- Home
- Popular IT Certifications
- How to Troubleshoot Router Security Features
How to troubleshoot router security features
Shield against dangers, for example, malware, interruptions, and dissent of-administration assaults while keeping up elevated amounts of system and limb office execution with Cisco Integrated Services Routers (ISRS) and Cisco Aggregated Services Routers (ASRS). Hence knowing about this key feature is a must for every candidate willing to have good future in field of networking.
Having an open remote system might be a security chance as it may permit any individual who is close enough to your switch (e.g. a neighbor or somebody war driving) access to your system. To make your home remote system more secure consider the beneath suggestions. If you have never been provoked for a key, watchword, or passphrase when associating with your remote system it is an open system, significance anybody close enough to your switch could join with it and peruse your system. To empower security, open your switch setup screen and search for a Wireless Security area. The picture demonstrated a case of a Linksys switch setup in the Wireless and Wireless Security segment.
Select the remote security system for either WEP or WPA (we propose WPA as said later) and enter the passphrase to produce the keys. In the wake of empowering security on the switch, any remote gadget that needs to associate must have the key keeping in mind the end goal to interface with your network. Make beyond any doubt the switch secret key is not still situated to the default watchword. In the event that the secret key could be speculated this could give somebody get to the switch setup, which could permit them to change your switch settings, including review any security keys. Many switches today will offer two diverse security plans: WEP and WPA. We propose WPA security, since it is more secure than WEP. In any case, for similarity with some more seasoned gadgets, for example, gaming supports, TiVo, and other system gadgets might just have the capacity to utilize WEP, and WEP is superior to no security. When empowered, remote organization permits anybody close enough to your switch to view or change your switch settings. In the event that you never anticipate remotely administrating your system, e.g. remote interfacing with the switch, we suggest crippling remote organization. With switches that help this choice, it is frequently crippled through the Administration area. After incapacitated, the switch settings can at present be changed utilizing any machine joined with the switch utilizing a system cable. The SSID is the name that distinguishes your remote switch. Of course, numerous switches will utilize the name of the switch as the default SSID, for instance, Linksys switches use "Linksys" as the SSID. This is a security hazard since it distinguishes the brand of the switch and would tell any assailant instantly what adventures to use. Many switches likewise have their own particular firewall that might be empowered. On the off chance that accessible, we additionally recommend empowering this gimmick as it aides include an additional layer of security for your network.to help make discovering your remote system simpler remote switches telecast your SSID, which implies anybody searching for a remote switch could see your SSID. To help make it more troublesome for somebody to discover your system when perusing for a remote system you can impair the SSID show characteristic. On the other hand, when debilitating the SSID telecast it will oblige that you physically enter your novel SSID when needing to unite any new gadget to your network. The Wireless MAC channel emphasizes just permits a remote gadget to interface with your switch if the MAC Address has been entered into the channel list. This can make associating new gadgets to your system more troublesome, however enhances the general security of your remote network. A snappy and simple to set this up is to unite any remote gadget you need on your system to your switch before empowering remote MAC channel. After every gadget has effectively associated, open the DHCP customer table, regularly found in the Status or Local Network area. Each one gadget that has joined with your switch hitherto is seen and could be replicated into a notepad and glued into the Wireless MAC channel area of the switch Security segment. Cisco coordinated administrations switches ship with the business' most complete security administrations, keenly inserting information, security, voice, and remote in the stage portfolio for quick, versatile conveyance of mission-discriminating business applications. The Cisco 800, 1800, 2800, and 3800 Series switches are perfect for little organizations and endeavor limb business locales, conveying a rich, coordinated answer for uniting remote work places, versatile clients, and accomplice extranets or administration supplier oversaw client premises gear (CPE). Many Cisco items Series Integrated Services Routers and the Cisco ASR 1000 Series Aggregation Services Routers, Cisco 7200 Series Routers, and Cisco 7301 Routers are essential segments of the Cisco Self-Defending Network (SDN), a compositional result intended for the advancing security scene. Security is coordinated all around, and with the assistance of a lifecycle administration's approach, your endeavor can plan, actualize, work, and improve system stages that guard discriminating business forms against assault and disturbance, secure protection, and help arrangement and administrative agreeability controls. With Cisco IOS IP Security (Ipsec) and Secure Sockets Layer (SSL) VPN, firewall, substance sifting, and IPS, and additionally alternatives for extra fittings quickening for a hefty portion of those security characteristics, Cisco coordinated administrations switches give a powerful and versatile security answer for the extension office. Cisco SDN Integrated Security changed system security by making each system component a state of safeguard, including switches, switches, machines, and endpoints. Built for conveying secure administrations, the incorporated administrations switches offer an imaginative mixing of both fittings quickened and programming security characteristics. Accessible in a mixed bag of arrangements, switch security packs give an important and simple approach to ensure the system establishment as security turns into an indispensable and principal system capability. Built-in VPN encryption speeding up comes standard on the Cisco 800, 1800, 2800, and 3800 Series Integrated Services Routers, however obliges a Cisco IOS Software Advanced Security or higher list of capabilities to empower it. Ipsec Data Encryption Standard (DES), Triple DES (3des), and Advanced Encryption Standard (AES) 128, 192, and 256 are supported. The Cisco 800, 1800, 2800, and 3800 Series Integrated Services Routers were composed with installed USB 1.1 ports, empowering vital security and capacity abilities. These capacities help to secure client validation, store removable qualifications for creating secure VPN associations, safely convey arrangement records, and give mass blaze memory stockpiling to documents and design. Exploiting these USB ports, USB E-Tokens can give secure setup circulation and permit clients to store VPN qualifications for sending. USB streak memory permits clients to store pictures and setups.
Secure Wireless LAN Services
The secluded Cisco 1800, 2800, and 3800 Series, and additionally the settled arrangement Cisco 850, 870, and 1800 Series Integrated Services Routers, offer an extensive suite of secure, undertaking class remote administrations to empower benefit improvements at remote venture limb business locales, SMBS, Wi-Fi hotspots, and teleworker locations. The VPN AIM for the Cisco 1841 and Cisco 2800 and 3800 Series Integrated Services Routers enhances VPN execution for both Ipsec and SSL VPN arrangements. It gives up to 40 percent better execution for Ipsec VPN over the inherent Ipsec encryption, and up to double the execution for Cisco IOS SSL VPN encryption.
Cisco Intrusion Prevention System Advanced Integration Module and Network Module
The Cisco Intrusion Prevention System Advanced Integration Module (IPS AIM) and IPS Network Module (IPS NME) for the Cisco 1841 and Cisco 2800 and 3800 Series Integrated Services Routers brings fittings based interruption aversion to limb business locales and little organizations. With the continually expanding unpredictability and advancement of security dangers, each purpose of the system might be at danger. Cisco IPS can precisely recognize, group, and stop malevolent movement, including worms, spyware, malware, adware, system infections, and application misuse. Vigilant assurance aides guarantee business progression and minimize the impact of exorbitant interruptions. Running Cisco IPS Sensor Software, the Cisco IPS AIM can screen up to 45 Mbps of activity and is suitable for T1/E1 and T3 situations. Cisco IPS AIM interoperates with an assortment of Cisco IOS Software security characteristics.
Cisco NAC Network Module
The Cisco NAC Network Module brings the peculiarity rich Cisco NAC Appliance Server abilities to Cisco 2800 and 3800 Series Integrated Services Routers. The Cisco NAC Appliance (some time ago Cisco Clean Access Server) is a quickly deployable NAC item that permits system heads to verify, approve, assess, and remediate wired, remote, and remote clients and their machines before permitting clients onto the system. The reconciliation of Cisco NAC Appliance Server capacities into a system module for incorporated administrations switches permits system managers to deal with a solitary gadget in an extension office for information, voice, and security necessities, decreasing system intricacy, IT staff preparing, gear saving prerequisites, and support costs.
Troubleshooting and Monitoring:
In screen mode, Cisco SDM gives a fast, graphical status of essential switch assets and execution estimations, for example, the interface status (up or down), CPU, and memory utilization (see Figure 4). For remote models, Cisco SDM gives far reaching backing to continuous 802.11 a/b/g interface facts. Cisco SDM exploits incorporated routing and security emphasizes on switches to give inside and out diagnostics and troubleshooting of WAN and VPN associations. Case in point, while troubleshooting a fizzled VPN association, the Cisco SDM checks the switch setups and network from the WAN interface layer to the Ipsec Crypto Map layer. While testing arrangement and remote-peer integration at each one layer, Cisco SDM gives pass status, conceivable reasons of disappointment, and Cisco TAC-proposed activities for recuperation.
IPv4 access control lists (standard, extended, time-based)
Cisco MDS 9000 Family switches can course IP form 4 (Ipv4) movements in the middle of Ethernet and Fiber Channel interfaces. The IP static directing peculiarity courses activity between VSANS. To do in this way, every VSAN must be in an alternate Ipv4 sub network. Every Cisco MDS 9000 Family switch gives the accompanying administrations to system administration frameworks (NMS):
- IP sending on the out-of-band Ethernet interface (mgmt0) on the front board of the administrator modules.
- IP sending on the in-band Fiber Channel interface utilizing the IP over Fiber Channel (IPFC) capacity IPFC defines how IP edges could be transported over Fiber Channel utilizing exemplification strategies. IP casings are typified into Fiber Channel outlines so NMS data can cross the Fiber Channel system without utilizing an overlay Ethernet system.
- IP Routing: (default directing and static routing)-If your arrangement does not require an outer switch, you can arrange a default course utilizing static routing.
Switches are consistent with RFC 2338 benchmarks for Virtual Router Redundancy Protocol (VRRP) characteristics. VRRP is a restart able application that gives an excess, exchange way to the entryway switch.
Ipv4 Access Control Lists give fundamental system security to all switches in the Cisco MDS 9000 Family. A channel contains the tenets to match an IP parcel, and if the bundle matches, the guideline likewise stipulates if the bundle ought to be allowed or denied
IPv6 traffic filter
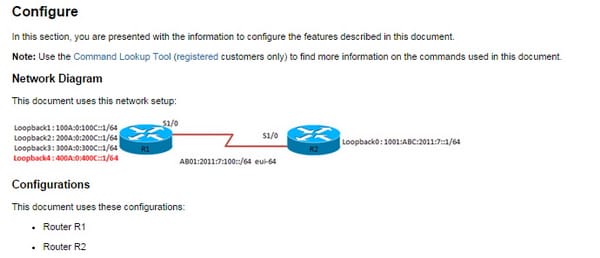
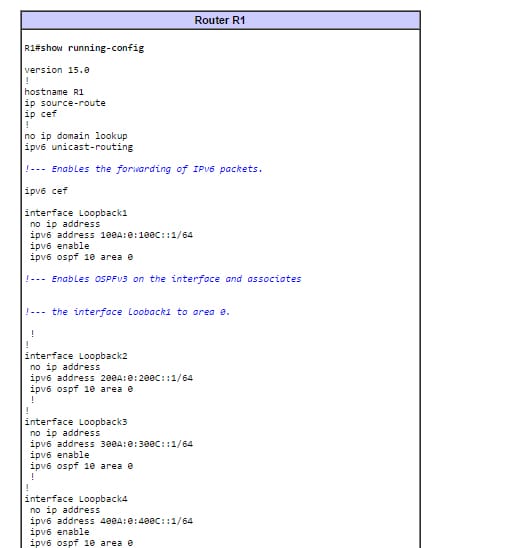
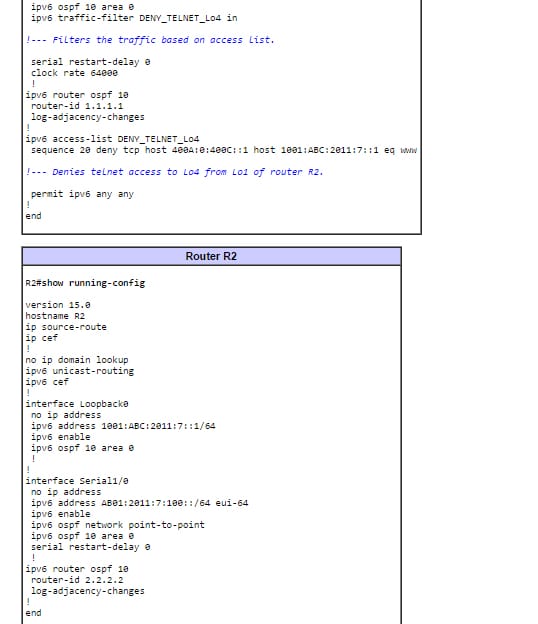
In the sample portrayed in this report, switches R1 and R2 are designed with Ipv6 tending to plan and associated through serial connection. The routing protocol empowered on the two switches is Ipv6 OSPF, and the loopback locations arranged on both the switches (R1 and R2) are publicized to one another in territory 0 with this order: ipv6 OSPF process-id region id. In this illustration, it is obliged to deny telnet movement that begins from the loopback 0 interface of switch R2 and ranges loopback interface 4 of switch R1.
Unicast reverse path forwarding
System directors can utilize Unicast Reverse Path Forwarding (Unicast RPF) as far as possible the malevolent activity on an undertaking system. This security gimmick meets expectations by empowering a switch to confirm the reachability of the source address in bundles being sent. This ability can restrict the presence of mock addresses on a system. On the off chance that the source IP location is not substantial, the parcel is tossed. Unicast RPF lives up to expectations in one of three separate modes: strict mode, detached mode, or VRF mode. Note that not all system gadgets help every one of the three modes of operation. Unicast RPF in VRF mode won't be secured in this record. At the point when directors use Unicast RPF in strict mode, the parcel must be gotten on the interface that the switch would use to forward the return bundle. Unicast RPF designed in strict mode may drop honest to goodness movement that is gotten on an interface that was not the switch's decision for sending return activity. Dropping this honest to goodness activity could happen when halter kilter directing ways are available in the system. At the point when directors use Unicast RPF in detached mode, the source address must show up in the directing table. Heads can change this conduct utilizing the permit default alternative, which permits the utilization of the default course in the source check process.
The router is very important part of the network since it is the key gadget which helps us getting connected to the internet. So learning about its security can bring much benefit to the candidates giving any exam so they can utilize this knowledge in practical field as well.
Site Search:






