- Home
- Popular IT Certifications
- Comparing OSI and TCP Model
Comparing OSI and TCP/IP models
The OSI and TCP/IP Models are the most widely known models involved in the process of networking. They define a lot of foundation rules which are used in the process of networking. While the TCP/IP model is the standard model which is used in the modern day, the OSI model quite old but is used to study and understand the concepts of networking. Most of the protocols defined in OSI model are used in TCP/IP model. While OSI Model comprises of 7 different layers, TCP/IP model comes will only 4 layers which are more specialized and developed on modern platforms.
OSI Model
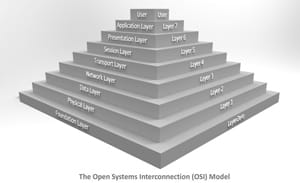
The OSI model is known as Open Systems Interconnect model. OSI is one of the most traditional methods of networking that formed the base of protocols. OSI is not used today as a primary model, although some of the protocols today are based on it. The OSI model is defined by 7 different layers. The existence of these seven layers tended to distinguish between each process that occurred and to enable the model to run smoothly. Each layer in this model serves the layer which is above it and is facilitated by the layer below it. This provides an effective path to the data packets to get transferred from one layer to the other. These seven layers are further divided in two categories. The first 3 layers lie under the category of "Media Layers" while the remaining four lie under the category of "Host Layers".
Following are the 7 layers that form the base of the OSI model.
Physical Layer: This layer is the first one in the OSI model. The responsibility for determining the physical requirements for the transferring of data lies on this layer. First of all, this layer reads all the data signals in digital form. At this instant, the data will be in the form of 0s and 1s, which is the binary form of data. The physical layer will determine whether the data needs to be transmitted into analogue form or not. It will also determine the physical requirements of the connection; the number of pins switches and ports which are required for the connection to work properly. The amount of electrical voltage required will also be judged at this point to ensure the smooth flow of the whole process. Depending on the physical medium of transmission, this layer will also sort out whether the signals have to be converted into electrical signals or optical signals.
Data-Link Layer: The primary purpose of the Data-Link layer is to scan the data for any errors in order to correct it, and establish a smooth connection between the Physical and Network layer. It will be checking all the data packets to make sure that they are complete and no data has been lost up till now. If it finds any problem, the data packets will be sent back to the physical layer for correction. In fact, it is the responsibility of the Data-Link layer to define all the rules that when the data can be sent by the device over a medium. Moreover, the Data-Link layer will also make sure that the data is sent and received by the devices in a smooth manner.
Network Layer: Depending on the conditions of the network, the network layer will decide that which physical path should be taken by the data. In this regard, it will enable the data to choose the best path where there will be minimum amount of loss of data packets. At this layer, the logical addresses will be converted into physical addresses to determine the path which the data has to follow and specify its destination. If the router receiving the data has got any problems, the Network layer wills the hold data for that time until the path is clear. In fact, Network layer is the most important layer where most of the integral processes will take place. It is also the responsibility of the network later to minimize the data traffic by allocating the most probable route to each data packet and enable it to reach the destination in least amount of time.
Transport Layer: It is the responsibility of the transport later to make sure that the data packets are delivered to their destination without any loss or modification during the path. In addition, it also makes sure that the data sequence has been maintained and there is no duplication of data; the data reaches the destination as accurately as possible. It should also be kept in mind that if the network layer does not cater to the issues of security, it is the responsibility of the transport layer to make sure that the data is secure enough to be transmitted. The transport layer also receives the messages in its original form and breaks them into small packages for transmission. The boundaries of the messages are also determined to make sure that they are received in the prescribed order. In fact, some transport layers number the data packets in the specified order to make sure that the sequence and number of data packets is conserved.
Session Layer: Session is basically an establishment of a connection between two applications running on different devices. Thus, Session layer makes sure that this connection between the two devices is established effectively. It provides the methods for starting and ending various conversations and makes sure that the data is received and sent simultaneously. It will also determine the security measures for this connection and recognize various other features of this connection. It also gives signals when the messages have been transmitted successfully. Session layer basically takes all the measures before the messages are transferred to the presentation layer.
Presentation Layer: The primary purpose of the presentation layer is to define and present the data formats to the Application Layer. In fact, it acts the purpose of a translator by converting the data into a suitable format to be read by the Application layer. There are a number of important steps which are carried out in the Presentation layer. First of all, it has got the ability to convert data into a number of different formats including ASCII, binary, JPEG etc. In addition to this, it determines the order of the bits according to the requirement. It is also the responsibility of the Presentation layer to make sure that the data is transmitted quickly. Hence, it compresses the number of data bits which are supposed to be transferred over the network. Most importantly, the encryption of data is done at this layer. The process of encryption is done due to prevent the data to be read by any intruder and make sure that it reaches the destinations without being changed or modified. For example, the password can be encrypted by the presentation layer.
Application Layer: Application layer is the final layer in an OSI model. This layer provides an interface between the application and the communications software. It provides the final messages in digital form to the user. This is the layer which will actually have a direct connection with the user. There are a number of tasks which are carried out by the Application layer. The user will be able to use a number of facilities including electronic messaging and inter-process communication. The user is also given the facility to access files and printers remotely and sends instructions through this interface. This is the layer which will actually display all the features to the users and will provide them an interactive interface.
TCP/IP Model
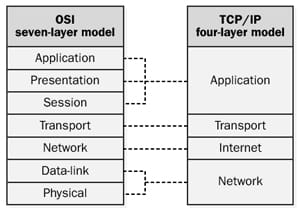
Transmission Control Protocol (TCP) / Internet Protocol (IP) Model is widely used in the modern day as a model for networking. It is termed as one of the most secure and reliable models and is used as a form of networking in most of the areas. Although some of the protocols used in the TCP/IP Model have been inspired from the OSI model, most of the protocols are of its own. The TCP/IP model comprises of four different layers which interconnect which each other to carry out the task of data transmission effectively. The TCP/IP model is reliable enough to ensure the secure transmission of data packets and ensures that there is minimum loss of data. This model can be thought of as a simplified form of the OSI Model, with less and more dedicated number of layers. All the processes, starting from the sending of the data to its receiving will be catered by the layers of this model. The reason for the popularity of the TCP/IP model is its versatility and reliability.
Following are the four layers which are included in the TCP/IP Model.
Network Interface Layer: This is the first layer in the TCP/IP protocol. The responsibility of initiation of the whole process lies on this layer. There are basically two processes which this layer looks after. Firstly, it has to cater to the physical requirements of the system. Secondly, it has to deal with the organization and transfer of data for the Internet Layer. It will determine that how the data is supposed to be sent over; electrically or optically. It also has to make sure what physical devices will be needed for the process, for example the number of pins, ports and wires. Before sending the data, the Network access layer will make sure that the traffic is minimized on each wire and the data is sent in an effective manner. This is the layer where the data will be converted from digital to analogue form for transmission over the wires and then the network. In addition to this, it will also the responsibility of the Network Access Layer to make sure which protocols are supposed to be used over the network and what other hardware is required. The most important protocol for transmission is generally Ethernet.
Internet Layer: This is the second layer in the TCP/IP Model. The primary purpose of the Internet layer stands to ensure that the data packets are converted into IP Datagrams and are good enough to reach their destination. In order to accomplish this, each IP Datagram is given an address where it has to reach. This address is generally the IP address of the receiving machine. However, this layer does not ensure the receiving of data in the specified order. The sorting and sequencing of data in the correct order is the responsibility of all the higher level Layers. During this process, each data packet is set to get independently to its destination to ensure that there is no loss of data. There are few protocols used in this layer, while the most famous protocol is the IP (Internet Protocol). UDP (User Datagram Protocol) is also used at some instances, although it is used in cases where the security of data is not a delicate issue.
Transport Layer: This is the third layer in the IP/TCP Model and holds a great amount of significance. The primary purpose of this layer is to transport the data and send it over the transmission line. There are a number of tasks which are associated with this layer. It is the responsibility of the Transport Layer to ensure that data packets reach their desired destination. In addition to this, it also makes sure that the data packets are accurate and Error-Free. This is done by checking the sequence of the data packets to make sure that there has not been any replacement, addition, deletion or amendment. There are various methods to approach this process. If there is any error, the data packets are corrected while passing through the Transport Layer. This layer also facilitates the simultaneous communication; it allows the data packets to be received and sent at the same time. There are only few protocols used during this layer, prominently TCP and UDP. TCP is used where secure connections are quite essential whereas UDP is used in situations where the amount of data is large but its security is not an issue.
Application Layer: This is the final layer in the TCP/IP protocol. The main purpose of this layer is to provide an interactive interface to the user which will be used to provide a number of facilities. The protocols used in this layer provided all the services to the application software which is running on a computer. This is the layer which actually displays all the data to the user in a digital form. In addition to this, this layer also supports the user to send and receive data simultaneously with the help of all the layers below it. Application layer defines the path through which the programs on the computer can communicate directly with the Transport Layer.
As we have discussed above, each layer in the OSI or TCP/IP model holds great significance. Each of the layers is responsible to make sure that the process of networking is fluent and there is not any problem. There are various protocols which are used in this process and which define the basic rules for networking. It is through the collective functioning of these layers and the protocols within them which make these Models so perfect.
Site Search:






