- Home
- Popular IT Certifications
- IPv4 Addressing Using VLSM in LAN/WAN
Describe the operation and necessity of using private and public IP addresses for IPv4 addressing and appropriate IPv4 addressing scheme using VLSM and summarization to satisfy addressing requirements in a LAN/WAN environment.
Web Protocol form 4 (IPv4) is the fourth form in the advancement of the Internet Protocol (IP) Internet, and courses most movement on the Internet. However, a successor protocol, IPv6, has been characterized and is in different phases of generation organization. IPv4 is portrayed in IETF distribution RFC 791 (September 1981), supplanting a prior definition (RFC 760, January 1980).
IPv4 is a connectionless protocol for utilization on bundle exchanged systems. It works on a best exertion conveyance model, in that it doesn't promise conveyance, nor does it guarantee legitimate sequencing or evasion of copy conveyance. These viewpoints, including information honesty, are tended to by an upper layer transport protocol, for example, the Transmission Control Protocol (TCP).
Addressing:
IPv4 utilizes 32-bit (four-byte) addresses, which restrains the location space to 4294967296 (232) address. As address were allocated to clients, the quantity of unassigned address diminished. IPv4 address fatigue happened on February 3, 2011, in spite of the fact that it had been essentially postponed by location changes, for example, classful system plan, Classless Inter-Domain Routing, and system address interpretation (NAT). This impediment of IPv4 animated the advancement of IPv6 in the 1990s, which has been in business organization since 2006. IPv4 holds uncommon location obstructs for private systems (~18 million address) and multicast addresses (~270 million addresses).IPv4 address may be composed in any documentation communicating a 32-bit number esteem, however for human accommodation, they are frequently composed in the spot decimal documentation, which comprises of four octets of the location communicated exclusively in decimal and differentiated by periods.
The accompanying table demonstrates a few representation designs:
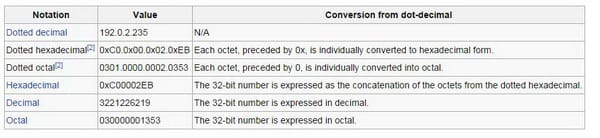
Blending decimal, octal and hexadecimal is permitted in spotted arrangement for every octet. Note that in non-spotted arrangements, numbers greater than 32-bit, might be given now and again (e.g. Firefox) and will get changed over mod 232.
Initially, an IP location was isolated into two sections: the system identifier was the hugest (most noteworthy request) octet of the location, and the host identifier was whatever remains of the location. The recent was in this manner likewise called the rest field. This empowered the production of a greatest of 256 systems. This was rapidly discovered to be deficient. To beat this utmost, the high request octet of the address was reclassified to make a set of classes of systems, in a framework which later got to be known as systems administration. The framework characterized five classes, Class A, B, C, D, and E. The Classes A, B, and C had distinctive bit lengths for the new system distinguishing proof. Whatever is left of a location was utilized as long ago to recognize a host inside a system, which implied that each one system class had an alternate ability to address, has. Class D was apportioned for multicast tending to and Class E was saved for future applications.
Beginning around 1985, systems were concocted to subdivide IP systems. One technique that has demonstrated adaptable is the utilization of the variable-length subnet veil (VLSM). In view of the IETF standard RFC 1517 distributed in 1993, this arrangement of classes was formally supplanted with Classless Inter-Domain Routing (CIDR), which communicated the quantity of bits (from the most critical) as, for example, /24, and the class-based plan was named by complexity. CIDR was intended to allow repartitioning of any location space so that more diminutive or bigger squares of address could be apportioned to clients. The various leveled structure made by CIDR is overseen by the Internet Assigned Numbers Authority (IANA) and the local Internet registries (RIRS). Every RIR keeps up a freely searchable WHOIS database that gives data about IP address assignments.
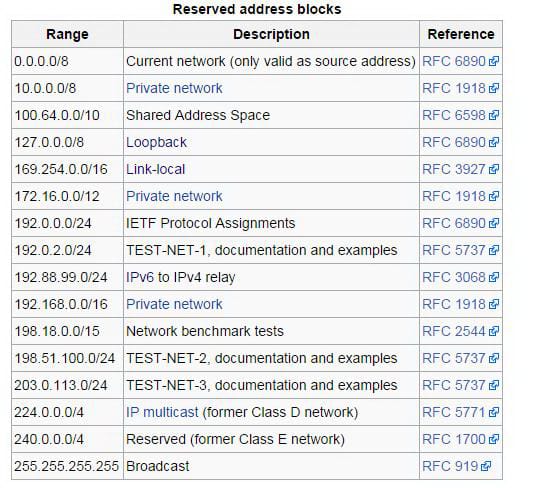
Here is the special addressing which is used by it;
Private networks:
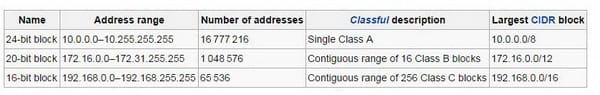
Of the roughly four billion address permitted in IPv4, three scopes of location are held for utilization in private systems. These extents are not routable outside of private systems, and private machines can't straightforwardly correspond with open systems. They can, in any case, do so through system address interpretation. The accompanying are the three territories saved for private systems (RFC 1918):
Bundles with a private end of the line location are disregarded by all open switches. Two private systems (e.g., two extension work places) can't impart through general society web, unless they utilize an IP shaft or a virtual private system (VPN). At the point when one private system needs to send a bundle to an alternate private system, the first private system exemplifies the parcel in a protocol layer so that the bundle can go through people in general system. At that point the bundle goes through people in general system. At the point when the parcel achieves the other private system, its protocol layer is uprooted, and the bundle makes a trip to its goal.
Alternatively, epitomized bundles may be encoded to secure the information while it goes over people in general network. RFC 6890 characterizes the uncommon location hinder 169.254.0.0/16 for connection neighborhood tending to. These address are just substantial on connections, (for example, a nearby system fragment or point-to-point association) joined with a host. These addresses are not routable. Like private addresses, this address can't be the source or end of parcels crossing the web. These address are basically utilized for location auto configuration (Zero config) when a host can't get an IP address from a DHCP server or other inward setup techniques.
At the point when the location piece was saved, no measures existed for location auto configuration. Microsoft made a usage called Automatic Private IP Addressing (APIPA), which was sent on a large number of machines and turned into a true standard. Numerous years after the fact, in May 2005, the IETF characterized a formal standard in RFC 3927, entitled Dynamic Configuration of IPv4 Link-Local Addresses. IP bundles whose source address fit in with this system ought to never show up outside a host. The usual way of doing things of this system develops that of a loopback interface: IP bundles whose source and end of the line address have a place with the system (or sub network) of the same loopback interface are come back to that interface; IP bundles whose source and end of the line address have a place with systems (or sub networks) of diverse interfaces of the same host, one of them being a loopback interface, are sent customarily.
Addressing which end with 0 and 225:
Systems with subnet veils of no less than 24 bits, i.e. Class C systems in glassful systems administration, and systems with CIDR additions might not have a location finishing in 0 or 255. Tending to recommended just three conceivable subnet veils: Class A, Class B, and Class C, For instance, in the subnet (192.168.5.0/24) the identifier 192.168.5.0 ordinarily is utilized to allude to the whole subnet. To dodge vagueness in representation, the location finishing in the octet 0 is saved.
A telecast location is a deliver that permits data to be sent to all interfaces in a given subnet, as opposed to a particular machine. For the most part, the show location is found by acquiring the bit supplement of the subnet veil and performing a bitwise OR operation with the system identifier. As it were, the telecast location is the last address in the location scope of the subnet. Case in point, the telecast address for the system 192.168.5.0 is 192.168.5.255. For systems of size/24 or bigger, the telecast address dependably closes in 255. On the other hand, this does not imply that each location finishing in 0 or 255 can't be utilized as a host address. For instance, in the/16 subnet 192.168.0.0/255.255.0.0, which is comparable to the location extend 192.168.0.0-192.168.255.255, the show location is 192.168.255.255. One can utilize the accompanying address for hosts, despite the fact that they end with 255: 192.168.1.255, 192.168.2.255, and so on. Likewise, 192.168.0.0 is the system identifier and must not be relegated to an interface. The address 192.168.1.0, 192.168.2.0, and so forth. may be appointed, notwithstanding closure with 0. Previously, clash between system addresses and show addresses emerged in light of the fact that some product utilized non-standard telecast addresses with zeros rather than ones.
In systems littler than/24, show address don't essentially end with 255. Case in point, a CIDR subnet 203.0.113.16/28 has the show address 203.0.113Has on the Internet are typically known by names, e.g., www.example.com, not essentially by their IP address, which is utilized for routing and system interface distinguishing proof. The utilization of space names obliges interpreting, called determining, them to addresses and the other way around. This is undifferentiated from finding a telephone number in a telephone directory utilizing the beneficiary's name.
The interpretation in the middle of address and space names is performed by the Domain Name System (DNS), a various leveled, disseminated naming framework which takes into account sub delegations of name spaces to different DNS servers.an IP parcel comprises of a header area and an information segment. An IP bundle has no information checksum or some other footer after the information area. Regularly the connection layer exemplifies IP parcels in edges with a CRC footer that identifies most blunders, and ordinarily the end-to-end TCP layer checksum locates most other errors. The second field (4 bits) is the Internet Header Length (IHL), which is the quantity of 32-bit words in the header. Since an IPv4 header may contain a variable number of alternatives, this field indicates the measure of the header (this additionally harmonizes with the balance to the information). The base worth for this field is 5 (RFC 791), which is a length of 5x32 = 160 bits = 20 bytes. Being a 4-bit esteem, the greatest length is 15 words (15x32 bits) or 480 bits = 60 bytes.an eight-bit time to live field aides keep datagrams from enduring (e.g. going in rings) on a web. This field restrains a datagram's lifetime. It is pointed out in seconds; however time interims short of what 1 second are gathered together to 1. In practice, the field has turned into a jump number when the datagram touches base at a switch, the switch decrements the TTL field by one. At the point when the TTL field hits zero, the switch tosses the parcel and regularly sends an ICMP Time Exceeded message to the sender. The system traceroute utilizes these ICMP Time Exceeded messages to print the switches utilized by parcels to go from the source to the objective.
Fragmentation:
The Internet Protocol empowers systems to correspond with each other. The configuration suits systems of differing physical nature; it is free of the underlying transmission innovation utilized within the Link Layer. Systems with distinctive equipment typically shift in transmission speed, as well as in the greatest transmission unit (MTU). At the point when one system needs to transmit datagrams to a system with a more modest MTU, it may piece its datagrams. In IPv4, this capacity was put at the Internet Layer, and is performed in IPv4 switches, which along these lines just oblige this layer as the most noteworthy one executed in their outline.
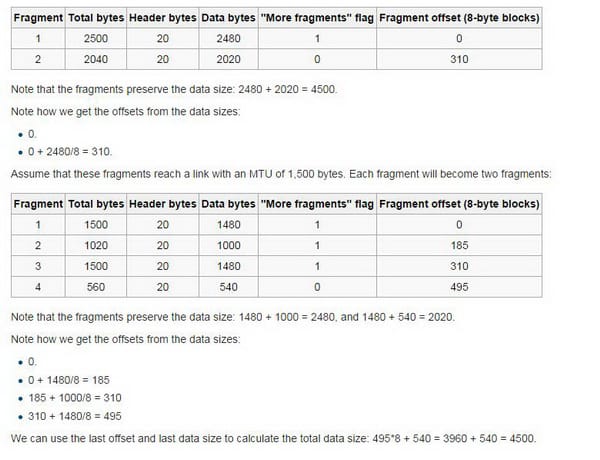
Interestingly, IPv6, the up and coming era of the Internet Protocol, does not permit switches to perform fracture; has must focus the way MTU before sending datagrams. For sample, for a MTU of 1,500 bytes and a header size of 20 bytes, the piece balances would be products of (1500-20)/8 = 185. These products are 0, 185, 370, 555, and 740.
It is feasible for a bundle to be divided at one switch, and for the parts to be divided at an alternate switch. Case in point; consider a bundle with an information size of 4,500 bytes, no choices, and a header size of 20 bytes. So the bundle size is 4,520 bytes. Expect that the bundle goes over a connection with a MTU of 2,500 bytes. At that point it will turn into two pieces which are as follows;
IPv4 is the protocol which has been there for some long time. It has much importance in networking. So a network engineer must know this protocol so he can configure the network properly. Through this, he would also be able to pass his CCNA exam easily.
Site Search:






