- Home
- Popular IT Certifications
- Device Security With IOS AAA, TACACS+ & RADIUS
Describe IOS AAA using local database and device security using IOS AAA with TACACS+ and RADIUS
The local AAA server features allow to configure the router so that the user authentication and the authorization attributes available currently on the AAA servers available locally on the router. An attribute can add to the existing framework, including subscriber profile or user database. A local AAA server offer access to a complete dictionary of the Cisco IOS supported attributes. The local database may act as the fallback method for the several functions. In this section, let us see the device security using AAA with RADIUS and TACACS+ and the local privilege authorization fallback.
5.1 Describe IOS AAA using local database
The IOS local AAA is one of the feature which is often overlooked for some reason. It also allows the router into the full functional AAA server, allowing not simply the local authentication of the remote VPN users and also local authorization for the protocols such as PPP or IKE. Access control is a way to control who is allowed access to a network server and which services it is allowed to use once they access.
Authentication: It offers the way of identifying users such as password and login dialog, response and challenge, messaging support and based on a security protocol that you select, encryption.
Authorization: It provides the way for remote access control such as authorization for every service or one time authorization, per user account list and the profile, support of Telnet, ARA, IPX and IP and user group support.
Accounting: It provides the way for collecting as well as sending the security information used for the auditing, reporting and billing including start and stop times, the user identifies, number of bytes, number of packets and executed commands.
The AAA will increase the flexibility as well as control of the access configuration, multiple backup systems, scalability and standardized authentication ways such as Kerberos, RADIUS, TACACS+.
You can also configure the AAA to operate without the server by setting a switch to implement AAA in the local mode. A switch handle, then handle authentication as well as authorization. No accounting is available in this configuration especially.
IOS local AAA
The syntax for using the per user AAA is somewhat straight forward. So first create the AAA attribute list by using aaa attribute list command as follows:
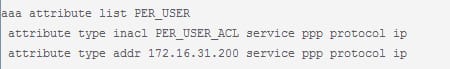
It is important to specify the service and protocol very correctly in order for the attributes to apply very correctly. To get a list of all the IOS supported attributes, use the context sensitive assist under the "aaa attribute list" configuration mode. Use the show aaa an attributes command for a list of all IOS attribute and its format. To map the radius ietf attribute numbers or name to a name used by the IOS, then use show aaa attributes protocol radius command.
Steps to configure AAA:
- Enable AAA
New AAA model of the authentication is enabled with the single command that unlocks all the other aaa command on a command line interface. Remember this command will break the non AAA line and also enable the password. - Configure the server to be used for the AAA
Configure the address of the AAA servers that you like to use. - Define authentication and authorization method list
Then define the method that instructs the router to use the AAA authentication for the terminal logins. - Enforce AAA authentication on a relevant lines
The last step is actually being done by already in step one by enabling the AAA. Then create the custom authentication method list for the line, use the command by substituting the method list name for the word default.
Although AAA is a primary method for the access control, IOS software offers additional feature for the simple access control which are outside the AAA scope, including local username authentication, enable password authentication and line password authentication. In the below example, here configured PPP for the local authentication and using the local database to authorize the network attributes. There was an attribute list, that is later assigned to the user. The list instructs a router to apply the inbound access list and also assign the interface into the specific VRF by using an interface level command. Then assign the fixed IP address to the user as an operation that is commonly needed. Then the final attribute applies the rate limit command to an interface, simply to illustrate few simple QoS configuration. You can use the sub policy out and also sub policy in to apply the policy map to a cloned interface. Then set up the PPTP in the quick and dirty way and test the configuration. Then you can also configure any of the windows host to connect the VPN server by using the CHAP and PPTP authentication.
5.2 Describe device security using IOS AAA with TACACS+ and RADIUS
The AAA attribute list define the user profile that is local to a router. Each attribute which is known to a AAA subsystem are made available for the configuration. An AAA attributes which are defined in an AAA attribute lists are standard TACACS+ and RADIUS attributes. Even though, both from the Cisco IOS internal format for the attribute. The attribute has to be converted from a RADIUS format to the IOS AAA interface format. The TACACS+ attribute is generally identical to the IOS AAA interface format.
5.2.a AAA with TACACS+ and RADIUS
TACACS+: It is the terminal access controller access control system. It refers to the family of protocols which handling the remote authentication and the related services for the networked access control via centralized server. The TACACSplus is derived from the TACACS. It is the separate protocol which handles authentication, authorization and accounting services. It encrypts all the body of a packet but leaves the standard TACACS+ header. In the debugging process, it is very useful to have a body of the packets unencrypted.
RADIUS: Remote authentication dial in user service is the networking protocol, which provides the centralized AAA management for users that connect and also use the network service. It is the system of the distributed security which secures the remote access to the network services and networks against the unauthorized access. The RADIUS consist of 3 components are the server, the client and the protocol with the frame which utilizes the UDP/IP. There are 3 responses in the RADIUS such as access challenge, access accept and access reject. The RADIUS encrypts only a password in an access request packet from the client to a server. Here the remainder of the packet is unencrypted.
These 2 prominent security protocols are used to control access into the network. The Cisco is committed to supporting both the protocol the best of the class offerings. The Cisco seriously evaluated the RADIUS as the security protocol before it was developed TACACS+. Many of the features included in a TACACS+ protocol to meet the requirements of the growing security market. The protocol is mainly designed to scale as the network grow as well as to adapt to the new security technology as a market matures.
Steps to configure the AAA with RADIUS and TACACS+ as follows:
Enable the AAA
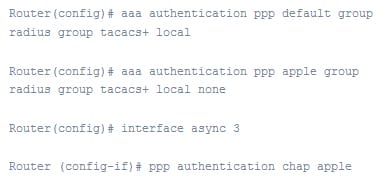
Configure the authentication by using the TACACS+ or RADIUS
Define a method list for the authentication
Apply a method list per line or per interface.
The Cisco IOS software tries authentication with a next listed authentication method when there is no response from a before method. Suppose the user database or security server respond by denying the user access, then the authentication process and the user also gets the denied user prompt. So to configure the AAA, make use of the below global configuration command:
Router(config)# aaa new-model
To apply the method list only to the set of interfaces or specific interfaces. Then create the method list and apply that to the interfaces. Give below is the authentication method which can be applied only to the interface as follows:
Literally, there are various methods to configure AAA with the TACACS+ and RADIUS.
You can use the TACACS+ and RADIUS to secure the access such as web management access, SSH access, Telnet access and the access to a privileged EXEC level and the CONFIG level of the CLI
Procedure to configure TACACS+:
- Identify the TACACS+ servers
- Set the optional parameters
- Configure the authentication method list
- Optionally configure the TACACS+ authorization
- Optionally configure the TACACS+ accounting
Procedure to configure RADIUS:
- Configure the brocade vendor specific attribute of a RADIUS server
- Identify the RADIUS server to a ServerIron
- Set the RADIUS parameters
- Configure the authentication method list
- Optionally configure the RADIUS authorization
- Optionally configure the RADIUS accounting.
5.2.b Local privilege authorization fallback
The local database will behave like a fallback method for various functions. This type of behavior is proposed to assist you to prevent the accidental lookout from a security appliance. For the users who required fallback support, it is recommended that the username and password in a local database match its username and password in an AAA server. It offers the transparent fallback support. The user cannot find out whether the AAA server or a local database is offering the service by using the password and username on the AAA servers which are different than the password and username in a local database implies that the user could not be specific which password and username should be provided.
Console and enable the password authentication: when the command aaa authentication console is used, you can also add a local keyword after an AAA server group tag. Suppose the servers in a group all are unavailable, then the security appliance uses a local database to the authenticate administrative access. It includes enabling the password authentication also.
Command authorization: when the command aaa authorization command is used, you can add a local keyword after an AAA server group tag. Suppose the TACACS+ server in a group all becomes unavailable, then the local database is mostly used to authorize the commands based on the privilege level.
VPN authorization and authentication: the VPN authentication and authorization are mainly supported to enable the remote access to a security appliance if the AAA servers which normally support that VPN services becomes unavailable. The command of the authentication server group, available in the tunnel group attribute mode, will allow to specify a keyword LOCAL when configuring the attributes of the tunnel group. When the VPN client of the administrator specifies the tunnel group configured to the fallback to a local database, then the VPN tunnel will establish, although an AAA server group becomes unavailable, offered that a local database is configured with the required attributes.
To use a local AAA authentication or local fallback, centralized AAA servers are unavailable, then you must configure minimum one user in a local database. A local database will support only the password authentication and can use to assign the privilege level to all the locally defined users. The privilege level is the simple mechanism which allows the differentiation of the user access privilege and also offers the simplest way for the multiple level of management access. The privilege level may range from 0 to 15. The privilege level will define which commands and management functions are mostly available to the user. It is highly recommended to create minimum local administrator account, although proposed to use the remote AAA authentication on the regular basis. You can use that account in case of emergencies, if the communication to a central AAA server fail, either due to network issues or experiencing problems with the servers. This account must be granted full administrative access, that ensure it is not limited in their functionality must use become essential.
AAA is the critical piece of the network infrastructure. The AAA is what keeps the network secure by making sure by allowing the right users to access the network resources. The authentication, authorization and accounting network security service provide a primary framework via which you set set up access control on the access server or router. The IOS using the local database and service security using RADIUS and TACACS+ described in detail. It helps you to learn the concepts and techniques behind the AAA also.
Site Search:






