- Home
- Popular IT Certifications
- DMVPN (single hub) and Easy Virtual Networking
Describe DMVPN (single hub) and Easy Virtual Networking (EVN)
The concept behind the VPN has been around some time now and the problem in the past years has been that the configuration of the VPN was typically the point to point and static in nature. But now, the implantation of the DMVPN provides the ability to get around both of the previous limitations. The DMVPN deployments provide the ability to configure the dynamic virtual tunnels that can be automatically created depends on the traffic needs and the certain topology. Based on the certain configuration, it is possible to have the virtual tunnels be created between the spoke sites to remove the load from a hub router. This section takes a look at the most available DMPVN and the easy virtual networking concepts in detail.
4.2 DMVPN (single hub)
The DMPVN stands for the dynamic multipoint VPN. It is the Cisco IOS software solution for building the IPsec VPN. The Cisco DMVPN uses the centralized architecture to offer easier implementation as well as management for the deployments which need granular access control for diverse the user communities such as telecommuters, extranet users and mobile workers. There are different ways to implement the DMVPN based on the specific need of a traffic being transmitted and the type of hardware being used and since there are a variety of options, just take single hub DMVPN in this section. The DMVPN configuration is very simple, if they have knowledge and worked with the GRE tunnels.
The DMVPN is the Cisco answer to an increasing demand of the enterprise companies to connect branch offices with the head offices and between each other when keeping costs low, increasing flexibility and minimizing configuration complexity. With the DMVPN, 1 central router is usually placed in a head office, undertakes a role of the hub when all other branch routers are spokes which connect to the hub router. So that the branch offices can easily access the resources of the company. The DMVPN comprises of 2 deployment designs such as DMVPN hub & spoke and DMVPN spoke - to - spoke. In both the cases, a hub router is assigned the static public IP address when the branch routers will be designated dynamic or static public IP addresses.
Operation of DMVPN
- Every spoke has the permanent IPsec tunnel to a hub, but not to other hubs within a network.
- Every spoke will registers as the client of an NHPR server. A hub router undertakes the NHPR server role.
- When the spoke requires to send the packet to a destination subnet to the other spoke, then it queries on the NHRP server for the real address of a target or destination spoke.
- Then after originating spoke learns the address of the peers of a destination spoke, it may initiate the dynamic IPsec tunnel to the destination spoke.
- A spoke to spoke tunnel is built over a mGRE (multipoint GRE) interface.
- Then spoke to spoke link may establish on demand whenever there was a traffic between a spoke. Hence the packets can able to bypass a hub and also use a spoke to spoke tunnel.
- All the data traversing a GRE tunnel is encrypted by using the IP security.
Configuring DMVPN on a single hub:
This scenario is used for the service provider providing the DMVPN connectivity to 2 unrelated customers and both the customers require connectivity among the own sites and to the internet service provider, but not able to communicate with each other. In the same way, each customer should use their own unique preshared key for the authentication. Take the example of the below:
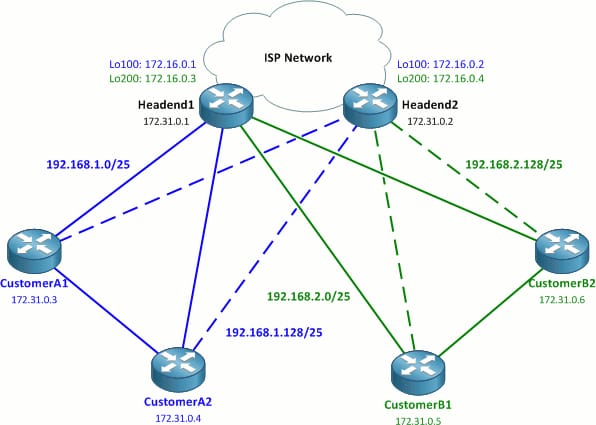
In the above figure, the 172.16.0.0/20 space denotes the public address space and in the real world deployment, that will be effectively a random public IP addresses. The 2 internet service provider headend router connects the 4 sites, 2 per user/customer, to an ISP network. Every headend router has the 2 loopback interfaces to that the DMVPN tunnels can be terminated.
AS per Cisco design, every customer can have 4 redundant DMVPN tunnels, 1 to each headend router. It adds up to the total of 4 DMVPN networks. Remember that the lab may some muddy too sometimes.
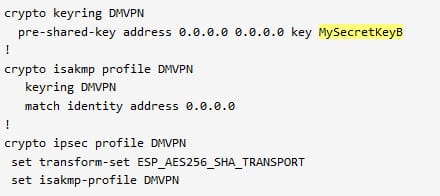
Single ISAKMP policy and the IPsec transform set is common to all the routers in the configuration. Let us see the crypto configuration first which will lay foundation.
All routers:
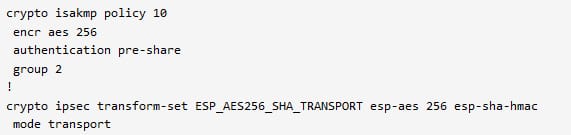
Then configure the needed crypto profile on a headend routers. The ISAKMP and the keyrings are explicitly sources by the loopinterfaces. It ensures that the right preshared keys are applied to the every DMVPN spoke router depends on a destination IP address of the incoming encrypted packet.
Headend routers as follows:
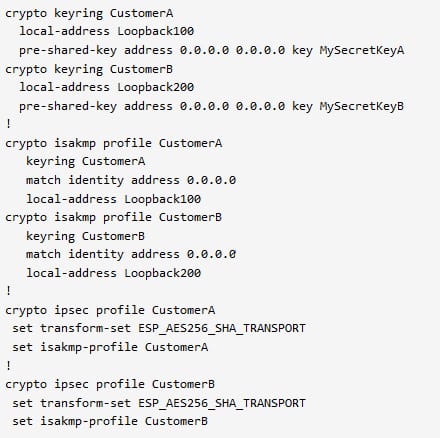
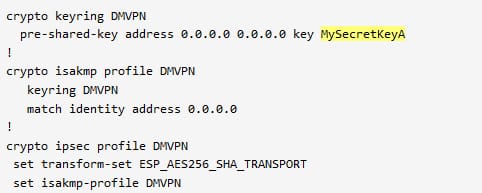
The spoke router configuration is similar to the headend router, but simple, because only adding the configuration applicable to a respective user or customers. Here single wildcard mask is used to match the preshared key.
Configuration of customer A routers as follows:
Configuration of customer B routers:
DMVPN configuration:
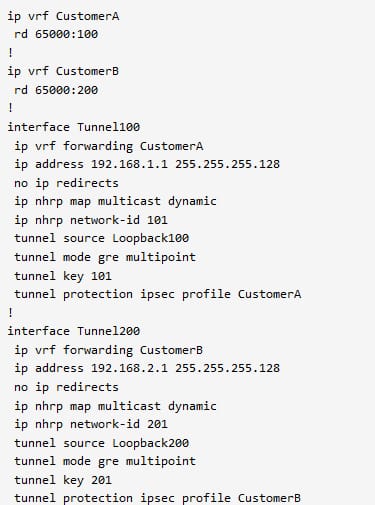
First, create the 2 unique tunnels on the 2 headend routers, with one in either VRF of the customer.
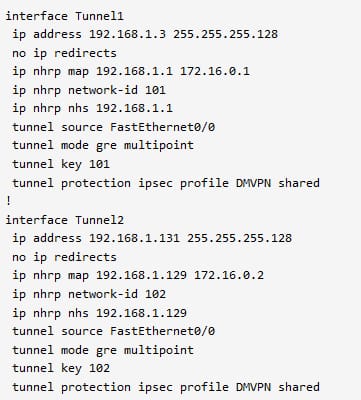
Configuration of headend 1:
Headend 2 configuration:
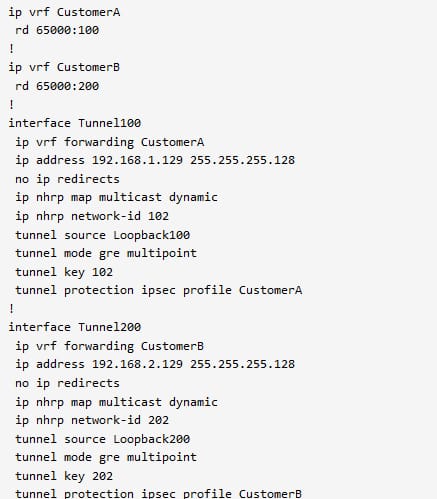
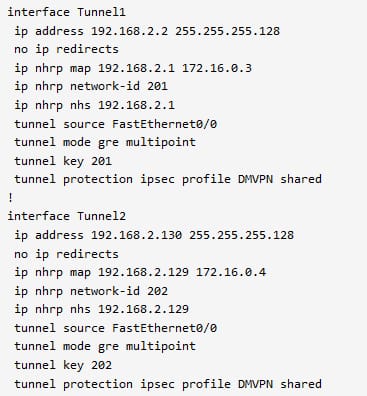
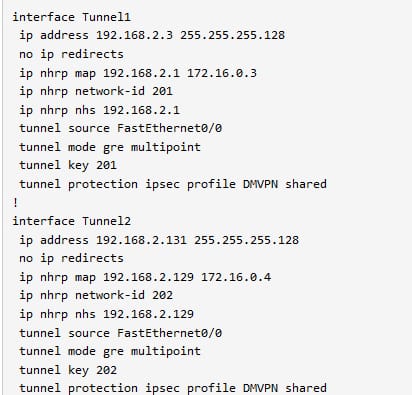
The tunnel interface is sourced from a loopback interface. Then each tunnel is assigned to a unique tunnel key and the NHRP network ID. The spoke router tunnel interface is configured similarly to a headend router, along with the NHS specification. It is mainly sourced from the physical interfaces.
Configuration of customer A1:
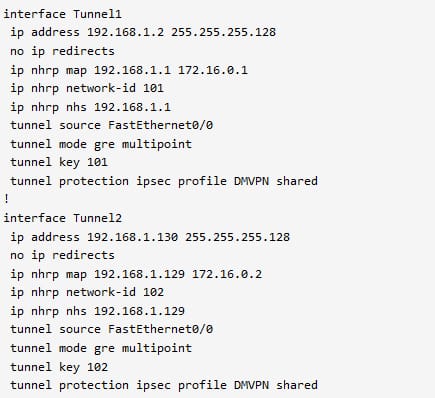
Configuration of customer A2:
Configuration of customer B1:
Configuration of customer B2:
The benefits out of the DMVPN is very higher than the others. It lowers the operational and capital expenses, simplifies the branch communications, improves the business resiliency and reduces the deployment complexity. It prevents the disruption of the business critical application as well as services by simply incorporating the routing with the standard based IPsec technology. It offers the zero touch configuration, which dramatically decreasing the complexity of deployment in the VPN. It enables the direct branch to branch connectivity for the business applications such as voice.
4.3 Easy virtual networking (EVN)
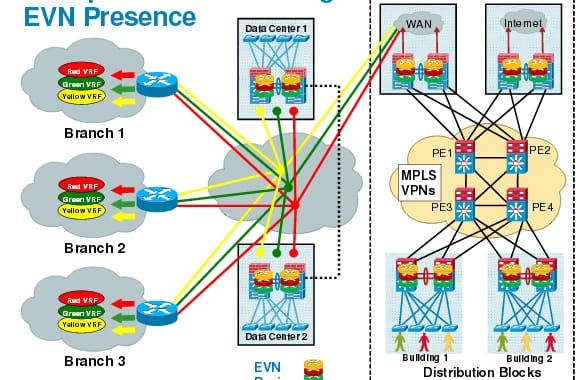
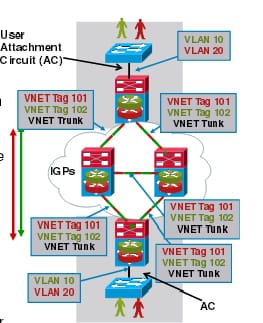
The network virtualization is the economical way to offer traffic separation. The multiple virtualized network can be overlaid on the single physical infrastructure. The corporation can require to offer separation in between the different user groups. Several well adopted network virtualization solutions are widely available. In that the Easy virtual networking is the simplified LAN virtualization which helps to enable the network managers to offer service separation on the shared network infrastructure. The EVN is the IOS software innovation to multi VRF deployments without changing any switching protocols and existing industry standard routing protocols.
It is an IP based virtualization, which offers end to end virtualization of 2 or more layer 3 networks. The EVN builds on an existing IP based virtualization is known as the VRF-lite. The EVN is also backward compatible with the VRF lite which helps to enable the seamless network migration from the VRF lite to the EVN.
An EVN supports for the OSPFv2, EIGRP for unicast routing, static routes, IPv4, MSDP for IPv4 multicast routing and PIM. The EVN also support for the Cisco express forwarding as well as SNMP- simple network management protocol.
Before configuring the EVN you must have the functioning campus design before adding the virtualization to the network, understand the VRF instances and how to maintain the traffic separation over the network and for implementation it needs the single IP infrastructure.
The network virtualization used to secure the network and also reduce the network expenses by simply utilizing a same network infrastructure for the multiple virtual networks. The path isolation can be acquired by separating the paths by using the dedicated routers that are very expensive than the virtual networks.
EVN offers the below benefits: Increased business flexibility due to the decrease in an infrastructure needs for maintaining the traffic separation via the network core. Reduced capital expenditure by not having to keep maintain the separate physical infrastructure to maintain the traffic isolated. EVEN is very compatible with the VRF lite.
The VRF were born from the MPLS - VPN and grew into an adolescent with the VRF lite. Now EVN brings VRF into the maturity enhanced and simplified VRF lite. The ASR1k is the first platform which supports the EVN. In the LAN trunks, the sub interface inheritance and VLAN ID re-suse will take place. The IGP based shared services will take place in the route duplication. The usability and enhanced troubleshooting by using the command such as traceroute, debug condition, routing context and cisco vrf-mib.
The functional components of the path isolations are device virtualization and data path virtualization.
How it works:
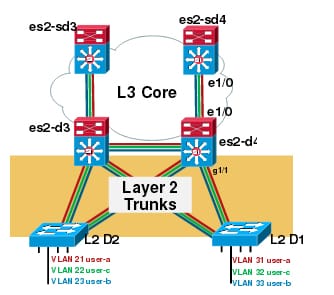
Step 1:
Create the L2 VLAN and trunk it to the 1st L3 device
Step 2:
Define the VRF at the 1st L3 device and also map an L2 VLAN to the proper VRF.
Step 3;
Define the VRF on all the other L3 device in a network.
Step 4:
Configure as VNET trunk all the physical links, which connecting to the L3 devices in a network core.
Step 5:
Enable the routing protocol in the every VRF.
Step 6:
The traffic is carried to the end to end across a network which maintain the logical isolation in between the defined group.
The single trunk interface will transport the multiple VRF traffic. The trunks are pre provisioned for the new VRF.
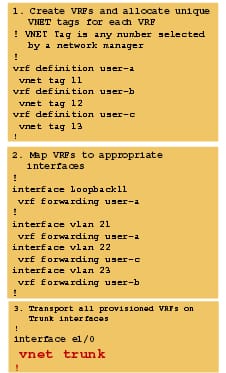
The VNET tag # is defined for the every VRF used as the part of numbering the sub interfaces. Every sub interface will inherit the same characteristics from a main interface. Unless the VRF filters are applied, the trunk interface can transport the traffic to all the provisioned VRF. While creating the VRF sub interfaces, the vnet tag is mainly used. This tag also used with the encap dot 1q. The best practice to change the vnet tag so verf sub-int is created by removing the old vnet tag and configuring the new vnet tag.
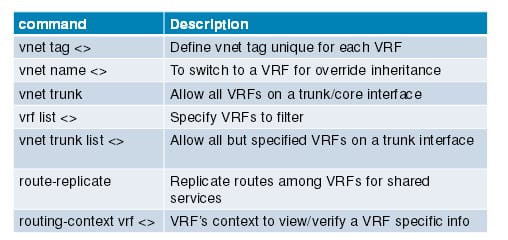
The device which is connected to the virtual network can not understand the virtual network tags and also send & receive the untagged traffic. This device is considered as the VRF unaware. In contrast, the device which sends & receive tagged traffic and hence takes a tag value into consideration while processing, then such type of traffic is referred as the VRF aware. Each EVN runs the separate instance of the routing protocol. It allows each EVN to fine tune the routing separately and limits the fate sharing. The different virtual network can run the different routing protocol concurrently. The EVN is wire compatible with the VRF lite. The packets enter the EVN through the edge interfaces, traverse the multiple trunk interface and also exit a virtual network via another edge interface. In the ingress edge interfaces, the packets are mapped from the VLAN into the particular EVN. When the packet is mapped once to the EVN, it is then tagged with an associated virtual network tag. A virtual network tag will allow a trunk interface to specially carry the packets for the multiple EVN. That the packets remain tagged until it exit the EVN via an egress edge interface. Over the edge interface, an EVN associated with an interface is mainly used for the route lookup. Over the trunk interface, a virtual network tag is carried in a packet is used to locate corresponding EVN for routing a packet.
Hopefully, this content will enable you to have the general understanding of what possible when deploying the DMPVN and description of the DMPVN single hub. The possibilities available via the DMPVN solutions will provide the network designers lot of interesting and valuable options which enable the very scalable dynamic VPN design. The engineers and network professionals have to understand this concept truly about this technology. Deliver path isolation and traffic separation capabilities of the shared network infrastructure with the EVN. The EVN takes the advantage of the existing virtual routing and forwarding lite technology to simplify the layer 3 network virtualization, enhance, manage and troubleshoot and improve support for the shared services.
Site Search:






