- Home
- Popular IT Certifications
- Ethernet Networks: Tech & Media Access Control
What are the technologies and media access control method for Ethernet networks?
Ethernet is used in our daily life every day. No matter whether we are at office or at home, we must use the Ethernet cable and must know about the media access control methods for the networks which deal with the Ethernet cable's usage. Following is some information about what Ethernet is and how it works.
The term Ethernet alludes to the family of LAN products secured by the IEEE 802.3 standard that characterizes what is ordinarily known as the CSMA/CD protocol. The Ethernet standard has developed to create some new innovations as Machine systems administration has developed, yet the mechanics of operation for each Ethernet organize today come from Metcalfe's unique outline. The first Ethernet depicted correspondence over a solitary link imparted by all gadgets on the system. When a gadget appended to this link, it had the capacity to correspond with another connected gadget. This permits the system to grow to oblige new gadgets without obliging any adjustment to those gadgets effectively on the system. Three information rates are at present characterized for operation over twisted cables and optical fibers:
- 10 Mbps-10base-T Ethernet
- 100 Mbps-Fast Ethernet
- 1000 Mbps-Gigabit Ethernet
Different advances and protocols have been developed as likely substitutions, yet the markets have talked. Ethernet is one of the major LAN innovations (it is presently utilized for pretty nearly 85 percent of the world's LAN-associated Pcs and workstations) in light of the fact that its protocol has the accompanying attributes:
- It is easily understandable, maintainable, and implementable.
- Permits easy system executions
- It has broad topological adaptability for network establishment
- Ensures some useful interconnection and the operations of some standard complaints products, no matter who their makers are.
The first Ethernet was created as a trial coaxial link network in the 1970s by Xerox Corporation to work with an information rate of 3 Mbps utilizing CSMA/CD protocols for the LANS with sporadic yet infrequently overwhelming traffic prerequisites. Accomplishment with that extend got some good amount of attraction which was needed and hence it led to 1980 joint improvement of the 10-Mbps Ethernet Version 1.0 detail by the three-organization consortium: Digital Equipment Corporation, Intel Corporation, and Xerox Corporation.
The first IEEE 802.3 standard was focused around, and was fundamentally the same as, the Ethernet Version 1.0 determination. The draft standard was endorsed by the 802.3 working gathering in 1983 and was therefore distributed as an authority standard in 1985 (ANSI/IEEE Std. 802.3-1985). From that point forward, various supplements to the standard have been characterized to exploit changes in the innovations and to help extra system media and higher information rate abilities, in addition to a few new discretionary system access control characteristics.
Ethernet Networks Structures and the Topologies:
The two conceivable topologies for Ethernet are bus and star.
The bus topology is the least difficult (and the protocol) topology. Standard Ethernet (10base5) and Thin Ethernet (10base2), both focused around urge link frameworks, utilize the bus. In this one-link LAN, all workstations are joined in progression (a "bus" game plan) on a solitary link. All transmissions go to all the joined workstations. Every workstation then chooses the transmissions it ought to get focused around the location data contained in the transmission.
In a star topology, all appended workstations are wired specifically to a focal center that secures, keeps up, and softens associations between them (up the occasion of a mistake). The focal point of a star topology is that it's not difficult to disengage an issue hub. The disservice is that if the center point fizzles, the whole framework is bargained. Bent Pair Ethernet (10base-T), focused around unshielded contorted pair, and Fiber Optic Ethernet (FOIRL and 10base-FL), focused around fiber optic link, utilize the star.
The typical applications:
Utilize a bus topology for an extensive system with numerous clients and more fragments. With repeaters or media converters, you can without much of a stretch interconnect to different systems with diverse topologies.
Utilize a star topology when you need to utilize bent pair cabling (10base-T Ethernet) for a different building grounds setup (you may have turned pair-phone wire-introduced on your premises). Utilize a star topology for your fiber optic connections.
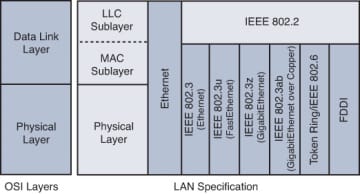
Ethernet divides the capacities of the information connection layer into two unique sub layers:
- Logical Links Control (LLC) sub layer: Defined in the 802.2 standard
- Media Access Controls (MAC) sub layer: Defined in the 802.3 standard
The LLC sub layer handles correspondence between the system layer and the MAC sub-layer. As a rule, LLC gives an approach to recognize the protocol that is passed from the information connection layer to the system layer. Along these lines, the fields of the MAC sub layer are not populated with protocol sort data, as was the situation in prior Ethernet executions.
The MAC sub layer has two essential obligations:
- Data encapsulation: It includes outline gathering before transmission, edge parsing upon gathering of a casing, information connection layer MAC tending to, and slip recognition.
- Media Access Control: Because Ethernet is an imparted media and all gadgets can transmit whenever, media access is controlled by a system called Carrier Sense Multiple Access with Collision Detection (CSMA/CD) when working down the middle duplex mode.
At the physical layer, Ethernet tags and actualizes encoding and interpreting plans that empower outline bits to be conveyed as signs crosswise over both unshielded curved pair (UTP) copper links and optical fiber links. In right on time usage, Ethernet utilized coaxial cabling.
MAC:
This protocol controls which gadgets can transmit information to the system, and when they can do so. CSMA/CD is the acronym for the Carriers Sensed Multiple Accesses with Collisions Detections. This extravagant term essentially signifies "Don't talk while another person is talking, however in the event that it happens, everybody stop and attempt again later." Let's take a gander at how it functions in finer grained subtle element:
Carriers Sense Multiple Accesses (CSMA)
This is a path for some gadgets to get to the same system (Multiple Access). The way it works is that each gadget expecting to send information to the system first "tunes in" to the wire to figure out whether any other individual is sending anything (Carrier Sense). On the off chance that there is any movement at the time, then the gadget expecting to transmit will hold up until the transmission closes, else it sends its information.
Collisions Detection (CD)
When a gadget establishes that the system is clear, it starts sending information. While sending, it screens what information is really on the wire, and contrasts it with what is continuously sent. It is feasible for two gadgets to see that the system is open in the meantime and for both to begin sending. At the point when this happens, the information on the wire will be distorted and none, of this gadget will see that what is really on the wire matches what it sent. This is known as an impact. The gadgets locate this crash, and both stop their current transmission, hold up an irregular measure of time, and attempt once more.
Each Ethernet system, paying little respect to sort, acts in this way. Commonly, this right to gain entrance system is most effective under times of light load, as there is a more noteworthy chance the system will be accessible when the gadget needs to transmit, and there is additionally less risk an alternate gadget will attempt to transmit in the meantime. As the heap on the system expands, crashes expand with it. In the long run, it is conceivable to come to the heart of the matter where there are an excess of crashes and gadgets invest more of a chance retransmitting and holding up than they do really sending information.
The CSMA/CD protocol is generally enough to keep the system running extremely well, however there are circumstances which can make it fall flat. Legitimate outline of the system is paramount to keep a breakdown of the fundamental CSMA/CD protocol. Configuration botches which cause issues are frequently either surpassing the greatest repeater tally or surpassing the separation furthest reaches of a system fragment.
One thing which ought to be remembered is that CSMA/CD happens consequently in each one Machine's system interface card, and there is nothing the client needs to program or set up to execute it, nor is the client generally informed of crashes.
The LANs utilized as a part of IEEE 802 systems and FDDI systems are the MAC addresses; they are focused around the tending to plan utilized within right on time Ethernet usage. A MAC location is a one of a kind serial number. When a MAC address has been allocated to a specific system interface (ordinarily at time of fabricate), that gadget ought to be extraordinarily identifiable amongst all other system gadgets on the planet. This ensures that every gadget in a system will have an alternate MAC address (closely resembling a road address). This makes it feasible for information bundles to be conveyed to an end of the line inside a sub network, i.e. hosts interconnected by some synthesis of repeaters, centers, spans and switches, yet not by system layer switches. In this way, for instance, when an IP bundle achieves its terminus (sub) network, the goal IP address (a layer 3 or system layer idea) is determined with the Address Resolution Protocol for Ipv4 or by Neighbor Discovery Protocol (Ipv6) into the MAC address (a layer 2 idea) of the end of the line host.
Cases of physical systems are Ethernet systems and Wi-Fi systems, both of which IEEE 802 systems and utilization IEEE 802 are 48-bit MAC addresses. A MAC layer is not needed in full-duplex point-to-point correspondence; however address fields are incorporated in some point-to-point protocols for similarity reasons. The channel access control components gave by the MAC layer is otherwise called a numerous access protocol. This makes it feasible for a few stations joined with the same physical medium to impart it. Cases of imparted physical media are transport systems, ring systems, center point systems, remote systems and half-duplex point-to-point joins. The different access protocol may discover or maintain a strategic distance from information bundle crashes if a parcel mode controversy based channel access strategy is utilized, or store assets to build a coherent channel if a circuit-exchanged or channelization-based channel access system is utilized. The channel access control instrument depends on a physical layer multiplex plan.
The most boundless numerous access protocols is the controversy based CSMA/CD protocol utilized as a part of Ethernet systems. This system is just used inside a system crash space, for instance an Ethernet transport system or a center point based star topology system. An Ethernet system may be separated into a few crash spaces, interconnected by extensions and switches.
A different access protocol is not needed in an exchanged full-duplex system, for example, today's exchanged Ethernet systems, yet is frequently accessible in the gear for similarity reasons. MAC's Forced Forwarding (MACFF) is utilized to control undesirable telecast movement and host-to-have correspondence. This is accomplished by administering system activity from hosts found on the same subnet yet at distinctive areas to an upstream portal gadget. This gives security at Layer 2 since no activity can pass specifically between the hosts. MACFF is suitable for Ethernet systems where a layer 2 spanning gadget, known as an Ethernet Access Node (EAN), join Access Routers to their customers. MACFF is arranged on the EANS. MACFF is portrayed in RFC 4562, MAC-Forced Forwarding: A Method for Subscriber Separation on an Ethernet Access Network. Partnered Telesis switches execute MACFF utilizing DHCP snooping to keep up a database that shows up on each one switch port. At the point when a host tries to get to the system through a switch port, DHCP snooping checks the host's IP address against the database to guarantee that the host is legitimate. MACFF then uses DHCP snooping to check whether the host has an entryway Access Router. On the off chance that it does, MACFF utilizes a manifestation of Proxy ARP to answer to any ARP solicitations, giving the switch's MAC address. This compels the host to send all activity to the switch, even movement bound to a host in the same subnet as the source. The switch gets the movement and settles on sending choices focused around a set of sending tenets, normally a QOS strategy or a set of channels.
So basically, Ethernet is pretty important component of networking. So, one trying to master this field must know about Ethernet so that he can understand the workings and the technologies which are involved behind this amazing cable.
Site Search:






