- Home
- Popular IT Certifications
- Protocols in the OSI and TCP/IP Models
What are the purpose and basic operation of the protocols in the OSI and TCP/IP models?
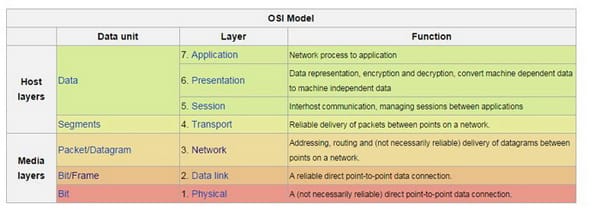
(OSI) is a calculated model that portrays and institutionalizes the interior capacities of a correspondence framework by parceling it into reflection layerss. The model is a result of an Open System Interconnections venture at the International Organization for Standardization (ISO).
The model gatherings correspondence capacities into seven legitimate layerss. A layers serves the layers on it and is served by the layers underneath it. Case in point, a layers that gives lapse free correspondences over a system gives the way required by applications which are above it, and while on other hand, it calls some lower layers to convey and get bundles that creates the substance of that way. Two occasions at one of the layers are joined by a level association on that layers.work on the layersed models of system building design was begun and International Organizations for the Standardization (ISO) started to create its OSI structure construction modeling. OSI had two significant segments: an unique model of systems administration, called Basic References Models or the seven-layerss model including some set of the particular protocols. The idea of a seven-layerss model was given by the works of Mr. Charles Bachman, Honeywell Information Services. Different parts of OSI configuration developed from encounters with ARPANET, the juvenile Internet,EIN, NPLNET, CYCLADES system and the works in the IFIP Wg6.1. A new plan was archived in the ISO 7498. In this specific model, a systems administration framework was separated into layerss. Inside each of the layerss, 1 or even more elements execute its usefulness. Every element associated straightforwardly just with the layerss quickly underneath it, and gave places to be used by a layers which is above it.
The Protocols empowered an element in one of the hosts to associate with a comparing substance at some same kind of layers in an alternate host. Administration definitions uniquely portrayed the usefulness gave to a (N)-layerss by a (N-1) layerss, and here N was one among total 7 layerss of protocols working in the nearby have. The OSI guidelines records are accessible from the ITU-T as the X.200-arrangement of recommendations. Some of the protocol determinations were additionally accessible as a feature of the ITU-T X arrangement. The comparable ISO and ISO/IEC guidelines for the OSI model were accessible from ISO, however just some of them without fees.
OSI
Layers:At each one level (N), two elements (layers N companions) trade protocol information units (Pdus) by method for a layers-N protocol. An administration information unit (SDU) is the payload of a PDU, transmitted unaltered to a companion. The SDU is an unit of information that is passed down starting with one OSI layers then onto the next lower layers, and which the lower layers typifies into a PDU. Layers N-1 includes a header or a footer, or both, to the SDU, making a PDU out of layers N-1. The added encircling make it conceivable to get the information from a source to a goal. The PDU at a layers N consequently turns into the SDU of layers N-1. Some orthogonal perspectives, for example, administration and security, include each layers. Security administrations are not identified with a particular layers: they might be connected by a few layerss, as characterized by ITU-T X.800 Recommendation. These administrations are planned to enhance the CIA triad (secrecy, uprightness, and accessibility) of transmitted information. In practice, the accessibility of correspondence administration is dictated by the collaboration between system plan and system administration protocols. Proper decisions for both of these are required to ensure against dissent of service.
A simple approach to envision the vehicle layers are to contrast it and a mail station, which manages dispatch and characterization of packages sent. Do recall, nonetheless, that a mail station deals with the external envelope of the mail. The higher layers might have what might as well be called twofold envelopes, for example, cryptographic presentation benefits that could be perused by the recipient just. Generally talking, burrowing protocols work at the vehicle layers; for example, convey non-IPs protocols, for example, IBM's SNA or Novell's IPX over the IP system, or the ends-to-ends encryptions with Ipsec. At same time, the Generic Routings Encapsulation may appear to be the system layers protocols, if the epitome of a payload happens just at endpoint, the GRE gets to be closer to the vehicle protocol which uses the IP headers however contains complete casings or parcels to convey to some endpoint. The L2tp conveys PPP outlines inside transport parcel. Despite the fact that not created under the OSI Reference Model and not strictly fitting in with the OSI meaning of the vehicle layers, the Transmission Controls Protocol (TCP) and the User Datagram Protocol (UDP) of the Internet Protocol Suite are ordinarily sorted as layers-4 protocols inside OSI. Protocol details definitely characterize the interfaces between distinctive machines, however the product interfaces inside machines, known as system attachments are usage particular. Interface norms, aside from the physical layers to media, are rough usage of OSI administration details.
OSI
vs. TCP/IP:In a TCP/IP's model of Internet, the conventions are deliberately not so unbendingly composed into the strict layers same as they are in OSI model. However, the TCP/IP really does perceive four wide layers of usefulness which are inferred from the working extent of their contained protocols: the extent of the product application; the ends-to-ends transport association; the internetworking territory; and the extent of the immediate connections to different hubs on the neighborhood network. Despite the fact that the idea is unique in relation to an OSI model, all those layers are all things considered regularly contrasted and the OSI's layering plan in the accommodating way.
The connection layers incorporates the OSI information connection and the physical layerss, and parts of the OSI's system layers. These examinations are focused around the first seven-layers protocol demonstrate as characterized in ISO 7498, instead of refinements in these type of things as an inside association of the system layers document. The probably strict companion layersing of the OSI demonstrate as it is generally depicted does not show inconsistencies in TCP/IP, as it is allowable that protocol use does not take after the order inferred in a layersed model. Such samples exist in some routing protocols (e.g., OSPF), or in the portrayal of burrowing protocols, which give a connection layers to an application, in spite of the fact that the passage host protocol may well be a vehicle or even an application-layers protocol in its own particular right.
TCP
(TCP) is one of the center protocols of the Internet's protocol suite (IP), and is common to the point that the whole suite is regularly called TCP/IP. TCP gives solid, requested and mistake checked conveyance of a stream of octets between projects running on machines joined with a neighborhood, intranet or the general population Internet. It lives at the vehicle layers. Web programs use TCP when they join with servers on the World Wide Web, and it is utilized to convey email and exchange records starting with one area then onto the next. HTTPS, HTTP, Pop3, SMTP, SSH IMAP, FTP, Telnet and a mixed bag of different protocols are regularly epitomized in TCP.
Applications that don't require the unwavering quality of TCP association might rather utilize the connectionless User Datagram Protocol (UDP), which underscores low-overhead operation and lessened inertness as opposed to lapse checking and conveyance validation. The protocol compares to the vehicle layers of TCP/IP suite. TCP gives a correspondence administration at a middle of the road level between an application program and the Internet Protocol (IP). That is, the point at which an application project longings to send an extensive lump of information over the Internet utilizing IP, as opposed to breaking the information into IP-sized pieces and issuing an arrangement of IP appeals, the product can issue a solitary appeal to TCP and let TCP handle the IP subtle elements. IP meets expectations by trading bits of data called bundles. A bundle is a grouping of octets (bytes) and comprises of a header took after by a body. The header depicts the parcel's source, terminus and control data. The body contains the information IP is transmitting.
Because of system blockage, movement burden adjusting, or other unusual system conduct, IP bundles could be lost, copied, or conveyed out of request. TCP locates these issues, demands retransmission of lost information, improves out-of-request information, and even helps minimize system blockage to diminish the event of alternate issues. Once the TCP recipient has reassembled the grouping of octets initially transmitted, it passes them to the accepting application. Subsequently, TCP edited compositions the application's correspondence from the underlying systems administration points of interest. TCP is used broadly by a hefty portion of the Internet's most well-known applications, including the World Wide Web (WWW), E-mail, File Transfer Protocol, Secure Shell, shared record imparting, and some streaming media applications. TCP is improved for exact conveyance instead of convenient conveyance, and thusly, TCP once in a while causes moderately long postpones (on the request of seconds) while holding up for out-of-request messages or retransmissions of lost messages. It is not especially suitable for constant applications, for example, Voice over IP. For such applications, protocols like the Real-time Transport Protocol (RTP) running over the User Datagram Protocol (UDP) are typically prescribed instead. TCP is a dependable stream conveyance benefit that ensures that all bytes got will be indistinguishable with bytes sent and in the right request. Since parcel exchange over numerous systems is not solid, a procedure known as positive affirmation with retransmission is utilized to ensure unwavering quality of bundle exchanges. This essential procedure requires the beneficiary to react with an affirmation message as it gets the information. The sender keeps a record of every bundle it sends. The sender likewise keeps up a clock from when the parcel was sent, and retransmits a bundle if the clock terminates before the message has been recognized. The clock is required in the event that a parcel gets lost or corrupted.
While IP handles genuine conveyance of the information, TCP stays informed concerning the individual units of information transmission, called fragments that a message is separated into for proficient routing through the system. For instance, when a HTML document is sent from a web server, the TCP programming layers of that server separates the succession of octets of the record into sections and advances them independently to the IP programming layers (Internet Layers). The Internet Layers embodies every TCP section into an IP parcel by including a header that incorporates (among other information) the terminus IP address. At the point when the customer program on the end of the line machine gets them, the TCP layers (Transport Layers) reassembles the individual sections and guarantees they are effectively requested and lapse free as it streams them to an application. Transmission Control Protocol acknowledges information from an information stream, isolates it into lumps, and includes a TCP header making a TCP fragment. The TCP section is then exemplified into an Internet Protocol (IP) datagram, and traded with peers. The term TCP bundle shows up in both casual and formal use, though in more exact phrasing section alludes to the TCP Protocol Data Unit (PDU), datagram to the IP PDU, and casing to the information connection layers PDU:
Techniques transmit information by approaching the TCP and passing cradles of information as contentions. The TCP bundles the information from these supports into fragments and approaches the web module to transmit each one fragment to the end of the line TCP.
A TCP fragment comprises of a section header and an information area. The TCP header contains 10 compulsory fields, and a discretionary augmentation field (Options, pink foundation in table).
The information area takes after the header. Its substance is the payload information conveyed for the application. The length of the information area is not determined in the TCP fragment header. It could be figured by subtracting the joined length of the TCP header and the epitomizing IP header from the aggregate IP datagram length (pointed out in the IP header).
OSI layerss and TCP are of immense importance when it comes to networking. So those wishing to have future in this field should get to know them both so they can pass their CCNA exams easily.
Site Search:






