- Home
- Popular IT Certifications
- How to Deter and Mitigate an Attack Types and Techniques
How to deter and mitigate an Attack: Types and techniques
There are many attacks which can affect the computer performance of the user. But many of them are now known and there are some methods too which can be used to make sure those attacks do not affect the system that bad. Hence one should know about those preventive measures and should try his best to get rid of those attacks threats which can result into some better computer security. Here are some ways through which one can get those attacks ignored;
Monitoring system logs;
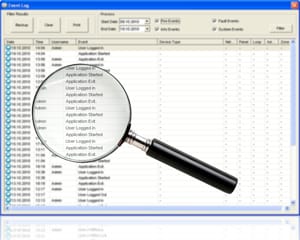
If someone can monitor the logs, he will know what the usual happenings are. Hence he can know if something special happens somehow and he would be able to take some preventive measures for that. Logs motoring are something very important since it can help someone monitor the logs for the sensitive data too and hence can know if there is any breach which has been done within the data. There are some software's too which are available for this purpose. Like one should know that the log monitors is a type of software's which can monitor the files and the logs. Many of the networks, security devices, servers etc. generate the log files. Also, the errors and the problems which happen again and again also generate the logs which can be used for some analysis. So for detecting the problems in automatic way, the administrations normally set up some monitors for the logs. Those mentors can scan the files which contain the log and can search for the text pattern which are known and the rules which can indicate the events which are important/ once an event has been detected, then an alter would be sent to the software or the hard ware system or some person so that he can take some actions on it. Here are some types of the system logs which are available to one;
Event logs: event logs are generated through event monitoring. When some event takes place like some software's has run some program or the data analysis has taken place, then the logs are generated. Event monitoring is he process in which collected, analysis and some other events are occurred like the processes done by the OS. These events may originate form open sources which are arbitrator as well like the hardware's and the software's as well.
Audit logs: Audit log is basically the historic account of all the events which have happened to the computer and they are related to some certain object. Normally, people just keep the logs of the rich target that are managed by some promising server. But there are some problems too, which are related to the audit log monitoring. Like, it is difficult to maintain such logs. One can maintain that log at the target but the management agent talks with the server and hence it can also keep the log as well. So basically question that pops up here is that how can one maintain the log? What types of events should it include and what is event itself? The audit log should be reusable and it should be simple so people can also review it easily and can put up some queries on it. There are some of the cases which can be defined, like the store event. They can be the new log into the audit log. There can be the get events, which mean the queries as the subset of events. There can be the merge events as well which means the new events are merged with some existing events. Hence all these logs are generated and one cane easily keep same track of them to get their hands on some good quality log monitoring of audit.
Security logs: the security log is the log which is used for keeping track of what is happening in the system and all those events relate to the security and the information is then saved and is checked later. It should be easy and readable as well. Hence people will be able to put up some questions and would be able to comment on it as well. There are many logs which are generated on some weekly bases as well. They can be the logs generated through windows security, the security log of the internet connection and the firewall, etc. Stephen Accession said that many of the UNIX installations do not really run any of the forms of security lagging software's, actually. The reason is that the logging files related to security facilities are pretty much excessive and they can cost a lot when it comes to the processing of time, disk damages and hence the costs which are associated to them while analysing the trail of audit. can be done through some software or by manually. In any case, the logs generated can help estimating the damage and its extent.
Access logs: As the name suggests, one should know, that the access log means the list of all the requests for some files which have been requested by the people through the HTML files and whatever is embedded into them. They can vet the associated files, graphics images etc. and they are the files which are transferred. This access log is sometimes also known as the raw data. This data can be analysed and then can summarized by some other person. Normally, this access log can be sued for analysing and telling someone about the fact that how any visits have been paid to some home page and how many of them were the first timers. Also, the visitors' location and the origin are also mentioned in terms of the Doman their server has. Like, there can be the eddo, .com, .up etc. at the bed of the website hence I t can be recorded. Also, it can be there that how many of the requests have been generated for each of the pages and hence which can be sued for presenting with pages with some most requested lists first. Also, the pattern of usage is also logged like the time of the day, the day of the week and etc. Another important thing is, that the those software's who have been keeping logs and have been putting up some analysis for that, they can be found as the shareware located on the website or they might even come with the web keeper.
Hardening

When someone knows that there is some problem and the systems to be guarded well, then he would start putting some restrictions. It is a very good step since it can ensure that the data is not being stolen frequently and hence h can help protecting his precious data that he has on the files. Here are some of the ways through which one can make sure that the security settings are hardened and no one can get access into the computer' files;
Disabling unnecessary services: as it has been mentioned that there can be many applications too which can become the source of the attacks, then first thing that should be done, is making sure that the services which are not necessary are disabled first. This can help someone better since if the UN necessary application is running, one would have to monitor their activities as well and it would take too much time and so many opened things can divert one's attention easily. So closing them down through task manager or any other way can help one getting hold of the system.
Protecting management interfaces and applications: One must be able to protect the interfaces and the applications. The disabling of the applications is very important since they may bring the attack and can be the weak piutn if there is some developing error residing within them. The interface services can also be disabled. There are some global services which can be pretty insecure and they are not so necessary. If someone feels that these services are not so secure, he can disable them and hence can disable them on the router's interface as well. There are some basics which one should know about them first, like there is some caution which one would have to have. Like, there are the loopback interfaces and some null interfaces which are the physical interfaces and are location on the router. So while disabling, they should be disabled as well since it is better to be the safe one instead of being sorry at the end of the day. Any of the interface which is insecure, is basically the one which isn't connected to the internet network that one has. They are the ones which are actually connected to some public network like the internet is connected to it. Also, that one can be connected to some private network, Also; there can be the connection with the private LAN and the remote office.
Password protection: Well, there isn't anything to say too much about this thing, since it is a common understanding that passwords are the gateway to one's accounts and it is something that one has to protect. So one should set some strong asked passwords with some characters in it and if there is any default password, one should simple disable it and set a new one.
Disabling unnecessary accounts: If one imagines, that what will happen if he walks out of the room where computer is, and someone else sits and gets access to the computer through some guest account or some account which is idle. Then one would know how important it is to manage the accounts as well.
Network security
Following are the ways through which one can ensure network security;MAC limiting and filtering: this term means that there can be the access control methods used for disabling the address which are assigned to some network. They are a great tool since these addresses can be used for the taking some access to the described network.
802.1 xs: this standard is used basically for getting access to the network so it should be made sure that this standard is secure so one can stay away from the risk of being exposed to any cyber-attack.
Disabling unused interfaces and unused application service ports: The interfaces which are unnecessary should be disabled since it is clear that they might harm the computer by bringing in the cirrus. Also, there are some ports on the routers which can also be cleared and closed up for secure system.
Rogue machine detection: There can be some rouge machines which can be detected through many methods and hence one cans are guard his interest through getting away from this.
Security posture
Here are some security postured which one should have to protect himself;
Initial baseline configuration: The configuration of the baseline should be done initially so that risks can be minimized.
Continuous security monitoring: Setting up security isn't the only thing, in mist measure and monitor it too to check if it's effective.
Remediation: if there is some problem which occurs, then some steps should be taken like instating some programs to defend the computer.
Reporting:
Here are the reporting methods which can be used;
Alarms: Alarms can alert someone easily so they should be paid notice to.
Alerts: Alters shouldn't be ignored since they carry important messages.
Trends: Trends should be followed to see which cirrus is in these days.
Detection controls vs. prevention controls
There are not only detection controls there are prevention ones as well and they should be done as follows;
IDS vs. IPS: The IPS makes a report when there is some intrusion while IDS doesn't just reports but takes action too so enable the IDS.
Camera vs. guard: The cameras are effective then goads since goads can doze off too but cameras can catch everything in them if kept at secured position.
Hence one can know that one can stay safe from the attacks and all he needs to do is simply keep him safe. He can follow all the steps mentioned above. They will not only keep him secured but will act as a good defence as well.
Site Search:






