- Home
- Popular IT Certifications
- How to Configure Network Device Security Features
How to configure and verify network device security features
Cisco Integrated Services Routers ship with the business' most thorough security administrations, brilliantly inserting information, security, voice, and remote in the stage portfolio for quick, adaptable conveyance of mission-basic business applications.
With router execution and IP Security (Ipsec) VPN and firewall quickening up to five times that of past incorporated administrations switches with administrations enabled, the Cisco 1900, 2900, and 3900 Series Integrated Services Routers are perfect for little organizations and venture extension work places. The switches convey a rich, coordinated answer for joining remote business locales, teleworkers, versatile clients, and accomplice extranets or administration supplier oversaw client premises gear (CPE). By joining demonstrated Cisco IOS Software capacities and industry-heading LAN and WAN integration with world-class system security peculiarities, incorporated switch security results offer clients a financially savvy methodology to meet the most recent limb office administrations prerequisite, finished while exploiting existing system plans and operational best practices.
Ensure your system from all dangers while upgrading the limb office experience:
- Up to 5x execution increment over past era switches
- Secure joint effort and feature systems: Advanced VPN and Cisco IOS Firewall gimmicks convey secure, fantastic voice and feature and ensure against call spying, toll extortion, and refusal of administration (Dos).
- Secure portability with 802.11n remote combination
Through borderless administrations, you utilize the current framework to secure extension office associations. You can exploit your current system framework to control security dangers at remote locales and moderate WAN transmission capacity without conveying extra fittings. You have the adaptability to apply security capacities, for example, firewall, interruption avoidance framework (IPS), substance separating, and VPN, anyplace in your system to augment security profits. Late highlights include:
- Secure distributed computing administrations: Group Encrypted Transport VPN provides for you the apparatuses to make secure mists registering, enabling administrative agreeability particularly from the viewpoint of information in travel.
- Secure bound together portable building design: This construction modeling gives an open system to advanced mobile phones by utilizing Cisco security, VPN, and open key-framework (PKI) advances as enabling influences for provisioning, sending, and overseeing versatile administrations. It gives a protected versatile framework to a mixed bag of distinctive administrations, for example, voice, meandering, Wi-Fi, email messages, and so on.
- Cisco Virtual Office as a Service: This administration conveys progressed secure teleworking, enabling business versatility amid calamities and pandemics. Switch based system security results diminish both capital consumptions (Capex) and working costs (OPEX) by bringing down the quantity of gadgets, preparing, sensibility, power, and administration contract costs. What's more, security packs give critical investment funds contrasted with purchasing the switch and security emphasizes independently.
- One-touch PSIRT upgrade: This switch based result permits you to naturally download Product Security Incident Response Team (PSIRT) reactions from Cisco.com. Alternatively, the upgrade permits you to execute the PSIRT proposals.
- Advanced instrumentation: Router-based progressed instrumentation capacities help you procurement; screen; keep up; make system execution estimations; gather and measure information; and troubleshoot the gadget, the system, and the administrations that are enabled.
- Hardened foundational security: You can defend your switch and all entrance indicates into your system safeguard against assaults, for example, hacking and dispersed D
Device password security
Passwords control access to assets or gadgets. This is proficient through the definition a watchword or secret that is utilized as a part of request to validate demands. At the point when a solicitation is gotten for access to an asset or gadget, the appeal is tested for confirmation of the secret word and character, and access could be in truth, denied, or constrained focused around the result. As a security best practice, passwords must be made do with a Tacacs+ or RADIUS confirmation server. On the other hand, note that a mainly designed secret word for favored access is still required in the occasion of disappointment of the Tacacs+ or RADIUS administrations. A gadget can additionally have other secret word data exhibit inside its design, for example, a NTP key, SNMP group string, or Routing Protocol key. The enablesecret order is utilized within request to set the watchword that gives advantaged authoritative access to the Cisco IOS framework. The enablesecret order must be utilized, as opposed to the more seasoned enable secret key charge. The enable secret word charge utilizes a powerless encryption calculation.
In the event that no enablesecret is situated and a secret word is arranged for the comfort TTY line, the support watchword might be utilized as a part of request to get advantaged access, even from a remote virtual TTY (VTY) session. This activity is more likely than not undesirable and is an alternate motivation to guarantee arrangement of an enable secret. The administration watchword encryption worldwide setup charge regulates the Cisco IOS programming to encode the passwords, Challenge Handshake Authentication Protocol (CHAP) mysteries, and comparable information that are spared in its arrangement document. Such encryption is valuable keeping in mind the end goal to keep easy eyewitnesses from perusing passwords, for example, when they take a gander at the screen over the marshal of a director. The calculation is not intended to ensure setup records against genuine examination by even somewhat refined aggressors and must not be utilized for this reason. Any Cisco IOS setup document that contains scrambled passwords must be treated with the same mind that is utilized for a clear text rundown of those same passwords. While this feeble encryption calculation is not utilized by the enablesecret order, it is utilized by the enable secret word worldwide design charge, and the watchword line arrangement command. Passwords of this sort must be wiped out and the enablesecret order or the Enhanced Password Security peculiarity needs to be utilized. The enablesecret charge and the Enhanced Password Security gimmick utilization Message Digest 5 (Md5) for secret word hashing. This calculation has had significant open audit and is not known to be reversible. Then again, the calculation is liable to lexicon assaults. In a lexicon assault, an aggressor tries each saying in a word reference or other rundown of competitor passwords with a specific end goal to discover a match. Accordingly, arrangement records must be safely put away and just imparted to trusted people.
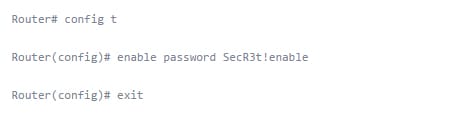
Enable secret vs. enable
The enable secret key keeps somebody from getting full get to your switch. The enable order is really used to change between distinctive securities levels on the switch (there are 0-15 levels of security). In any case, it is regularly used to go from client mode (level 1) to special mode (level 15). Indeed, in the event that you are at client mode and you simply sort enable, it accept you need to go to favored mode. To set a watchword to control access from client mode to advantaged mode, go to the worldwide design mode and utilize the enable secret word charge, in the same way as this:
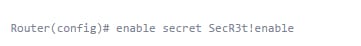
The enablesecret word has the same capacity as the enable watchword, however with enablesecret; the secret key is put away in a much stronger manifestation of encryption:
Transport
Overseeing optical systems is a gigantic test. Cisco Transport Manager is a wise, multi-engineering, bearer class component administration framework for optical systems. Its outline takes after the Tele management Forum (TMF) Multi-Technology Network Management (MTNM) principles. Here are the benefits of this feature;
- Keeping up a logged off database of assets and connections that are adjusted to the genuine system
- Confirming that circuits are set up and acting not surprisingly
- Intermittently going down the arrangement over substantial quantities of system components and programming pictures
- Making on-interest reports indicating authentic execution and satisfaction of client administration level assertions
- Transport Manager helps you address these issues, while it keeps up transport system effectiveness amid the whole lifecycle and bolsters OSS with real system information.
- Rearrange Management and Integrate with OSS
- Cisco Transport Manager disentangles provisioning and system administration and decreases general expenses by giving:
- Single framework to oversee optical systems, expanding profit by rearranging complex provisioning assignments
- Single storehouse for system data, supporting arrangement, deficiency, execution, and security administration
- Incorporation with OSS
More than 300 clients overall utilization Cisco Transport Manager to improve system security and help guarantee administration congruity. To ask for a demo, please click here.
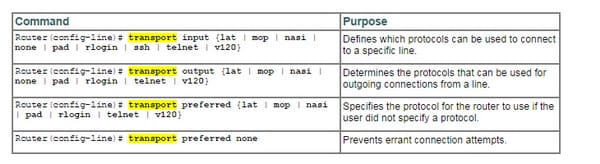
These are the configuration used for transport command;
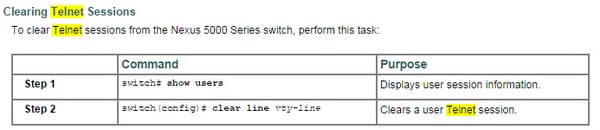
Disable telnet
This is how it's done;
SSH
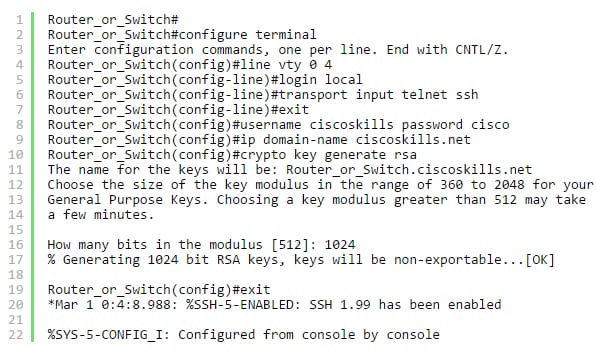
To add help for SSH to a Cisco switch or switch, the gadget needs some included data then simply passwords. The gadget will require a username and secret key, this could be arranged on an AAA server (Authentication Authorization and Accounting) or on the gadget generally this exercise will concentrate on by regional standards designed usernames and passwords. To set up SSH you have to design that after data with the end goal of this exercise the username will be ciscoskills and the secret key will be cisco. The main thing you have to do is change the VTY lines in the gadget (switch/switch) contingent upon the gadget you will have more VTY lines. This command will check its nearby database for usernames and passwords. The command is entered under (config-line) # instant with login nearby. The following step depends in the event that you need to still permit telnet associations with the gadget (switch/switch). This charge is entered under (config-line) # brief which is transport information telnet SSH. If you need SSH associations then sort the accompanying in transport data SSH. You must enter a no less than one username and secret word for the gadget (switch/switch). This charge is entered in worldwide design mode (config) # which for this case the username will be ciscoskills and the secret word will be cisco. The charge would be username ciscoskills secret key cisco in worldwide design mode. You likewise must arrange a DNS area name for this illustration the space will be ciscoskills.net. This charge is entered in worldwide arrangement mode (config) # which for this illustration isIP area name ciscoskills.net. The last charge to arrange SSH is produce a key match, this order is entered in worldwide design mode (config) # which is crypto key createsRSA. At the point when posed the question what number of bits in the modulus? Cisco documentation prefers 1024. The more bits you have the more drawn out the key and harder to break. The default is 512.
The new commands will seem like this;
VTYs
Through VTY's, you can utilize some application which is (Telnet, secure Shell, Hyper Terminal Win Applicant. Furthermore these are setup to remote access to your Host into the Router or Switch.
Physical security
Physical security is very vital when it comes to routers. So keep them in some drawers or cupboards where air can get passed through, so the theft or another physical damage by any incident can be prevented.
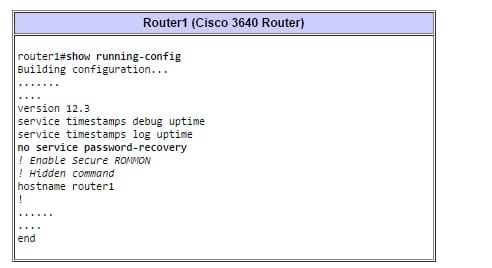
Service password
In the event that a switch is designed with the no administration secret key recuperation charge, this incapacitates all right to gain entrance to the ROMMON. On the off chance that there is no substantial Cisco IOS programming picture in the Flash memory of the switch, the client is not ready to utilize the ROMMON XMODEM command within request to load another Flash picture. Keeping in mind the end goal to settle the switch, you must get another Cisco IOS programming picture on a Flash SIMM, or on a PCMCIA card, for instance on the 3600 Series Routers. To minimize this hazard, a client who utilizes ROMMON security should additionally utilize double Flash bank memory and put a reinforcement Cisco IOS programming picture in a different parcel.
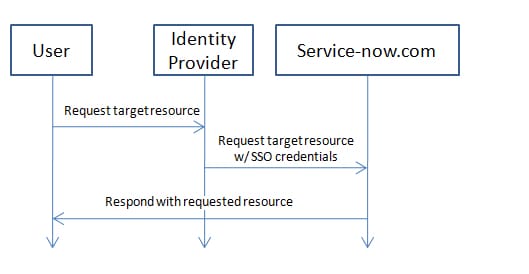
Describe external authentication methods
Outside Authentication, likewise alluded to as SSO (Single Sign-on), is a technique for access control that enables a client to log in once and get access to the assets of different programming frameworks without being incited to log in once more. It lets end clients login to their organization entryway page and be administered without needing to enter a client name and secret word once more. This is extremely valuable in extensive corporate situations where overseeing different client databases is restrictive.
Cisco routers hold an important position when it comes to networking. Network security is something which should be learn first when someone is learning about network engineering since it can help one protecting the data and establishing the secured connection.
Site Search:






