- Home
- Popular IT Certifications
- How to Implement Wireless Security Measures
How to implement wireless security measures.

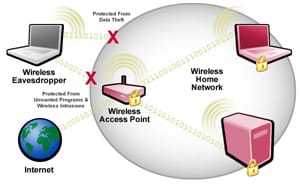
It is hard to believe that the network computers are to increase the security. In reality, the network computers are to share the resources and to address a myriad of threats and security issues. It is possible to address the those threats and security issues using both software and hardware. Anyway, the protocols are specially proposed to mitigate the network security threats. When comes to wireless networks, the word security and wireless are not belonging same category. In fact, few organization first preference for security and then second preference to the wireless networking. An Earlier type of security protocols which was developed for the wireless networks is not offered much security to the networks. The wireless security is the prevention of the damage or unauthorized access to the computers using wireless networks.
Nowadays, the advancements in the new technology are providing possible security to the wireless networks from intruders. But still it is possible to set an unsecure network or the temporary uses. In the below sections, the wireless security configuration and protocols, and its impact on each option. The most common types of wireless security are WiFi protected access and wired equivalent access.
Encryption protocols
An encryption is the old concept that goes days of Pharaoh in Egypt days. The basic idea behind encryption, the message will be coded and can be read by an entity or a person who possesses the right key or decoder. There are different kinds of encryption algorithm in use today. Listed below are some of the wireless encryption methods
WEP
Wired equivalent privacy is one among the first try at the wireless security. It is the first one which is used to secure the wireless connections. The WEP tried to secure a connection by encrypting the data transfers, but Wired equivalent privacy was found never be equivalent to the wired security. In that, the security mechanism which was used to accomplish the encryption was not encrypted. The WEP uses a stream cipher RC4 for confidentiality and CRC 32 checksum for the integrity.
This used the key length, which was 64 bit originally and then it upgraded as 128 bits. The WEP operates at a lower layer of an OSI model and it cannot provide end to end security for the application. Due to these shortcomings, most of the people have selected more sophisticated and newer methods for securing wireless communication. But, some of the innocent and unknowing peoples still using same unsecure protocol.
This WEP protocol proposed to offer security by encrypting data from sending and the receiving devices. There are 2 types of WEP security available such as dynamic and static. The static and dynamic WEP differ in some manner, that the dynamic WEP changes the security key periodically to making it secure more. At the same time, the static WEP uses the same type of security key on the ongoing basis. The new 128 bit encryption in the WEP makes it more robust than previous versions. As the WEP is the static string with characters, it might be compromised by the brute force attack, where the attacker tries all the possible combination of characters until it matches with the WEP key. The most basic line is that the WEP can keep the curious snooper out, however, any of the hacker worth his salt won't have the hard time cracking the WEP security. In the year 2004, with a ratification of a full 802.11i standard as per WPA2, the IEEE announced that both of the WEP-40 as well as WEP 104 have been deprecated as it fails to meet their security goals and requirements.
WPA
The WPA is the Wi-Fi protected access which was proposed to improve the security weakness over WEP and it will be backward compatible with the older devices which is uses the WEP standard. This WPA addressed 2 main security concerns such as enhanced data encryption and authentication. It is generally being installed as the upgrade on the systems that it currently uses.
An enhanced data encryption is the one, in which WPA uses the temporal key integrity protocol, which scrambles the encryption keys with the help of the hashing algorithm. The key is issued the integrity check to determine that they are not tampered or modified during the transit.
With the help of an extensible authentication protocol, WEP regulates the access to the wireless networks depends on the computer hardware and specific MAC address. It is relatively very simple to be stolen and sniffed. The EAP- extensible authentication protocol is built on the more secured public type key encryption systems to ensure that only an authorized network user can access a network.
The WPA includes the message integrity check. It is proposed to prevent an attacker from altering, resending or/and capturing data packets. It replaces the cyclic redundancy check which was used by a WEP standard. The cyclic redundancy check main flaw is that it will never offer a sufficient strong data integrity for the packets it handling. The well tested message authentication code existed to resolve this issue, but it needs much computation has to be used on the old network cards.
WPA2
This WPA2 has replaced the WPA. It requires certification and testing by Wi-Fi, implements a mandatory element of the IEEE 802.11i. The Wi-Fi protected access version -2 is the improved version of WPA. It offers additional benefits than the earlier version. The WPA2 favors the counter mode with the CCMP- cipher block chaining message authentication code protocol. The CCMP will use 128 bit and AES encryption with 48 bit initialization vector. By larger initialization vector, it also increases a difficulty in cracking as well as minimizes the risks of replay. The new AES and CCMP are encrypted based mode with strong security, which was introduced by the WPA2. The WPA2 certification is mostly mandatory for the whole new device to bear the trademark of Wi-Fi.
The advanced encryption standard is the mode of encryption for stronger security as well as longer security keys. The CCMP is based on 802.11i standards and provides the enhanced data cryptographic encapsulation mechanism which replaces TKIP with the security method which is more stronger. It becomes mandatory on the Wi-Fi certified device since 2006. Some of the hardware will not support WPA2 without any firmware replacement or upgrade. The WPA2 uses an encryption devices which encrypts the network with the 256 bit key, the longer key length will improve security over WEP.
WPA enterprise
The WPA enterprise is more properly called as 802.1x for IEEE standard defining that, indicates port based network access control. It is intended for the enterprise networks and needs a radius authentication server. It needs a more complicated set up and however it offers an additional security like protection against the dictionary attacks on the short passwords. The extensible authentication protocol is moreover used for authentication, which is available in different variety of flavors. This WPA enterprise mode is available with both the WPA2 and WPA.
This 802.1x is not specially proposed for the wireless networks and rather it offers an authenticated access for both the wireless and wired network. The access control of port based network depends on the physical characteristic of the switched LAN infrastructure to authenticate device attached to the LAN port to prevent access to where an authentication fails. It is suitable for for organizations ranges from medium to large size. This can serve to enhance the security by allowing to centralize the security policies.
MAC address filtering
In the computer networking, the MAC filtering refers to the security access control method and the 48 bit address are assigned to every network card to determine access to the networks. The Mac addresses are mostly uniquely assigned to the each card, so that using Mac address filtering on the network denies and denies network access via the use of the list, straightforward, an individual is not identified by the MAC address, rather the deice only. So that only authorized person can require to have a whitelist entry for every device that she or he use to access the networks.
Each and every host on the network have 48 bit MAC - media access control address which is generally expressed in hexadecimal. Additionally, each internet packet comprises a source media access control address and the destination MAC address. Sometimes a destination MAC address is the broadcast address includes FF-FF-FF-FF-FF-FF. The MAC filtering can also be applied to the wireless access point as well as configured to allow only some specific MAC address through the interface on the WAP. On the other hand, the user will connect to the wireless access point only, if the users MAC address is configured as the accepted address. It may be a great idea, but never use it only for the wireless security, if really like to have a secured wireless network. With the help of the right software, an acceptable MAC address can be determined easily and spoofed. This can also be done in the command line tools or by using windows registry on the Linux platform. The MAC address filtering is also referred to as security through obscurity. This Mac address filtering is effective in the wireless as well as wired networks.
Device placement
By positioning an antenna, it does not broadcast outside the premises limit access to the people in the premises. The performance is enhanced by keeping the WAP as close to a center of communication area as much as possible. This effective when the radio waves radiate out in all possible directions and hence it is possible to cover more area effectively and provide computers sufficient area in which it can connect if the work take place from the center.
This technique will improve the security of the wireless networks, but in a different method. By keeping the WAP close to a center of the communication area, then it can control the perimeter of a communication area effectively. On the other hand, it is possible to limit the instance in which the wireless area will go further than it had proposed.
Signal strength
Mostly, people don't control a signal strength of the wireless network as an ongoing basis. There is at least no signal strength dial which will turn own or other way. By making use of latest technologies like 802.11n, then they will broadcast it with high signal strength when compared with the earlier technologies. In relation to the security, the additional strength may not necessary. To shape the signal, use directional antennas which allow the device to connect with each other, but don't radiate it in all the directions. In so many ways, the placement of the WAP can affect a signal strength of the broadcast.
This signal strength can also be adjusted to limit the transmission range to limit, how can connect to the AP.
The risks to the users of wireless technology have increased day by day as the service become more popular among users. There are relatively few dangers when the wireless technology was introduced. Later by introducing new security measures it becomes easier and simpler. There are so many various wireless encryption protocols from which can choose. The WPA and WEP are now no longer considered to secure and it should be avoided if perfect security is the main goal. In the WAP2 is considered as the secure protocol and has to be used whenever necessary. For that it is necessary to learn all the protocols to select the perfect one among them.
MAC address filtering control who can connect a WAP based MAC address. These MAC addresses will be easily spoofed and it can also used in conjunction with the stronger forms like WPA2.
Device placement as well as signal strength will go hand in hand. It is possible to change the signal patterns by keeping WAP close to a center of the WAN or by using some specialized directional antennas. The key to maintaining the wireless network security is limited in the area which is used by the them.
Site Search:






