Pass Your Juniper JNCIA-Junos Certification Easy!
Juniper JNCIA-Junos Certification Exams Questions & Answers, Accurate & Verified By IT Experts
Instant Download, Free Fast Updates, 99.6% Pass Rate.

$69.99
Download Free JNCIA-Junos Practice Test Questions VCE Files
| Exam | Title | Files |
|---|---|---|
Exam JN0-103 |
Title Junos, Associate (JNCIA-Junos) |
Files 3 |
Exam JN0-105 |
Title Junos, Associate (JNCIA-Junos) |
Files 1 |
Juniper JNCIA-Junos Certification Exam Dumps & Practice Test Questions
Prepare with top-notch Juniper JNCIA-Junos certification practice test questions and answers, vce exam dumps, study guide, video training course from ExamCollection. All Juniper JNCIA-Junos certification exam dumps & practice test questions and answers are uploaded by users who have passed the exam themselves and formatted them into vce file format.
JNCIA-Junos Certification Guide: From Fundamentals to Advanced Networking Skills
The Juniper Networks Certified Internet Associate (JNCIA-Junos) certification is a foundational credential for networking professionals seeking to establish expertise with Juniper devices. Unlike general networking certifications, JNCIA-Junos focuses on practical knowledge of Junos OS and the ability to apply networking principles in real-world scenarios. It is recognized globally and serves as a stepping stone for more advanced Juniper certifications, offering a structured pathway for IT professionals to grow in network engineering roles.
The certification is designed to validate both theoretical understanding and practical skills. It ensures that candidates can configure, manage, and troubleshoot Juniper devices while demonstrating a strong grasp of networking fundamentals such as IP addressing, routing, switching, and network security. For those entering the field, JNCIA-Junos offers a credible credential that sets them apart in competitive job markets.
Who Should Pursue JNCIA-Junos
JNCIA-Junos is suitable for a variety of professionals and learners who want to strengthen their networking expertise. Network engineers, system administrators, IT professionals transitioning into networking roles, and students entering the field can all benefit. Additionally, those aiming for higher-level Juniper certifications such as JNCIS or JNCIP often start with JNCIA-Junos to build a solid foundation.
For network engineers already working with Juniper devices, the certification confirms their skills and knowledge. IT professionals looking to transition into networking gain structured learning that prepares them for practical challenges. Students or recent graduates can leverage the credential to stand out in entry-level network roles, demonstrating both initiative and industry-recognized skills.
The certification is particularly valuable in environments where Juniper solutions are deployed, including service providers, enterprise networks, and government infrastructures. Employers recognize the credential as proof of hands-on expertise with Junos OS and familiarity with networking protocols, which translates to higher confidence in the candidate's ability to manage complex network operations.
Key Knowledge Areas
The JNCIA-Junos certification covers a broad spectrum of topics to ensure candidates are prepared for real-world network environments. Understanding these areas is critical for exam success and practical application.
Networking Fundamentals
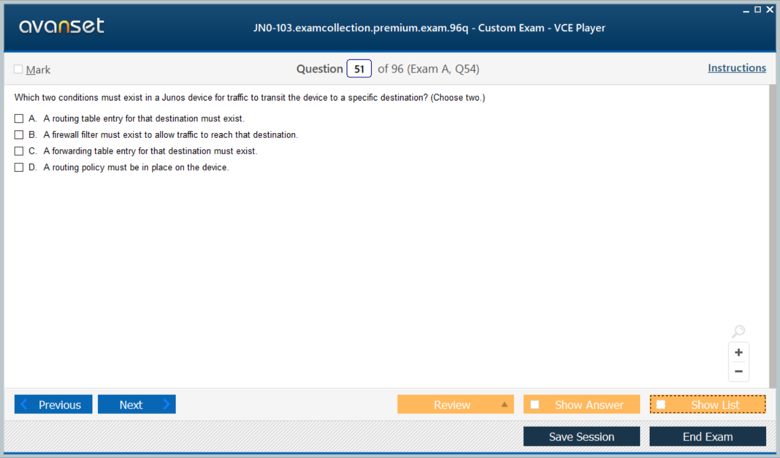
Networking fundamentals provide the baseline knowledge required to work with any network infrastructure. Candidates must understand OSI and TCP/IP models, IP addressing, subnetting, and the basics of routing and switching. Familiarity with how devices communicate across networks and the functions of different protocols is essential.
Understanding IP addressing includes knowledge of IPv4 and IPv6 formats, subnet masks, and how to calculate network and host addresses. Subnetting skills are particularly important for designing efficient networks and managing traffic flows effectively.
Routing and switching concepts include the role of routers and switches in forwarding data, the difference between static and dynamic routing, and how network topologies influence performance and reliability. This foundation ensures candidates can interpret network diagrams and implement basic connectivity solutions.
Junos OS Fundamentals
Junos OS is the operating system powering Juniper devices, and proficiency in it is crucial for network professionals. Candidates learn the structure of the command-line interface (CLI), which includes operational and configuration modes. Understanding how to navigate the CLI and apply commands effectively is central to managing Junos devices.
Candidates also learn to work with configuration files, including how to edit, save, and roll back configurations to ensure network stability. Software management is another critical aspect, encompassing software upgrades, patch management, and maintaining device health. Knowing how to perform these tasks safely prevents disruptions and supports reliable network operations.
Routing Fundamentals
Routing is a core component of the JNCIA-Junos curriculum. Candidates gain knowledge of both static and dynamic routing. Static routing involves manually configuring routes between networks, while dynamic routing uses protocols such as OSPF, RIP, and BGP to adaptively manage network paths.
Understanding how routing decisions are made, how to troubleshoot routing issues, and how to implement routing protocols in Junos OS ensures that candidates can maintain optimal network performance. Emphasis is placed on practical application, so candidates can configure and verify routes in lab or production environments.
Firewall Filters and Security
Network security is a fundamental requirement for modern IT infrastructures. The JNCIA-Junos certification introduces candidates to firewall filters and packet filtering, allowing them to control traffic flows effectively. Understanding how to create and apply firewall filters helps prevent unauthorized access and protects network resources.
Security concepts also cover the role of policies in managing traffic between networks. Candidates learn to identify risks, apply rules that mitigate those risks, and monitor network behavior for anomalies. This knowledge is vital for ensuring both compliance and operational safety.
Operational Monitoring and Troubleshooting
Network operations require ongoing monitoring and the ability to troubleshoot problems quickly. JNCIA-Junos candidates are trained to use Junos OS tools for operational monitoring, including commands that provide real-time insights into device performance and network traffic.
Troubleshooting skills include identifying connectivity issues, analyzing logs, and resolving configuration errors. Candidates learn systematic approaches to problem-solving, ensuring that they can maintain network uptime and performance. Regular practice in lab environments reinforces these skills and builds confidence in handling real-world network challenges.
Exam Overview
Understanding the exam structure is crucial for effective preparation. The JNCIA-Junos exam evaluates both conceptual knowledge and practical abilities.
The exam format typically includes multiple-choice questions covering networking fundamentals, Junos OS, routing, security, and operational monitoring. Candidates are given 90 minutes to complete the exam, and a passing score generally falls around 70 percent. While the exam does not require hands-on lab work, practical experience in configuring Junos devices is highly recommended. Simulation tools, lab setups, and guided practice sessions significantly increase the chances of success.
Benefits of JNCIA-Junos Certification
The certification provides a wide range of advantages for networking professionals. First, it validates core networking skills and proficiency with Junos OS, making candidates more attractive to employers. It also opens the door to higher-level Juniper certifications, providing a clear career progression path.
Professionals holding JNCIA-Junos can access more advanced roles, including network engineering, network operations, and infrastructure management. The credential also demonstrates a commitment to continuous learning, which is highly valued in IT and networking industries. Additionally, Juniper’s recognition as a leading network technology provider ensures that certified individuals are acknowledged in both enterprise and service provider networks.
Preparation Strategies
Effective preparation is key to passing the JNCIA-Junos exam and mastering Juniper technologies. Hands-on practice is essential; candidates should work with Junos OS in lab environments, configuring interfaces, routing protocols, and security features. Familiarity with the CLI is critical, as many exam questions assume basic operational knowledge.
Reviewing exam objectives thoroughly ensures no topic is overlooked. Study materials such as official guides, video tutorials, and practice questions help reinforce learning. Collaborative study groups or online communities provide opportunities to discuss concepts, ask questions, and gain insights from peers. Time management is also important; candidates should allocate sufficient time for theory review and hands-on practice to build both knowledge and confidence.
Real-World Applications
JNCIA-Junos certification equips professionals to handle practical tasks in enterprise and service provider networks. Tasks include configuring network devices, managing traffic flows, implementing security policies, and monitoring network performance. Knowledge of routing protocols enables engineers to optimize network paths, reduce latency, and ensure redundancy.
Additionally, firewall filters and security configurations protect networks from unauthorized access and potential attacks. Monitoring and troubleshooting skills allow professionals to quickly identify and resolve network issues, minimizing downtime and maintaining service quality. Organizations benefit from certified staff who can maintain reliable, secure, and efficient networks, reducing operational risks and improving productivity.
Career Opportunities
Holding a JNCIA-Junos certification can significantly impact career growth. Entry-level roles include network support engineer, network technician, and junior network administrator. With experience, certified professionals can move into network engineer or network operations roles, managing more complex infrastructures.
The certification also provides a stepping stone for advanced Juniper certifications, such as JNCIS and JNCIP, which open doors to senior network engineering positions, solutions architect roles, and specialized areas such as network security or service provider networks. The combination of Juniper knowledge and general networking expertise positions certified individuals as highly desirable in competitive IT markets.
The Juniper JNCIA-Junos certification serves as a strong foundation for networking professionals seeking to build expertise in Junos OS and network management. By covering networking fundamentals, routing, security, operational monitoring, and troubleshooting, the certification ensures candidates are prepared for both the exam and real-world networking scenarios.
With practical skills, validated knowledge, and industry recognition, JNCIA-Junos helps professionals establish credibility, advance their careers, and pursue higher-level certifications. Whether entering the networking field or seeking to specialize in Juniper technologies, this certification offers valuable opportunities for growth, skill development, and professional success.
Preparing for the JNCIA-Junos Exam
Success in the JNCIA-Junos certification begins with understanding the exam objectives and creating a structured preparation plan. The exam evaluates knowledge of networking fundamentals, Junos OS, routing, security, and troubleshooting. Candidates should review the official exam blueprint to identify key topics and allocate study time accordingly.
A well-structured plan includes a combination of theoretical study and practical hands-on practice. Reading official Juniper guides, watching video tutorials, and reviewing online resources help build a strong knowledge base. Setting up a lab environment or using virtual labs is critical to gaining experience with Junos commands, configurations, and network scenarios. Practicing regularly allows candidates to internalize concepts and build confidence for the exam.
Setting Up a Lab Environment
Hands-on experience is essential for mastering Junos OS and network configurations. Setting up a lab environment allows candidates to practice commands, configure interfaces, and test routing and security policies.
A lab can be physical, using actual Juniper devices, or virtual, leveraging emulators and simulation tools. Virtual labs provide flexibility, cost-effectiveness, and the ability to reset configurations easily. Candidates should practice basic tasks such as configuring IP addresses, setting up static routes, implementing firewall filters, and monitoring network performance. Regular lab exercises help reinforce concepts and improve troubleshooting skills, ensuring candidates are prepared for both the exam and real-world applications.
Mastering Junos OS Commands
A significant portion of the exam assesses proficiency with Junos OS commands. Candidates should be comfortable navigating the CLI, switching between operational and configuration modes, and using commands to monitor, configure, and troubleshoot devices.
Key commands include viewing system status, configuring interfaces, verifying routes, applying firewall filters, and managing software versions. Practicing these commands in a lab environment ensures that candidates can execute them quickly and accurately. Understanding command syntax, operational modes, and configuration hierarchy is essential for exam success and practical network management.
Understanding Routing Protocols
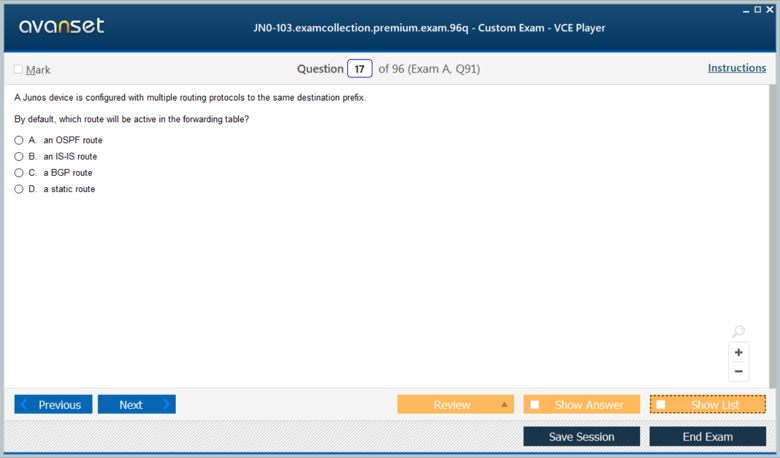
Routing protocols are a core focus of the JNCIA-Junos exam. Candidates must understand static routing and dynamic routing protocols such as OSPF, RIP, and BGP.
Static routing involves manually defining routes between networks, which is important for simple network topologies or backup paths. Dynamic routing allows devices to automatically share routing information and adapt to changes in the network.
Understanding how routing decisions are made, how to interpret routing tables, and how to troubleshoot routing issues is critical. Candidates should practice configuring routing protocols in the lab, verifying route propagation, and resolving common routing problems. Familiarity with route preferences, metrics, and protocol-specific commands ensures comprehensive preparation.
Implementing Firewall Filters and Security Policies
Network security is increasingly important, and the JNCIA-Junos exam evaluates knowledge of firewall filters and traffic management. Candidates must understand how to control traffic flows, allow or deny specific packets, and implement security policies effectively.
Practicing the creation and application of firewall filters in a lab environment reinforces learning. Candidates should explore how filters are applied to interfaces, how to verify their effects, and how to troubleshoot misconfigurations. Understanding the interaction between routing and firewall policies is also important for maintaining secure and efficient network operations.
Monitoring and Troubleshooting Networks
Operational monitoring and troubleshooting skills are essential for real-world network management. Candidates should learn to use Junos OS tools to monitor device status, traffic, and system performance.
Troubleshooting involves systematically identifying and resolving connectivity issues, configuration errors, and performance problems. Candidates should practice common troubleshooting scenarios, such as interface failures, routing conflicts, and misapplied firewall filters. Developing a structured approach to problem-solving ensures quick resolution of network issues, reducing downtime and maintaining service quality.
Utilizing Study Resources
Effective preparation relies on a combination of study materials and practice. Candidates should use official Juniper study guides, online tutorials, and practice exams to reinforce learning.
Practice exams provide a benchmark for readiness and highlight areas that require further study. Video tutorials and interactive labs enhance understanding of concepts and commands, while study groups and online forums offer opportunities to discuss challenges and solutions with peers. A diverse set of resources ensures comprehensive preparation and builds confidence for exam day.
Time Management Strategies
Time management is crucial for both exam preparation and test-taking. Candidates should create a study schedule that balances theory, practice, and review. Allocating specific hours to lab exercises, command practice, and concept revision ensures consistent progress.
During the exam, time management involves pacing through questions, identifying easier questions first, and revisiting more challenging ones later. Practicing with timed mock exams can simulate the actual test environment, improving focus and efficiency. Strong time management reduces stress and increases the likelihood of success.
Real-World Applications of JNCIA-Junos Skills
The knowledge and skills gained through JNCIA-Junos preparation are directly applicable to professional network environments. Configuring interfaces, managing routing protocols, applying firewall policies, and troubleshooting network issues are everyday tasks for network engineers.
Organizations benefit from certified professionals who can optimize network performance, enhance security, and minimize downtime. Practical experience with Junos OS allows candidates to transition smoothly into operational roles, managing enterprise or service provider networks with confidence. Skills developed during preparation provide long-term value, supporting both career growth and organizational success.
Common Challenges and How to Overcome Them
Candidates often face challenges such as memorizing command syntax, understanding complex routing concepts, and troubleshooting configuration issues. To overcome these challenges, consistent practice and repetition are essential.
Breaking down complex topics into smaller, manageable segments improves comprehension. Hands-on labs reinforce theory, while group discussions or mentorship provide additional support. Reviewing mistakes in practice exams and understanding why errors occurred ensures continuous improvement. Maintaining focus, discipline, and a structured study plan helps candidates navigate difficulties and achieve certification success.
Tracking Progress and Assessing Readiness
Monitoring progress during preparation helps candidates identify strengths and weaknesses. Regular self-assessment through quizzes, lab exercises, and practice exams provides measurable feedback.
Focusing on weaker areas, revisiting challenging concepts, and practicing under timed conditions enhance readiness. Confidence grows as candidates gain familiarity with exam objectives, command execution, and troubleshooting scenarios. A structured progress assessment ensures that preparation is comprehensive and aligned with the demands of the certification exam.
Career Growth Opportunities
JNCIA-Junos certification opens doors to numerous career opportunities. Entry-level positions include network support engineer, network administrator, and junior network technician. Certified professionals demonstrate a foundation of networking knowledge and practical skills, making them attractive candidates for employers.
With experience, JNCIA-Junos holders can advance to network engineer roles, managing larger infrastructures and more complex network scenarios. The certification also serves as a gateway to advanced Juniper credentials, such as JNCIS and JNCIP, leading to specialized roles in network security, service provider networks, and enterprise architecture. Career growth is supported by both the certification and the practical skills acquired during preparation.
Benefits of Hands-On Experience
While theoretical knowledge is important, hands-on experience is critical for mastering Junos OS and networking concepts. Working in labs or real network environments allows candidates to apply commands, configure devices, and troubleshoot issues.
Hands-on practice reinforces learning, builds confidence, and develops problem-solving skills. Candidates become familiar with real-world scenarios, learning to respond effectively to network challenges. Practical experience enhances employability, as employers value professionals who can immediately contribute to network operations.
Final Preparation Tips
Before the exam, candidates should focus on reviewing key concepts, practicing commands, and completing full-length practice exams. Familiarity with the CLI, routing configurations, firewall filters, and troubleshooting procedures is essential.
Time management, stress control, and confidence play important roles on exam day. Candidates should ensure they are well-rested, organized, and mentally prepared. Maintaining a positive mindset and reviewing difficult areas during final preparation increases the likelihood of success. Consistent preparation, combined with practical experience, ensures readiness for the JNCIA-Junos certification exam.
Preparing for the JNCIA-Junos certification requires a combination of theoretical knowledge, hands-on practice, and strategic study. Understanding exam objectives, mastering Junos OS commands, configuring routing protocols, implementing security policies, and developing troubleshooting skills are all essential components of preparation.
Candidates who approach preparation systematically, use diverse study resources, and practice regularly in lab environments gain confidence and competence. The skills and knowledge acquired not only support exam success but also translate directly to real-world network operations. Certification enhances career opportunities, builds professional credibility, and provides a foundation for advanced Juniper certifications.
Advanced Junos Features
After gaining foundational knowledge, understanding advanced Junos OS features is critical for managing complex networks. Junos OS includes capabilities such as routing policies, VLANs, virtual routing and forwarding (VRF), and advanced security mechanisms. Mastering these features allows network professionals to optimize performance, enhance security, and maintain scalable network infrastructures.
Routing policies enable granular control over traffic, allowing engineers to influence route selection, redistribute routes between protocols, and filter unwanted traffic. Configuring policies requires understanding route-maps, policy statements, and logical hierarchies within Junos OS. VRF implementation provides network segmentation, ensuring that multiple virtual networks can coexist securely on the same physical infrastructure. VLANs further support logical segmentation, improving performance and isolating traffic for specific departments or applications.
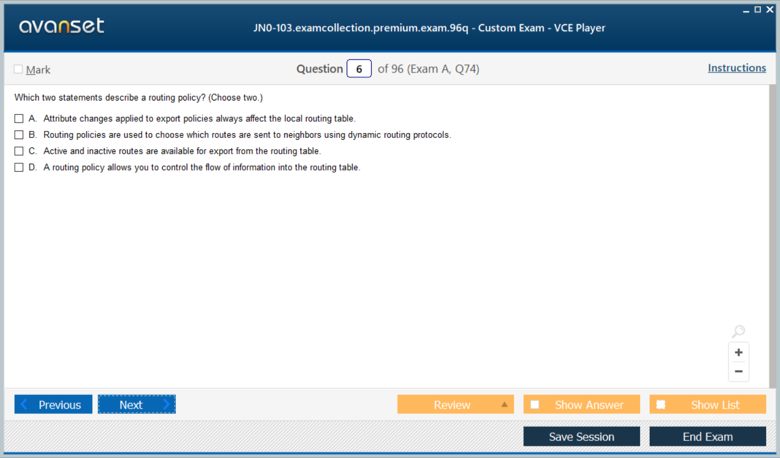
Understanding Routing Policy Implementation
Routing policies are essential in complex networks, allowing control over route advertisement, acceptance, and modification. Candidates must learn to create and apply policy statements, define match conditions, and configure actions such as accepting, rejecting, or modifying routes.
Advanced routing policies are often used in service provider environments or large enterprise networks to optimize traffic, implement redundancy, and enforce security measures. Practicing routing policy configurations in lab environments helps candidates understand their impact on routing tables and overall network behavior.
Virtual Routing and Forwarding
Virtual Routing and Forwarding (VRF) is a technique that allows multiple routing tables to coexist on a single router, providing network segmentation and isolation. VRF is widely used in enterprise and service provider networks to separate customer traffic, ensure privacy, and manage complex routing requirements.
Candidates should understand VRF concepts, configuration steps, and troubleshooting techniques. Hands-on practice in lab setups ensures that engineers can implement VRF correctly, verify routing behavior, and troubleshoot connectivity issues across virtual networks.
Advanced Security Configurations
Junos OS offers advanced security features beyond basic firewall filters, including zone-based policies, NAT, and intrusion detection/prevention integration. These tools allow network engineers to enforce strict security rules while maintaining optimal network performance.
Zone-based policies define traffic flows between security zones, providing a clear separation between internal, external, and DMZ networks. NAT allows translation between private and public IP addresses, supporting secure internet connectivity. Understanding how to configure and monitor these features is essential for protecting network assets against unauthorized access and attacks.
Troubleshooting Complex Network Issues
Troubleshooting is a critical skill for network professionals. Advanced troubleshooting in Junos OS involves diagnosing routing conflicts, interface errors, security misconfigurations, and performance bottlenecks.
Candidates should develop systematic troubleshooting methodologies, starting with identifying symptoms, isolating the affected components, analyzing configurations, and verifying solutions. Lab exercises that simulate network failures help engineers gain confidence and experience in resolving real-world issues. Common challenges include routing loops, misapplied firewall policies, and incorrect VLAN or VRF assignments.
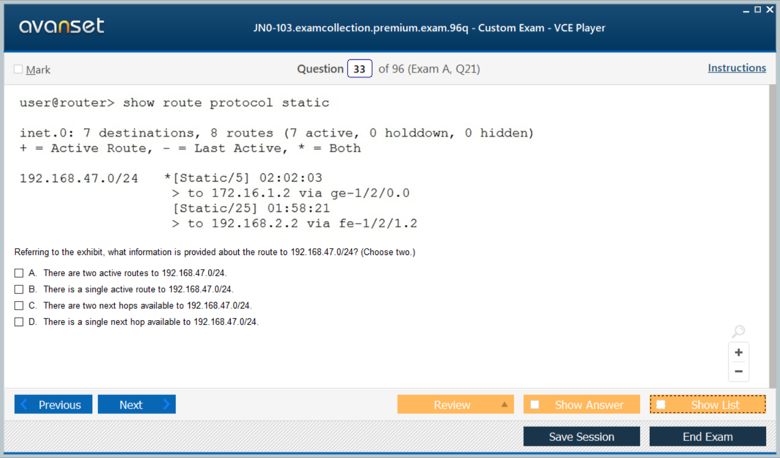
Using Operational Commands for Troubleshooting
Junos OS provides a variety of operational commands that are essential for network monitoring and troubleshooting. Commands such as show interfaces, show route, ping, traceroute, and monitor traffic allow engineers to assess device and network status in real-time.
Understanding how to interpret command outputs, identify anomalies, and take corrective actions is key to effective troubleshooting. Candidates should practice using these commands in different scenarios to become proficient in detecting and resolving network problems efficiently.
Configuration Management and Automation
Advanced Junos management includes configuration versioning, rollback, and automation. Configuration management ensures network stability and reduces downtime during changes. Candidates should be familiar with saving configurations, comparing versions, and performing rollbacks if errors occur.
Automation tools and scripts can simplify repetitive tasks, reduce human error, and increase operational efficiency. Understanding how to implement automation within Junos OS, including using templates and scripts, prepares candidates for modern network management practices.
Real-World Network Scenarios
Understanding real-world applications of Junos OS is critical for professional success. Candidates should analyze case studies and network scenarios that involve routing optimization, VLAN segmentation, firewall policy enforcement, and troubleshooting.
For example, configuring redundant links with OSPF or BGP ensures high availability, while implementing firewall filters protects sensitive data from unauthorized access. Segmentation using VLANs or VRF allows different departments or customers to share the same physical infrastructure securely. Practicing these scenarios in a lab or simulation environment helps candidates translate theoretical knowledge into practical skills.
Performance Optimization
Optimizing network performance is a key responsibility of certified Juniper professionals. Candidates should learn techniques for managing bandwidth, reducing latency, and ensuring efficient traffic flow.
Monitoring tools in Junos OS allow engineers to track interface utilization, packet loss, and error rates. Adjusting routing metrics, fine-tuning policy statements, and balancing loads across links contribute to improved network performance. Practical exercises that simulate high-traffic conditions teach engineers how to maintain optimal network operations.
Security Best Practices
Security is an ongoing concern in network management. Advanced Junos configurations include implementing ACLs, secure management access, and logging mechanisms to detect anomalies.
Candidates should learn how to configure secure SSH access, enforce password policies, and monitor system logs for unusual activity. Understanding how to integrate security features with routing and traffic management ensures that networks remain both efficient and protected. Continuous monitoring and proactive adjustments prevent potential vulnerabilities from being exploited.
Common Troubleshooting Scenarios
Candidates should become familiar with common troubleshooting scenarios, such as:
Routing misconfigurations causing unreachable networks
Misapplied firewall filters blocking legitimate traffic
VLAN or VRF assignment errors leading to connectivity issues
Interface errors affecting throughput and latency
Misconfigured NAT rules preventing external connectivity
Practicing these scenarios helps candidates develop problem-solving strategies and reinforces the importance of methodical troubleshooting approaches.
Lab Exercises for Advanced Skills
Hands-on labs remain essential for mastering advanced concepts. Recommended exercises include:
Configuring routing policies and verifying route behavior
Setting up VRFs and ensuring isolated traffic flows
Applying zone-based firewall policies and testing traffic
Performing interface and routing troubleshooting exercises
Implementing configuration rollback and testing recovery
Lab practice reinforces theoretical learning, ensures familiarity with commands, and builds confidence in handling real-world network challenges.
Integration with Enterprise Networks
JNCIA-Junos professionals often work in enterprise environments where multiple technologies coexist. Integration skills include understanding how Junos devices interact with non-Juniper equipment, how routing protocols interoperate, and how security policies align across platforms.
Candidates should study cross-vendor interoperability, traffic flow analysis, and policy alignment. Real-world deployments often involve multi-vendor environments, making these integration skills crucial for network engineers.
Continuous Learning and Certification Pathways
JNCIA-Junos is the first step in a broader Juniper certification journey. Continuous learning ensures that professionals stay updated with new features, best practices, and evolving network standards.
Following JNCIA-Junos, candidates can pursue JNCIS, JNCIP, and other specialized certifications in security, data center, or service provider networking. Building a roadmap of certifications supports career growth and deepens technical expertise. Networking professionals are encouraged to participate in online communities, forums, and training workshops to stay current with industry developments.
Mastering advanced Junos OS features, routing policies, VRF, security configurations, and troubleshooting techniques equips candidates to handle complex network environments confidently. Hands-on practice, scenario analysis, and performance optimization ensure readiness for professional roles and higher-level Juniper certifications.
JNCIA-Junos knowledge, when combined with practical application of advanced features, enables network engineers to manage enterprise and service provider networks effectively. Certified professionals contribute to network reliability, security, and efficiency while enhancing their career growth opportunities and technical credibility.
Exam Strategies for JNCIA-Junos
Preparing for the JNCIA-Junos exam requires more than technical knowledge; strategic planning and effective study techniques are equally important. Candidates should start by reviewing the official exam objectives and identifying areas of strength and weakness. Breaking the syllabus into manageable segments allows for focused learning, ensuring that no topic is overlooked.
A structured study schedule is recommended, balancing theoretical review, hands-on practice, and mock exams. Candidates should allocate time for revisiting challenging concepts and reinforcing skills through lab exercises. Understanding the weight of different topics in the exam can also guide prioritization, ensuring that time and effort are invested efficiently.
Understanding the Exam Format
The JNCIA-Junos exam consists primarily of multiple-choice questions that evaluate both conceptual knowledge and practical understanding. Familiarity with the exam format reduces anxiety and helps candidates manage their time effectively during the test.
Key areas covered include networking fundamentals, Junos OS commands, routing, security, and troubleshooting. Practicing with sample questions and simulated exams allows candidates to gauge readiness, identify gaps, and refine problem-solving approaches. Time management is crucial, as candidates must balance accuracy with speed to complete all questions within the allotted 90 minutes.
Mock Exams and Practice Questions
Taking mock exams is one of the most effective ways to prepare for JNCIA-Junos. Practice questions help candidates become familiar with question formats, identify areas that need further study, and develop test-taking strategies.
Mock exams should simulate real exam conditions, including time constraints and question complexity. Reviewing incorrect answers and understanding why mistakes occurred reinforces learning and ensures continuous improvement. Repetition of practice tests builds confidence and enhances the ability to tackle unfamiliar questions effectively.
Time Management During the Exam
Effective time management is essential for success. Candidates should first answer questions they find easier, ensuring that these do not consume excessive time. More challenging questions can be addressed later, allowing for thoughtful consideration without rushing.
Using time wisely also includes reviewing flagged questions before submission. Practicing with timed mock exams familiarizes candidates with pacing, reducing the risk of leaving questions unanswered. A calm, methodical approach ensures comprehensive coverage of the exam and increases the likelihood of achieving a passing score.
Developing Problem-Solving Techniques
The JNCIA-Junos exam tests not only knowledge but also analytical and problem-solving abilities. Candidates should approach questions logically, breaking down complex scenarios into manageable components.
For troubleshooting questions, understanding the sequence of network operations, interpreting command outputs, and analyzing configurations is crucial. Developing a step-by-step problem-solving methodology ensures that candidates can handle both theoretical and practical challenges effectively. Regular practice with simulated network scenarios enhances this skill, making it applicable to real-world environments.
Hands-On Lab Scenarios
Lab practice remains a critical component of preparation. Candidates should engage with scenarios that replicate real-world network environments, including configuring interfaces, setting up routing protocols, implementing firewall filters, and troubleshooting network issues.
Examples include simulating link failures to test routing convergence, applying policy statements to control traffic flow, and creating VRFs to segment networks. Practical lab experience reinforces theoretical knowledge and develops confidence in executing commands accurately under exam conditions.
Analyzing Past Exam Experiences
Learning from the experiences of previous candidates provides valuable insights. Online forums, study groups, and discussion boards often include tips on common pitfalls, challenging topics, and effective strategies for preparation.
Understanding areas that frequently pose difficulties, such as routing policy implementation or advanced security configurations, allows candidates to dedicate more time to these topics. Insights from others’ experiences can also highlight useful resources, lab exercises, and mnemonic techniques for memorizing key concepts.
Managing Exam Stress
Exam day can be stressful, and managing anxiety is crucial for optimal performance. Candidates should ensure they are well-rested, well-nourished, and mentally prepared. Relaxation techniques such as deep breathing, mindfulness, and positive visualization can help maintain focus and reduce tension.
Maintaining a confident mindset allows candidates to approach each question methodically, avoiding rushed or impulsive decisions. Regular practice, familiarity with the exam format, and thorough preparation all contribute to reduced stress levels and improved exam performance.
Post-Certification Benefits
Earning the JNCIA-Junos certification provides tangible benefits beyond exam success. Certified professionals gain recognition for their expertise in Junos OS and networking fundamentals, enhancing credibility with employers and peers.
The certification opens doors to entry-level network positions such as network support engineer, network administrator, or junior network technician. With experience, professionals can advance to roles in network operations, network engineering, or enterprise infrastructure management. The credential also serves as a foundation for pursuing advanced Juniper certifications, expanding career prospects and technical expertise.
Professional Development Opportunities
JNCIA-Junos is just the beginning of a continuous learning journey. Certified professionals are encouraged to pursue higher-level certifications such as JNCIS, JNCIP, and specialized tracks in security, data center, or service provider networking.
Participation in workshops, webinars, and online courses helps engineers stay updated with the latest features, best practices, and emerging technologies. Networking with peers through forums, professional associations, and Juniper communities fosters knowledge sharing and career growth. Continuous professional development ensures long-term success and adaptability in an ever-evolving networking landscape.
Networking with Industry Professionals
Building connections with industry professionals provides opportunities for mentorship, collaboration, and knowledge exchange. Engaging with the Juniper community, attending conferences, and participating in local networking groups allows certified professionals to gain insights into best practices, industry trends, and career advancement strategies.
Mentorship from experienced engineers helps candidates navigate complex scenarios, understand advanced concepts, and make informed career decisions. Networking also provides access to job opportunities, project collaborations, and professional recognition, enhancing both technical skills and career trajectory.
Leveraging Certification for Career Growth
Certified professionals can leverage JNCIA-Junos for career advancement by highlighting their skills in Junos OS, routing, security, and troubleshooting. Employers value candidates who can demonstrate both theoretical knowledge and practical abilities.
The certification can lead to higher salaries, increased responsibilities, and opportunities to work on advanced projects. Professionals can also position themselves for specialized roles in network security, service provider operations, or enterprise infrastructure management. Combining certification with hands-on experience ensures that candidates remain competitive in a dynamic IT job market.
Preparing for Advanced Certifications
JNCIA-Junos serves as the foundation for advanced Juniper certifications. Candidates interested in pursuing JNCIS or JNCIP should focus on developing deeper knowledge of routing protocols, network security, and troubleshooting techniques.
Advanced certifications require proficiency in complex scenarios, policy implementation, and multi-vendor interoperability. Building on JNCIA-Junos skills through continuous learning, lab exercises, and real-world experience prepares professionals for these higher-level credentials. A structured roadmap ensures progressive skill development and long-term career growth.
Continuous Learning and Skill Enhancement
Technology evolves rapidly, and continuous learning is essential for maintaining expertise. Professionals should stay current with Junos OS updates, new features, and best practices.
Regularly revisiting lab exercises, experimenting with new configurations, and exploring automation tools enhances technical proficiency. Engaging with online courses, webinars, and certification updates ensures that skills remain relevant and aligned with industry standards. Lifelong learning strengthens professional credibility and prepares engineers for emerging challenges in networking.
Exam Review Techniques
Reviewing material systematically is crucial for exam readiness. Candidates should focus on high-priority topics, practice configuration scenarios, and test their knowledge with mock exams.
Creating summaries, flashcards, and concept maps aids memory retention. Revisiting incorrect answers from practice tests helps identify knowledge gaps and reinforces learning. Consistent review ensures that candidates approach the exam with confidence, clarity, and a thorough understanding of all key concepts.
JNCIA-Junos certification preparation extends beyond understanding commands and protocols; it encompasses exam strategies, hands-on practice, scenario analysis, and professional growth. Effective study planning, time management, mock exams, and lab exercises build the foundation for success.
Certified professionals benefit from increased credibility, career opportunities, and a platform for pursuing advanced Juniper credentials. By combining technical knowledge with strategic preparation and continuous learning, candidates not only achieve certification but also develop the skills and confidence necessary to excel in real-world network environments.
Leveraging JNCIA-Junos for Career Advancement
Earning the JNCIA-Junos certification can significantly impact career growth in networking and IT. Certified professionals demonstrate a solid foundation in Junos OS, routing, security, and troubleshooting, which employers value when hiring for network-focused roles.
Entry-level positions often include network support engineer, network administrator, and junior network technician. These roles provide hands-on experience with real-world network environments, allowing professionals to apply their certification knowledge while building expertise in configuration, monitoring, and troubleshooting.
Mid-Level Career Opportunities
With experience and proficiency in Junos OS, certified individuals can transition into mid-level roles such as network engineer or network operations specialist. These positions involve greater responsibility, including managing larger network infrastructures, implementing complex routing policies, and maintaining network security.
Network engineers often work with multi-vendor environments, requiring integration skills and the ability to troubleshoot interoperability issues. The JNCIA-Junos certification equips professionals with the foundational knowledge needed to navigate these challenges effectively.
Senior-Level Roles and Specializations
Advanced career paths include senior network engineer, solutions architect, or network security specialist. Professionals in these roles are responsible for designing, implementing, and maintaining enterprise-scale networks, often incorporating advanced Junos features such as VRF, routing policies, and zone-based security.
Specialization opportunities arise in areas such as service provider networking, data center operations, and network security. Each specialization requires in-depth knowledge of protocols, configurations, and performance optimization, building on the foundational skills gained through JNCIA-Junos certification.
Exploring Multi-Vendor Networking
Many organizations operate networks composed of multiple vendors’ devices. JNCIA-Junos professionals often collaborate with equipment from Cisco, Arista, or other vendors, requiring interoperability knowledge.
Understanding protocol standards, route redistribution, and cross-vendor troubleshooting enables certified professionals to work effectively in these environments. Multi-vendor expertise enhances employability and positions engineers as versatile problem solvers capable of managing complex infrastructures.
Industry Applications of JNCIA-Junos Skills
JNCIA-Junos knowledge is applicable across a wide range of industries. Telecommunications companies rely on network engineers to manage service provider infrastructure, configure routers and switches, and ensure high availability for clients.
Enterprise IT departments use Junos OS skills to maintain internal networks, segment traffic with VLANs and VRFs, implement security policies, and optimize performance. Government agencies and financial institutions also value Junos-certified professionals for their ability to maintain secure, reliable, and efficient networks.
Real-World Impact of Certification
Certified network professionals contribute directly to organizational efficiency and security. Accurate routing configuration reduces downtime and prevents data loss, while firewall policies and security configurations safeguard sensitive information.
By applying best practices learned during certification, professionals can implement robust network architectures that withstand failures, optimize traffic flow, and provide scalable solutions. Organizations benefit from the reduced risk of network issues, improved performance, and increased operational reliability.
Long-Term Benefits of JNCIA-Junos Certification
The long-term benefits of obtaining JNCIA-Junos include enhanced employability, credibility in the networking community, and a pathway to advanced Juniper certifications.
Professionals gain recognition for their technical expertise and hands-on skills, increasing opportunities for promotions, higher salaries, and specialized roles. Additionally, the certification provides a foundation for continuous learning, enabling engineers to expand into advanced domains such as JNCIS, JNCIP, and Juniper security specializations.
Professional Networking and Mentorship
Networking with peers and industry experts is an important aspect of career growth. Engaging in professional communities, attending conferences, and participating in online forums provides access to mentorship, collaborative opportunities, and insider knowledge on best practices and industry trends.
Mentorship can guide career development, offering advice on advanced certifications, career paths, and skill enhancement. Collaborating with experienced engineers allows for practical insights that complement formal training and certification knowledge.
Integrating Automation and Modern Network Management
As networks evolve, automation and programmable infrastructure are becoming critical. JNCIA-Junos professionals benefit from learning automation tools compatible with Junos OS, including scripts, templates, and orchestration platforms.
Automation reduces repetitive tasks, minimizes human error, and improves operational efficiency. Understanding how to integrate automation into network management enhances professional value and prepares engineers for future-focused roles in software-defined networking (SDN) and network function virtualization (NFV).
Continuous Skill Development
Certification is a milestone, not the endpoint. Ongoing skill development ensures that professionals remain competitive and proficient in emerging technologies.
Activities such as updating lab environments, exploring new Junos OS features, participating in workshops, and engaging with community forums reinforce knowledge. Continuous learning allows professionals to adapt to new network challenges, maintain expertise in evolving standards, and prepare for advanced certification opportunities.
Strategies for Long-Term Career Success
Sustained career growth requires a strategic approach. Certified professionals should set short-term and long-term goals, including pursuing advanced certifications, gaining hands-on experience in diverse environments, and developing soft skills such as project management and communication.
Documenting achievements, maintaining a portfolio of network projects, and seeking challenging assignments demonstrate initiative and competence. Building a reputation as a reliable, skilled network professional enhances visibility and opens doors to leadership positions.
Transitioning to Leadership Roles
With experience and continuous skill development, JNCIA-Junos professionals can transition into leadership roles such as network operations manager, solutions architect, or infrastructure lead. These positions involve overseeing teams, managing projects, and designing complex network architectures.
Leadership roles require both technical expertise and strategic thinking, including resource management, risk assessment, and long-term network planning. Certification provides a credible foundation for technical authority, while experience and professional growth prepare engineers to lead teams effectively.
Preparing for Advanced Juniper Certifications
JNCIA-Junos serves as the foundation for advanced certifications, including JNCIS, JNCIP, and specialist tracks. Candidates should build on their foundational knowledge by mastering complex routing, security, and troubleshooting skills.
Structured preparation for advanced certifications involves deeper study of protocols, hands-on lab scenarios, and exposure to large-scale network environments. Achieving higher-level credentials positions professionals as experts in Juniper technologies and opens doors to specialized roles in data centers, service providers, and enterprise networks.
Real-World Networking Case Studies
Analyzing real-world network scenarios reinforces practical understanding and decision-making skills. Case studies often include traffic optimization, redundant link configuration, multi-site routing, and firewall policy implementation.
Practicing these scenarios helps professionals understand the implications of design choices, troubleshooting strategies, and policy enforcement. Knowledge gained from case studies translates directly to professional environments, enabling engineers to solve complex network problems efficiently and reliably.
Networking Best Practices in Enterprises
Applying best practices ensures reliable, secure, and scalable networks. Certified professionals are expected to implement consistent configurations, enforce security policies, monitor network performance, and maintain redundancy.
Proficiency in Junos OS commands, routing protocols, and security configurations ensures that network operations run smoothly. Following best practices also reduces operational risks, improves service quality, and enhances overall organizational performance.
Conclusion
JNCIA-Junos certification offers a comprehensive foundation for network professionals seeking to establish credibility, develop expertise, and advance their careers. The certification equips candidates with practical skills in Junos OS, routing, security, and troubleshooting, applicable across diverse industries.
Certified professionals gain access to entry-level, mid-level, and advanced career opportunities, including specialized and leadership roles. The credential provides long-term benefits, including professional recognition, skill enhancement, and a pathway to higher-level Juniper certifications. Continuous learning, hands-on experience, and engagement with the networking community ensure sustained career growth and success in dynamic network environments.
ExamCollection provides the complete prep materials in vce files format which include Juniper JNCIA-Junos certification exam dumps, practice test questions and answers, video training course and study guide which help the exam candidates to pass the exams quickly. Fast updates to Juniper JNCIA-Junos certification exam dumps, practice test questions and accurate answers vce verified by industry experts are taken from the latest pool of questions.
Juniper JNCIA-Junos Video Courses






Top Juniper Certification Exams
Site Search: