Pass Your Cisco CCNA Certification Easy!
Cisco CCNA Certification Exams Questions & Answers, Accurate & Verified By IT Experts
Instant Download, Free Fast Updates, 99.6% Pass Rate.

$69.99
Download Free CCNA Practice Test Questions VCE Files
| Exam | Title | Files |
|---|---|---|
Exam 200-301 |
Title Cisco Certified Network Associate (CCNA) |
Files 2 |
Cisco CCNA Certification Exam Dumps & Practice Test Questions
Prepare with top-notch Cisco CCNA certification practice test questions and answers, vce exam dumps, study guide, video training course from ExamCollection. All Cisco CCNA certification exam dumps & practice test questions and answers are uploaded by users who have passed the exam themselves and formatted them into vce file format.
Introduction to Cisco CCNA Certification
The Cisco CCNA certification is an essential milestone for networking professionals aiming to validate their knowledge of IP connectivity, routing and switching, network security, and basic automation. Achieving this credential demonstrates not only theoretical understanding but also practical skills that can be applied in real-world enterprise environments. Many candidates start their preparation without fully grasping the breadth of topics, which include VLAN configuration, routing protocols, and subnetting fundamentals. Structured preparation, including practice test questions, is key to understanding the concepts rather than just memorizing commands.One effective way to gain a broader perspective is by exploring the mindset of cybersecurity professionals. For example, beginners who follow a roadmap to ethical hacking can develop analytical skills that reinforce their understanding of network behavior under attack scenarios. Understanding attacks and their prevention indirectly strengthens CCNA-relevant knowledge, particularly in areas related to network security and monitoring.
Recognizing Security Threats in Networking
A fundamental part of CCNA preparation is understanding security threats, even at the entry-level. Candidates often encounter scenario-based questions that require them to identify vulnerabilities, choose proper access control mechanisms, and recommend mitigation strategies. While CCNA does not focus on deep cybersecurity topics, understanding threats helps candidates approach networking with a defensive mindset. Network segmentation, ACLs, and secure routing practices become easier to grasp when students know the potential risks.To develop this awareness, candidates can see CISSP threat identification guides, which categorize weaknesses, attacks, and threat vectors in an organized way. These resources build conceptual clarity, allowing learners to correlate networking principles with real-world security implications.
Networking for Modern Connected Systems
The world of networking is evolving rapidly, with emerging technologies like autonomous vehicles, IoT, and smart infrastructure. While CCNA focuses on foundational networking concepts, awareness of these modern applications enhances understanding of why scalability, redundancy, and security are emphasized. Candidates should recognize that networking principles learned in CCNA exams form the foundation for managing complex, connected environments.Exam questions often present scenarios requiring conceptual application rather than rote memorization. For instance, understanding the challenges of connected vehicle networks can clarify why redundant routing, failover mechanisms, and secure communication channels are critical. Discussing cybersecurity strategies for autonomous vehicles provide context for network design considerations, enriching the candidate’s perspective.
Hands-On Labs and Practical Skills
Practical experience is crucial for CCNA exam success. Candidates should engage in hands-on labs that reinforce their understanding of routing, switching, and troubleshooting. Analytical skills develop when students study packet flows, protocol behavior, and consequences of misconfigurations. Scenario-based practice questions test these skills, helping learners move beyond memorization into applied knowledge.Supplementing CCNA labs with structured exercises, such as malware sandbox setups, can enhance analytical thinking. Though malware analysis is not part of CCNA, the discipline of observing system behavior under different conditions builds the careful observation and troubleshooting mindset that is tested in the exam.
Linux and Command-Line Skills for Networking
Cisco devices rely heavily on command-line interfaces, and familiarity with operating systems like Linux can improve candidate confidence. Networking tasks, scripting, and automation exercises benefit from exposure to Linux environments, where commands and configuration logic mirror aspects of Cisco IOS. Candidates with strong CLI skills can navigate labs more efficiently and troubleshoot scenarios during practice exams.The Kali Linux essentials introduce learners to Linux basics in a security-focused environment. By practicing commands, understanding file structures, and configuring network interfaces in Linux, candidates reinforce skills directly applicable to CCNA exam labs and simulations.
Cloud Networking Fundamentals
Cloud technologies increasingly intersect with networking, and CCNA exams include concepts related to virtualized environments, hybrid networks, and network services. Understanding how networks operate in cloud environments helps candidates relate foundational routing and switching concepts to modern infrastructures. Exam scenarios may require candidates to analyze how data flows between on-premises and cloud networks or to identify appropriate virtual network configurations.Candidates can explore cloud storage solutions to understand performance, redundancy, and latency trade-offs. Evaluating these storage types demonstrates the network implications of cloud deployment models, preparing candidates for scenario-based exam questions that involve cloud-aware network design.
Cloud Compute Services Overview
Understanding cloud compute services is increasingly relevant for networking professionals because these platforms abstract complex infrastructure tasks, allowing engineers to focus on performance, reliability, and scalability. Cloud services are no longer just optional tools—they form an integral part of enterprise networking. Modern businesses leverage cloud compute services for virtualized environments, load balancing, failover mechanisms, and global service delivery. For CCNA candidates, exploring how these services handle networking can deepen their understanding of routing, subnets, and network design principles that are part of the exam syllabus.Evaluating service models helps candidates identify when to use traditional virtual machines versus managed platforms. For instance, virtual machines allow full control over the OS and networking configurations, whereas platform services abstract these details and handle scalability automatically. A thorough comparison of Google Compute Engine and App Engine demonstrates practical differences, showing how networking, firewall rules, and load balancing are applied in real-world scenarios. This understanding reinforces CCNA concepts related to network traffic, IP addressing, and connectivity, providing candidates with a practical frame of reference beyond the exam.
Starting a Cloud Data Engineering Journey
Data engineering in the cloud combines storage, processing, and networking, making it an excellent complement to CCNA study. While CCNA focuses on IP connectivity, routing, and switching, understanding data flow pipelines improves comprehension of how packets move across distributed systems. Exam questions sometimes simulate scenarios where multiple subnets or VLANs must be connected efficiently, and cloud data concepts can reinforce logical thinking for these designs.Structured learning pathways, such as a Google Cloud Data Engineer prep guide, walk candidates through core networking principles in cloud environments. Topics like data ingestion, ETL pipelines, and database connectivity highlight the importance of bandwidth management, network latency, and subnet segmentation. By understanding these concepts in a cloud context, candidates gain practical insight into the movement of data across complex networks, which can make CCNA troubleshooting questions more intuitive.
Automated Cloud Routing Fundamentals
Routing is at the core of CCNA, and understanding automated solutions in cloud networks introduces candidates to modern network management approaches. Automated routing reduces manual configuration errors, ensures consistency, and scales efficiently across enterprise environments. While CCNA focuses on foundational routing protocols such as OSPF, EIGRP, and RIP, exposure to cloud routing automation helps candidates see how these concepts apply in larger infrastructures.The Google Cloud Router automation provide practical examples of dynamic route propagation, BGP integration, and failover mechanisms. For example, automated cloud routers can learn multiple routes from on-premises networks and adapt automatically to failures, reflecting the same logic as HSRP or OSPF in Cisco labs. Understanding this parallel allows candidates to conceptualize routing decisions rather than memorizing tables, improving their ability to tackle scenario-based exam questions.
Ethical Search and Reconnaissance Techniques
Reconnaissance is the first step in any network assessment, and learning ethical techniques helps CCNA candidates develop analytical skills. Although ethical hacking is not tested directly in CCNA, understanding how to identify exposed services, open ports, and potential vulnerabilities complements network troubleshooting and monitoring tasks. Candidates who are familiar with reconnaissance can anticipate where misconfigurations might occur and why network traffic behaves unexpectedly.Studying guides such as advanced Google dorking commands shows structured approaches to discovering web-accessible information safely. These techniques reinforce analytical thinking and attention to detail, which are crucial for CCNA labs involving packet capture, interface monitoring, or identifying misconfigured devices. For example, recognizing patterns in network behavior or traffic flows is a skill that bridges ethical reconnaissance and network troubleshooting exercises.
Student-Driven Cloud Innovation Insights
Learning ecosystems that emphasize student-driven projects demonstrate how collaborative approaches accelerate skill acquisition. Networking candidates can gain insight into real-world problem solving by examining how cloud tools are integrated into student-led initiatives. These insights foster critical thinking, creativity, and adaptive learning, which are invaluable for CCNA preparation, especially when addressing troubleshooting scenarios.Exploring cases such as student-driven cloud innovation in the Philippines shows how cloud services are leveraged for experimentation, automation, and network deployment. By observing these applications, candidates understand the relevance of network design, traffic management, and security considerations in diverse and evolving environments. This perspective ensures that CCNA students are prepared for exam questions that require application-based reasoning rather than rote memorization.
Web Security and Traffic Validation
Ensuring network traffic integrity is a fundamental skill for CCNA candidates, especially when considering application-layer interactions and security controls. Web traffic validation techniques, such as monitoring referrer headers and enforcing policies, reinforce the need for careful traffic management. These practices parallel CCNA objectives in network security, where understanding data flow and access control is crucial.Furthermore, referrer header validation with CloudFront illustrate practical methods of enforcing security policies on network traffic. By studying these examples, candidates gain a conceptual understanding of how network policies are applied, how traffic can be filtered or monitored, and how misconfigurations might create vulnerabilities. This knowledge supports troubleshooting skills tested in CCNA labs.
Cloud Learning Platforms and Skill Development
Hands-on practice is essential for networking students, and cloud-based sandbox environments provide safe, scalable labs for CCNA exam preparation. These platforms allow learners to simulate routers, switches, firewalls, and end devices without requiring expensive hardware. By experimenting in these environments, candidates reinforce theoretical concepts and build confidence in troubleshooting and configuration tasks.Exploring future cloud learning sandbox platforms exposes students to immersive, interactive labs that mirror real-world network setups. Candidates can practice routing configurations, IP addressing, VLAN creation, and access control in a controlled environment. These activities build muscle memory and analytical reasoning that directly support CCNA exam performance.
Comparing Cloud Computing Models
Understanding the differences between Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) helps candidates contextualize where routing, switching, and security controls fit within modern networks. IaaS provides infrastructure control and network configuration flexibility, PaaS offers managed platforms for application deployment, and SaaS delivers software over the cloud without requiring network setup. This knowledge strengthens conceptual mapping between CCNA topics and cloud environments.A detailed cloud computing models overview helps candidates understand responsibilities, limitations, and practical applications of each model. For instance, knowing which model allows configuring firewalls, subnets, and routing policies can clarify why certain network design decisions are necessary, reinforcing CCNA exam objectives.
Certification Value and Career Progression
Planning for a career beyond CCNA is critical. Understanding how additional certifications complement networking knowledge allows candidates to make informed professional decisions. Evaluating the pros and cons of certifications like CCSP or other security-focused credentials shows how foundational networking skills can be leveraged for specialized roles.A CCSP certification value review illustrates how networking expertise integrates with advanced security responsibilities. For CCNA candidates, this knowledge underscores the importance of mastering routing, switching, and network security fundamentals as a foundation for more complex certifications and real-world job requirements.
Monitoring and Operational Visibility
Operational visibility is essential for maintaining network performance, troubleshooting, and security enforcement. Network engineers must analyze logs, monitor traffic, and detect anomalies to prevent downtime or vulnerabilities. CCNA candidates benefit from exposure to these principles because troubleshooting and monitoring are integral parts of both the exam and real-world network operations.Learning about platforms like Splunk expertise guides equips students with the ability to correlate events, track network changes, and detect performance bottlenecks. Understanding monitoring tools helps candidates anticipate problems and design networks with visibility in mind, reinforcing CCNA objectives such as device monitoring, interface analysis, and protocol behavior evaluation.
VoIP Security and Legacy Systems
Voice over IP networks are widely deployed in enterprise environments, requiring secure configuration and traffic management. CCNA candidates may not be directly tested on VoIP protocols in detail, but understanding these systems helps reinforce core networking principles, such as QoS, VLAN segmentation, and access control. Exposure to legacy communication systems also contextualizes why network reliability and security are emphasized in foundational exams.Studying analyses like modern VoIP security studies demonstrates how attackers exploit misconfigured systems and how monitoring, routing, and segmentation can mitigate these risks. Understanding these examples enhances the candidate’s ability to troubleshoot traffic, recognize vulnerabilities, and apply core networking principles effectively during exams.
Understanding Peripheral Hardware for Networking
Physical components of computers play a crucial role in overall network performance. While CCNA focuses on routing, switching, and IP connectivity, understanding the underlying hardware enhances troubleshooting skills. Devices like network interface cards (NICs), USB adapters, storage controllers, and expansion modules affect latency, throughput, and reliability. Recognizing how these peripherals integrate with servers and endpoints ensures that network engineers can identify bottlenecks or misconfigurations that impact connectivity.A detailed guide to comprehensive computer hardware extensions provides insight into real-world applications. For example, adding a high-speed NIC can reduce packet drops during peak traffic, and configuring storage controllers correctly can prevent data bottlenecks. CCNA candidates benefit by understanding how these hardware decisions influence network behavior, especially in labs simulating end-to-end connectivity across VLANs or subnets.
Red Hat Server Configuration Fundamentals
Server administration, particularly in Linux environments, complements networking knowledge by exposing candidates to OS-level networking and service management. While CCNA primarily covers routing, switching, and security fundamentals, hands-on server experience strengthens the ability to manage IP addresses, configure firewalls, and understand service dependencies.Guides like step by step server configuration illustrate how to set up servers, install necessary packages, and manage services via command-line tools. For CCNA candidates, practicing network interface configuration on a Linux server provides practical insight into IP addressing, routing, and subnet interaction. For example, configuring static IP addresses or custom firewall rules in a Red Hat environment allows candidates to see how servers interact with switches, routers, and VLANs, reinforcing Layer 2 and Layer 3 concepts.
Advanced Threat Detection Techniques
Security awareness is vital for network engineers. Even though CCNA focuses on foundational networking, understanding endpoint protection and threat detection enhances problem-solving capabilities. Network engineers must identify anomalies, monitor traffic, and implement policies that protect data integrity.Learning from expert endpoint security strategies provides practical guidance on threat detection, malware analysis, and real-time monitoring. Applying these insights in networking scenarios helps candidates think critically about how attacks might affect routing, switching, or VLAN segmentation. For instance, recognizing unusual traffic spikes or repeated authentication failures can indicate potential intrusion attempts, prompting candidates to adjust ACLs, firewalls, or routing policies.
Understanding advanced threat detection also builds a proactive mindset. Candidates learn to monitor endpoints, configure logging, and analyze patterns to prevent breaches before they impact network performance. Integrating security concepts into CCNA labs helps learners connect network topology with real-world defense strategies, improving both exam readiness and practical troubleshooting abilities.
HR and Enterprise Exam Awareness
Network engineers often support enterprise applications, including HR management systems. While these systems are not directly tested in CCNA, understanding their network dependencies helps candidates appreciate the broader context of enterprise networking. For example, automated HR platforms rely on VLAN segmentation, subnetting, and firewall policies to ensure secure and reliable access to sensitive employee data.Exploring human resources management exams offers insights into organizational systems that depend on network infrastructure. By understanding how HR systems interact with databases, cloud applications, and internal networks, candidates can better visualize traffic patterns and anticipate connectivity issues. This knowledge strengthens CCNA concepts like routing between subnets, access control lists, and traffic prioritization.
Networking for Content Management Systems
Content management systems (CMS) like Sitecore require reliable, high-performance networks. Understanding how these platforms interact with networking devices helps CCNA candidates grasp real-world traffic flow, routing, and security considerations.Learning about sitecore platform certification exams introduces candidates to deployment best practices, integration workflows, and network requirements. Candidates can simulate traffic routing scenarios, optimize packet flows, and troubleshoot connectivity issues between servers and clients. For example, ensuring efficient delivery of web content across multiple VLANs requires knowledge of inter-VLAN routing, switch port configuration, and traffic monitoring—key CCNA skills.
Understanding CMS networking also highlights security practices. Configuring firewalls, access controls, and secure communication protocols ensures content integrity and protection from unauthorized access. By linking CMS operation with network fundamentals, candidates can apply theoretical knowledge to practical enterprise scenarios, reinforcing the importance of reliability, performance, and security in network design.
Process Optimization and Lean Methodologies
Structured process methodologies, such as Six Sigma, improve systematic problem-solving skills. While Six Sigma is not networking-specific, its principles of efficiency, troubleshooting, and iterative analysis are transferable to network configuration and optimization.Studying six sigma methodology exams illustrates the importance of structured problem-solving. For example, when troubleshooting a VLAN connectivity issue, applying a step-by-step approach ensures that each layer of the OSI model is verified. Candidates learn to identify bottlenecks, analyze traffic flow, and implement corrective actions systematically.
Process optimization also emphasizes measurement and verification. CCNA candidates can apply these principles in lab environments, checking throughput, latency, and packet loss before and after configuration changes. This disciplined approach enhances troubleshooting efficiency, ensuring candidates are better prepared for scenario-based exams and practical networking challenges.
Collaboration Platforms and Network Performance
Collaboration platforms like Slack rely on network performance for seamless communication. Understanding the networking requirements of such tools helps CCNA candidates grasp real-world applications of routing, switching, and traffic prioritization.Exploring slack collaboration platform exams introduces candidates to network integration requirements for collaborative applications. Ensuring low-latency connections between endpoints and servers involves configuring VLANs, applying proper routing, and monitoring network health. For instance, VoIP calls and real-time messaging traffic may require QoS prioritization to prevent delays or packet loss—concepts directly applicable to CCNA labs.
Studying collaboration platforms also strengthens security awareness. Candidates learn to segment traffic, enforce access policies, and monitor endpoints, all reinforcing CCNA objectives related to secure network design and traffic management.
Storage Networking Essentials
Storage area networks (SAN) and network-attached storage (NAS) rely heavily on network infrastructure for high-speed, reliable access to data. While CCNA focuses primarily on routing, switching, and VLAN segmentation, understanding storage networking provides candidates with a broader perspective of how enterprise networks support mission-critical applications. Storage devices often generate large volumes of traffic that must traverse the network efficiently, making knowledge of storage protocols, QoS, and traffic prioritization essential.Such as, snia storage network exams provide detailed insights into technologies like Fibre Channel, iSCSI, and NAS implementations. For example, configuring an iSCSI target requires understanding IP addressing, subnet planning, and switch configurations to prevent congestion. By studying these concepts, CCNA candidates can visualize how storage traffic interacts with other network flows, which is particularly useful when simulating lab scenarios that include multiple VLANs or routing paths.
Cloud Data Platforms and Network Integration
Cloud-based data platforms, such as Snowflake, highlight the growing intersection between networking and cloud infrastructure. These platforms rely on scalable, high-performance network connections to ensure seamless data access and integration. CCNA candidates benefit from understanding how virtualized environments and cloud services depend on networking principles, such as subnetting, routing, and traffic prioritization.Exploring snowflake cloud certification exams provides practical insights into cloud networking dependencies. For instance, ensuring secure and efficient access to cloud-based databases requires configuring VPNs, firewalls, and VLANs correctly. Candidates can simulate scenarios where cloud data is accessed from multiple branch offices, requiring knowledge of routing policies, redundancy, and latency optimization—skills directly aligned with CCNA exam objectives.
Service-Oriented Architecture Networking
Service-Oriented Architecture (SOA) is widely adopted in enterprise networks, where services interact over reliable IP-based communication channels. Understanding SOA networking helps CCNA candidates appreciate distributed system dependencies and the importance of proper routing, VLAN segmentation, and traffic flow management. Network engineers must ensure that service requests traverse the correct paths efficiently, avoiding congestion and minimizing latency, soa integration certification exams illustrate inter-service communication patterns, fault tolerance, and network dependencies. By simulating scenarios where multiple services communicate across VLANs or subnets, CCNA candidates can practice troubleshooting packet drops, misrouted traffic, or firewall misconfigurations. For example, if a service fails due to routing errors, understanding the underlying network topology helps isolate and resolve the issue.
SOA networking exercises also teach candidates about monitoring and performance optimization. By analyzing service-to-service traffic, candidates learn to prioritize critical flows, implement proper ACLs, and ensure redundancy. These skills align closely with CCNA objectives, particularly in scenario-based labs that involve multiple network segments and layered troubleshooting challenges.
Security and Networking Fundamentals
Network security is a core component of enterprise IT and directly intersects with CCNA knowledge areas. Secure communication, monitoring, and threat prevention are critical for protecting sensitive data and ensuring network integrity. CCNA candidates must understand concepts such as access control lists (ACLs), port security, and traffic filtering to design resilient networks.Exploring secure operational fundamentals exams provides practical guidance on secure network operations. For example, candidates learn how encryption, traffic monitoring, and access policies protect enterprise resources from unauthorized access. Applying these principles in labs allows students to configure ACLs on routers, secure switch ports, and implement VLAN-based segmentation for sensitive traffic flows.
Software Certification and Networking Relevance
Understanding software deployment and certification is vital for maintaining reliable enterprise networks. Many applications, from database platforms to collaborative tools, rely on proper routing, switch configuration, and network segmentation to function optimally. CCNA candidates gain an edge by understanding how software interacts with underlying network infrastructure.Reviewing software certification networking exams teaches candidates how network configurations support application reliability. For example, ensuring smooth communication between clients and servers involves careful IP allocation, proper VLAN assignment, and appropriate firewall rules. Lab exercises that simulate software-dependent networks allow students to troubleshoot performance issues caused by misconfigurations or traffic bottlenecks.
This knowledge also highlights the importance of monitoring and logging. Candidates learn to track application performance, identify anomalies, and correlate software behavior with network conditions. By linking software behavior to network fundamentals, CCNA candidates develop a more comprehensive understanding of enterprise environments, improving both exam readiness and practical troubleshooting skills.
IBLCE Exam Practice Insights
Simulated exams are essential tools for mastering theoretical concepts and applying them in practical scenarios. While the IBLCE focuses on lactation and health certifications, the approach to structured problem-solving mirrors the skills needed for CCNA. Candidates can develop a methodical troubleshooting mindset by analyzing multiple-choice questions and identifying patterns. For example, integrating from IBLCE exam practice test into study sessions helps learners apply reasoning skills effectively, improving accuracy under timed conditions.
Practicing these tests helps CCNA learners understand the importance of logical sequencing and systematic analysis. Just as IBLCE scenarios require step-by-step reasoning for clinical decisions, CCNA lab exercises demand careful analysis of network topologies, packet flows, and configuration errors. Incorporating structured practice exams strengthens problem-solving speed and decision-making confidence, preparing candidates for both lab simulations and theoretical questions.
ISEE Exam Practice Guidance
Using structured exercises allows candidates to strengthen analytical reasoning and problem-solving skills. The ISEE tests critical thinking and quantitative reasoning, which are transferable to networking tasks in CCNA, particularly when working on IP addressing, subnetting, and route optimization. By incorporating the ISEE exam practice test in preparation routines, candidates can hone their ability to analyze complex problems and systematically arrive at solutions.
CCNA learners benefit by applying the same structured approach to network scenarios. For example, calculating subnet sizes or determining efficient routing paths requires logical deduction, similar to solving quantitative questions in the ISEE exam. Practicing these reasoning skills develops precision, reduces errors, and fosters confidence when tackling multi-step challenges in CCNA labs and simulations.
ITBS Exam Practice Strategies
Structured practice tests provide an excellent way to improve pattern recognition, analytical reasoning, and logical problem-solving. While the ITBS is academically focused, the skills developed directly translate to networking scenarios, where recognizing dependencies and relationships is critical. Candidates can practice these strategies effectively using the ITBS exam practice test, which simulates multi-step problem-solving environments that mirror troubleshooting complex network configurations.
For instance, a CCNA candidate analyzing a misconfigured VLAN or a routing loop can apply the same structured reasoning practiced in ITBS scenarios. Identifying patterns, predicting outcomes, and testing hypotheses systematically are crucial skills that improve both exam performance and practical network troubleshooting efficiency.
MACE Exam Practice Preparation
Multi-step exercises help candidates develop systematic problem-solving, critical thinking, and time management skills. The MACE practice tests present scenarios requiring careful analysis and structured decision-making, which is highly relevant to CCNA lab exercises. By using the MACE exam practice test in study routines, candidates learn to approach complex problems step by step, improving their confidence when tackling intricate network setups.
For CCNA preparation, these exercises are particularly useful when configuring multi-router topologies, analyzing packet captures, or resolving ACL conflicts. Practicing with scenario-based exams reinforces methodical troubleshooting and prepares candidates to handle both lab challenges and theoretical exam questions efficiently.
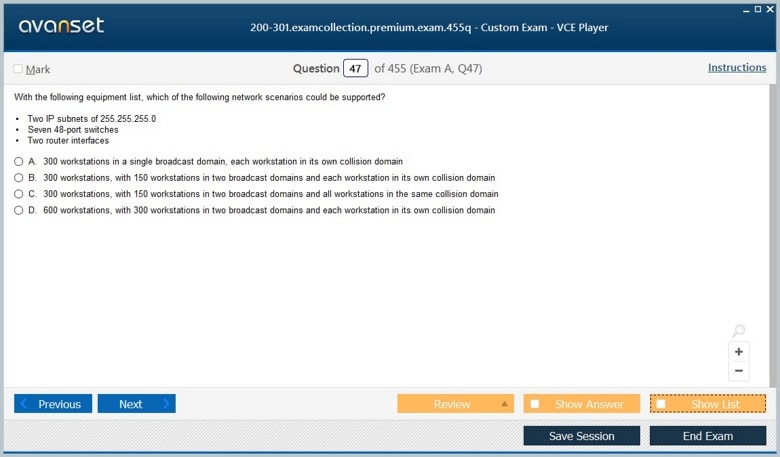
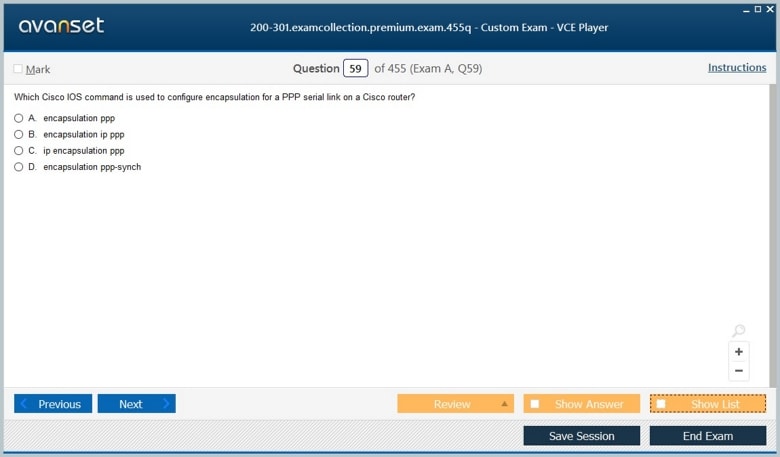
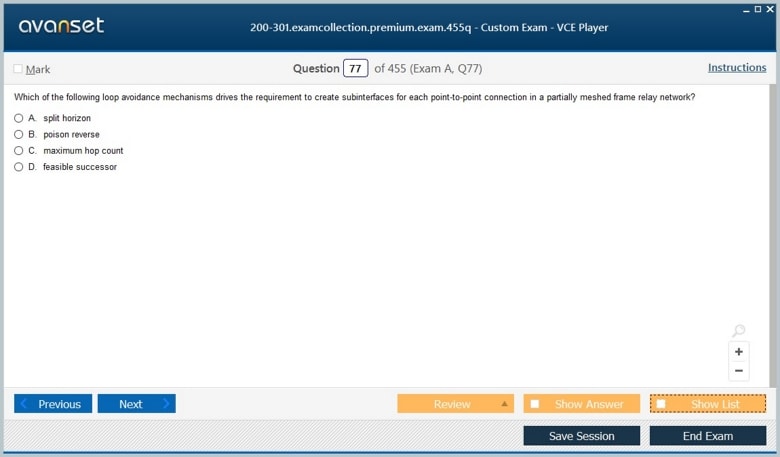
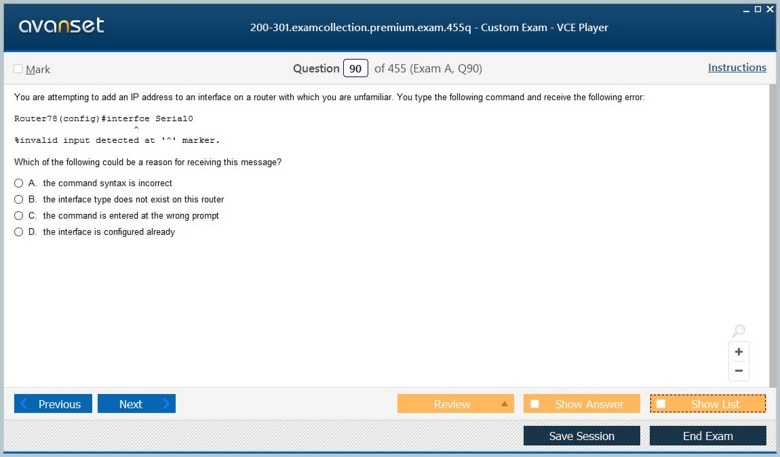
Enhancing Exam Readiness with MCQs Practice
Preparing for the Cisco CCNA exam requires consistent focus and a solid understanding of networking fundamentals. Topics such as IP addressing, routing protocols, VLANs, and subnetting form the backbone of the exam. Students must allocate sufficient time for theory study and practical lab exercises to build strong knowledge retention.Hands-on practice is essential for bridging the gap between theory and real-world application. Lab exercises involving router and switch configurations, troubleshooting connectivity issues, and implementing basic network topologies reinforce theoretical concepts.One of the most effective methods to assess learning is through scenario-based CCNA MCQs practice test. By attempting these questions under timed conditions, candidates can identify weaknesses, simulate exam pressure, and strengthen problem-solving skills in network scenarios.
Following up on practice tests with detailed review and reflection ensures that students understand the reasoning behind each answer. This approach allows learners to refine their knowledge, reinforce lab skills, and develop confidence for the actual exam.
Strategic Study Using NAPLEX Preparation Techniques
Organizing a structured study schedule is critical for CCNA candidates. Breaking the syllabus into smaller, manageable topics, such as routing, switching, and network security, ensures thorough coverage of all exam objectives.Combining multiple learning methods, including video tutorials, textbooks, and lab exercises, helps reinforce understanding. Regular revision of key concepts and flashcards can strengthen memorization of commands, subnetting rules, and protocols.Adopting techniques from timed NAPLEX practice test simulations can improve preparation efficiency. By simulating timed question sessions and reviewing mistakes, candidates can build stronger knowledge retention and approach exam scenarios strategically.Iterative practice, combined with consistent review, ensures learners track their progress effectively. Structured preparation sessions help students retain information, improve problem-solving skills, and remain confident when taking the CCNA exam.
Leveraging Certification for Networking Careers
Beyond CCNA, obtaining multiple certifications strengthens a candidate’s professional profile. It provides industry recognition and expands opportunities in networking careers.Exploring supplementary certification resources enhances understanding of network design, security, and cloud integration. These materials provide exposure to additional tools and real-world network scenarios.Using advanced network certification study resources mid-study allows candidates to practice scenario-based exercises and apply concepts in simulated environments. This integration reinforces CCNA topics while offering industry-relevant insights.Combining these certifications with CCNA study improves practical skills, analytical thinking, and problem-solving abilities. Students gain comprehensive knowledge that benefits both exams and professional networking environments.
Improving CCNA Knowledge with CBDE
Continuous learning is essential to succeed in Cisco exams. Candidates must combine theory, practical labs, and self-assessment to achieve exam readiness.CCNA study requires familiarity with multi-vendor network configurations and troubleshooting practices, preparing students for diverse enterprise networks.Leveraging CBDE network practice exercises helps candidates reinforce knowledge through scenario-based questions. These resources provide real-world simulations, allowing learners to apply concepts in practical setups.Integrating CBDE exercises into daily study routines ensures that learners identify gaps in understanding and strengthen weak areas. Repetition and analysis of mistakes build confidence for exam day.
Reinforcing Skills with CBDH Learning Materials
To fully master CCNA topics, students should combine theory with extensive lab practice. Concepts like routing protocols, subnetting, and VLAN management need repeated exposure.Lab exercises and hands-on practice help learners understand how configurations affect network performance and connectivity, supporting the application of theoretical knowledge.CBDH exam preparation modules are most effective in the study sessions. They provide guided exercises and scenario-based questions that reinforce CCNA learning objectives.Using these resources consistently ensures learners gain both conceptual and practical mastery. Repetition, review, and analysis of scenarios improve problem-solving skills and readiness for the exam.
Enhancing Knowledge Through CBSA Tools
Effective CCNA preparation combines structured study and practical experience. Students need to understand networking protocols, device configurations, and network troubleshooting.Regular hands-on labs and practice exercises help bridge theory and application, enhancing technical comprehension.Introducing CBSA network simulation exercises in the middle of study sessions reinforces learning through scenario-based practice. These exercises strengthen candidate understanding of routing, switching, and network security.Consistent engagement with these tools allows learners to track progress, analyze mistakes, and refine strategies. By integrating simulations with lab practice, candidates improve both confidence and exam readiness.
Integrating BCCPA Practice for Exam Readiness
Practice tests are essential for evaluating understanding and preparing for the CCNA exam. They allow candidates to assess knowledge gaps and improve time management.Combining different types of practice questions, such as multiple-choice and scenario-based items, helps simulate exam conditions and reinforces knowledge.Utilizing BCCPA practice tests for CCNA mid-study provides targeted evaluation opportunities. These highlight weak areas, reinforce learning, and ensure comprehensive preparation.Following up with lab exercises and review sessions ensures candidates internalize concepts. This integrated approach builds strong problem-solving skills and enhances overall readiness for the exam.
Advanced Practice Using BCCPP
Preparing for CCNA exams requires consistent practice and strategic study. Learners must master routing, switching, subnetting, and network security concepts to perform well on theoretical and practical exams.Hands-on labs help students reinforce configurations, troubleshoot network issues, and simulate real-world network environments. Combining theory with practical application builds both confidence and skill.Introducing BCCPP practice tests for Cisco in the middle of study sessions allows candidates to assess understanding of complex networking scenarios. These exercises improve problem-solving skills and help identify knowledge gaps efficiently.Following up with analysis of answers and additional lab practice strengthens retention. Iterative review of questions and solutions ensures that students are fully prepared for both exam and real-world scenarios.
Practical Learning with AD01 Modules
Structured study sessions are crucial for CCNA candidates, particularly when covering advanced topics like OSPF, EIGRP, and VLAN configurations. Breaking topics into smaller modules ensures comprehensive coverage.Students should incorporate hands-on practice alongside theory. Configuring routers, switches, and network devices in labs helps solidify understanding and builds troubleshooting experience.Utilizing AD01 scenario-based exam exercises helps candidates test their knowledge under simulated exam conditions. This approach reinforces key CCNA concepts and improves time management skills.Reviewing practice exercises and analyzing mistakes enables learners to identify weak areas, refine strategies, and gain confidence. This structured repetition supports long-term retention and exam readiness.
Effective Study Through AIE02
Candidates preparing for CCNA should adopt a systematic approach to learning. Core topics such as switching, routing, and network protocols must be studied consistently.
Complementary lab exercises allow students to apply theory in practical scenarios, such as configuring networks and troubleshooting connectivity issues. These activities reinforce comprehension.Introducing AIE02 guided practice modules mid-study ensures that learners engage with scenario-based exercises that replicate exam challenges. This hands-on practice strengthens conceptual understanding and problem-solving.Integrating these modules into study routines ensures consistent progress. Students build confidence, refine technical skills, and are well-prepared for practical and theoretical CCNA exam sections.
Integrating APD01 Exam Preparation Techniques
Efficient preparation for CCNA exams requires both theoretical learning and practical experience. Understanding network topologies, IP addressing, and routing protocols is fundamental.Lab exercises and network simulations help candidates apply concepts practically, improving troubleshooting abilities and retention of critical topics.Using APD01 exam preparation resources allows candidates to engage with scenario-based questions that mimic exam conditions. This enhances familiarity with question formats and time management.Reviewing results and reinforcing weak areas ensures steady improvement. This iterative approach builds both competence and confidence in tackling the CCNA exam successfully.
Building Foundations with JN0-102 Tutorials
Understanding network fundamentals is essential for exam success. CCNA candidates must master basic routing, switching, and VLAN concepts to ensure strong foundations.Hands-on practice in lab environments allows students to apply theoretical concepts and troubleshoot network configurations effectively.Midway through study sessions, JN0-102 Junos network fundamentals tutorials help learners compare Juniper and Cisco networking concepts, enhancing practical knowledge and broadening understanding.Following tutorials with lab exercises ensures knowledge reinforcement. Students gain confidence in configuring and troubleshooting networks while preparing for both exam scenarios and real-world tasks.
Expanding Skills with JN0-103 Junos Associate
Advanced understanding of routing protocols and network configurations strengthens exam readiness. Candidates must combine theory with practice to succeed in CCNA labs.Practical exposure to network setups, VLANs, and routing simulations helps learners internalize concepts. Consistent practice is key for long-term retention.Introducing JN0-103 Junos associate tutorials mid-study allows candidates to explore vendor-specific concepts and integrate them with Cisco knowledge, reinforcing network management skills.Using tutorials alongside lab exercises ensures practical competence. Candidates can troubleshoot complex network scenarios and prepare for real-world applications.
Applying JN0-104 Junos Concepts
CCNA candidates must strengthen configuration and troubleshooting skills to handle real network scenarios efficiently.Simulated labs help students test their understanding of routing, switching, and security protocols, bridging theory and practice.JN0-104 Junos associate tutorials provide practical exercises and lab simulations that reinforce understanding of multi-vendor networking environments.Regularly combining tutorials with lab practice enhances knowledge retention, problem-solving skills, and exam confidence, preparing candidates for both theoretical and practical CCNA assessments.
Strengthening Knowledge Through JN0-105 Tutorials
Advanced network practice strengthens conceptual understanding and practical troubleshooting skills for CCNA candidates.Lab configurations, scenario-based exercises, and repeated practice of subnetting and VLAN setups improve technical proficiency.Incorporating JN0-105 Junos associate tutorials mid-study reinforces practical knowledge and helps students apply networking concepts in simulated enterprise scenarios.Following up with repeated lab exercises ensures mastery of skills, reinforces problem-solving techniques, and builds confidence for exam and professional environments.
Mastering Security with JN0-230 Tutorials
Security is a critical area of CCNA certification. Students must understand ACLs, firewall configurations, and secure network protocols.Lab-based exercises help learners implement security measures, simulate attacks, and analyze network behavior under various conditions.Using JN0-230 security associate tutorials in the middle of study sessions provides targeted exercises on network security practices aligned with CCNA topics.Integrating security tutorials with lab practice ensures that learners can configure, monitor, and troubleshoot networks effectively, building both exam readiness and real-world proficiency.
Advanced Enterprise Skills with JN0-348 Tutorials
Advanced networking knowledge is essential for candidates aiming to design and manage enterprise-level networks. Concepts such as MPLS, BGP, and advanced routing protocols are key.Lab simulations and complex network scenarios help students practice configurations and troubleshoot multi-device networks effectively.Midway through study sessions, JN0-348 Juniper enterprise tutorials reinforce large-scale network concepts, providing exercises that simulate real-world enterprise environments.Consistent practice using these tutorials ensures learners develop strong analytical and problem-solving skills, preparing them for advanced certifications and professional network management roles.
Conclusion
In conclusion, achieving Cisco CCNA certification requires a disciplined approach that combines theoretical knowledge, hands-on practice, and continuous self-assessment. Candidates must develop a solid understanding of networking fundamentals, including IP addressing, routing protocols, switching, VLANs, subnetting, and network security. Consistent practice through scenario-based exercises and mock exams allows learners to identify weaknesses, reinforce their understanding, and build confidence in applying concepts under exam conditions.
Structured study plans are essential for covering the breadth of the CCNA syllabus effectively. Breaking complex topics into smaller, manageable modules, reviewing concepts iteratively, and integrating lab exercises helps learners retain critical information while improving practical skills. Additionally, exposure to multiple network environments and configurations strengthens adaptability, problem-solving, and troubleshooting abilities, which are vital for real-world network management.
Security remains a critical component of network proficiency. Understanding access control, firewall configuration, and secure routing practices prepares candidates to safeguard networks and address potential threats. Combining theoretical study with simulated security scenarios ensures that learners are well-equipped to handle practical challenges in professional environments.
Ultimately, preparing for the CCNA exam is not merely about passing a test; it is about building a comprehensive foundation in networking principles and gaining the practical experience necessary to succeed in enterprise environments. Through disciplined study, repeated practice, and methodical application of networking concepts, candidates can develop the confidence, skills, and professional expertise required to advance their careers and excel in the ever-evolving field of networking.
ExamCollection provides the complete prep materials in vce files format which include Cisco CCNA certification exam dumps, practice test questions and answers, video training course and study guide which help the exam candidates to pass the exams quickly. Fast updates to Cisco CCNA certification exam dumps, practice test questions and accurate answers vce verified by industry experts are taken from the latest pool of questions.
Top Cisco Certification Exams
- 200-301
- 350-401
- 350-701
- 300-410
- 350-601
- 300-715
- 300-710
- 350-501
- 200-901
- 300-415
- 350-801
- 400-007
- 300-420
- 200-201
- 500-220
- 300-620
- 300-425
- 300-730
- 100-150
- 820-605
- 350-201
- 300-815
- 300-510
- 300-430
- 300-435
- 300-440
- 300-515
- 700-805
- 300-445
- 300-720
- 350-901
- 300-610
- 300-725
- 300-635
- 300-630
- 300-615
- 500-445
- 300-220
- 300-215
- 300-820
- 500-420
- 100-140
- 300-745
- 100-160
- 500-470
Site Search:
















i need courses of certification cisco ccna
I was over the moon when I saw my results with 889 points. I decided to learn as many things as possible and study for several weeks to cover the whole topic. It was worth it, because I am a certified IT specialist from now on. Thank you, ExamCollection!
The 200-301 test is very easy when you know the answers to the questions and have learned the topics. And, the best thing is that this bundle can help you with the mastering of your skills.
The premium files in the bundle for the Cisco 200-301 exam are what I used on the ExamCollection website. The VCE emulator that you can get separately will help you to open these files. This is how I used them anyway. I was able to learn various details and evaluate my test-taking skills with the help of the emulator.