Continuous Improvement
Security programs are dynamic and must evolve alongside organizational needs and emerging threats. CISM professionals foster a culture of continuous improvement, regularly reviewing metrics, adjusting strategies, and implementing best practices to enhance overall security posture.
The Strategic Role of CISM Professionals
CISM certification positions professionals as strategic leaders within their organizations. Beyond technical expertise, CISM professionals:
Influence policy decisions and governance frameworks
Align security initiatives with business objectives
Lead risk assessment and mitigation efforts
Drive organizational resilience and preparedness
Mentor teams and foster a culture of security awareness
By taking a strategic approach, CISM-certified professionals contribute not only to risk reduction but also to organizational growth and long-term sustainability.
Global Implications and Opportunities
CISM certification is recognized worldwide, offering professionals opportunities to work across industries and geographies. Certified individuals are sought after for roles in multinational corporations, government agencies, and consulting firms, where governance, risk management, and program leadership are highly valued. The global recognition of CISM ensures that professionals can leverage their skills in diverse organizational contexts, influencing security strategy on an international scale.
Preparing for Emerging Threats
The cybersecurity landscape is constantly evolving, with new threats, technologies, and regulatory challenges emerging regularly. CISM professionals must stay informed about trends such as:
Advanced persistent threats and cybercrime tactics
Cloud security and virtualization risks
Regulatory changes and compliance requirements
Emerging technologies such as AI and IoT
By anticipating changes and adapting governance, risk, and program strategies, CISM professionals ensure that organizations remain resilient and secure in an unpredictable environment.
Mastering advanced governance frameworks, risk management strategies, and security program management is critical for CISM-certified professionals. By leveraging recognized frameworks, implementing structured risk management, developing comprehensive programs, and effectively managing incidents, CISM professionals position themselves as strategic leaders in information security.
The certification is not only a testament to knowledge but also a pathway to practical expertise in aligning security initiatives with organizational goals. CISM professionals play a pivotal role in shaping the cybersecurity posture of organizations, driving strategic decisions, and preparing for future challenges in an increasingly complex digital landscape.
Maintaining CISM Certification and Continuing Professional Development
Achieving Certified Information Security Manager (CISM) certification is a significant accomplishment, but maintaining the credential is equally important. CISM-certified professionals must commit to ongoing professional development to ensure that their knowledge remains current and relevant in the rapidly evolving field of information security. Continuous learning not only sustains certification but also enhances the ability to implement effective security strategies and advance in leadership roles.
Continuing Professional Education Requirements
ISACA mandates that CISM-certified professionals participate in Continuing Professional Education (CPE) to maintain their certification. CPE ensures that individuals remain up-to-date with emerging threats, technologies, regulations, and best practices. The general requirements include:
Annual CPE hours: Professionals must earn a minimum number of CPE hours each year to demonstrate active engagement in professional development.
Three-year reporting cycle: CISM-certified individuals must complete a set number of CPE hours over a three-year period.
Activities accepted for CPE: CPE credits can be earned through various activities, including attending conferences, webinars, workshops, publishing articles, participating in training programs, and teaching or mentoring in the field of information security.
By adhering to CPE requirements, professionals maintain the credibility of their certification while staying informed about evolving industry trends.
Professional Networking and Community Engagement
Engagement with professional communities is a key component of continuing development. Networking provides opportunities for knowledge sharing, mentorship, and collaboration on complex security challenges. CISM-certified professionals often participate in:
Local and international ISACA chapters
Professional conferences and symposiums
Security-focused forums and online discussion groups
Peer mentoring programs
Active involvement in these communities allows professionals to exchange insights, stay informed about emerging threats, and strengthen relationships that can support career growth.
Emerging Trends in Information Security
The field of information security is constantly evolving, driven by technological innovation, regulatory developments, and increasingly sophisticated threats. CISM-certified professionals must stay ahead of these trends to effectively protect organizational assets and guide strategic decision-making.
Cloud Security
As organizations increasingly migrate to cloud environments, securing cloud infrastructure has become a top priority. CISM professionals must understand cloud service models, shared responsibility frameworks, and cloud-specific risk factors. Implementing governance, compliance, and monitoring strategies tailored to cloud deployments ensures organizational resilience.
Artificial Intelligence and Machine Learning
AI and machine learning are transforming security operations, from threat detection to automated response. CISM professionals must evaluate the ethical, operational, and security implications of these technologies, integrating them into broader governance and risk management frameworks to enhance efficiency without compromising security or compliance.
Internet of Things (IoT)
IoT devices expand organizational networks and introduce new vulnerabilities. CISM-certified professionals assess IoT risks, establish policies for secure deployment, and monitor device behavior to minimize threats while supporting innovation and operational efficiency.
Regulatory and Compliance Changes
Global and regional regulations continue to evolve, affecting how organizations handle data privacy, cybersecurity reporting, and incident management. CISM professionals stay informed about these changes, ensuring that governance frameworks, policies, and risk management strategies remain compliant and effective.
Cyber Threat Landscape
Threat actors continuously develop more sophisticated attack techniques, including ransomware, social engineering, and advanced persistent threats. CISM professionals monitor emerging threats, adapt security programs, and ensure that incident response plans are agile and capable of addressing evolving risks.
Strategic Career Planning for CISM Professionals
CISM certification provides a foundation for strategic career growth. Professionals can leverage their expertise to secure leadership roles, influence organizational security strategies, and expand their impact across industries.
Leadership Roles
CISM-certified professionals are often considered for high-level positions such as Chief Information Security Officer (CISO), Information Security Manager, or IT Risk Manager. These roles require strategic thinking, governance expertise, and the ability to communicate effectively with executive leadership.
Specialized Roles
Beyond traditional leadership positions, CISM professionals can pursue specialized roles in risk assessment, compliance management, security auditing, or security consulting. These roles benefit from deep knowledge of governance, risk, and program management, positioning CISM-certified professionals as experts in their fields.
Global Opportunities
CISM is a globally recognized certification, opening opportunities to work across industries and geographic regions. Professionals may engage in international projects, manage cross-border compliance initiatives, or provide consulting services for multinational organizations, expanding their career reach and impact.
Mentorship and Thought Leadership
Experienced CISM professionals often mentor junior staff, contribute to professional publications, or speak at conferences. By sharing knowledge and shaping industry discourse, professionals strengthen their own expertise while enhancing their reputation and influence in the information security community.
Best Practices for Sustaining Career Growth
To sustain long-term career growth, CISM-certified professionals should adopt proactive strategies:
Continuous Learning: Regularly pursue certifications, training, and workshops to expand technical and strategic knowledge.
Practical Application: Apply knowledge through real-world projects, governance initiatives, and security program management.
Networking: Engage with professional communities to exchange ideas, identify opportunities, and stay informed.
Strategic Communication: Develop the ability to communicate security priorities and risks effectively to executives and stakeholders.
Adaptability: Remain flexible and responsive to technological changes, emerging threats, and regulatory developments.
These best practices ensure that CISM-certified professionals remain valuable assets to their organizations while advancing their careers.
Measuring Impact and Value
CISM professionals should measure the impact of their work to demonstrate value. Key indicators may include:
Reduction in security incidents and breaches
Compliance with regulatory requirements and successful audits
Improvements in risk management and mitigation outcomes
Efficiency and effectiveness of security program operations
Employee security awareness and engagement
By quantifying contributions, CISM-certified professionals can justify investments, secure leadership support, and reinforce their strategic role in the organization.
Preparing for the Future of Information Security
The future of information security will be shaped by technological advancements, evolving threats, and organizational transformation. CISM-certified professionals must prepare for:
The continued integration of AI, automation, and analytics in security operations
Increased regulatory scrutiny and data protection requirements
Expansion of hybrid and remote work environments
Advanced persistent threats and cybercrime innovations
Proactive planning, ongoing education, and strategic leadership will enable CISM professionals to navigate these challenges and maintain organizational resilience.
Conclusion
Maintaining CISM certification and engaging in continuous professional development are essential for long-term success in information security. By staying current with emerging trends, actively participating in professional communities, and applying strategic governance and risk management principles, CISM-certified professionals enhance their value and influence within organizations.
CISM provides not only a credential but also a framework for career growth, strategic decision-making, and leadership. Professionals who leverage their certification through ongoing education, mentorship, and real-world application position themselves for success in a dynamic, global, and high-stakes field. By committing to continuous improvement, CISM-certified individuals ensure that they remain at the forefront of information security management, capable of guiding organizations safely through an increasingly complex digital landscape.
ExamCollection provides the complete prep materials in vce files format which include Isaca CISM certification exam dumps, practice test questions and answers, video training course and study guide which help the exam candidates to pass the exams quickly. Fast updates to Isaca CISM certification exam dumps, practice test questions and accurate answers vce verified by industry experts are taken from the latest pool of questions.
Isaca CISM Video Courses

Top Isaca Certification Exams
Site Search: