- Home
- Popular IT Certifications
- How to Troubleshoot VLANs & Trunking
How to troubleshoot VLANs & trunking
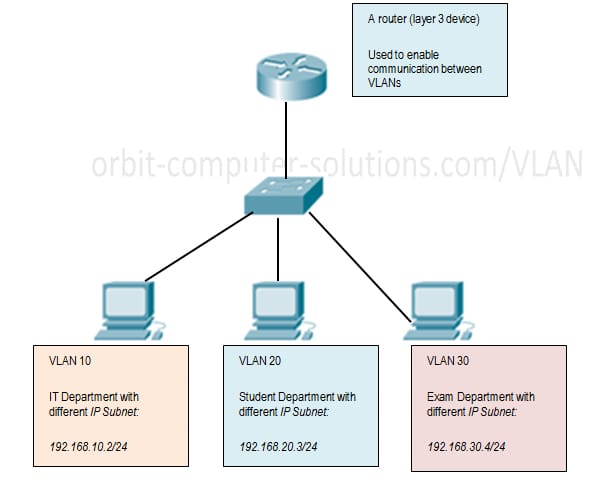
VLAN (Virtual Local Area Network) is usually a rationally different IP sub network which enables numerous IP sites in addition to subnets to exist for the same-switched community. VLAN is a reasonable send out site which could course numerous actual physical LAN portions. This can be a modern approach directors configure changes straight into electronic local-area sites (VLANs) to boost community overall performance through splitting huge layers to send out names into smaller types.
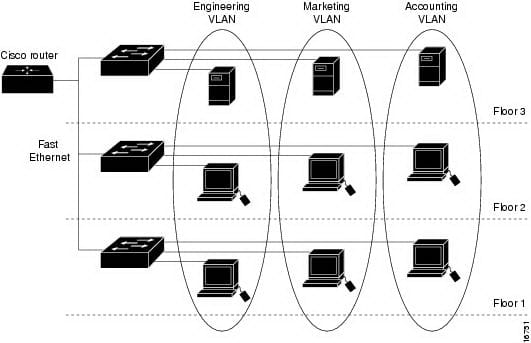
By making use of VLAN, a community manager should be able to team in concert programs through reasonable functionality, or through apps, without having regard to actual physical place from the users. Just about every VLAN functions as being a different LAN in addition to ranges a number of changes. This will give number of gadgets to become as long as they have been for a passing community section. Pertaining to targeted traffic to maneuver concerning VLANs, a coating 3 gadget (router) becomes necessary.
Working of VLAN
The operation provides enhanced scenarios and from now on covers over several buildings. An original circle is identical, however places of work and also business units desktops are disseminate over several buildings. Your places of work can continue to being a passing bottom and other departments' for the other flooring and buildings.
Even so, this circle owner desires to ensure each of the workplace desktops discuss identical protection functions and also bandwidth controls. Building a significant LAN and also electrical wiring every division collectively will amount to a massive activity and also won't possibly be uncomplicated with regards to handling the circle.
This specific VLAN transferring will come and simply group places of work and also business units using the means of people, and undoubtedly simpler to manage their protection and bandwidth requirement. Selecting the turned VLAN will allow this circle owner to make teams of logically networked equipment that will work as should they are on their own impartial circle, whether or not these people discuss a typical facilities having some other VLANs. Once you configure the VLAN, you are able to identify the idea to describe the principal purpose in the people with the VLAN.
Access Ports
Login to the account on website through the use of web host location. Once you are logged in and have seen your current bank account, verify your present IP address by considering the top left-hand option on the web site. You ought to view word of which flows "Logged With Because: (your user name here)" and "Current IP: (your ip address here)" Currently see a Hosts/Redirects web site and press "manage" Your present web host list really should seem plus the IP address to the web host you're attempting to accomplish really should match the actual IP address you're logged in via. When you go to a diverse IP address for ones hostname in comparison with whatever you count on, that's going to stop a person via setting up a connection to of which web host. If you're not necessarily nevertheless managing our own No-IP DUC computer software to help trail your current IP address, you should set it up today.
Should the correct IP address has found inside your bank account, the following thing to check is should the DNS server is coming back the right IP address any time staying wanted of which information. The best way to check this specific is to use the actual NSLOOKUP demand from the critical windows. Start demand line windows (terminal in Linux products, DOS field in Glass windows computers), and form this: nslookup.
VLAN database
Setup changes within CatOS tend to be prepared to help NVRAM once an alteration is done. As opposed, Cisco IOS Computer software doesn't preserve construction changes to help NVRAM if you don't clear this duplicate running-config. VTP buyer as well as server systems need VTP updates from other VTP servers to promptly end up saving within NVRAM without user involvement. The VTP update needs tend to be satisfied with the default CatOS operation, however the Cisco IOS update model needs a different update operation.
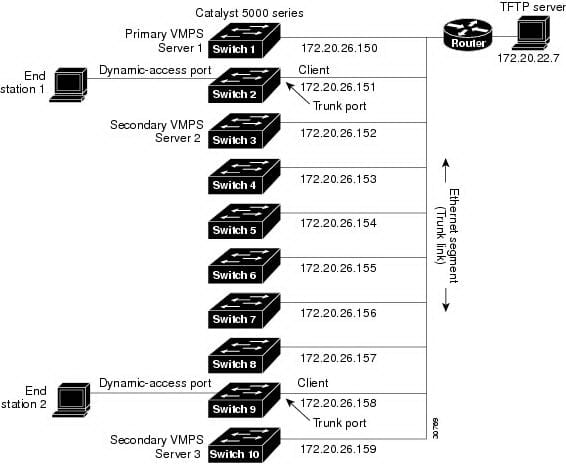
Due to this change, some sort of VLAN database ended up being launched in to Cisco IOS Computer software since a solution to promptly preserve VTP updates intended for VTP consumers as well as servers. In a few variants involving software program, this VLAN database is actually by means of an outside record within NVRAM, known as VLAN. You can view VTP/VLAN data that is saved within the vlan.dat and need to declare this VTP buyer or maybe VTP server when you analyze this display reputation. VTP server/client method changes don't preserve the full VTP/VLAN construction to the new venture config record within the NVRAM when you problem this duplicate running-config about these kinds of systems.
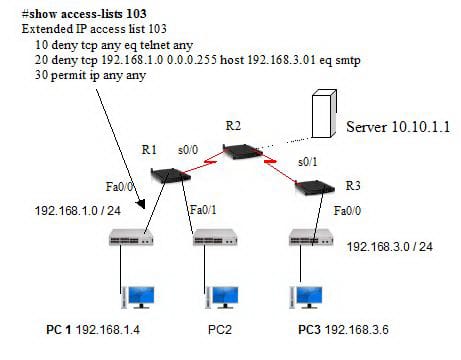
Normal, Extended VLAN and Voice VLAN
Some sort of VLAN is often a turned system that is logically segmented simply by perform, task group, or maybe program, devoid of consider to the actual locations in the consumers. VLANs have the same qualities since actual LANs, however you may class end areas regardless of whether they are not necessarily bodily situated on the same LAN message. Virtually any change dock may remain in some sort of VLAN, as well as uncast, transmitted and multicast packets are usually forwarded as well as flooded just to end areas inside the VLAN. Each VLAN is known as some sort of plausible system, as well as packets destined pertaining to areas that do not necessarily remain in the actual VLAN has to be forwarded by way of a router or maybe link since revealed throughout Physique 11-1. Just because a VLAN is known as some other plausible system, its content has a unique link Management Data Base (MIB) info and may support a unique execution connected with spanning woods. View "Configuring STP" as well as "Configuring RSTP as well as MSTP inches.
The actual Driver 3550 change sustains 1005 VLANs throughout VTP client, server, as well as translucent methods. VLANs are usually recognized having a range by 1 to help 4094. VLAN IDs 1002 by means of 1005 are usually set-aside pertaining to Expression Wedding ring as well as FDDI VLANs. VTP only learns normal-range VLANs, together with VLAN IDs 1 to help 1005; VLAN IDs in excess of 1005 are usually extended-range VLANs and are not necessarily saved inside the VLAN data source. The actual change has to be throughout VTP translucent setting whenever you produce VLAN IDs by 1006 to help 4094.
The actual change sustains per-VLAN spanning woods as well as per-VLAN fast spanning woods together with at the most 128 spanning-tree instances. One particular spanning-tree occasion is usually permitted each VLAN. Understand the "Normal-Range VLAN Setting Guidelines" part to read more regarding the quantity of spanning-tree instances as well as the quantity of VLANs. The actual change sustains both equally Inter-Switch Hyperlink (ISL) as well as IEEE 802. 1Q trunking options for giving VLAN traffic more than Ethernet ports.
VTPv1, VTPv2, VTPv3, VTP pruning
A new Move in VTP Server manner will constantly engage in transmitting along with obtaining VTP and synchronizing the VTP information document regardless of edition and a new move in VTP Client manner will constantly engage in VTP information document synchronization regardless of edition. A new change in VTP v1 see through Mode will not send, obtain VTP information or maybe engage in document synchronization.
A new change in VTP v2 See-through Mode will probably send, obtain VTP information, although doesn't engage in VTP document synchronization. Really the only setting it does not cross VTP packets is really a change set up in VTPv1 See-through Mode along with VTPv3 in away from manner.
Intended for VTPv3, the variation is quite a bit better. VTPv3 offers a number of processes: server, customer, see-through along with away from. The actual variation in between see-through along with away from may be the end of contract involving acquired VTP announcements instead of relaying all of them. Together with VTP edition 3, away from manner can be set up globally or maybe on each vent (for instance trunk) starting. The actual away from manner has been recently merely readily available with Feline OS. The actual setting involving away from by using an interface will probably apply at almost all VTP circumstances.
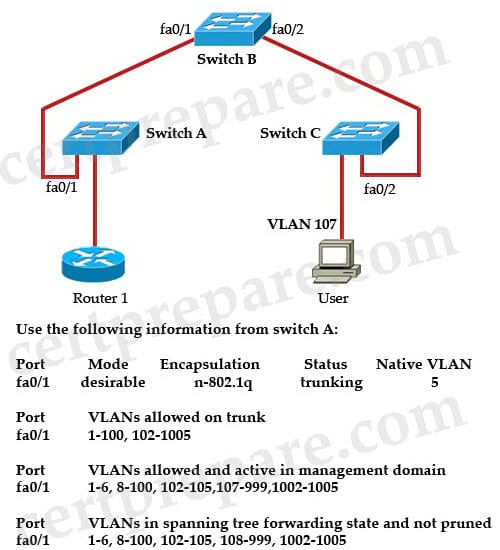
Dot1Q
Whenever establishing some sort of connection, the port has to be enabled in both knobs. We all will configure fa0/1 as being a shoe hyperlink in both Move A new in addition to Move W. I am accomplishing this via Cisco's packet tracer plan in a couple of Cisco 2950 knobs. Automatically just about all VLANs are allowed to end up being been given in addition to dispatched around shoe hyperlinks, this really is changed and will be reviewed afterwards.
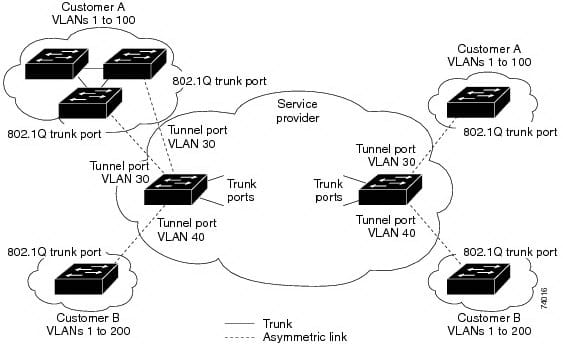
While using the 802.1Q tunneling attribute, carrier's networks can use an individual VLAN to aid consumers who have multiple VLANs. Buyer VLAN IDs are maintained in addition to targeted visitors via unique consumers is usually segregated inside the service-provider facilities regardless if they appear to be on the same VLAN. The 802.1Q tunneling grows VLAN space by using a VLAN-in-VLAN pecking order in addition to marking the tagged packets. A new port constructed to aid 802. 1Q tunneling is named some sort of tube port. When you configure tunneling, you allocate some sort of tube port to a VLAN that may be focused on tunneling. Each and every client takes a distinct VLAN, yet in which VLAN supports every one of the consumer's VLANs.
Native VLAN
While setting up 802. 1Q tunneling on a border move, you must employ 802.1Q trunk area locations with regard to sending out packets into your service-provider community. Even so, packets under-going the actual core from the service-provider community might be carried as a result of 802. 1Q trunks, ISL trunks, as well as non-trunking back links. While 802.1Q trunks are widely-used within these kinds of core turns, the actual local VLANs from the 802. 1Q trunks should not complement any local VLAN from the non-trunking (tunneling) slot about the same move due to the fact site visitors about the local VLAN wouldn't normally become marked about the 802.1Q sending trunk area slot.
Observe VLAN which is actually configured because local VLAN for the 802.1Q trunk area slot via ingress border move inside service-provider community (Switch 2). Move 1 regarding Buyer The communicates any marked box with VLAN 25 for the ingress canal slot regarding Move a couple of inside service-provider community, which connected to access VLAN forty. Since the gain access to VLAN from the canal slot (VLAN 40) is the same as the actual local VLAN from the border move trunk area slot (VLAN 40), the actual neighborhood label is not combined with marked packets gotten in the canal slot. The actual box holds only the actual VLAN 25 label through the service-provider community for the trunk area slot from the egress border move (Switch 3) and it is misdirected through the egress move canal slot to be able to Buyer M.
These are generally a few approaches to fix this matter:
- Use ISL trunks concerning core turns inside service-provider community. While client interfaces connected to border turns must be 802. 1Q trunks, we all suggest making use of ISL trunks to plug turns inside core coating.
- Ensure that the local VLAN IDENTIFICATION about the border move trunk area slot is not inside the client VLAN range. As an example, if the trunk area slot holds site visitors regarding VLANs 100 to be able to two hundred, delegate the actual local VLAN many external of which range.
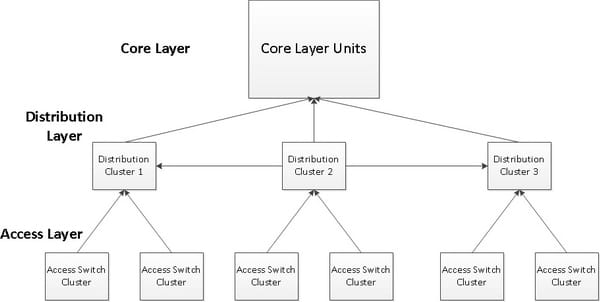
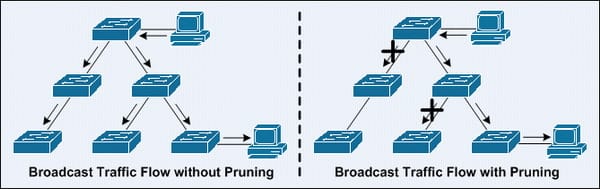
Manual Pruning
Pruning can be minimizing bombarded targeted visitors by uplinks - which often perform in the event of the targeted visitors can be pruned about sender area, which will be the submission coating. And so shifting this pruning towards accessibility Stratum can make good sense.
Exactly what may make good sense is to carry out this pruning about equally attributes:
- Reduces bombarded targeted visitors
- Fewer SPT-Instances about Access-Switch
- Easier Troubleshooting: If the VLAN cannot work using a Access-Switch, you do not have in order to SSH upon a different (Distribution-) Transition to determine whether it will get pruned. However: - In the event that minimizing SPT-Instances is often a worry to suit your needs, I might recommend people look into Numerous Spanning-Tree (MST).
- Without a doubt employ VTP, recommended is to make use of its handiest as well as less hazardous feature: VTP pruning. The actual having manual pruning can be IMHO the only justification regarding making use of VTP at all (unless obviously VAN pruning can be component of one's security principle, this cannot be done with VTP pruning).
Site Search:






