- Home
- Popular IT Certifications
- VLAN and Trunking problems on Cisco Switches
How to troubleshoot and resolve VLAN and trunking problems on Cisco switches
A Local Area Network (LAN) was initially characterized as a system of machines spotted inside the same territory. Today, Local Area Networks are characterized as a solitary telecast space. This implies that if a client shows data on his/her LAN, the show will be gotten by every other client on the LAN. Shows are kept from leaving a LAN by utilizing a switch.
The hindrance of VLANs strategy is switches generally take more of an opportunity to process approaching information contrasted with an extension or a switch. All the more vitally, the establishment of show spaces relies on upon the physical association of the gadgets in the system. Virtual Local Area Networks (VLAN's) were created as an option answer for utilizing switches to contain show traffic.in a protocol LAN; workstations are joined with one another by method for a center or a repeater. These gadgets spread any approaching information all through the system. Be that as it may, if two individuals endeavor to send data in the meantime, an impact will happen and all the transmitted information will be lost. Once the impact has happened, it will keep on being proliferated all through the system by center points and repeaters. The first data will subsequently need to be hate in the wake of sitting tight for the impact to be determined, accordingly causing a noteworthy wastage of time and assets. To keep crashes from going through all the workstations in the system, a scaffold or a switch could be utilized. These gadgets won't forward impacts, however will permit shows (to each client in the system) and multicasts to pass through. A switch may be utilized to keep shows and multicasts from going through the system.
The workstations, centers, and repeaters together structure a LAN portion. A LAN fragment is otherwise called an impact space since impacts stay inside the section. The territory inside which shows and multicasts are kept is known as a telecast space or LAN. Accordingly a LAN can comprise of one or more LAN portions. Characterizing telecast and crash spaces in a LAN relies on upon how the workstations, center points, switches, and switches are physically associated together. When a LAN scaffold gets information from a workstation, it labels the information with a VLAN identifier showing the VLAN from which the information came. This is called express labeling. It is additionally conceivable to focus to which VLAN the information got has a place utilizing verifiable labeling. In certain labeling the information is not labeled, however the VLAN from which the information came is resolved focused around other data like the port on which the information arrived. Labeling could be focused around the port from which it came, the source Media Access Control (MAC) field, the source system location, or some other field or blending of fields. VLAN's are ordered focused around the strategy utilized. To have the capacity to do the labeling of information utilizing any of the routines, the extension would need to keep an overhauled database containing a mapping in the middle of VLAN's and whichever field is utilized for labeling. Case in point, if labeling is by port, the database ought to demonstrate which ports fit in with which VLAN. This database is known as a separating database. Extensions would need to have the capacity to keep up this database furthermore verifying that all the scaffolds on the LAN have the same data in each of their databases. The extension figures out where the information is to go next focused around ordinary LAN operations. When the extension figures out where the information is to go, it now needs to figure out if the VLAN identifier ought to be added to the information and sent. On the off chance that the information is to go to a gadget that thinks about VLAN usage (VLAN-mindful), the VLAN identifier is added to the information. On the off chance that it is to go to a gadget that has no learning of VLAN execution (VLAN-uninformed), the extension sends the information without the VLAN identifier. So as to see how VLAN's work, we have to take a gander at the sorts of VLAN's, the sorts of associations between gadgets on VLAN's, the sifting database which is utilized to send movement to the right VLAN, and labeling, a procedure used to distinguish the VLAN beginning the data. There has been a late move towards building a set of models for VLAN items. The Institute of Electrical and Electronic Engineers (IEEE) is as of now dealing with a draft standard 802.1q for VLAN's. So far, items have been exclusive, intimating that anybody needing to introduce VLAN's would need to buy all items from the same merchant. Once the benchmarks have been composed and sellers make items focused around these guidelines, clients will never again be kept to buying items from a solitary seller. The real sellers have underpinned these norms and are anticipating discharging items focused around them. It is expected that these guidelines will be endorsed later not long from now.
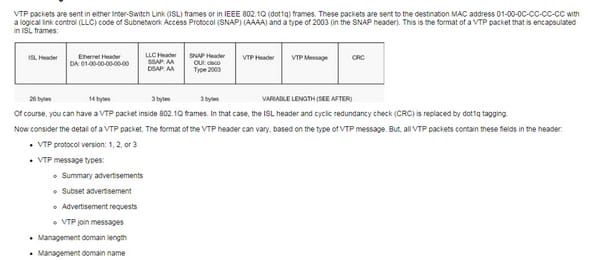
VLAN Trunk Protocol (VTP) decreases organization in an exchanged system. When you design another VLAN on one VTP server, the VLAN is disseminated through all switches in the space. This lessens the need to arrange the same VLAN all over the place. VTP is a Cisco-restrictive protocol that is accessible on the greater part of the Cisco Catalyst arrangement products.by default, Catalyst switches issue synopsis notices in five-moment increases. Rundown ads advise neighboring Catalysts of the current VTP area name and the setup update number. At the point when the switch gets an outline ad parcel, the switch contrasts the VTP space name with it VTP area name. In the event that the name is diverse, the switch essentially disregards the parcel. On the off chance that the name is the same, the switch then contrasts the arrangement modification with it update. On the off chance that it setup update is higher or equivalent, the bundle is disregarded. On the off chance that it is bring down, a promotion appeal is sent. The design update number is a 32-bit number that shows the level of modification for a VTP bundle. Every VTP gadget tracks the VTP arrangement correction number that is appointed to it. The majority of the VTP bundles contain the VTP design amendment number of the sender. This data is utilized within request to figure out if they got data is later than the current form. Each one time that you roll out a VLAN improvement in a VTP gadget, the arrangement amendment is augmented by one. With a specific end goal to reset the arrangement correction of a switch, change the VTP area name, and after that change the name over to the first name.
This is how trunking is configured;

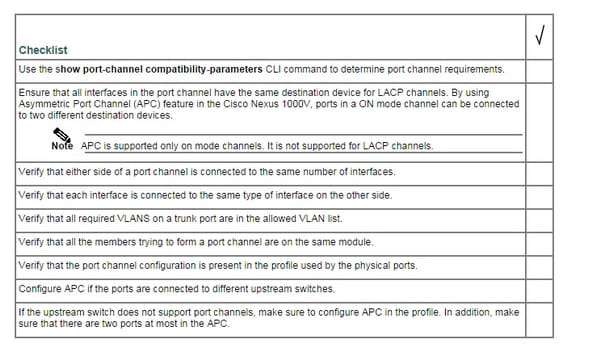
This is troubleshooting checklist;
Identify that VLANs are configured
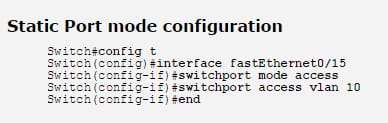
Cisco impetus switches help Dynamic VLANs by utilizing a VLAN Management Policy Server so as to dole out particular VLAN Ids to relating MAC addresses. Generally, Static task of VLANs to switch ports is arranged. To have the capacity to do along these lines, initially, all distinctive VLAN subnets need to be characterized. A while later, VLAN Ids could be allotted to switch ports and a have that appends on a given port consequently expect the VLAN enrollment of that port.
When a VLAN enrollment is without a doubt, a host can impart to different has inside the same VLAN. In the event that routing between distinctive VLANs is obliged then a switch needs to be joined in the system. A host connection can have entry to stand out VLAN. A connection that can convey more than one VLAN labeled casing is known as a trunk and the technique for distinguishing a few distinctive VLANS on a trunk is called tagging. CISCO used to backing it exclusive trunking protocol for VLAN labeling - ISL, or Inters witch Link Protocol. Be that as it may, ISL is not upheld any longer and Cisco proposes utilizing IEEE 802.1q protocol.
The IEEE 802.1q header contains a 4-byte label header containing a 2-byte protocol identifier (TPID) and 2-byte control data (TCI). The TPID has an altered estimation of 0x8100 that demonstrates that the casing which conveys the 802.1q/802.1p protocols.
Verify port membership correct
When you arrange a VLAN, you must allot it a number ID, and you can alternatively provide for it a name. The reason for VLAN executions is to partner ports with specific VLANs. You arrange the port to forward a casing to a particular VLAN.
As said formerly - Types of VLAN - you can design a VLAN in voice mode to help voice and information activity originating from a Cisco IP telephone. You can arrange a port to fit in with a VLAN by allotting a participation mode that points out the sort of movement the port conveys and the VLANs to which it can have a place.
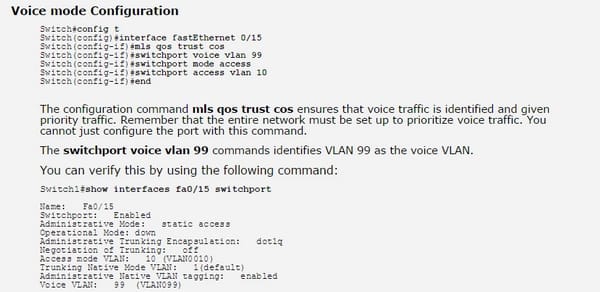
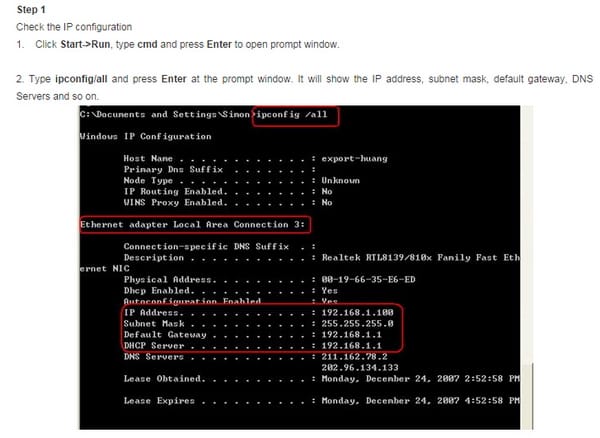
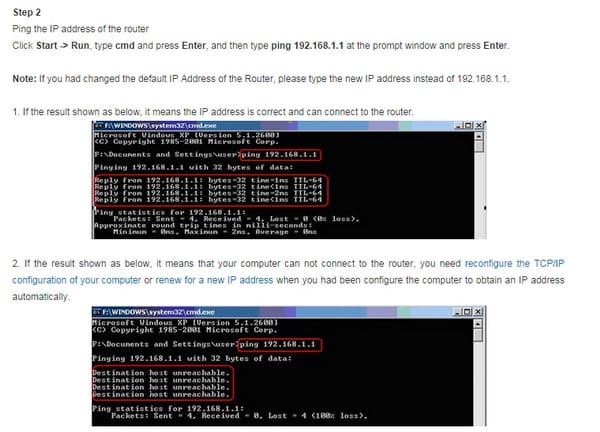
Correct IP address configured
Here is how to configure it;
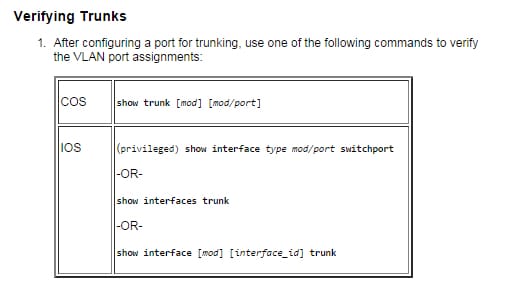
Verify correct trunk states
Trunk connections are obliged to pass VLAN data between switches. A port on a Cisco switch is either a right to gain entrance port or a trunk port. Access ports have a place with a solitary VLAN and don't give any recognizing checks on the edges that are passed between switches. Access ports likewise convey activity that originates from just the VLAN doled out to the port. A trunk port is of course a part of every last one of VLANs that exist on the switch and convey movement for each one of those VLANs between the switches. To recognize the activity streams, a trunk port must stamp the edges with uncommon labels as they pass between the switches. Trunking is a capacity that must be empowered on both sides of a connection. In the event that two switches are joined together, for instance, both switch ports must be designed for trunking, and they should both be arranged with the same labeling component (ISL or 802.1q). Numerous Cisco switches utilize a programmed trunking instrument known as the Dynamic Trunking Protocol (DTP), which permits a trunk to be progressively settled between two switches. All COS switches and coordinated IOS switches can utilize the DTP protocol to structure a trunk join. The COS alternatives auto, alluring, and on and the IOS choices of element auto, dynamic attractive, and trunk design a trunk connection utilizing DTP. In the event that one side of the connection is arranged to trunk and will send DTP signals, the opposite side of the connection will alterably start to trunk if the alternatives match accurately.
In the event that you need to empower trunking and not send any DTP flagging, utilize the alternative Nonegotiate for switches that help that capacity. In the event that you need to impair trunking totally, utilize the off alternative for a COS switch or the no switch port mode trunk order on an IOS switch. It is paramount to recall that not all switches help DTP and may not make a trunk without mediation. Additionally recollect that DTP offers no profit when you are trunking with a non-Cisco switch. To dispose of any overhead connected with DTP, it is valuable to utilize the Nonegotiate choice when DTP is not supported. The other alternative when picking a trunk connection is the epitome technique. For Layer 2 IOS switches, for example, the 2900xl or the 3500xl, the default epitome system is ISL. You can transform from the default with the switch port trunk exemplification command.
Here is the command for verifying trunks;
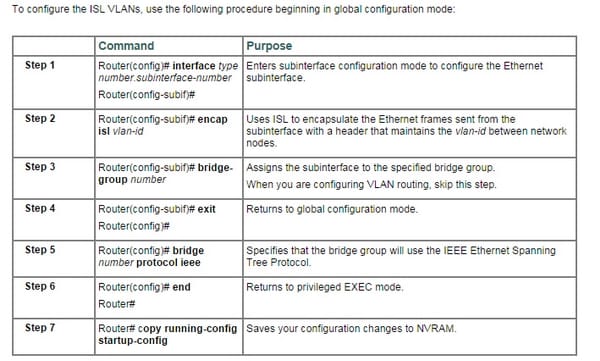
Verify correct encapsulation configured
Correct VLANs allowed
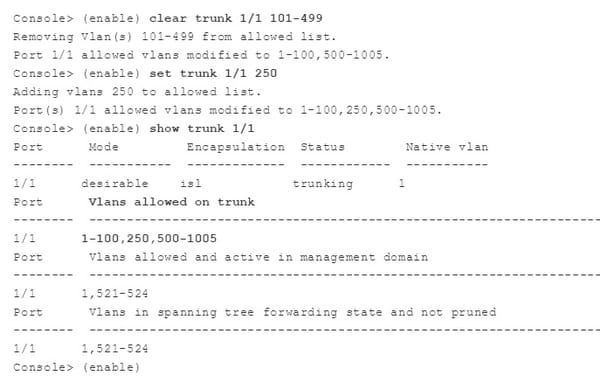
Here is to know how to verify the VLANS which are allowed;
VLANs are the most important part of the networking. They are the ways through which getting connected has become so easy. So in order to get some skills in networking, one must know about VLANS so that they can make sure that they can become a good network engineer and can pass any test required for that.
Site Search:






