- Home
- Popular IT Certifications
- Device Management and Troubleshooting
How to troubleshoot device management
The device management provides an approach to consistently inform all applications and framework gimmicks of changes that may influence their operation or access to assets. Applications and the framework utilize and process gadget occasions to exploit new assets when they get to be accessible and to avoid loss of information when existing assets get to be distracted.
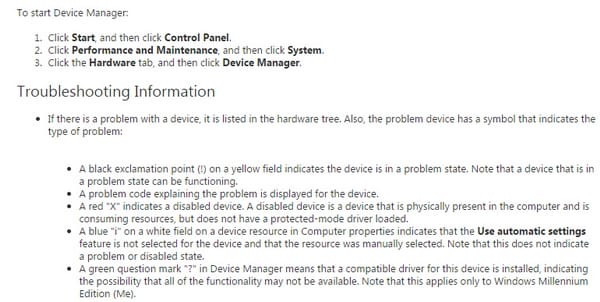
The Device Manager is a Control Panel applet in Microsoft Windows working frameworks. It permits clients to view and control the fittings joined to the machine. At the point when a bit of equipment is not meeting expectations, the culpable fittings are highlighted for the client to manage. The rundown of equipment might be sorted by different criteria.
Here is how the device management can be troubleshooter;
Console and VTY
A Console Television is a kind of CRT TV most prominent in, however not selective to, the United States of America. Console CRT TVs are recognized from standard CRT TVs by their plant constructed, non-removable, wooden cupboards and speakers, which structure a fundamental piece of the TV's design. Some models incorporated a peculiarity whereby the viewer/administrator could answer the phone, by pressing a particular catch on the remote control, and could then move ahead to take part in a phone discussion by method for a speakerphone incorporated with the bureau of the TV, in this manner killing the need to utilize a conventional phone receiver. Console TVs were initially suited in roughly rectangular radiogram style cupboards and included radio and phonograph offices. However from roughly the mid-1970s onwards, as radiograms diminished and Hi-fi gear expanded in fame, comfort TVs got to be more cuboid fit as a fiddle and contained most regularly TV, and radio accepting gimmicks, and less ordinarily the expansion of an eight track player.
YTV is a Canadian English-dialect Category A link and satellite TV forte station that is possessed by Corus Entertainment. Its programming comprises of unique real life and vivified TV arrangement, motion pictures, and outsider programming from the USA link channel Nickelodeon and different wholesalers. YTV works two time-moved bolsters, running on Eastern and Pacific Time Zone plans. It is accessible in excess of 11 million Canadian family units starting 2013.
The "YTV" moniker was initially thought by a few viewers to be a truncation for "Youth Television"; be that as it may, the station's site has denied this, in spite of the way that the system initially marked itself as a young system at dispatch.
Telnet, HTTP, HTTPS, SSH, SCP
Here is the information about them;
Telnet:
Telnet is a system convention utilized on the Internet or neighborhood to give a bidirectional intelligent content situated correspondence office utilizing a virtual terminal association. Client information is blended in-band with Telnet control data in an 8-bit byte arranged information association over the Transmission Control Protocol (TCP). Telnet was created in 1968 starting with RFC 15, stretched out in RFC 854, and institutionalized as Internet Engineering Task Force (IETF) Internet Standard STD 8, one of the first Internet models. Generally, Telnet gave access to an order line interface (normally, of a working framework) on a remote host. Most system gear and working frameworks with a TCP/IP stack help a Telnet administration for remote arrangement (counting frameworks focused around Windows NT). Notwithstanding, on account of genuine security issues when utilizing Telnet over an open system, for example, the Internet, its utilization for this reason has disappeared significantly for SSH.
The term telnet might likewise allude to the product that actualizes the customer piece of the convention. Telnet customer applications are accessible for basically all machine stages. Telnet is additionally utilized as a verb. To telnet intends to create an association with the Telnet convention, either with summon line customer or with an automatic interface. Case in point, a typical order may be: "To change your secret word, telnet to the server, log in and run the past charge." Most regularly, a client will be telnet ting to an Unix-like server framework or a system gadget, (for example, a switch) and acquiring a login brief to a summon line content interface or a character-based full-screen manager. All information octets aside from 0xff are transmitted over the TCP transport as seems to be. Subsequently, a Telnet customer application might likewise be utilized to secure an intelligent crude TCP session, and it is normally accepted that such session which does not utilize the IAC (0xff, or 255 in decimal) is practically identical. This is not the situation, notwithstanding, on the grounds that there are other system virtual terminal (NVT) guidelines, for example, the necessity for an uncovered carriage return character (CR, ASCII 13) to be trailed by a NUL (ASCII 0) character, that recognize the telnet convention from crude TCP sessions. On the other hand, numerous frameworks now have genuine crude TCP customers, for example, net cat or scat on UNIX and Putty on Windows, which additionally could be utilized to physically "talk" to different administrations without specific customer programming. In any case, Telnet is still off and on again utilized as a part of debugging system administrations, for example, SMTP, IRC, HTTP, FTP or Pop3 servers, to issue summons to a server and look at the reactions, however of all these conventions just FTP truly utilizes Telnet information form. An alternate distinction of Telnet from a crude TCP session is that Telnet is not 8-bit clean as a matter of course. 8-bit mode may be arranged, yet high-bit-set octets may be jumbled until this mode was asked for, and it clearly won't be asked for in non-Telnet association. The 8-bit mode (so named double choice) is proposed to transmit parallel information, not characters however. The standard recommends the elucidation of codes 0000-0176 as ASCII, yet does not offer any significance for high-bit-set information octets
HTTP:
It is an application convention for dispersed, collective, hypermedia data systems. HTTP is the establishment of information correspondence for the World Wide Web. Hypertext is organized content that uses legitimate connections (hyperlinks) between hubs containing content. HTTP is the convention to trade or exchange hypertext. HTTP works as a solicitation reaction convention in the customer server figuring model. A web program, for instance, may be the customer and an application running on a machine facilitating a site may be the server. The customer submits a HTTP solicitation message to the server. The server, which gives assets, for example, HTML records and other substance, or performs different capacities in the interest of the customer, gives back a reaction message to the customer. The reaction contains consummation status data about the solicitation and may additionally contain asked for substance in its message body.
A web program is a sample of a client operator (UA). Different sorts of client operator incorporate the indexing programming utilized via look suppliers (web crawlers), voice programs, portable applications, and other programming that gets to, devours, or showcases web content. HTTP is intended to allow moderate system components to enhance or empower interchanges in the middle of customers and servers. High-movement sites regularly profit from web reserve servers that convey content in the interest of upstream servers to enhance reaction time. Web programs store a while ago got to web assets and reuse them when conceivable to diminish system movement. HTTP substitute servers at private system limits can encourage correspondence for customers without a universally routable location, by handing-off messages with outer servers. HTTP is an application layer convention planned inside the structure of the Internet Protocol Suite. Its definition presumes an underlying and dependable transport layer protocol, and Transmission Control Protocol (TCP) is usually utilized. HTTP assets are distinguished and placed on the system by Uniform Resource Identifiers (Uris)-or, all the more particularly, Uniform Resource Locators (URLS)-utilizing the http or https URI plans.
HTTPS:
It is a correspondences convention for secure correspondence over a machine system, with particularly wide organization on the Internet. In fact, it is not a convention all by itself; rather, it is the aftereffect of basically layering the Hypertext Transfer Protocol (HTTP) on top of the SSL/TLS convention, along these lines including the security abilities of SSL/TLS to standard HTTP correspondences. The primary inspiration for HTTPS is to forestall wiretapping and man-in-the-center assaults.
The security of HTTPS is along these lines that of the underlying TLS, which uses long haul open and mystery keys to trade a transient session key to scramble the information stream in the middle of customer and server. An imperative property in this connection is immaculate forward mystery (PFS), so the fleeting session key can't be inferred from the long haul awry mystery key; in any case, PFS is not generally adopted.
Truly, HTTPS associations were principally utilized for installment transactions on the World Wide Web, email and for touchy transactions in corporate data frameworks. In the late 2000s and early 2010s, HTTPS started to see far reaching utilization for securing page genuineness on different sorts of sites, securing records and keeping client correspondences, personality and web perusing private.
SSH:
It is a cryptographic system convention for secure information correspondence, remote order line login, remote summon execution, and other secure system benefits between two organized machines. It joins, by means of a protected channel over a shaky system, a server and a customer running SSH server and SSH customer programs, respectively. The convention determination recognizes two significant forms that are alluded to as SSH-1 and SSH-2.
The best-known application of the convention is for access to shell accounts on Unix-like working frameworks, however it can likewise be utilized within a comparative design for records on Windows. It was planned as a trade for Telnet and other unstable remote shell conventions, for example, the Berkeley rsh and rexec conventions, which send data, quite passwords, in plaintext, rendering them helpless to capture and divulgence utilizing bundle analysis. The encryption utilized by SSH is proposed to give uprightness of information over an unsecured system, for example, the Internet. SSH utilizes open key cryptography to verify the remote machine and permit it to confirm the client, if necessary. There are a few approaches to utilize SSH; one is to utilize naturally created open private key sets to just scramble a system association, and after that utilization secret key confirmation to log on. An alternate is to utilize a physically created open private key pair to perform the verification, permitting clients or projects to log in without needing to define a secret word. In this situation, anybody can create a matching pair of distinctive keys (open and private). The general population key is set on all machines that must permit access to the manager of the matching private key (the holder keeps the private key mystery). While confirmation is focused around the private key, the key itself is never exchanged through the system amid validation. SSH just checks whether the same individual offering general society key likewise possesses the matching private key. In all renditions of SSH it is essential to confirm obscure open keys, i.e. partner people in general keys with characters, before tolerating them as legitimate. Tolerating an aggressor's open key without approval will approve an unapproved assailant as a legitimate client.
SCP:
The SCP convention is a system convention, in light of the BSD RCP protocol, which backings record exchanges between hosts on a system. SCP uses Secure Shell (SSH) for information exchange and uses the same systems for verification, in this way guaranteeing the validness of the information in travel. A customer can send (transfer) documents to a server, alternatively including their fundamental qualities (authorizations, timestamps). Customers can likewise ask for documents or registries from a server (download). SCP runs over TCP port 22 as a matter of course. Like RCP, there is no RFC that characterizes the specifics of the convention.
(T)FTP:
It is a standard system convention used to exchange machine records starting with one host then onto the next host over a TCP-based system, for example, the Internet. FTP is based on a customer server structural planning and uses separate control and information associations between the customer and the server. FTP clients may validate themselves utilizing an agreeable content sign-in convention, regularly as a username and secret word, yet can interface namelessly if the server is arranged to permit it. For secure transmission that secures the username and secret key, and encodes the substance, FTP is frequently secured with SSL/TLS (FTPS). SSH File Transfer Protocol (SFTP) is frequently likewise utilized rather, yet is mechanically diverse. The primary FTP customer applications were summon line applications created before working frameworks had graphical client interfaces, regardless are sent with most Windows, Unix, and Linux working systems. Many FTP customers and mechanization utilities have following been produced for desktops, servers, cell phones, and equipment, and FTP has been consolidated into benefit applications, for example, Web page editors.
Site Search:






