- Home
- Popular IT Certifications
- Troubleshooting for IPv6 Addressing & Subnetting
Describe troubleshoot for IPv6 addressing and subnetting
The principal thing that ought to be said about Ipv6 subnetting is that an alternate mode of thought is called for. In Ipv4 you generally ponder what number of locations you have accessible and how you can allot enough of them to each one end client. In Ipv6 you typically consider what number of (/64) subnets you have accessible and how you can dispense them to end clients. You just about never stress over what number of IP locations will be utilized as a part of a given subnet. Aside from some uncommon cases like point to point interfaces, every subnet simply essentially has way a larger number of locations accessible than it will ever oblige, so all things being equal you stress just over designating subnets, not has inside them. Ipv6 subnets are typically/64 in light of the fact that that is needed in place for SLAAC (stateless location auto configuration) to work. Indeed where SLAAC is not being used, there may be different motivations to utilize/64. For instance, there may be some end client gadgets out there that simply accept/64, or else directing subnets longer than/64 may be wasteful on a few switches on the grounds that the switch practitioner has enhanced the instance of/64 or shorter courses to spare steering table memory.
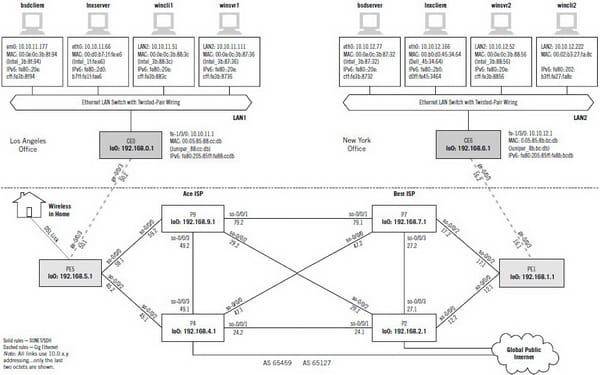
Various network sizes for an IPv6 Subnet
From a low level point of view, how tending to and directing works, the prefix length has the same significance in Ipv6 and Ipv4. On that level, you can make a relationship, for example, "an Ipv4/16 uses a large portion of the bits for the system location and a large portion of the bits for the host address that is similar to a/64 in Ipv6". At the same time this correlation is not by any means able. Solid traditions have developed in Ipv6 which make the divisions of system sizes look sort of additional like the old universe of classful systems in Ipv4. Undoubtedly, Ipv6 didn't reintroduce classful tending to in which the most noteworthy few bits of the location compel a specific net mask, however what Ipv6 has is sure [defacto/conventionally] standard system sizes:
/64: the essential size of a solitary subnet: LAN, WAN, square of locations for web virtual hosts, and so forth... "Ordinary" subnets are never anticipated that will be any littler (longer prefix) than/64. No subnets are ever anticipated that will be bigger (shorter prefix) than/64 since a/64's value of host locations is path more than we can envision requiring.
/56: a square of 256 essential subnets. Despite the fact that current approaches grant Isps to pass out pieces as huge as/48 to each end client and still consider their location use generally defended, a few ISPS may (and as of now do) decide to apportion a/56 to customer grade clients as a tradeoff between assignment bunches of subnets for them and location economy.
/48: a square of 65536 essential subnets and the prescribed size of piece that each ISP client end site ought to get.
/32: the default size of square that most ISPS will get each one time they ask for more addresses from a provincial location registry.
Inside administration supplier and enterprise systems, a lot of people more prefix lengths than these 4 might be seen. At the point when taking a gander at the directing tables of switches inside these systems, Ipv4 and Ipv6 have much in as something to be shared including the greater part of the way steering works: courses for more prefixes override covering courses for shorter prefixes, so it is conceivable to total (make shorter) and bore down (make longer) courses. Like in Ipv4, courses might be amassed or abridged to larger obstructs with shorter prefixes to minimize the measure of steering tables.
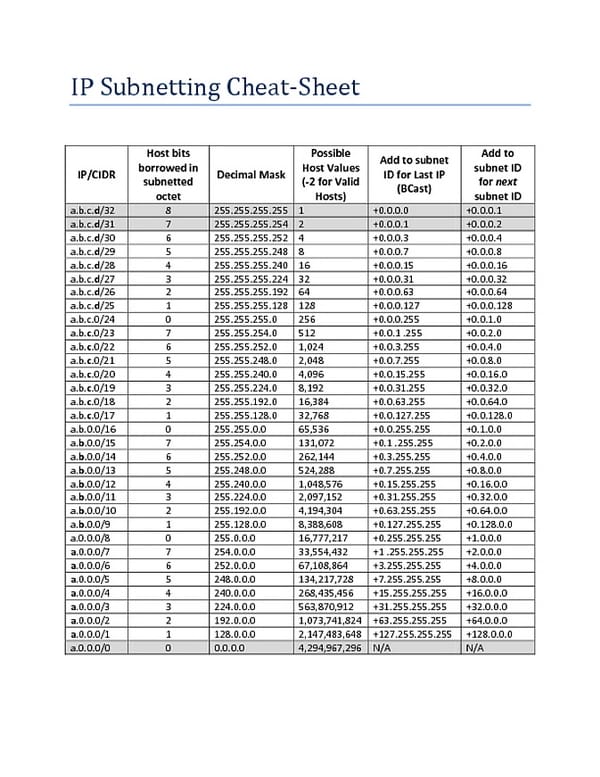
Unicast
Much the same as Ipv4 you can isolate the Ipv6 location space utilizing the high-request bits that don't as of now have an appointed quality to make subnetted location prefixes. Since Ipv6 has such a large number of more addresses accessible, 18,446,744,073,709,551,616 to be somewhat more particular, that is 18 quintillion, 446 quadrillion, 744 trillion, 73, billion, 709 million, 551 thousand and 616 fair in the event that you're checking, there are a couple of alternatives. I'm certain you get the thought, yet the genuine purpose of it is every one of those locations make a ton more choices and a ton more adaptability for making an Ipv6 tending to arrange so you may need to be contemplating how you could update you current Ipv4 tending to want to exploit some of these capacities.
Making an Ipv6 tending to arrange is to some degree closely resembling making an Active Directory OU structure. You can make a subnet arrange by geographic area having an alternate essential subnets for every area to encourage switch enhancement. You may make essential subnets by use sort, for example, Engineering and Accounting which makes it less demanding to oversee security and approaches, you may utilize a consolidation of both or concoct something totally distinctive. That is one of the profits of having each one of those extra addresses in Ipv6.
EUI-64
Amplified Unique Identifier (EUI), according to Rfc2373, permits a host to allot iteslf a novel 64-Bit IP Version 6 interface identifier (EUI-64). This gimmick is a key profit over Ipv4 as it kills the need of manual arrangement or DHCP as in the realm of Ipv4. The Ipv6 EUI-64 configuration location is gotten through the 48-bit MAC address. The Mac location is initially differentiated into two 24-bits, with one being OUI (Organizationally Unique Identifier) and the other being NIC particular. The 16-bit 0xfffe is then embedded between these two 24-bits to for the 64-bit EUI address. IEEE has picked FFFE as a held quality which can just show up in EUI-64 created from the EUI-48 MAC address.
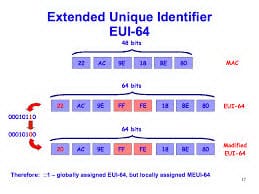
Next, the seventh bit from the left, or the all inclusive/neighborhood (U/L) bit, needs to be upset. This bit distinguishes whether this interface identifier is generally or mainly directed. On the off chance that 0, the location is generally controlled and if 1, the location is all inclusive interesting. It is worth recognizing that in the OUI bit, the all around interesting locations doled out by the IEEE has dependably been set to 0 while the mainly made locations has 1 designed. Consequently, when the bit is modified, it keeps up its unique degree (worldwide remarkable location is still worldwide novel and the other way around).
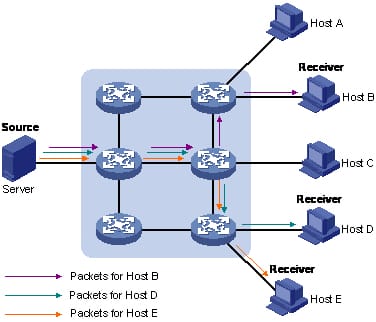
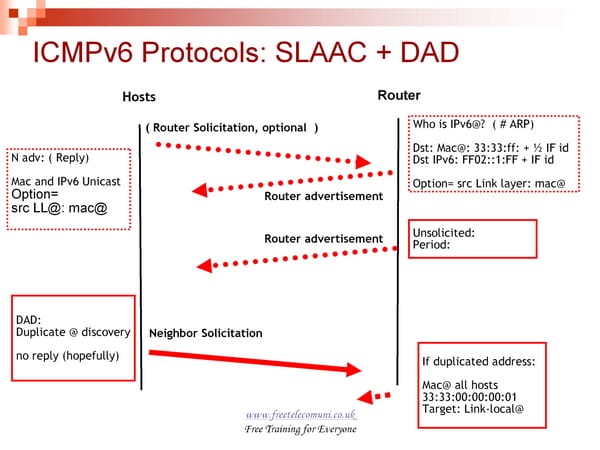
ND, RS/RA
A truly slick aspect concerning Ipv6 is that is can design itself even without the utilization of DHCP! By utilizing a methodology of switch revelation, which includes a trade of Router Solicitation and Router Advertisement messages, the host figures out which system to use to get an Ipv6 address and the locations of neighboring switches, extra stateless locations, on-connection prefixes, and other arrangement parameters.
Included in the Router Advertisement message are banners that demonstrate whether a location arrangement convention, (for example, Dhcpv6) ought to be utilized for extra setup. The host chooses which system to utilize focused around the design of a Router Advertisement message. Join residential locations constantly created paying little heed to some other choices. Ipv6 hosts are continually listening for Ra's. Furthermore a host will ask for a RA by sending a Router Solicitation when the host's setup progressions (Power-up, Network Configuration Change). A RA is normally sent by a Layer 3 gadget and has particular alternatives accessible. RA's control both tending to and directing on the host is an important aspect.
Autoconfig (SLAAC)
SLAAC is a standout amongst the most critical parts of Ipv6. It will be key to arrangements of substantial quantities of IP telephones, sensors, keen Tvs, associated Mp3 players, machines in a home system, and so on. You know, the "Web of Things". SLAAC is not all that appropriate to hubs like a PC in a corporate system, where things, for example, grouping of IP addresses inside a "/64" by authoritative gathering, and midway oversaw IP locations are important. SLAAC is inalienably a decentralized instrument (dissimilar to Dhcpv4 in Ipv4). The subnet switches send Router Advertisement messages, and the inward hubs self-rousingly create worldwide locations focused around that data. No focal hub is included in that era separated from supplying the prefixes substantial in the subnet. The switch has no clue about what addresses every hub has created (and no basic approach to find that out). That is the reason it is "stateless" - no "state" (concentrated data, kept over a long time of time) is kept up by the switches.
No Dhcpv6 server is needed for SLAAC to happen, yet SLAAC can illuminate hubs that a Dhcpv6 server is accessible, from which it can get stateless data, (for example, Ipv6 locations of DNS) and (if the Dhcpv6 server helps "stateful" operation), from which the hub can likewise get a halfway oversaw worldwide Ipv6 Unicast deliver notwithstanding the address (es) it has produced with SLAAC. A wellspring of Router Advertisement messages is not an immediate trade for a DHCP server in light of the fact that SLAAC is stateless - it doesn't deal with a pool of locations - it gives the data needed to every hub to self-sufficiently make one or more substantial worldwide Ipv6 addresses.
DHCP relay and server
The Dynamic Host Configuration Protocol (DHCP) is based on a customer server model, in which a customer sends an arrangement solicitation and afterward the server gives back an answer to send design parameters, (for example, IP address, subnet veil, and passage) to the customer. The solicitation and answer messages are both typified utilizing UDP. With the ip address dhcp-alloc charge executed, an interface does not show a DHCP-DISCOVER message instantly; rather, it arbitrarily telecasts it inside 10 seconds. The DHCP customer continues sending appeals until it gets an answer from a DHCP server.
After the customer gets the DHCP-ACK message, it will test whether the IP location doled out by the server is being used by TV an unwarranted ARP bundle. On the off chance that the IP location is being used, the customer sends a DHCP-DECLINE message to the server and solicitations an IP address once more. In the event that the allotted IP location is on the same subnet as some other interface's IP address on the DHCP customer, the DHCP customer not one or the other uses the IP address nor asks for once more.
DHCP protocol operations
Element Host Configuration Protocol is utilized by machines for asking for Internet Protocol parameters, for example, an IP address from a system server. The convention works focused around the customer server model. DHCP is extremely normal in all present day networks running in size from home systems to huge facilities systems and territorial Internet administration supplier systems. Most private system switches get an all around extraordinary IP address inside the supplier system. Inside a neighborhood system, DHCP allots a nearby IP location to gadgets associated with the neighborhood system.
At the point when a machine or other arranged gadget unites with a system, its DHCP customer programming in the working framework sends a show question asking for important data. Any DHCP server on the system may benefit the appeal. The DHCP server deals with a pool of IP addresses and data about customer setup parameters, for example, default door, area name, the name servers, and time servers. On accepting an ask for, the server may react with particular data for every customer, as at one time designed by an executive, or with a particular location and some other data legitimate for the whole system, and the time period for which the distribution (lease) is substantial. A host regularly questions for this data promptly in the wake of booting, and occasionally from that point before the termination of the data. At the point when a task is revived by the customer machine, it at first demands the same parameter values however may be allotted another location from the server, in view of the task approaches set by executives.
On expansive systems that comprise of numerous connections, a solitary DHCP server may benefit the whole system when helped by DHCP hand-off operators found on the interconnecting switches. Such operators hand-off messages between DHCP customers and DHCP servers found on distinctive subnets.
Site Search:






