Pass Your Cisco CCNP Data Center Certification Easy!
Cisco CCNP Data Center Certification Exams Questions & Answers, Accurate & Verified By IT Experts
Instant Download, Free Fast Updates, 99.6% Pass Rate.

Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
Includes 584 Questions & Answers
$69.99
Download Free CCNP Data Center Practice Test Questions VCE Files
| Exam | Title | Files |
|---|---|---|
Exam 300-610 |
Title Designing Cisco Data Center Infrastructure for Traditional and AI Workloads |
Files 1 |
Exam 300-615 |
Title Troubleshooting Cisco Data Center Infrastructure (DCIT) |
Files 1 |
Exam 300-620 |
Title Implementing Cisco Application Centric Infrastructure (DCACI) |
Files 1 |
Exam 300-635 |
Title Automating Cisco Data Center Solutions (DCAUTO) |
Files 1 |
Exam 350-601 |
Title Implementing and Operating Cisco Data Center Core Technologies (DCCOR) |
Files 2 |
Cisco CCNP Data Center Certification Exam Dumps & Practice Test Questions
Prepare with top-notch Cisco CCNP Data Center certification practice test questions and answers, vce exam dumps, study guide, video training course from ExamCollection. All Cisco CCNP Data Center certification exam dumps & practice test questions and answers are uploaded by users who have passed the exam themselves and formatted them into vce file format.
Mastering Cisco CCNP Data Center: Complete Guide to Core Technologies, Specializations, and Career Growth
The CCNP Data Center certification is a professional-level credential that validates the skills required to implement, operate, and troubleshoot Cisco data center technologies. It is designed for IT professionals who work with enterprise-level data center environments and seek to advance their careers in networking, storage, and automation. Unlike entry-level certifications, CCNP Data Center emphasizes real-world skills and prepares candidates to manage complex infrastructure effectively.
In the modern enterprise landscape, data centers are not only the backbone of business operations but also a hub for massive volumes of data and interconnected systems. This has led to a growing demand for professionals who can design resilient networks, optimize server and storage infrastructure, and implement automation to improve efficiency. The CCNP Data Center certification equips candidates with these capabilities and allows them to demonstrate their expertise to employers.
Importance of the CCNP Data Center Certification
Data centers have evolved dramatically over the past decade. With cloud computing, virtualization, and the Internet of Things generating unprecedented amounts of data, businesses require highly skilled professionals to manage and secure these environments. CCNP Data Center certification provides the knowledge and skills necessary to meet these challenges.
Professionals with this certification gain credibility in areas such as network automation, application-centric infrastructure, and storage networking. It also enhances career prospects by qualifying individuals for roles like Data Center Engineer, Network Architect, and Infrastructure Consultant. Organizations recognize CCNP Data Center-certified professionals as capable of handling the technical complexity and operational demands of modern data centers.
The certification also emphasizes automation and programmability. Candidates learn to leverage intent-based networking and orchestration tools to streamline operations, reduce manual errors, and secure the infrastructure. By mastering these skills, professionals can support scalable and highly available environments while aligning technology with business goals.
CCNP Data Center Exam Structure
Achieving the CCNP Data Center certification requires passing two exams: a core exam and a concentration exam. This structure allows candidates to demonstrate proficiency in foundational technologies as well as specialized areas that align with their career focus.
Core Exam
The core exam is 350-601 DCCOR: Implementing and Operating Cisco Data Center Core Technologies. This exam covers essential data center concepts, including network infrastructure, compute, storage, automation, and security. Candidates are tested on their ability to deploy, manage, and troubleshoot integrated solutions in complex enterprise environments. The core exam lays the foundation for advanced skills and is a prerequisite for the concentration exam.
Concentration Exam Options
Candidates must also choose one concentration exam to complete their certification. The options include:
300-610 DCID: Designing Cisco Data Center Infrastructure
300-615 DCIT: Troubleshooting Cisco Data Center Infrastructure
300-620 DCACI: Implementing Cisco Application Centric Infrastructure
300-625 DCSAN: Implementing Cisco Storage Area Networking
300-635 DCAUTO: Automating and Programming Cisco Data Center Solutions
Selecting a concentration exam allows candidates to specialize in an area aligned with their career goals. For example, professionals interested in automation may choose the DCAUTO exam, while those focused on storage may select the DCSAN exam.
Prerequisites and Recommended Experience
There are no official prerequisites for the CCNP Data Center certification. However, candidates are strongly advised to review exam objectives thoroughly before attempting the exams. Hands-on experience in enterprise networking is highly beneficial. Typically, candidates have three to five years of experience working with data center solutions. This experience allows candidates to understand complex concepts more easily and apply practical solutions during exams.
Familiarity with Cisco technologies such as UCS servers, SAN/NAS storage, and application-centric infrastructure is recommended. Candidates should also have a basic understanding of routing and switching, virtualization, and security principles. While theoretical knowledge is essential, practical experience significantly enhances understanding and exam performance.
Key Skills Tested in CCNP Data Center Exams
The CCNP Data Center certification evaluates a broad range of skills across multiple domains. Candidates must demonstrate proficiency in the following areas:
Networking in Data Centers
Networking is a fundamental aspect of any data center. Candidates are expected to understand Layer 2 and Layer 3 protocols, virtual networking, and routing mechanisms. Key topics include designing and deploying redundant networks, implementing high availability protocols, and configuring scalable network solutions. Mastery of network fundamentals allows candidates to troubleshoot connectivity issues and optimize performance in large-scale data centers.
Compute Infrastructure
Cisco UCS servers and virtualization technologies are essential components of modern data centers. Candidates should understand server architecture, including blade and rack-mounted systems, as well as integration with virtualization platforms. Knowledge of compute infrastructure allows professionals to deploy workloads efficiently, balance resources, and maintain operational consistency across multiple servers.
Storage Networking
Storage is a critical component of enterprise data centers. Candidates are tested on SAN and NAS configurations, storage protocols, and troubleshooting storage networks. Proficiency in storage networking ensures that data is accessible, secure, and resilient. Candidates must understand how to design storage solutions that meet performance and capacity requirements while integrating seamlessly with other infrastructure components.
Automation and Programmability
Modern data centers increasingly rely on automation to reduce manual configuration and improve efficiency. Candidates should have experience with automation tools, APIs, and scripting languages such as Python. Automation skills enable professionals to deploy, configure, and maintain data center resources consistently. Candidates are expected to understand orchestration, workflow automation, and programmability concepts to optimize operations.
Security in Data Centers
Data center security is essential to protect sensitive information and maintain compliance. Candidates must demonstrate knowledge of access control, segmentation, firewall configuration, and policy enforcement. Security skills ensure that data centers remain protected against unauthorized access, cyber threats, and operational vulnerabilities.
Exam Preparation Strategies
Effective preparation begins with selecting quality study materials. Candidates should start by reviewing exam objectives to understand the topics covered. Study resources should include up-to-date guides, instructor-led training, and hands-on labs. Learning from Cisco-certified instructors ensures accuracy and alignment with current exam content.
It is important to focus on both theoretical knowledge and practical application. Candidates should practice configuring networks, deploying servers, and managing storage systems. Access to a lab environment allows candidates to test configurations and troubleshoot real-world scenarios, reinforcing their learning.
Develop a Structured Study Plan
A well-organized study plan is essential for exam success. Candidates should divide study sessions by exam topics and allocate sufficient time for each domain. Starting with foundational topics builds confidence and provides a strong base for more advanced areas.
Minimizing distractions during study sessions is critical. Candidates should avoid multitasking and dedicate focused time to learning. Early and consistent preparation prevents last-minute cramming and ensures thorough understanding of all exam objectives.
Take Detailed Notes
Note-taking is an effective way to reinforce learning and retain critical information. Candidates should summarize key concepts, configurations, and terminology in concise notes. Visual aids such as diagrams and flowcharts can enhance understanding and make complex topics easier to remember.
Reviewing notes regularly ensures that important concepts remain fresh in memory. Candidates should use their notes as a primary resource for revision before the exam. This method allows quick reference to essential information and reduces reliance on lengthy study materials during final preparation.
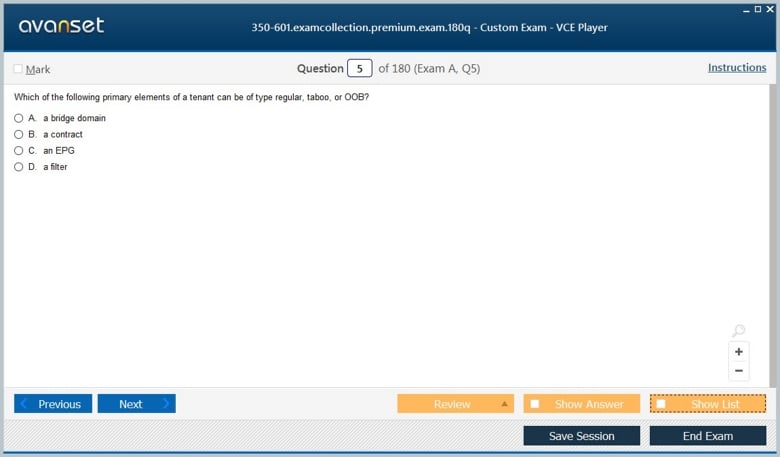
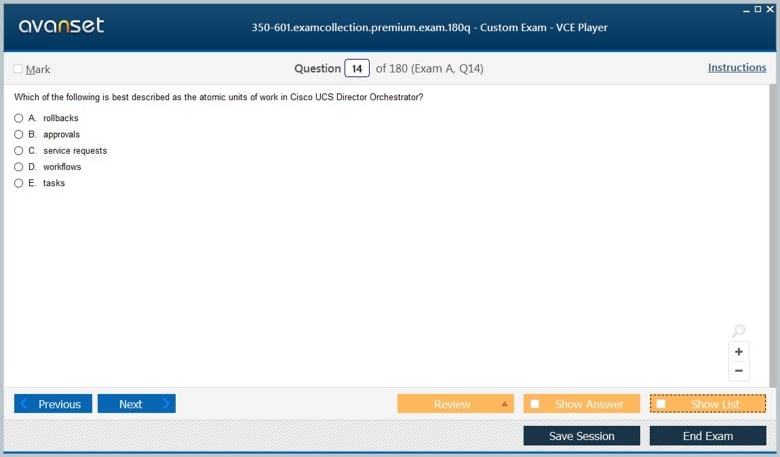
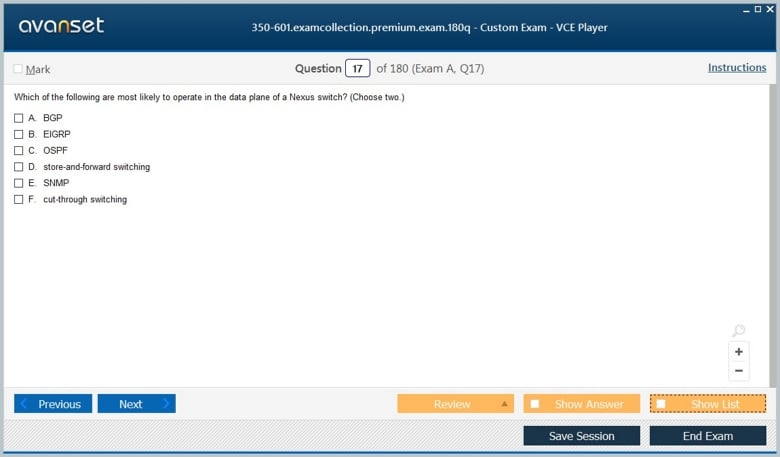
Practice with Sample Tests
Practice exams are invaluable for assessing knowledge and identifying areas that require further study. Candidates should take multiple practice tests under timed conditions to simulate the actual exam environment.
These tests help candidates become familiar with question formats, improve time management, and reinforce understanding of key topics. Analyzing incorrect answers provides insight into weak areas, allowing candidates to focus on improving knowledge before the real exam.
Regularly Review and Refresh
Consistent review is essential to retain knowledge and ensure readiness for the exam. Candidates should revisit notes, practice labs, and challenging topics regularly. Two to three weeks before the exam, intensive revision of all exam objectives helps reinforce understanding and boosts confidence.
Candidates should also practice explaining concepts aloud or teaching them to others. This technique reinforces comprehension and improves the ability to recall information during the exam.
Career Benefits of CCNP Data Center Certification
Achieving the CCNP Data Center certification offers several advantages for IT professionals. Certified individuals are recognized for their advanced skills and expertise in managing data center infrastructure. Employers value these professionals for their ability to implement scalable solutions, optimize performance, and enhance security.
The certification also opens opportunities for higher-level positions, including Data Center Engineer, Network Architect, and Infrastructure Consultant. It provides a competitive advantage in the job market and can lead to increased salary potential. Additionally, CCNP Data Center-certified professionals are better prepared to handle the technical demands of modern enterprise environments, making them valuable assets to organizations.
The CCNP Data Center certification represents a significant milestone for IT professionals seeking to advance in data center technologies. By validating skills in networking, compute, storage, automation, and security, it equips candidates to manage complex enterprise environments effectively.
Success in the certification exams requires thorough preparation, practical experience, and a structured study approach. Candidates should focus on high-quality learning resources, detailed note-taking, regular practice, and consistent review. With dedication and strategic preparation, IT professionals can achieve the CCNP Data Center certification and unlock new career opportunities in the rapidly evolving field of data center technologies.
Deep Dive into Core Technologies for CCNP Data Center
The foundation of CCNP Data Center certification lies in mastering core technologies. Understanding these components thoroughly is essential not only for passing the 350-601 DCCOR exam but also for managing real-world enterprise data centers efficiently. Core technologies include networking, compute, storage, automation, and security, all of which form the backbone of modern data center environments.
Networking Fundamentals in Data Centers
Networking is the backbone of any data center, providing connectivity between servers, storage, and external networks. CCNP Data Center candidates must have a strong grasp of both Layer 2 and Layer 3 networking concepts. Key areas of focus include VLANs, Spanning Tree Protocol, virtual routing and forwarding, and dynamic routing protocols such as OSPF and BGP.
Redundancy and high availability are critical. Data centers must remain operational even if a network component fails. Candidates should understand how to configure link aggregation, EtherChannel, and virtual port channels. They must also know about overlay networks like VXLAN, which allow scalable multi-tenant environments and efficient resource utilization.
Software-defined networking (SDN) is increasingly integral in data centers. SDN abstracts the control plane from the physical infrastructure, enabling centralized management, automation, and faster deployment of network services. Candidates should become familiar with Cisco ACI (Application Centric Infrastructure), which leverages SDN principles to optimize connectivity and policy enforcement.
Compute Infrastructure
Modern data centers rely on unified computing systems to manage server resources efficiently. Cisco UCS (Unified Computing System) is a key technology in this space. Candidates should understand the architecture of UCS servers, including chassis, blades, fabric interconnects, and service profiles.
Virtualization plays a central role in compute infrastructure. Understanding hypervisors, virtual machine deployment, and resource allocation is essential. Candidates should also know how to integrate UCS with virtualization platforms such as VMware vSphere or Microsoft Hyper-V to optimize performance and scalability.
High availability and fault tolerance are crucial in compute design. Candidates should understand redundancy configurations, load balancing, and server failover techniques. Knowledge of server monitoring and management tools allows professionals to proactively address performance issues and ensure operational continuity.
Storage Networking
Data centers generate enormous amounts of data, making storage a critical component. Candidates must understand storage technologies including SAN (Storage Area Network) and NAS (Network Attached Storage). They should be able to configure storage protocols like Fibre Channel, iSCSI, and FCoE to support reliable and high-performance data access.
Storage integration with compute infrastructure is also essential. Candidates should know how to deploy storage resources efficiently, manage capacity, and implement data protection strategies such as replication and backup. Troubleshooting storage connectivity and performance issues is another key skill tested in the CCNP Data Center exams.
Understanding modern storage trends, such as flash storage, hyperconverged infrastructure, and cloud-based storage solutions, is important. These technologies impact how data is stored, accessed, and managed, and candidates should be prepared to work with hybrid environments combining on-premises and cloud resources.
Automation and Programmability
Automation is transforming data center operations by reducing manual configuration and enabling consistent deployments. Candidates should be proficient in using APIs, Python scripting, and orchestration tools to automate routine tasks such as network configuration, server provisioning, and storage management.
Understanding intent-based networking and policy-driven automation is essential. Candidates should be able to define desired outcomes, implement policies, and monitor the environment to ensure compliance. Tools such as Cisco UCS Director and Cisco ACI provide automation frameworks that streamline operations and reduce operational errors.
Programmability skills also include integrating third-party tools and monitoring systems to optimize workflows. Candidates should practice creating scripts that interact with network and compute resources, perform automated checks, and generate reports. Mastery of these skills allows professionals to improve operational efficiency and reliability in modern data centers.
Security in Data Centers
Data center security is critical to protect sensitive data and maintain operational integrity. Candidates should understand security concepts such as access control, segmentation, firewalls, and policy enforcement. Knowledge of role-based access control (RBAC), AAA protocols, and network segmentation is essential.
Security also involves monitoring and compliance. Candidates should be familiar with intrusion detection and prevention systems, logging, and auditing practices. Understanding best practices for securing network devices, servers, and storage ensures that the data center remains protected against internal and external threats.
Implementing secure automation is another important area. Candidates should know how to ensure that automated scripts, policies, and orchestration processes adhere to security standards. This reduces the risk of vulnerabilities and maintains the integrity of automated operations.
Hands-On Lab Experience
Practical experience is crucial for mastering CCNP Data Center concepts. Candidates should work in lab environments to configure networking, compute, storage, and automation solutions. Hands-on practice reinforces theoretical knowledge and prepares candidates for real-world scenarios.
Lab exercises should include configuring VLANs, routing protocols, UCS service profiles, SAN connections, and ACI policies. Candidates should also practice troubleshooting connectivity and performance issues, implementing automation scripts, and validating security configurations.
Simulating real-world scenarios helps candidates develop problem-solving skills and build confidence. Labs allow professionals to test configurations, understand dependencies between components, and explore the impact of design decisions on performance and reliability.
Study and Revision Techniques
Effective preparation requires structured study and consistent revision. Candidates should break down the exam topics into manageable sections and allocate sufficient time for each area. Starting with foundational topics ensures a strong base for more advanced concepts.
Note-taking is an essential strategy. Summarizing key concepts, configurations, and troubleshooting steps in a notebook or digital document allows for quick revision. Visual aids such as diagrams, flowcharts, and tables help in understanding complex topics and retaining information.
Regular practice exams are valuable for assessing knowledge and identifying areas that need improvement. Time-bound simulations familiarize candidates with exam conditions, enhance time management skills, and reduce anxiety on the exam day.
Exam Strategies
Candidates should read all questions carefully and focus on key concepts. Time management is critical; allocate time wisely to ensure all questions are answered. For scenario-based questions, consider the dependencies and relationships between network, compute, and storage components before selecting solutions.
Understanding the exam format helps in anticipating the types of questions and scenarios presented. Candidates should focus on applying practical knowledge rather than memorizing theory, as most exam questions test real-world problem-solving abilities.
Career Impact and Opportunities
Mastering core technologies through CCNP Data Center certification opens several career opportunities. Professionals are well-prepared for roles such as Data Center Engineer, Network Architect, Infrastructure Consultant, and Automation Specialist. Employers value certified individuals for their ability to deploy, manage, and troubleshoot complex data center environments efficiently.
The certification also enhances earning potential and provides a competitive edge in the job market. Organizations are increasingly looking for professionals who can combine technical expertise with automation and programmability skills, and CCNP Data Center certification demonstrates these capabilities.
Core technologies form the foundation of modern data centers. Networking, compute, storage, automation, and security are essential skills that every candidate must master for the CCNP Data Center certification. Hands-on practice, structured study, and focused revision are critical to success.
Understanding these technologies not only prepares candidates for the 350-601 DCCOR exam but also equips them with the skills needed to excel in real-world enterprise environments. Professionals who master these areas can design scalable, efficient, and secure data center solutions, positioning themselves for career growth and success.
Concentration Exam Selection and Focus Areas
After passing the core 350-601 DCCOR exam, CCNP Data Center candidates must choose a concentration exam. The concentration exam allows professionals to specialize in a specific area of interest, such as data center design, troubleshooting, storage, application-centric infrastructure, or automation. Selecting the right concentration exam is critical, as it aligns the certification with your career goals and strengths.
Understanding Your Options
Candidates can select from the following concentration exams:
300-610 DCID: Designing Cisco Data Center Infrastructure
300-615 DCIT: Troubleshooting Cisco Data Center Infrastructure
300-620 DCACI: Implementing Cisco Application Centric Infrastructure
300-625 DCSAN: Implementing Cisco Storage Area Networking
300-635 DCAUTO: Automating and Programming Cisco Data Center Solutions
Each concentration exam focuses on practical application, scenario-based problem solving, and real-world deployment strategies. Understanding the exam objectives and your career goals is the first step in selecting the appropriate path.
Data Center Infrastructure Design (DCID)
The 300-610 DCID exam emphasizes the design and planning of scalable and resilient data centers. Candidates should focus on:
Designing networks for high availability and performance
Planning compute and storage architecture for enterprise environments
Integrating virtualization and cloud solutions
Ensuring disaster recovery and business continuity
Strong design skills ensure that data centers meet performance requirements while remaining flexible for future expansion.
Data Center Troubleshooting (DCIT)
The 300-615 DCIT exam assesses a candidate’s ability to diagnose and resolve problems in complex data center environments. Key areas include:
Identifying network, compute, and storage issues
Using monitoring and diagnostic tools effectively
Resolving configuration errors and performance bottlenecks
Implementing best practices for fault isolation and recovery
Troubleshooting skills are critical in maintaining operational uptime and minimizing the impact of failures on business operations.
Application-Centric Infrastructure (DCACI)
The 300-620 DCACI exam focuses on Cisco’s Application Centric Infrastructure (ACI), an advanced SDN solution. Candidates should understand:
ACI architecture, including fabrics, leaf and spine topology, and policies
Application network profiles and endpoint groups
Implementing multi-site deployments and integration with external networks
Troubleshooting ACI fabric issues
ACI specialization is highly valued in organizations adopting intent-based networking and automation for large-scale environments.
Storage Area Networking (DCSAN)
The 300-625 DCSAN exam targets storage networking, including SAN and NAS solutions. Key topics include:
Configuring Fibre Channel, iSCSI, and FCoE networks
Implementing SAN zoning, multipathing, and redundancy
Integrating storage solutions with servers and virtualization platforms
Troubleshooting storage connectivity and performance issues
Storage expertise ensures reliable data access, optimal performance, and business continuity.
Automating Data Center Solutions (DCAUTO)
The 300-635 DCAUTO exam evaluates skills in automation and programmability, focusing on:
Scripting using Python and other automation tools
Orchestrating network, compute, and storage operations
Implementing policy-driven automation workflows
Integrating automation with monitoring and security systems
Automation specialists are in high demand as organizations adopt modern operational practices to improve efficiency and reliability.
Creating a Study Plan for Concentration Exams
A structured study plan is essential for passing concentration exams. Candidates should:
Review exam objectives thoroughly
Allocate dedicated time to each domain based on strengths and weaknesses
Combine theoretical study with hands-on practice
Include regular revisions and practice exams
Breaking down the syllabus into manageable sections allows candidates to cover all topics effectively while avoiding last-minute cramming.
Hands-On Labs and Practical Experience
Practical experience is crucial for concentration exams. Candidates should use lab environments to simulate real-world scenarios. For example:
DCID candidates can practice designing network topologies and compute/storage layouts
DCIT candidates should troubleshoot network, server, and storage issues
DCACI candidates can configure ACI fabrics and endpoint groups
DCSAN candidates should configure SAN/NAS networks and storage integration
DCAUTO candidates can develop scripts and workflows for automated operations
Hands-on labs not only reinforce theoretical knowledge but also build confidence for scenario-based questions.
Practice Questions and Simulations
Practice questions help candidates identify knowledge gaps and improve problem-solving skills. Scenario-based simulations are particularly useful for concentration exams because they mimic real-world situations. Candidates should:
Attempt multiple practice exams under timed conditions
Analyze incorrect answers to understand mistakes
Focus on weak areas while continuing to reinforce strengths
Practice applying concepts rather than memorizing solutions
Regular practice ensures familiarity with the exam structure and reduces anxiety on test day.
Advanced Study Techniques
Candidates preparing for concentration exams can use several advanced study techniques:
Mind Mapping: Visualizing concepts and their relationships can help with retention
Flashcards: Use for key terminology, commands, and protocols
Peer Discussions: Explaining concepts to others reinforces understanding
Scenario Analysis: Solve hypothetical problems to simulate exam scenarios
Incremental Revision: Review topics periodically rather than all at once
Combining these techniques improves knowledge retention and ensures readiness for complex questions.
Time Management Strategies
Managing study time effectively is critical. Candidates should:
Set a daily study schedule and stick to it
Allocate more time to weaker topics
Include breaks to prevent burnout
Track progress to adjust the study plan as needed
Time management ensures comprehensive coverage of all exam objectives and reduces stress.
Exam-Day Preparation
Preparation on the day of the exam is just as important as prior study. Candidates should:
Ensure adequate rest before the exam
Eat a healthy meal to maintain energy
Review key notes or diagrams briefly, avoiding heavy studying
Arrive early at the test center or set up a quiet environment for online exams
Stay calm and focus on understanding questions before answering
Confidence and composure contribute significantly to exam performance.
Integrating Core and Concentration Knowledge
Success in the CCNP Data Center certification requires integrating knowledge from both the core and concentration exams. Candidates should:
Apply core networking, compute, storage, and security concepts in concentration scenarios
Use automation and orchestration where applicable
Understand dependencies between different infrastructure components
Solve problems using a holistic approach
This integrated understanding ensures that professionals can handle complex data center challenges in real-world environments.
Career Opportunities with Concentration Specialization
Selecting a concentration allows candidates to pursue specialized roles, such as:
Network Designer or Architect (DCID)
Data Center Troubleshooting Engineer (DCIT)
ACI Specialist (DCACI)
Storage Network Engineer (DCSAN)
Automation and Orchestration Specialist (DCAUTO)
Specialization enhances career prospects and aligns certification with industry demand.
Advanced Troubleshooting in Data Centers
Troubleshooting is an essential skill for data center professionals. Complex environments involving networking, compute, storage, and automation components can fail for multiple reasons. The CCNP Data Center certification emphasizes not only theoretical knowledge but also the ability to identify, analyze, and resolve issues efficiently.
Troubleshooting Network Infrastructure
Network failures are among the most common issues in data centers. Candidates should understand:
Diagnosing connectivity issues at Layer 2 and Layer 3
Using ping, traceroute, and network monitoring tools to isolate faults
Identifying configuration mismatches, VLAN misconfigurations, or spanning tree issues
Troubleshooting routing protocols like OSPF, EIGRP, and BGP
Effective troubleshooting also involves understanding redundancy and high-availability configurations. Candidates should be able to determine whether link aggregation, virtual port channels, or redundant paths are causing the issue.
Compute Troubleshooting
Compute resources can experience failures due to hardware, virtualization, or configuration errors. Candidates should focus on:
Monitoring server health using UCS Manager or equivalent tools
Diagnosing failed blades, chassis, or fabric interconnects
Troubleshooting virtual machine deployment issues and resource allocation conflicts
Identifying hypervisor errors or misconfigurations that affect performance
Being able to analyze logs and system reports is crucial for resolving compute-related issues promptly.
Storage Troubleshooting
Storage problems can disrupt business-critical applications. Candidates should understand:
Diagnosing SAN and NAS connectivity issues
Identifying multipath failures and implementing failover solutions
Troubleshooting performance issues in Fibre Channel, iSCSI, or FCoE networks
Validating storage integration with virtualization and compute environments
Storage troubleshooting often involves coordinating between network, compute, and storage teams, making communication and documentation skills essential.
Automation Troubleshooting
Automation can streamline operations, but it also introduces unique challenges. Candidates should know how to:
Debug Python scripts or automation workflows
Identify failed API calls and connectivity errors
Monitor orchestration tools to ensure policies are applied correctly
Implement error handling in automation scripts to prevent system disruption
Proficiency in troubleshooting automation ensures continuous operational efficiency and reduces the risk of outages caused by misconfigured scripts.
Scenario-Based Troubleshooting Practice
Lab practice is crucial for mastering troubleshooting skills. Candidates should:
Simulate real-world network, compute, and storage failures
Practice root cause analysis for complex issues
Document solutions to reinforce understanding
Perform end-to-end troubleshooting, considering interactions between components
Scenario-based labs prepare candidates for concentration exams and real-world job responsibilities, where problems often involve multiple layers of infrastructure.
Advanced Study Techniques for Concentration Exams
Beyond core concepts, concentration exams require advanced study strategies. Candidates should:
Break down complex topics into smaller, manageable sections
Use diagrams and flowcharts to visualize relationships between systems
Create case studies based on lab simulations for practical understanding
Regularly revise both theory and hands-on configurations
These techniques improve retention and enhance problem-solving skills in exam scenarios.
Integrating Core and Concentration Knowledge
Successful candidates integrate knowledge from the core 350-601 DCCOR exam with their chosen concentration exam. Integration involves:
Applying networking, compute, and storage fundamentals to specialized tasks
Leveraging automation and programmability to optimize solutions
Using troubleshooting methodologies across multiple infrastructure layers
Developing comprehensive solutions that consider interdependencies
Integration ensures that professionals are prepared for complex scenarios and practical tasks in real-world environments.
Practice Tests and Simulation Exams
Practice tests are invaluable for assessing readiness. Candidates should:
Attempt timed simulations to mimic real exam conditions
Focus on scenario-based questions that test critical thinking
Analyze mistakes to identify knowledge gaps
Use simulation tools to practice configuration, troubleshooting, and automation tasks
Regular practice improves confidence, reinforces concepts, and ensures familiarity with exam structure.
Exam Preparation and Time Management
Effective exam preparation includes structured study schedules and time management strategies:
Allocate daily or weekly study blocks for different topics
Focus on weaker areas without neglecting strong areas
Include hands-on lab practice in the study plan
Practice time-bound exams to improve pacing
Time management ensures all exam objectives are covered and helps candidates remain calm during testing.
Leveraging Documentation and Notes
Creating detailed notes and documentation is key for exam success. Candidates should:
Summarize commands, configurations, and troubleshooting steps
Use diagrams to represent network and storage topologies
Maintain a separate section for automation scripts and workflows
Review notes regularly to reinforce memory
Effective documentation allows for quick revision and helps candidates recall critical concepts during exams.
Real-World Application of Skills
CCNP Data Center certification is not only an exam credential; it reflects practical skills applied in real environments. Certified professionals are expected to:
Troubleshoot complex network, compute, and storage issues
Automate repetitive tasks for operational efficiency
Implement secure and scalable data center designs
Collaborate across teams to ensure seamless operations
Practical application of skills ensures value to employers and readiness for advanced responsibilities.
Career Advancement Opportunities
Mastering advanced troubleshooting, automation, and concentration skills opens doors to senior-level roles, such as:
Data Center Operations Engineer
Network and Infrastructure Architect
Automation and Orchestration Specialist
Storage and SAN Consultant
These roles require technical expertise, problem-solving skills, and the ability to implement enterprise-level solutions, making CCNP Data Center certification highly valuable.
Soft Skills for Data Center Professionals
Technical skills alone are not enough. Candidates should develop soft skills including:
Communication: Explaining complex issues clearly to stakeholders
Collaboration: Working effectively across teams in large-scale environments
Problem-Solving: Approaching challenges methodically and creatively
Adaptability: Learning and implementing new technologies quickly
Soft skills complement technical expertise and enhance overall career potential.
Final Exam Strategies
To maximize performance on the exam, candidates should:
Read all questions carefully before answering
Focus on scenario analysis for practical questions
Manage time effectively to complete all sections
Remain calm and confident, relying on hands-on experience
Confidence, preparation, and clear thinking are critical for successfully passing both the core and concentration exams.
Final Preparation for CCNP Data Center Exams
Preparing for the CCNP Data Center exams requires a combination of knowledge, practical skills, and strategic study methods. By the time candidates reach this stage, they should have completed their core and concentration exam studies and be ready for final review and reinforcement.
Review Core and Concentration Exam Objectives
A thorough review of exam objectives ensures that no area is overlooked. Candidates should:
Revisit all topics in the 350-601 DCCOR exam
Review the chosen concentration exam objectives, whether design, troubleshooting, ACI, storage, or automation
Focus on areas of weakness identified during practice tests
Ensure familiarity with scenario-based questions and practical configurations
Understanding the relationship between core technologies and specialized topics helps in solving integrated scenarios efficiently.
Comprehensive Revision Techniques
Effective revision is crucial to retain information and reinforce understanding. Recommended techniques include:
Creating summary notes for key concepts, commands, and configurations
Developing visual diagrams for network, compute, and storage topologies
Practicing troubleshooting scenarios repeatedly in labs
Using flashcards for terminology, protocols, and automation commands
Revision should be incremental, allowing candidates to revisit topics multiple times rather than cramming at the last minute.
Hands-On Lab Practice
Practical experience is essential for both core and concentration exams. Candidates should:
Configure networks, servers, and storage in a lab environment
Simulate real-world scenarios to test troubleshooting skills
Implement automation scripts and orchestration workflows
Validate configurations and monitor system behavior under different conditions
Hands-on labs bridge the gap between theoretical knowledge and practical application, boosting confidence and problem-solving ability.
Practice Exams and Simulations
Practice exams are effective for assessing readiness and identifying knowledge gaps. Candidates should:
Take multiple timed practice tests to simulate exam conditions
Focus on scenario-based questions requiring critical thinking
Analyze incorrect answers to understand the underlying concepts
Adjust study plans based on performance results
Regular practice exams help familiarize candidates with the exam format and improve time management during testing.
Time Management Strategies
Effective time management ensures that all exam objectives are covered while minimizing stress. Candidates should:
Allocate specific time blocks for each topic in their study plan
Prioritize weaker areas without neglecting strengths
Include time for hands-on lab exercises, revision, and practice exams
Avoid last-minute cramming to maintain mental clarity
Good time management allows candidates to study efficiently and approach the exam with confidence.
Exam-Day Preparation
Being well-prepared on the day of the exam is as important as prior study. Candidates should:
Ensure adequate rest the night before the exam
Eat a nutritious meal to maintain energy
Arrive early at the test center or prepare a quiet environment for online exams
Review key notes briefly without overloading the brain
Stay calm and focused, reading all questions carefully
Confidence and composure on exam day contribute significantly to performance.
Troubleshooting Real-World Scenarios
Candidates should apply knowledge from both core and concentration exams to troubleshoot integrated scenarios. This involves:
Analyzing complex network, compute, and storage issues
Applying automation and orchestration to resolve problems efficiently
Considering interdependencies between infrastructure components
Documenting solutions and lessons learned for future reference
Scenario-based thinking prepares candidates for real-world challenges and exam questions alike.
Integrating Automation and Security Skills
Automation and security are increasingly critical in modern data centers. Candidates should:
Use automation scripts and orchestration tools to streamline repetitive tasks
Implement policy-driven automation for network, compute, and storage
Apply security best practices in configuration and deployment
Monitor compliance and performance continuously
Integration of these skills ensures efficient, secure, and scalable operations.
Professional Development and Career Growth
CCNP Data Center certification opens doors to advanced career opportunities. Professionals can pursue roles such as:
Data Center Engineer or Architect
Network Automation Specialist
Storage and SAN Consultant
ACI Implementation Specialist
Infrastructure Orchestration Expert
Certification demonstrates expertise in designing, deploying, and managing complex data center solutions, enhancing professional credibility and marketability.
Continuous Learning and Skill Enhancement
The IT landscape evolves rapidly, and continuous learning is essential. Professionals should:
Stay updated with emerging data center technologies and trends
Explore cloud integration, hybrid environments, and next-generation networking
Enhance programming and automation skills to keep pace with modern operations
Participate in forums, webinars, and professional networks to share knowledge
Continuous learning ensures long-term career growth and relevance in the industry.
Soft Skills for Career Advancement
Technical proficiency alone is insufficient for career growth. Professionals should cultivate:
Effective communication to explain complex solutions to stakeholders
Collaboration and teamwork in multi-disciplinary projects
Problem-solving and analytical thinking to address challenges creatively
Adaptability to implement new technologies and methodologies quickly
Soft skills complement technical expertise, enhancing leadership potential and career progression.
Leveraging Certification for Professional Recognition
CCNP Data Center certification serves as a mark of professional competence. Benefits include:
Recognition by employers for technical proficiency and hands-on skills
Increased opportunities for promotions and specialized roles
Validation of expertise in high-demand areas such as automation, ACI, and storage
Competitive advantage in the job market
The certification demonstrates a commitment to professional development and technical excellence.
Maintaining Certification and Continuing Education
Certification maintenance is important to remain current. Candidates should:
Track recertification requirements and exam updates
Participate in ongoing training programs and advanced certifications
Apply learned skills in practical projects to reinforce knowledge
Stay engaged with Cisco’s technology community for updates and best practices
Active maintenance ensures that professionals remain relevant and capable in evolving data center environments.
Final Exam Strategies
To maximize success on the exam, candidates should:
Focus on understanding concepts rather than rote memorization
Approach scenario-based questions methodically, considering all dependencies
Manage time efficiently, prioritizing questions based on complexity
Use hands-on experience to guide decision-making in practical questions
A calm, focused approach combined with thorough preparation increases the likelihood of achieving a high score.
CCNP Data Center certification represents mastery of core technologies, concentration specialization, and advanced operational skills. Success requires structured study, hands-on practice, scenario-based learning, and integration of automation and security expertise.
Professionals who earn this certification are equipped to design, deploy, and manage complex data center environments efficiently. The combination of technical proficiency, troubleshooting skills, automation knowledge, and soft skills positions certified individuals for advanced career opportunities and long-term success in the rapidly evolving IT industry.
Investing in preparation, applying knowledge practically, and maintaining continuous learning ensures that professionals not only pass the exams but excel as highly skilled data center specialists.
CCNP Data Center Certification: Comprehensive Summary
The CCNP Data Center certification is designed for IT professionals seeking expertise in designing, implementing, and managing modern data center environments. It validates advanced skills across networking, compute, storage, automation, and security, preparing candidates for professional-level roles in enterprise IT.
Core Exam and Concentration Path
The certification requires passing a core exam (350-601 DCCOR: Implementing and Operating Cisco Data Center Core Technologies) and one concentration exam of choice. Concentration exams include:
DCID: Designing Data Center Infrastructure
DCIT: Troubleshooting Data Center Infrastructure
DCACI: Implementing Application-Centric Infrastructure
DCSAN: Implementing Storage Area Networking
DCAUTO: Automating and Programming Data Center Solutions
The core exam ensures a strong foundation in data center technologies, while the concentration exam allows specialization aligned with career goals.
Key Knowledge Areas
Candidates gain proficiency in multiple domains:
Networking: Layer 2 and Layer 3 design, routing protocols, redundancy, and high-availability solutions.
Compute: Server deployment, virtualization, UCS management, and troubleshooting.
Storage: SAN/NAS configurations, Fibre Channel, iSCSI, and storage integration with virtualization.
Automation and Orchestration: Scripting, API usage, workflow automation, and policy-driven operations.
Security: Implementing access control, segmentation, and compliance within data center environments.
Exam Preparation Strategies
Effective preparation involves:
Structured Study Plans: Allocating time to core and concentration topics.
Hands-On Labs: Practicing configuration, troubleshooting, and automation in simulated environments.
Practice Tests and Simulations: Scenario-based exercises to reinforce learning and build confidence.
Revision and Notes: Summarizing key concepts, commands, and workflows for quick review.
Time Management: Balancing study sessions, lab practice, and revision efficiently.
Troubleshooting and Real-World Skills
Candidates develop advanced troubleshooting abilities to address complex issues across networking, compute, and storage layers. Scenario-based practice enhances problem-solving skills, preparing professionals for real-world enterprise environments.
Career Advancement and Opportunities
Certification opens doors to specialized and senior-level roles, such as:
Data Center Engineer or Architect
Network Automation Specialist
Storage/SAN Consultant
ACI Implementation Specialist
Infrastructure Orchestration Expert
These roles require both technical proficiency and soft skills like communication, collaboration, and problem-solving, all of which are emphasized throughout the certification process.
Automation and Future-Readiness
Automation and programmability are integral in modern data centers. Candidates learn to:
Streamline operations using scripts and orchestration tools
Apply policy-driven workflows across compute, storage, and network layers
Enhance operational efficiency and reduce human error
Integrate automation with security and monitoring
Mastery of automation positions professionals for emerging trends in intent-based networking and intelligent data centers.
Final Exam Strategies and Mindset
Success on the exams requires:
Thorough understanding of concepts rather than rote memorization
Scenario-based problem-solving using practical experience
Efficient time management during study and on exam day
Confidence and calmness while approaching questions
A combination of preparation, hands-on practice, and strategic thinking ensures readiness and high performance.
Continuous Learning and Certification Maintenance
To remain relevant, certified professionals should:
Stay updated with emerging technologies and trends
Participate in ongoing training, webinars, and professional networks
Apply skills in practical projects and real-world environments
Maintain certification through recertification and continuous skill enhancement
Continuous learning ensures long-term career growth and relevance in rapidly evolving IT environments.
Conclusion
The CCNP Data Center certification equips IT professionals with the knowledge, practical skills, and problem-solving abilities needed to excel in complex data center environments. From mastering core technologies to specializing in concentration areas and implementing automation, candidates emerge as highly skilled, future-ready professionals.
By combining theoretical understanding, hands-on practice, strategic exam preparation, and continuous learning, CCNP Data Center certified individuals are well-positioned for career advancement, leadership opportunities, and success in modern enterprise IT infrastructure management.
ExamCollection provides the complete prep materials in vce files format which include Cisco CCNP Data Center certification exam dumps, practice test questions and answers, video training course and study guide which help the exam candidates to pass the exams quickly. Fast updates to Cisco CCNP Data Center certification exam dumps, practice test questions and accurate answers vce verified by industry experts are taken from the latest pool of questions.
Cisco CCNP Data Center Video Courses
Top Cisco Certification Exams
- 200-301
- 350-401
- 350-701
- 300-410
- 350-601
- 300-715
- 300-710
- 400-007
- 200-901
- 350-501
- 350-801
- 300-420
- 300-415
- 200-201
- 300-620
- 500-220
- 300-425
- 300-730
- 350-201
- 100-150
- 820-605
- 300-815
- 300-510
- 300-430
- 300-435
- 300-515
- 300-440
- 300-445
- 700-805
- 300-720
- 350-901
- 300-725
- 300-610
- 300-630
- 300-615
- 300-635
- 300-220
- 300-215
- 500-445
- 100-140
- 100-160
- 500-470
- 300-820
- 500-420
- 300-745
Site Search: