- Home
- Popular IT Certifications
- Configuration Management Documentation
Configuration Management Documentation
Over the past 25 years, the tools which helps to view the best network have tremendously improved. The new technologies have made everything easier and simpler, but it is important that whether you are using old or latest tools, the need of having better configuration management documentation is the same like ever which help to make good decisions about the network. For that it is necessary to learn the things such as wire schemes, baselines, asset management, cable management, documentation and network maps.
Wire schemes
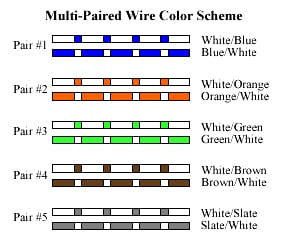
In future, maybe most of the networking will become wireless, but as of now still wiring network is there. In fact, most of the network has some thousands of wring feet, which works its own way around the building. The Wiring is the backbone for any network which comprises of fiber optical cable. It is important that the network administrators must understand the wiring connection and where it from and to. They need to regarding fault tolerant connection as well as changes to a network design.
To grasp the knowledge, most of the companies have to keel their detailed wiring schematics which shows how cable are wired to an entire organization, which is connected with each one and where the cables will be used for the growth.
The network wiring will be confusing one for most of the people who don't have proper knowledge on that. Most of the wiring will hide in ceilings and walls, making it tough to find where the wiring from and kind of wire used on the networks. So that it becomes important to keep documentation about the whole wiring up to date to troubleshoot it as soon as possible. This network documentation includes the information on the wiring between and inside the buildings. It includes information on how many pairs of copper are in a riser cable which interconnects the second and first floors and the number of cables used. Therefore, it should complement of the network physical topology maps.
It is important that the network administrator must maintain those wiring schematics up to date while the changes are made with the network. It is important to label the wires for good practice to make it familiarize.
Network maps
There was a huge difference between the logical and the physical shape of the network. A physical shape is like a looking the network with naked eye and the logical shape defining the method that the packet takes to obtain from 1 part to another part of the network. However, these concepts are something different, then the diagrams which represent, it can also very different.
The physical network map is the one which describes where you have switches, routers, port numbers, location of the network devices, circuit IDs, network equipments, client workstation and servers as well as the cables going to connect the devices. It may look like the wiring schematic, expect the emphasis on the device at the end of the wire rather than a multitude of the wires connecting it. The detailed details about the devices presently being used like capabilities, in service date, IP addresses and so on. This kind of diagram will be used for eventually replacing the outdated equipment or planning the network that is hampering the network performance. The logical network map, that describes the way a traffic takes to receive from 1 router or else switch to another, and might use for troubleshooting also. The network designers will often use multiple paths via various kinds of network devices to offer a fault tolerant routes and load balance the network when it needs. This kind of diagram will normally list the subnet information and IP addresses of the device and also it will take into the configuration of devices accounts such as access list on routers or VLSNs on the switches. If the traffic is not able to receive suddenly from 1 part of the network to the other, then the diagram shows the exact path, then the traffic is to take of great value to the one who troubleshoot the problem.
Documentation
It is important to maintain the documentation as much as possible with up to date information. Any upgrade or replacement of the network equipment is the necessary things and require an update to the physical network diagram. The change in the configuration on a switch or a router such as a new VLAN and the new router interface will require necessary change in a logical diagram. For tracking those changes and its documentation, most of the companies using job logs in that list a change which was made, when it was documented and when it was prepared or made. The Microsoft and other companies are offering software to facilitate the processes. Some of the organization will allot the team member for this job to ensure that the documentation is maintained up to date. Still, everyone has the responsibilities for logging their individual changes, but only one person is always responsible primarily for the whole processes. This will decrease finger pointing as well as headaches. There 2 types of network configuration configuration are essential for the hardware and software documentation.
The well functioning network is characterized by the documented configuration, procedures, regulations and policies.
The policies refer to the organization documented rule about what is done and not done as well as why. This policy indicates who can or cannot access the network resources, backup tapes, server rooms and more. The network policies will provide guidelines and network rules for the network conduct. It is often reviewed and updated and are changed which will reflect on the business requirements. The network usage policy is the policy who can use the network resources such as printers, PCs, remote connections and scanners. No other outside systems are networked without getting proper permission from the network administrators. The internet usage policy is the policy specify the rules and regulations for the internet use on their job roles. Sometimes, incidental personal use was allowed during specific times. The regulations are legal restrictions with the legal consequences. This regulation is not set by the industries, but by applicable laws in a particular area. Improper use of internet and network can lead to the legal consequences and violations.
The documentation is the most important one, because when the administrator who configured the hardware or software become unavailable or absence and some other one has to recreate the configuration without helps but the documentation. To act effectively, the documentation must be as present as possible. The older configuration will never help at any point.
Cable management
The information technology industry has been concern in regards to many cables which are used all over the building. These cables are not large individually or else bulky, but it will become bulky while many cables combined together. The cables have to be physically secured that is normally accomplished with the help of cable trays, cable baskets, cable ties and cable ladders through the cables route. The cable ends and cable must accessible so that the network administrators can able to terminate it to patch panels to allow for the easier changes if the cables should be inoperable or damaged. Basically, in most of the organizations, cables are colored specially or labeled which is used to determine the cable type and also make ongoing cable managements as so easier.
Asset management
The asset management is simply not a technical term and also refers to the system whereby a thing of any values are maintained or monitored. There are so many things associated network systems and network in the things of value. Normally, most components that discussed earlier also has a considerable value. The IT asset management also includes maintenance, updating, standards, process for the procurement, life cycle management as well as eventual disposal of the equipments such as switches, appliances, servers, routers and so on.
As asset management related to the networks, it is the formalized system of managing the life cycle and tracking network components. Some companies defines the life cycle service maintenance model, that defines the distinct phases in network asset life cycle with the help of acronym PPDIOO, it stands for prepare, plan, design, implement, operate and optimize.
Baselines
If the doctor conveys that the temperature of the body is 104 degree Fahrenheit, then it indicates that the person has a fever. The normal temperature for the healthy human being is 98.6 degrees, so that anyone can determine that the person whose temperature is above the particular limit is considered as normal. It is an indication for the abnormal. Like that, there was a normal readings available for the network also, but it is so simple like degrees. In fact, the normal readings are customized to a particular type of network and even for the specific networks.
There are 4 lifeblood resources available to any device on the network or any network such as memory, processor, network subsystem and disk subsystem. The serious weakness in the network resources will easily affect or spread any other resources. While the lack of resources will cause this kind of problem, and it is normally referred as a bottleneck. It is important to know how to prevent these bottlenecks like that preventing fever before it attacks. It is important to understand what networks like in regards to those resources and when it was healthy so that it is easy to find what to make change while it is not. The record of measurement taken by the network diagnostics as well as system monitoring equipments while the networks are healthy, then it is referred as the baseline of a network. Although the network is similar to the other network, no 2 networks will be exactly same and it is important to have this baseline for the network.
Normally, these baselines are always stored in the log files which are accessible to a network administrator when it is needed for the comparison.
This baseline is the measure of performance which implies how hard the network was working and also where the network resource are spent. It is important to compare the baseline details at the time while the network face problem to record information when the networks was operating with higher efficiency. This comparison helps to determine whether there was a problem with the network and how significant the problem is and where the issues lies.
Change management
Generally, most of the organizations will determine their own policies for configuring, managing and designing own networks. These types of procedures and policies have to be created by network team who knows about the system and must be signed off by the high category management authority like executive of that company. They must reflect the goal of the company to disaster recovery, network connectivity, security, fault clearance and much more. Each and every company have to decide what is essential to them. After the procedures and policies are in place will correct configuration be administered and initiated by a networking team.
To make changes in the network, like upgrading the operating system on the router requires the network outage of 15 minutes, realize that the actions can impact the business operation. Hence, most of the large companies institute the change management system that is commonly available in the form of software used by the network administrator to alert the other network administrator about the upcoming changes in the networks. By viewing the outage of the network, the other network administrators can provide feedback to the originator of notification. Then the 2 network administrators will then select different time to implement a planned change.
It is essential to understand the various network documents and the use of physical diagram, network documentation, baseline, wire scheme and logical diagram. Additionally, it is important to update the network documentation in a regular period of time or any replacement or repair take in the networks. Understand the consistent and frequent needs to update the network documents and logs which are used to track the changes of the network and has to record the changes in each document.
Site Search:






