- Home
- Popular IT Certifications
- How to Configure and Verify EtherChannels
How to Configure and verify EtherChannels
Ether channels are designed to provide the fault tolerant high capacity links between servers, routers and switches. EtherChannels can be used to enhance the bandwidth between data centre and wiring closets, you can also apply it anywhere in network where the bottlenecks can possibly occur. EtherChannel allows automatic recover in case of link loss by redistributing the network load across the rest of the links. If a single links fails, the Etherchannel will redirect traffic from that specific link to the rest of the links available in the channel, without delay.
PAGP:
PAgP, known as port aggregation protocol is proprietary network protocol designed by Cisco. It is used for logical aggregation and automated aggregation of Ethernet ports, called etherchannel. This implies that this feature can be used for only for the cisco designed switches and the related licensed vendors.
PAgP is allowed to be configured on Cisco switches to work in three modes:
Auto- This is the passive negotiation of channel
Desirable- This is the active negotiation of channel
On- No protocols used here, it assumes that the remaining side has enabled aggregation link
Cisco devices that are running CatOS, one single switch mode can be configured to run PAgP and LACP modes. Cisco devices running IOS support single port configuration for LACP. It is not constrained by the restriction of per module setting.
The messages sent by PAgP are always sent to the known multicast addresses 01-00-0C-CC-CC-CC and 0X0104 2 protocol code
PAgP also uses the similar multicast group
Limitation:
Pago is limited by the fact that in aggregation group, all the physical ports should reside on same switch. Soon 4500E and present Cisco 6500 platforms eliminate this limitation by using the VSS technology which allows the etherchannels to be divided between two chassis. HP is performing this through the IRF techncology, however without limitation of 2 boxes only (4-9 boxes are allowed in a stack). Similarly, the company Avaya's is also eliminating this limitation by allowing physical ports to be divided between two switches in the triangle configuration or more than four switches in a mesh. Other than that, Extreme networks are also performing this function by using M-LAC Multilink aggregation. Nexus switches allow perform this through Virtual port channel.
LACP:
In the networking system, term LACP applies for different methods of combining the numerous network connections working parallel in order to enhance the throughput which a single network may not be able to sustain. Also, to allow redundancy when one link fails.
- LAG allows automatic recovery when the single physical link fails. As far as atleast one link exists, LAC connection remains to continue.
- It distributes data transmission like frames on the physical links
- All the frames forming specific data communication part will eventually be transmitted to the same connection. This ensures that the delivery of single frames of a data packet will be received in the right order.
-
Data Transmission Distribution:
LACP feature allows the distribution of Ethernet frames to the available physical links to LAG connection. Therefore, the effective data throughput will increase the rate of data possible in a single physical link. Not to mention that IEEE standard will not define specific algorithm for the frame distribution. The guidelines for individual links are:
- Frames will not be duplicated
- The set of frames for a particular data packet will not be transposed.
-
Static Link Aggregation
The static link aggregation allows the settings of configuration to set up on both LAC participating components.
Dynamic Link Aggregation
Other than that, LACP will allow the information exchange in regard to the link aggregation among two members of the provided aggregation. This information will be stored in Link Aggregation Control Protocol Data Units.
Each single port is to be configured as passive or active LACP by using the feature of control protocol.
- Active LACP: this interface allows transmitting LACPDUs and thus to communicate the protocol, regardless of the fact that whether its counterpart utilizes passive LACP or not.
- Passive LACP: This port allows not transmitting the LACPDUs. The port will allows only transmitting LACP while the counterpart uses Active LACP
-
Manual EtherChannel Configuration
The etherchannel manually configured ports will not exchange etherchannel packets of protocol. The manually configured etherchannel will only form when all ports are configured in the etherchannel compatibility.
Load Balancing
The Etherchannel will balance the traffic across links in EtherChannel by decreasing a part of binary pattern which is formed from frame addresses, to a numerical value which selects from the channel one of the links. Load balancing Etherchannel can also use IP addresses or Mac addresses. Layer 4 port values are also utilized by the Etherchannel. Etherchannel load balancing will either use destination or source or both ports of destination and source. Whatever the mode is selected will apply to Etherchannel which is configured on switch. Load balancing etherchannel can also use the layer 2 MPLS information. It is recommended to go for the option which provides balance criteria with highest variety in configuration. For instance, in case the traffic on Etherchannel goes only to one MAC address, you can use MAC address destination mode as Etherchannel load balancing basis. Ether channel will always select the same link, using IP addresses or source addresses can result in better kind of load balancing.
Layer 2 and Layer 3
MAC addresses are automatically learned by layer 2 switches, creating a table that can be used to forward packets. For instance, if a single switch receives from MAC addresses X a packet on Port number 1, it will know that the destined packet for MAC address X will be simply forwarded out of that interface instead of having to try every available port in return.
As layer 2 data can be easily retrieved, the packets are easily forwarded, typically, at the speed of wire network. Therefore, the layer 2 switching has no or little impact on network performance or bandwidth. As they are relatively slow devices, no management and setup is required, making them easy and cheap to deploy.
The layer 2 switches cannot apply while forwarding packets, any intelligence. They are unable to route packets that are based on IP addresses or priorities sent by specific application, for instance, guarantee bandwidth Voice over the IP users.
Based on layer 3, the intelligent packet forwarding information is usually the feature of routers. It is here that the IP addresses are found, for instance, allowing a router to link various subnets together. Specialized routing protocols use layer 3 as well, allowing routers to learn about routes among the networks.
Following is an example of Layer 2 and 3 configuration:
Sample:
Switch(config-if)#int ra gi 0/20-21
Switch(config-if-range)#switchport
Switch(config-if-range)#switchport mode access
Switch(config-if-range)#switchport access vlan 4
Switch(config-if-range)#channel-group 4 mode active
Switch(config-if-range)#int po 4
Switch(config-if)#no shutdown
Configuring L3 ether channel:
Configure port-channel interface, no switch port, assign IP address. Then inside physical interface mode, configure no switch port, no ip address and then channel-group command.
Sample:
Switch(config)#int po 5
Switch(config-if)#no switchport
Switch(config-if)#ip address 5.5.5.5 255.255.255.0
Switch(config-if)#no shutdown
Switch(config)#int rang gi 0/23-24
Switch(config-if-range)#no switchport
Switch(config-if-range)#no ip address
Switch(config-if-range)#channel-group 5 mode active
Show commands:
Show lacp { number | sys-id | counters | internal | neighbor}
Show pagp { number | counters | internal | neighbor}
Show etherchannel { number | summary | port | details | load-balance | port-channel }
EtherChannel Guard:
Ether Channel guard allows you to know if one part of ether channel is not properly configured. The reason may be that a few parameters don't match up like speed and duplex. Or, may be one side is the trunk while the other is not. During the misconfiguration, the switch will put the interface in err disable state, displaying an error.
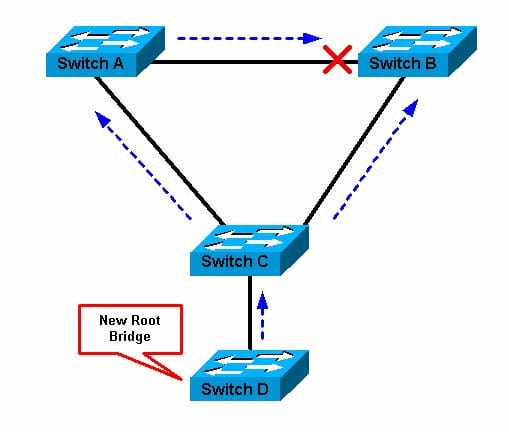
Root Guard
The layer 2 network of SP includes many switch connections which are not SP owned. In such situation, the spanning tree can select and reconfigure itself a customer switch as root switch. You can easily avoid this case by enabling the root guard on SP port connected to the switch in customer's network. If the spanning tree calculations result in interface in customer network, planned to be selected as root port, the root guard features puts the interface in blocked state in order to prevent the customer's switch from converting into root switch or being a root path.
If a switch that is outside SP network converts into root switch, the port is blocked, while the spanning tree selects a fresh root switch. The switch of customer does not become a root switch, and will not come in the root path.
In case the switch operates in MST mode, the root guard will force the interface to be the designated port. If a boundary port seems to be blocked in IST instance due to root guard, the interface is also blocked in all the MST instances. The boundary port is an interface which connects to LAN, the selected switch of which is either a switch with multiple MST regions or an IEEE 802.1 D configuration.
The root guard allows an interface to apply all the VLANs to which the port belongs. VLANS can easily be mapped and grouped to a MST instance. You are also able to enable this function through the spanning tree guard root port configuration command.
Root Guard configuration on interface basis.
vega> (enable) show spantree guard
Port VLAN Port-State Guard Type
------------------------ ---- ------------- ----------
1/1 1 forwarding root
1/2 1 not-connected none
3/1 1 not-connected none
3/2 1 not-connected none
3/3 1 not-connected none
3/4 1 not-connected none
5/1 1 forwarding none
5/25 1 not-connected none
15/1 1 forwarding none
vega> (enable)
Loop Guard
Loop guard is one of the most important features of Etherchannel. Loop guard is used to avoid root or alternate ports from converting into the designated ports, as due to the failure which leads to unidirectional links. This feature works most effectively when enabled on the whole switched network. Loop guard also prevents root and alternate ports from becoming the designated ports; spanning tree due to this does not send the BPDUs on alternate or root ports.
You are allowed to enable loop guard by using the spanning tree loopgaurd default global configuration command.
When switch is operating in PVST rapid or PVST mode, the loop guard feature prevents root and alternate ports from becoming the designated ports, while spanning tree avoids sending the BPDUs on alternate and root ports.
While the switch works in MST mode, the BPDUS are not received by ports on non boundary, however, only when the interface is blocked in all MST instances by the loop guard. The loop guard blocks port in all MST on a boundary port.
The following table provides an example of how Loop guard can be enabled globally and on an interface.
*** Enable Loop Guard on globally ***
6506(config)# spanning-tree loopguard default
6506# show spanning-tree interface fastEthernet 4/4 detail
Port 196 (FastEthernet4/4) of VLAN0010 is forwarding
Port path cost 1000, Port priority 160, Port Identifier 160.196.
Designated root has priority 32768, address 00d0.00b8.140a
Designated bridge has priority 32768, address 00d0.00b8.140a
Designated port id is 160.196, designated path cost 0
Timers:message age 0, forward delay 0, hold 0
Number of transitions to forwarding state:1
The port is in the portfast mode by portfast trunk configuration
Link type is point-to-point by default
Bpdu filter is enabled
Loop guard is enabled by default on the port
BPDU:sent 0, received 0
*** Enable Loop Guard on an interface ****
6506(config-if)# spanning-tree guard loop
Router# show spanning-tree interface fastEthernet 4/4 detail
Port 196 (FastEthernet4/4) of VLAN0010 is forwarding
Port path cost 1000, Port priority 160, Port Identifier 160.196.
Designated root has priority 32768, address 00d0.00b8.140a
Designated bridge has priority 32768, address 00d0.00b8.140a
Designated port id is 160.196, designated path cost 0
Timers:message age 0, forward delay 0, hold 0
Number of transitions to forwarding state:1
The port is in the portfast mode by portfast trunk configuration
Link type is point-to-point by default
Bpdu filter is enabled
Loop guard is enabled on the port
BPDU:sent 0, received 0
Site Search:






