- Home
- Popular IT Certifications
- Cisco Express Forwarding Concepts & Challenges
Cisco Express Forwarding concepts and challenges in general network
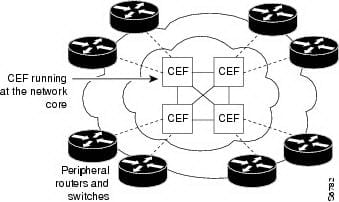
The CEF is referred as a Cisco express forwarding. It is an advanced one in layer 3 switching technology, which is mainly used in the internet or else core networks to enrich the overall performance of the network. However, CEF is the Cisco proprietary protocol, remarkable vendors of the high capacity or multi layer switches provides a similar functionality at where the layer 3 routing or switching is taking place in the hardware rather than the CPU or software.
1.1 Identify Cisco express forwarding concepts
The CEF is most often used to improve the speed of the packet switching by deducting the overhead as well as delays which is introduced by means of other routing techniques. This CEF also optimizes the scalability for the networks with a dynamic and large traffic pattern. It offers the capability to switch the packets via device in an efficient way when keeping the load on a router processor as low.
The CEF is mainly made up of 2 different main components such as FIB and Adjacency table. Those 2 components will updates same time automatically as a routing table.
1.1.a FIB
The routing itself will not truly optimize for the rapid look ups. It mostly comprises of lots of information which is crucial to its construction, however, it is not so essential for the routing lookups like administrative an origin distances of a route, their ages, metrics and much more.
The FIB is referred as a forwarding information base. It contains the destination reachability details and the next hop details. This detail is mostly used by a router to decide the forwarding decision. Then the FIB is mainly organized as the multiway trie that allows for easy lookups and very efficient. Within the FIB and the routing table there will be a one on one relationship will exist between the routes.
The CEF uses this FIB to make the IP destination based switching decisions. It is conceptually very similar to the information base, or routing table. It also maintains the mirror of a forwarding information in an IP routing table. When a topology or routing changes may occur in a network, a routing tables are updated as well as those changes will reflect on the FIB.
The entries in a routing table will need some recursive lookups such as: after matching the entry of the destination network, next hop information might comprise next hop's IP address but not an egress interface, so that the IP address of the next hop has to be searched up in a next iteration of the routing table and this recursion depth is literally theoretical. After matching the immediate entry in a routing table which identifies an egress interface finally. Then the final IP address of the next hop at the time of lookup process must be matched further in ARP or the similar mapping table for an egress interface to determine how to design the header of the layer 2 frame. All those shortcomings can also be improved by: destination prefixes from a routing table can also be stored in the separate data structure is called as forwarding information base. Rather than transferring the plain IP address of the next hop from a routing table through FIB, every entry in a forwarding information base which represents the prefix of the destination can rather comprise the pointer into the specific entry in an adjacency table which stores an appropriate information of the egress interface and layer 2 header frame indication.
The routing table recursion is resolved when making the entries of FIB as well as setting up a pointer into appropriate entries of the adjacency table. This FIB will only store the destination prefixes and the forwarding information is stored as the rewrites information of the layer 2 in an adjacency table and also FIB points entries towards appropriate adjacency table entries.
All the FIB entries will describe that the networks are reachable through specific next hop point to a similar entries of the adjacency table that may contain intended egress information and layer 2 header towards the next hop.
1.2.b Adjacency Table
Once the forwarding information base is checked, then the next hop in the troubleshooting a CEF lies to rewrite information in an adjacency table. An adjacency table comprises the rewrite information which CEF uses to switch the packets. Every adjacency entry stores the pre computed frame headers are used while forwarding the packet using the FIB entry referencing the associated entry. This adjacency table is highly populated as an adjacencies are discovered. Every time when an adjacency entry is produced, such as via the ARP protocol, the link layer headers for that the adjacent node is pre computed as well as stored in an adjacency table.
The routes may have mostly more than the 1 path per entry, allowing it possible to use the CEF to switch the packets when loading over the multiple paths. Additional to the next hop of the interface adjacencies, few exception adjacencies will exist to expedite the switching for a non standard condition.
Typically a router has only the handful neighbors, a next hop into all of the known destination. All destinations are reachable via a specific next hop are using the similar layer-two rewrites information and to reach any networks behind the specific adjacent next hop, then the packets may be encapsulated towards the frame which has the similar layer two headers addressed and also sent out the same egress interfaces. Once the perfect entry is chose, encapsulating a packet, and forwarding that out the egress interfaces will be done in an effective rapid way, as the required data are available readily.
Once the FIB as well as adjacency table are produced, then the routing tables are not used anyway for route packet for which all the forwarding information is found in an adjacency table or FIB. The routing table will become a more source of the routing data to build an adjacency table and FIB contents, but it is not required to use route packets anymore.
1.2 Explain general network challenges
The LAN switches uses forwarding tables, content addressable memory to direct traffic to a particular port based on a VLAN number and the destination frame of the MAC address. When there are no entries corresponding to the destination MAC address of the frame in the incoming virtual LA, then the frame ( unicast ) may be sent to all the forwarding ports within the associated VLAN that causes flooding. The cause of the flooding is that the destination packet of the MAC address is not the layer 2 forwarding table. Listed below are the most common reasons which play major role in the network challenges.
1.2.a Unicast
The initial impact of this flooding is that all the hosts connected to that virtual LAN receive the traffics. If 2 of the 10gig servers are communicating and also the asymmetric routing is happening. If there are 100mbps hosts on the similar switch, then it is allowed to receive all the server traffic, effectively suturing a link. The STP topology change notification - TCN causes the forwarding table to age out faster than its normal timers. Suppose, the flapping link causing the STP re-convergence, it may cause some excessive unicast flooding. The configuring port will quick on all the edges of the interfaces which limits the TCN. The local area network switches use the CAM table to forward the frames.
The CAM overflow is one among the cause which is unlikely naturally happen in the modern switches, as it is usually sufficient memory to facilitate the requirements of the most networks. Although, the CAM overflows attack will be caused maliciously. While MAC address table grows large which it exceeds the content addressable memory size, then no recent MAC addresses will be learned that causes a unicast flooding. It can be protected by means of the port security.
The selected port can also be blocked from the unicast flooding with the help of switchport block unicast. It can be desirable in the highly safe networks and also where the PVLAN are used.
1.2.b Out -of-order Packets
The out of order is one among the general network challenges. In that, the time sensitive UDP application doesn't buffer the packets for a very long, so that they don't cope well with the reordering packets. An excessive packet rearranging in the TCP may cause the receiver to send the duplicate of ACK to trigger the retransmit fast. It might cause an excessive overheads in both the bandwidth and CPU, and also causing the sender to decrease the window size. A Receiver has to buffer as well as reorder packets and at the same time its takes memory, CPU cycles and time.
Out of order packets is the well popular phenomenon that the packet order is inverted over the internet. It can also be caused by per packet of the load sharing algorithm. It can affect the receiver's slow TCP sessions and network's re-transmission.
It causes the unnecessary retransmissions: when a TCP receiver gets the out of order packets, it delivers the duplicate ACK to trigger the retransmit algorithm most fast at a sender edge.
This also reduces the receiver efficiency: the TCP receiver need to hand in data to high layer in particular order. When the reordering happens, the TCP need to buffer the entire packets of out of order until receiving all the packets in the specific order. At the same time, the higher layers will get the data in burst instead of smooth, which reduce the efficiency of the system as a whole.
1.2.c Asymmetric routing
An asymmetric flooding is the when the return traffics take a different path via the network instead of the forward path. It can cause problems with the NAT as well as firewalls and among other things too. If any one link is higher delay or highly saturated, then the asymmetric routing may cause huge problems with the jitter and delay. It may cause unicast flooding too. This asymmetric flooding is considered as the major network challenge among all other types. Large amounts of flooded traffic may saturate low bandwidth links which cause the network performance problems or completely connectivity outage to the devices connected along such a low bandwidth link.
In short, a packet traverses from the source to the destination in 1 path and returns in a different path when come to the source. It is most commonly takes place in the L-3 routed networks.
This asymmetric routing is more common in most of the networks, larger networks too. It is an undesirable situation for most network devices such as VPN, steelhead appliances and firewalls. Those devices will rely on viewing each packet functionality.
It can also occur in the smaller scale. It can take place in the situation where the organization uses the 2 different routes such as leased line and VPN for instance. This will cause different issues in the fullcluster environment which mainly depends on the type of firewall running along with the fullcluster.
An asymmetric routing itself is not a problem, but it will cause issues when a firewall or NAT are used in its routed path. Incase:at the firewall, the state information is built while the packet flow from the higher security domain into the lower security domain. Then the firewall can be an out way point from 1 security domain to another. Suppose, the return path is flowed via another firewall, then the packets cannot be allowed to traverse a firewall from the lower to the higher security domain, it is because the return path of the firewall can not have any other state of information. This state information state will exists in a first firewall.
The Asymmetric routing problems have long been depends with the routing designs which involved packets flowing through the firewall. The asymmetric routing support in the firewall changes the prior design philosophy. This support with the other new features may be leveraged for getting greater scalability as well as redundancy in the traffic passing via the infrastructure of the firewall.
Site Search:






