- Home
- Popular IT Certifications
- Cisco Routers: PPP Connection & Frame Relay
Describe how to configure and verify a PPP connection between Cisco routers and verify frame relay on cisco routers
Point-to-Point Protocol (PPP) is an information join protocol used to secure an immediate association between two hubs. It can give association validation, transmission encryption (utilizing ECP), and packing.
PPP is utilized over numerous sorts of physical systems including serial link, telephone line, trunk line, cell phone, specific radio connections, and fiber optic connections, for example, SONET. PPP is likewise utilized over Internet access associations. Web access suppliers (ISPs) have utilized PPP for client dial-up access to the Internet, since IP parcels can't be transmitted over a modem line all alone, without some information join protocol. Two subsidiaries of PPP, Point-to-Point Protocol over Ethernet (PPPoE) and Point-to-Point Protocol over ATM (PPPoA), are utilized most ordinarily by Internet Service Providers (ISPs) to build a Digital Subscriber Line (DSL) Internet administration association with clients. PPP is regularly utilized as an information connection layers protocol for association over synchronous and offbeat circuits, and there it holds up to a great extent superseded the more seasoned Serials Line Internet Protocols (SLIP) and the phone organization ordered benchmarks, (for example, Links Access Protocols, Balanced in the X.25 protocols suite). The main prerequisite for PPP is that the circuit gave is full duplex. PPP was intended to work out with various system layers protocols, containing Internet Protocols (IP), TRILL, Novell's Internetwork Packets Exchanges (IPX), NBFs, and the AppleTalk. PPP was planned to some degree after the first HDLC particulars. The planners of the PPP included numerous extra gimmicks that have been observed just in exclusive information join protocol up to the time.
RFC 2516 depicts Point-to-Point Protocol over Ethernet (PPPoE) as a strategy for transmitting PPP over Ethernet that is now and then utilized with DSL. RFC 2364 portrays Point-to-Point Protocol over ATM (PPPoA) as a technique for transmitting PPP over ATM Adaptation Layer 5 (Aal5), which is additionally a typical option to PPPoE utilized with DSL. PPP is a layered protocol that has three segments:
- An exemplification part that is utilized to transmit datagrams over the determined physical layer.
- A Link Control Protocol (LCP) to create, arrange, and test the connection and also arrange abilities.
One or more NCPS used to arrange discretionary setup parameters and offices for the system layer. There is one Network Control Protocol (NCP) for every protocol underpinned by PPP. Link Control Protocol (LCP) launches and ends associations nimbly, permitting hosts to arrange association choices. It is a vital piece of the PPP, and is characterized in a same kind of standard determination. LCP gives programmed setup of interfaces at each one end, (for example, setting the datagram's size, got away characters, and enchantment numbers) and for the selection of discretionary verification. The LCPs protocols run on top of the PPPs (with PPPs protocol numbers 0xc021). In this way an essential PPP association must be secured before LCP has the capacity arrange it. RFC 1994 depicts Challenge-handshake confirmation protocol (CHAP), which is favored for building dial-up associations with ISPs. Albeit censured, Password validation protocols (PAP) is still now and again utilized. After the connection has been secured, extra system (layer 3) design may happen. Most usually, the Internet Protocols Control Protocol (IPCP) is utilized, despite the fact that Internetwork Packet Exchange Control Protocols (IPXCP) and AppleTalk's Control Protocols (ATCP) were once exceptionally popular. Internet Protocols Version 6 the Control Protocols will see broadened use later on, when Ipv6 replaces Ipv4 as the overwhelming layers-3 protocol. PPP grants different system layer protocols to work on a same correspondence join. For each system layers protocol utilized, a different Networks Control Protocols (NCP) is given with a specific end goal to embody and arrange alternatives for the numerous system layer protocols. It arranges system layer data, e.g. system location or squeezing choices, after the association has been secured.
Case in point, Internet Protocols (IP) utilizes the IP Controls Protocols, and Internetworks Packets Exchange (IPX) utilizes the Novell IPX's Control Protocols. NCPS incorporate fields containing institutionalized codes to demonstrate the system layer protocol sort that the PPP association exemplifies.
Configuration Options:
The past area presented the utilization of LCP choices to meet particular WAN association necessities. PPP may incorporate the accompanying LCP alternatives:
- Validation - Peer switches trade verification messages. Two verification decisions are Password Authentication Protocol (PAP) and Challenge Handshake Authentication Protocol (CHAP). Verification is clarified in the following segment.
- Squeezing - Increases the compelling throughput on PPP associations by decreasing the measure of information in the casing that must traverse the connection. The protocol decompresses the casing at its objective. See RFC 1962 for more subtle elements.
- Slip recognition - Identifies shortcoming conditions. The Quality and Magic Number alternatives help guarantee a solid, circle free information join. The Magic Number field helps in identifying connections that are in a circled back condition. Until the Magic-Number Configuration Option has been effectively arranged, the Magic-Number must be transmitted as zero. Enchantment numbers are created haphazardly at each one end of the association.
- Multilink - Provides burden adjusting a few interfaces utilized by PPP through Multilink PPP
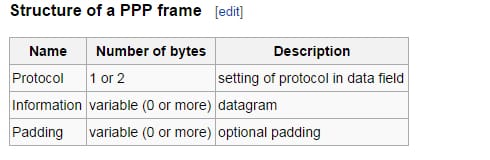
The Protocol field shows the sort of payload parcel. The Information field contains the PPP payload; it has a variable length with an arranged greatest called the Maximum Transmission Unit. Naturally, the greatest is 1500 octets. It may be cushioned on transmission; if the data for a specific protocol could be cushioned, that protocol must permit data to be recognized from cushioning.
Encapsulation:
PPP edges are epitomized in a lower-layer protocol that gives encircling and may give different capacities, for example, a checksum to locate transmission mistakes. PPP on serial connections is typically epitomized in a surrounding like HDLC. The Flag field is available when PPP with HDLC-like confining is utilized.
The Address and Control fields dependably have the worth hex FF (for "all stations") and hex 03 (for "unnumbered data"), and could be precluded at whatever point PPP LCP Address-and-Control-Field-Compression (ACFC) is arranged. The casing check succession (FCS) field is utilized for figuring out if an individual edge has a slip. It contains a checksum processed over the casing to give essential assurance against lapses in the transmissions. That is the CRC code like the one utilized for other layers two protocol mistake assurance plans, for example, the one utilized as a part of Ethernet. As per RFC 1662,this might be the 16 bits (2 bytes) or the 32 bits in size. The FCS is computed over the Addresses, Control, Protocols, Information and the Padding fields after the message has been embodied.
PPP Lines:
The periods of the Points to Points Protocol are recorded beneath:
The Link dead:
The stage happens when the connection comes up short, or one of the sides is advised to detach (client has completed his or her dialup associations.)
The Links Establishment Phase:
It is the place Link Control Protocols transaction is endeavored. On the off chance that fruitful, control goes either to the confirmation stage or the Network-Layered Protocols stage, contingent upon whether verification is wanted.
Validation Phase:
This stage is discretionary. It permits the sides to validate one another before an association is built. On the off chance that fruitful, control goes to the system layer protocol stage.
System Layer Protocol Phase:
This stage is the place each one sought protocols' Network Control Protocols are conjured. For instance, IPCP is utilized as a part of making IP benefit above the line. Information transports for all protocols which are effectively begun with their system control protocols additionally happens in this stage. Shutting down of system protocols likewise happen in this stage.
Links Termination Phase:
It can cause the shut down this association. This might happen if there is a confirmation disappointment, if there are such a variety of checksum blunders that the two gatherings choose to tear down the connection consequently, if the connection abruptly falls flat, or if the client chooses to hang up his association.
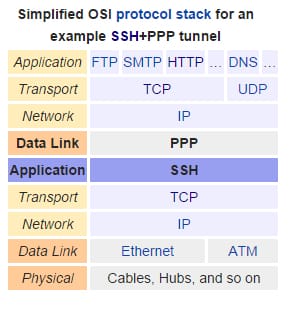
PPP, acting as a second payer protocol at ends of tunnel:
Numerous protocols might be utilized to tunnel information over IP systems. Some of them, in the same way as SSL, SSH, or L2tp make virtual system interfaces and give the impression of an immediate physical associations between the shaft endpoints. On a Linux host for instance, these interfaces would be called tun0. As there are just two endpoints on a tunnel, the shaft is a point-to-point association and PPP is a common decision as an information connection layer protocol between the virtual systems interfaces. PPP can allocate IP locations to these virtual interfaces, and these IP locations might be utilized, for instance, to course between the systems on both sides of the shaft.
IPsec in burrowing mode does not make virtual physical interfaces at the end of the shaft, since the tunnel is taken care of specifically by the TCP/IP stack. L2tp might be utilized to give these interfaces; this method is called L2tp/IPsec. For this situation as well, PPP gives IP locations to the limits of the tunnel.
Debugging the PPP:
On the off chance that an association can't be secured, turn fittings stream CTS/RTS to off utilizing set ctsrts off. This is for the most part the situation when joined with some PPP-skilled terminal servers, where PPP hangs when it tries to compose information to the correspondence connection, and sits tight for a Clear to Send (CTS) signal which might never come. At the point when utilizing this choice, incorporate set ACCMAP as it might be obliged to annihilation fittings reliant on passing certain characters from end to end, more often than not XON/XOFF. Allude to PPP for more data on this alternative and how it is utilized.
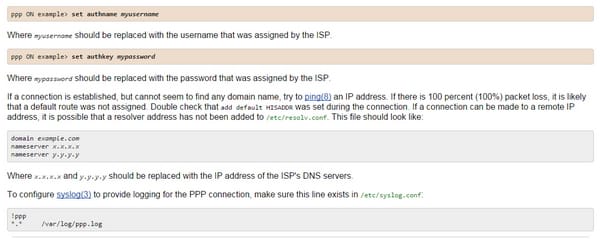
Equality is situated at none be default, yet is utilized for lapse checking with an expansive increment in activity, on more seasoned modems. PPP may not come back to the order mode, which is generally an arrangement blunder where the ISP is sitting tight for arranging to start. As of right now, utilizing ~p will drive PPP to begin sending the arrangement data. In the event that a login incites never shows up, PAP or CHAP confirmation is probably needed. To utilize PAP or CHAP, add the accompanying choices to PPP before going into terminal mode:
On the off chance that packing or encryption is, no doubt utilized, then the PPP payload is not translated by Network Monitor. Packed or encoded payloads are demonstrated with the PPP protocol ID of 3d (accepting protocol ID pressure). To see the structure of client information inside PPP payloads, handicap pressure and encryption.
At the point when utilizing Network Monitor, remember the accompanying:
Received PPP casings don't contain a Flag character yet do contain an Ethernet-like source location and terminus address. This conduct is because of the way that Network Monitor gets the bundles from the Ndiswan.sys driver. Review that Ndiswan.sys is a moderate NDIS driver that resembles an Ethernet connector to protocols. For every PPP outline, the Ethernet-like source and objective locations are both situated to either SEND or RECV to demonstrate that the PPP edge was either sent or got by the machine on which the catch was taken. The SEND and RECV locations don't essentially distinguish the movement of a remote access server or remote access customer. In the event that the catch was undertaken the remote access server, then SEND edges was sent by the remote access server and RECV casings were sent by the remote access customer. On the off chance that the catch was tackled the remote access customer, then SEND casings were sent by the remote access customer and RECV edges were sent by the remote access server. Received PPP casings contain an Address or Control field paying little respect to whether address and control field squeezing are arranged.
Protocol ID clamping is generally arranged with Microsoft PPP associates, making the PPP Protocol ID a solitary byte when conceivable. Case in point, to view just the IPCP arrangement, set the showcase channels to impair the presentation of all protocols aside from IPCP.
Verify Frame relay in Cisco:
This is how it's done;
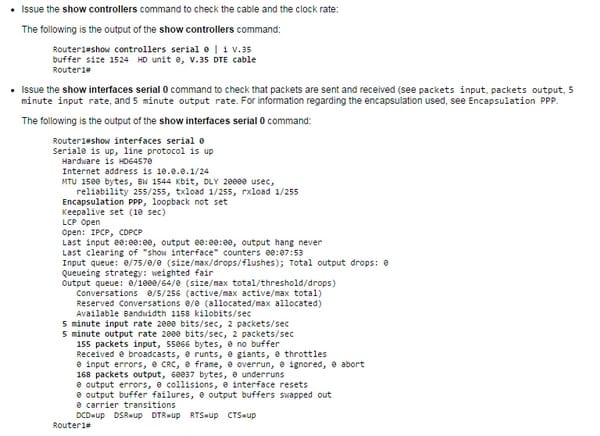
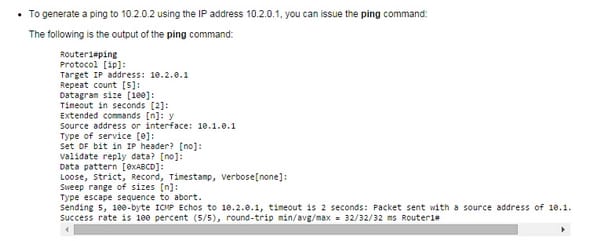
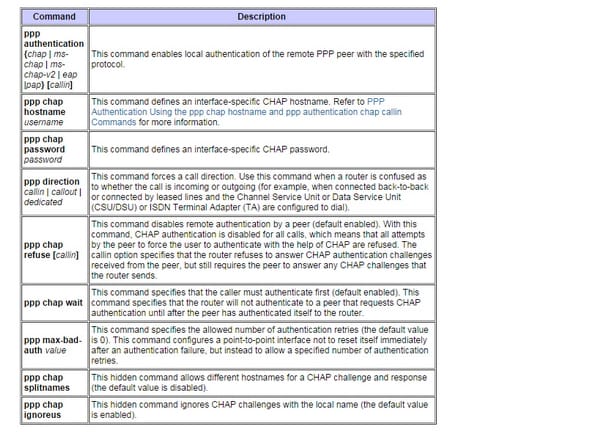
Verifying PPP connection:
Here are the PPP CHAT configuration commands;
The PPP protocol is very important when it comes to cisco routers. The reason is that they are necessary for establishment of internet connections. So, one must understand of these so he doesn't face any problem while giving exams for cisco CCNA.
Site Search:






