- Home
- Popular IT Certifications
- Applying Changes to the Network
Recognize the proposed changes to the network
It is essential to recognize the changes to a network to operate the network without any issues. By learning the changes and impact or effect of the existing network infrastructure, one can able to perform the tasks in a better way. In the following sections, let us see the about the changes to routing he protocol parameters, migrate parts of the network to IPv6 and routing protocol migration.
1.6.a Changes to routing protocol parameters
The routing protocol helps to specify how routers communicate with the each other which enables to select routes between any 2 nodes on the computer network. The routing protocol will share the information among the immediate neighbors at first and throughout the network. In this way, the routers gain the knowledge of the network topology. The routing protocols can be classified mainly into 3 different groups such as behavior, operation and purpose.
The changes include things such as metrics, redistribution, additional routes. The right selection of the routing protocol for the network is mostly sensitive tasks and difficult to understand in some cases. It is essential to consider many factors, ranging from the speed of convergence and protocol scalability via the advanced feature, ends with the compatibility problem, particularly in the multi vendor environment, all are related to the network requirement and design only. As the networks evolved, it may become need to reevaluate a choice of the particular routing protocol. If it is defined as inappropriate, then it required to be replaced.
The migration from the 1 routing protocol to the other is mostly the disruptive change to a network. It needs the careful planning to reduce the outages as well as even, it was inevitable, however its duration can be maintained very low. Hence, the routing protocol migration always needs the maintenance window.
The point to point protocol is the form of serial line data encapsulation. It can negotiate the connection parameters like speed along with an ability to support the CHAp and PAP use authentication.
The routing protocols are most often used in the implementation of the routing algorithms to offer the facility to exchange the routing information in between the networks, which allows the routers to build the routing table dynamically. In some instances, the routing protocols will run over routed protocols themselves. If the BGP run over the TCP then take is important in the implementation of that system for not to create the circular dependency between the routed protocols and routing protocols.
The routing metric is one of the parameters which consist of the value used by the algorithms to examine to choose one route over the other. The metrics take into consideration such information like delay, bandwidth, load, MTU, cost, reliability, MTU, and hop count. A routing table stores, the best routes which is possible, when the topological databases or link state may store all the other information well.
The border gateway protocol routes traffic in between the autonomous systems. It is the very scalable and robust routing protocol. To gain the scalability, the BGP uses the many routes parameters such as attributes which helps to define the routing policies as well as keep the routing environment.
1.6.b Migrate parts of the networks to IPv6
IPv6 is the next generation protocol, which is the only internet protocol in use. Even though IPv6 is not al compatible with the IPv4, to ensure the business continuity and growth, all the organizations require to carefully plan for the coexistence between the IPv4 as well as IPv6. There plenty small business that runs with the IPV6 phase.
There are so many factors involved in the migrate parts of the networks to IPv6. As the technology moves forward with the recent technology with the new standard, the migration to IPv6 is an important one in the day to day tasks. For the most part, the migration to the IPv6 will take associated planning and time to assure the integrity of the existing networks. It will need to upgrade or replace the older equipment such as routers, switches, firewalls, endpoint devices and also other security elements.
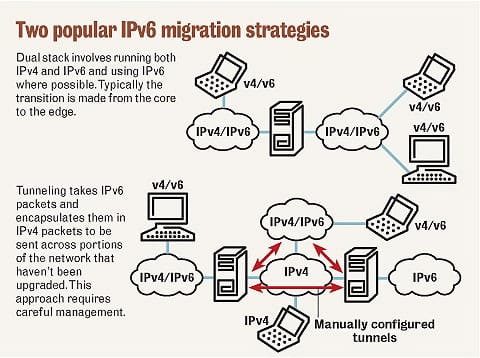
This migration mainly involves looking at the IPv6 transition mechanism such as toredo, Dual stack, ISATAP, 6 to 4 tunnels and much more. It also includes the I,pact on the existing interoperability, services and etc.
In that the Teredo is the mechanism in the windows systems which is used to provide the single system behind the IPv4 Nat access to the IPv6. Like version 6 to 4, it uses the public relays. The teredo combines it with the setup protocol with the help of teredo servers to detect and break via the IPv4 NAT. This is not all reliable but the teredo is used when the explicitly connected to the IPv6 address and not while connecting to the hostname and also looking for the DNS addresses. It happens while using the BitTorrent and the lesser reliability is not a big matter.
The IPv6 transition mechanism is the technology which facilitates transitioning of the internet from the current or initial infrastructure to a successor addressing and the routing system of the IPv6. The IPv6 is not able to interoperable directly, this technology is designed to permit the hosts on either the network to allow the networking with the other networks. The tunnel broker combines the several IPv6 mechanisms of migration and also enables the users to use it. This transition is provided by the tunnel broker is the IPv6 in IPv4 tunneling, with the help of the 6in4, AYIYA or TSp tunnels.
1.6.c Routing protocol migration
The routing protocol is the protocol used by the router to identify the appropriate path over which data is transmitted. It also specifies how the routers in the network share the information with one another and report changes. This protocol enables the network to make the dynamic adjustment to its condition. Hence the routing decisions cannot be predetermined and static.
Each routing protocol is assigned a default AD- administrative distance. This term is something of the misnomer and instead of effecting any of the metric calculations within the protocol, the AD is simply the way to prefer 1 routing protocol over the other. If the router has learned of the route through both EIGRP and OSPF. In certain case, it will prefer a route learned through the EIGRP regardless of the metric because the EIGRP has the lowest default administrative distance. The defaults can also be modified by the any number lies in between 1 to 255. It can especially handy while migrating from the 1 routing protocol to the other. Suppose, migrating a network from the Is IS to the OSPF. As default, the routers will start to follow the OSPF routes as soon it is done within the single maintenance window to omit the disruption, which is really tough in pratical, especially on the larger networks.
The routing protocol migration will always need the maintenance window. This routing migration is generally established in the below steps:
- Plan the strategy for migration
- Activate a new routing protocol on the entire router in a topology, raising the AD above the AD of a current IGP. If a new IGP is the EIGRP or RIP, the redistributions from a current into a new IGP needs to be configured on every router also. A current IGP is the left intact.
- Verify a new IGP adjacencies and an optional working database content.
- Deactivate a current IGP in the gradual fashion.
- Remove all the temporary settings from a new IGP
In the above, planning the migration strategy is more important than anything. The deployment of the new routing protocol must pre planned for all the network, such as split of the network as areas if the link state IGP has to be used, filtration or prefix summarization, external information redistribution and stub features and much more. This type of planning must involve the right order in which the routers will be migrated through from a current IGP to a new one. In the ideal, the router has to be migrated so that it forms the contiguous and ever growing part of a network running a new IGP, then shrinking the contiguous remainders of a network in which both the new and current IGP are run gradually. If a current IGP is the link state protocol, then it is advisable to do the migration in the per area fashion. A backbone routers must be the last one to migrate.
The routing protocol migration includes the manipulating metrics, administrative distances and redistribution and much. In order to migrate, it is essential to determine the EIGRP or IGRP network design and scope of OSPF areas, according to the number of the EIGRP or IGRP routers. According to planning the migration, the new IGP must be activated on a router in a network, the first setting its AD to higher value than a current Ad of IGP, and only adding the networking and interfaces to a new IGP and also activating the selected features. A current IGP is kept running and the configuration remains constant throughout the entire steps. If a current IGP uses the different administrative distance for the various network types, a new administrative distance of IGP has to be reconfigured as higher that of the AD which is used by an existing IGP. The new IGP can also be deployed over a network, making adjacencies between the routers as normal, but it will never influence the routing and routing table simply yet. If a new IGP is the distance vector type routing protocol, then every router must be configured with the redistribution from a current IGP into a new IGP. After a new IGP configuration over all the networks, it must create adjacencies in usual fashion despites a routing table is not populated by the routes yet. Those adjacencies must be verified to ensure the completeness. After IGP is deactivated, the adjacency is the only routing protocol adjacency kept left in between the migrated routers. It has to work as expected before a current IGP begins being removed. It is recommended to check the working database content in a new IGP to analyze whether all the expected networks are there or not. As the result, if a new IGP is EIGRP or RIP, then the working database can contain partial content only until the migration begins inducing the verification before the migration impossible. After this stage, the routing protocol migration will involve removing or deactivate the current IGP from the contiguous set of the routers. Then finally, remove all the temporary settings from a new IGP.
With migration by means of redistribution, then the migration is staged as the series of smaller steps. In the every step, the part of the network will convert from the old to a new routing protocol. In the huge networks, the approach with AD might use to support that type of conversion. In the smaller network, the simpler approach or an overnight cutover is sufficient. To offer the full connectivity at the time of migration by redistribution, then a boundary routers in between the 2 parts of a network has to redistribute bidirectionally between the protocols. The filtering through the tags is one among the simple method to manage this when compared to others. A boundary routers will move as more as possible about the region is migrated.
The network has become the critical resource and the organizations requires strategies to strengthen the continuity as well as to improve the network. It includes the capability to predict, avoid as well as lessen the costly network effects and service disruption and provides the confidence to adapt the networking to face the changes. It is very, very essential to recognize the proposed changes to the network. It has been carried out different techniques such as routing protocol migration, migrate parts of the network of internet protocol version -6 and changes to the routing protocol parameters. This technique will help a lot to diagnose the effect and also gives effective knowledge to avoid the problems. This will make the greatest impact on the network as well.
Site Search:






