- Home
- Popular IT Certifications
- Configuring InterVLAN Routing & SVI Interfaces
How to Configure inter VLAN routing & SVI interfaces
VLAN routing and the SVI interfaces are the terms which we hear every day and they have become so common now. So to get command on them, one must first learn what they are and how they can be configured. Doing so, one can become the master of them and can even sort out any kind of problem which might arise during the networking engineering. Here are the details of the topics and how they can be configured;
Sub interfaces
A sub interface is a virtual interface made by isolating one physical interface into numerous consistent interfaces. A sub-interface is a sensible interface that uses the "guardian" physical interface for really moving the data. If we had a switch with just 1 physical interface, yet required to have the switch associated with two IP organizes, so it could do routing, we could make 2 coherent sub interfaces, dole out each one sub interface an IP address inside every subnet, and we can then course between them.
A sub-interface in a Cisco Router utilizes the guardian physical interface for sending and accepting data. Sub interfaces are utilized for a mixed bag of purposes. On the off chance that we have one Router with one physical interface, however required to have the switch joined with two IP systems to course activity between two switches, we can make two sub interfaces inside the physical interface, allocate each one sub interface an IP address inside every subnet and afterward course the information between two subnets. We use Sub interfaces for entomb VLAN movement routing by utilizing a Router-on-a-Stick arrangement, NBMA (Non Broadcast Multiple Access) WAN results like casing hand-off or ATM and so on.
A Sub interface could be arranged much the same as a physical interface. In the event that you take the assistance from Cisco IOS utilizing inquiry mark, we can see the number range which we can used to make sub interfaces. Since VLANs are practically equivalent to numerous separate switches each with its own particular subnet, a switch is obliged to course activity between them. . The same would ordinarily be valid for VLANs inside a solitary switch; you would require a different physical association from a port in every VLAN on the switch, to various ports on the switch. This turns into an issue for various reasons, however most of the switches don't have more than a couple of Ethernet ports, and even with enough ports this would be an unnecessary waste of assets on the switch. The answer for this various association issue is to utilize what is known as a trunk line.in a NBMA system, telecast or multicast parcels are not passed between circuits. This presents issues for movement utilizing these parcels, for example, routing overhauls. To take care of this issue, sub interfaces are once in a while used to consider every sensible circuit in a physical association with be considered as its own particular interface, hence taking into consideration routing redesigns and other non-unicast movement to be passed between them, which is overall impractical.
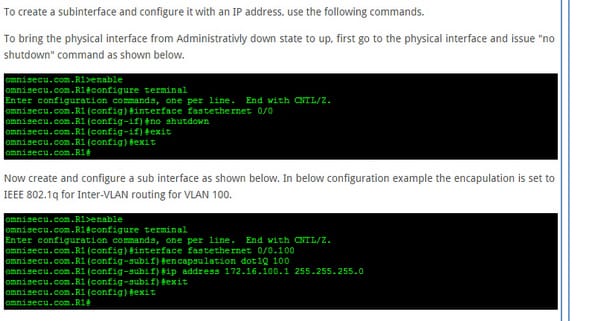
Here is how you can configure the sub interface:
Upstream routing
Term "upstream routing" implies that other than ordinary ROAS design that empowers routing bundles between diverse VLANs you have to recollect to arrange courses (or empower routing protocols) to different subnets of the system so the switch will have the capacity to forward parcels to other "upstream" destinations. Conversely, downstream movement streams to the client's machine. Movement on most systems streams in both upstream and downstream headings all the while, and regularly when information streams in one heading, system protocols frequently send control directions (by and large imperceptible to the client) in the inverse direction.one approach to produce upstream activity is to transfer documents to a server or send an email message. Alternately, downloading records and accepting email create downstream movement. Normal Internet clients make significantly more downstream than upstream activity.
Illustration: he Web program sends HTTP asks for upstream to the Web server, and the server answers with downstream information for the most part as HTML pages. Asymmetric DSL (ADSL) administrations gives less transmission capacity in the upstream bearing keeping in mind the end goal to hold more transfer speed for downstream movement.
Encapsulation
Encapsulation is the pressing of information and capacities into a solitary segment. The gimmicks of Encapsulation are backed utilizing classes. It permits specific stowing away of properties and routines in a class by building an impervious divider to ensure the code from incidental defilement. Exemplification, legacy, and polymorphism are the three mainstays of article arranged programming. In programming languages, exemplification is utilized to allude to one of two related however different ideas, and frequently to the mixture thereof:
- It is a language component for limiting access to a portion of the object's parts.
- A language build that encourages the packaging of information with the routines (or different capacities) working on that information.
Some programming language scientists and scholastics utilize the first significance alone or in mix with the second as a recognizing peculiarity of article arranged programming, while other programming languages which give lexical terminations view Encapsulation as a gimmick of the language orthogonal to question introduction. The second definition is spurred by the way that in numerous OOP languages stowing away of segments is not programmed or might be overridden; therefore, data covering up is characterized as a different idea by the individuals who incline toward the second definition. Under this definition, Encapsulation implies that the inner representation of an item is by and large escaped view outside of the object's definition. Regularly, just the object techniques can straightforwardly review or control its fields. A few languages like Smalltalk and Ruby just permit access by means of item strategies, however most others (e.g. C++, C# or Java) offer the developer a level of control over what is stowed away, ordinarily through magic words like open and private. It ought to be noted that the ISO C++ standard alludes to ensured, private and open as "access specifies" and that they don't" "conceal any data". Data stowing away is refined by outfitting an incorporated rendition of the source code that is interfaced through a header record. Concealing the internals of the article secures its trustworthiness by keeping clients from setting the inner information of the part into an invalid or conflicting state. An assumed profit of Encapsulation is that it can diminish framework multifaceted nature, and along these lines build power, by permitting the designer to point of confinement the between conditions between programming components. Quite often, there is an approach to override such insurance - normally through reflection API (Ruby, Java, C#, and so forth.), now and then by component like name mutilating (Python), or unique catchphrase utilization like companion in C++.
The following is a sample in C# that demonstrates how gets to an information field that might be limited through the utilization of private keywords:

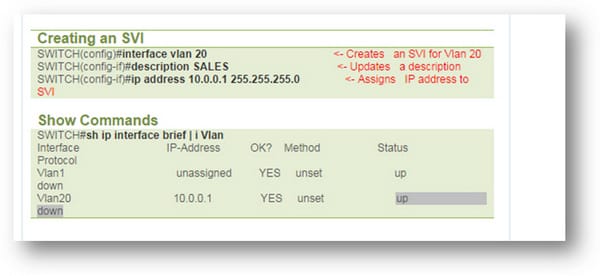
Configure SVI interface
A switch virtual interface (SVI) is a VLAN of switch ports spoke to by one interface to a routing or crossing over framework. There is no physical interface for the VLAN and the SVI gives the Layer 3 transforming to parcels from all switch ports connected with the VLAN. There is balanced mapping between a VLAN and SVI, in this manner just a solitary SVI might be mapped to a VLAN. Naturally, a SVI is made for the default VLAN (VLAN1) to allow remote switch organization. A SVI can't be initiated unless connected with a physical port.
SVIs are by and large arranged for a VLAN for the accompanying reasons:
- Permit movement to be directed between VLANs by giving a default portal to the VLAN.
- Give fallback crossing over (if needed to non-routable protocols).
- Give Layer 3 IP network to the switch.
- Help crossing over designs and routing protocol.
A SVI can additionally be known as a Routed VLAN Interface (RVI) by a few merchants. Customarily, switches send movement just to has inside the same show space (Single VLAN) and switches took care of activity between diverse telecast spaces (Different VLANs). This implied that system gadgets in distinctive telecast spaces couldn't impart without a switch. With SVIs the switch will utilize virtual Layer 3 interface to course activity to other Layer 3 interface subsequently killing the requirement for a physical switch. VLANs lessen the heap on a system by partitioning a LAN into more modest fragments and keeping neighborhood movement inside a VLAN. Be that as it may, on the grounds that every VLAN has it space, a system is required for VLANs to pass information to different VLANs without passing the information through a switch. The result is to utilize exchanged virtual interface - SVI. A SVI is ordinarily found on switches (Layer 3 and Layer 2). With SVIs the switch perceives the parcel objectives that are nearby to the sending VLAN and switches those bundles and parcels bound for distinctive VLANs are steered. There is balanced mapping between a VLAN and SVI, subsequently just a solitary SVI might be mapped to a VLAN. In default setting, a SVI is made for the default VLAN (VLAN1) to allow remote switch organization. In most regular plans we have the default entryway for the hosts indicating the switches SVI, then the switch will course the bundles to rest of the Layer 3 domain.an SVI can't be initiated unless the VLAN itself is made and no less than one physical port is related and dynamic in that VLAN. Unless the VLAN is made there will be no spreading over tree occurrence running subsequently the line protocol will be down for the SVI VLA.
Also, check the following diagram for understanding the SVIs.
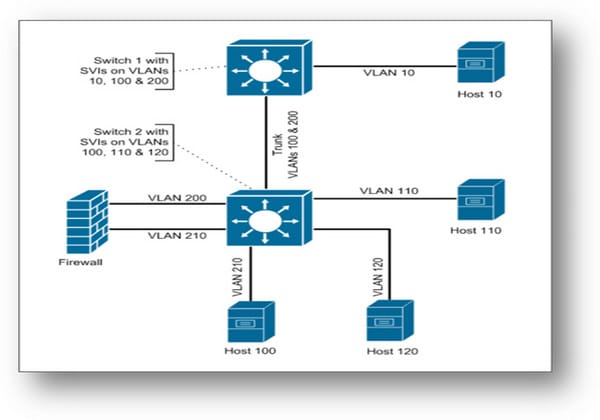
The outline shows A circumstance where its regular to see switches with SVIs on a few VLANs yet not others are in a DMZ switch deployment.in this configuration we have two switches. One of them has the LAN and the SVI. Other one has the VLANS and the SVI as well, but different ones as it can be seen in the picture. In this outline if the host 110 needed to converse with host 120, then the host 110 would send a data packet to SVI on the VLAN. On other hand, switch 2 will course the bundle straightforwardly to the VLAN 120. It is on the grounds that switch 2 contains SVIs at each of the VLANs and it would have straightforwardly associated courses for these VLANs. Anyhow suppose it is possible that have 110 needed to converse with host 210. The again, the host 110 will send a bundle to switch 2's SVI on VLAN 110; however switch 2 couldn't course the parcel straightforwardly to the VLAN 210. It is on the grounds that despite the fact that the VLAN 210 is designed on the switch 2 and it doesn't have a SVI for this VLAN. Another important thing is, that Switch 2 contains a L2 association with that VLAN, however not a L3 association. Rather switch 2 would need to course the parcel on VLAN 100 through the storage compartment to switch 1. Switch 1 would then course the bundle to VLAN 200 and send the parcel to the firewall. The bundle would be sent again over the storage compartment to switch 2, however switch 2 just demonstrations as an ordinary regular switch for that VLAN, so it just switches (L2) the parcel (truly the edge) to the port in VLAN 200 associated with the firewall. The firewall got the parcel, and afterward courses that bundle out its interface joined with VLAN 210 on switch 2. Again switch 2 just barely switches the bundle on VLAN 210 to have 210. So in this outline the bundle between host 110 and 210 pass through switch 2 few times, yet sometimes switches 2 courses the bundles and in different cases switch 2 just switches the parcel.
Hence these are the ways through which you can configure them all. One must know about all the concepts so that he can utilize them in the networking. Also, there are some concepts which are quite important like the concept of Encapsulation which is very important since it is a language and can be done through java and C++.
Site Search:






