- Home
- Popular IT Certifications
- ACLs Types, Features, Application & Configuration
Describe the types, features, and applications of ACLs & configure ACLs in a network environment
The ACL is a rundown of consents appended to an article. An ACL indicates which clients or framework courses of action are allowed access to questions, and what operations are permitted on given objects. Each entrance in an average ACL details a subject and an operation. Case in point, if a document has an ACL that contains (Alice: read, write; Bob: read), this would give Alice consent to peruse and compose the record and Bob to just read it.
When a subject demands an operation on an article in an ACL-based security show, the working framework first checks the ACL for an appropriate passage to choose whether the asked for operation is approved. A key issue in the meaning of any ACL-based security model is deciding how get to control records are altered; specifically which clients and methods are conceded ACL-change access.in the 1990s the ACL and RBAC models were widely tried and used to administrate record consents. A file system ACL is an information structure (generally a table) containing sections that detail singular client or gathering rights to particular framework protests, for example, projects, courses of action, or documents. These sections are known as access control entrances (Aces) in the Microsoft Windows NT, Openvms, Unix-like, and Mac OS X working frameworks. Every available item contains an identifier to its ACL. The benefits or authorizations focus particular access rights, for example, whether a client can read from, keep in touch with, or execute an item. In a few executions, an ACE can control whether a client, or gathering of clients, may adjust the ACL on an article. A large portion of the UNIX and Unix-like working frameworks (e.g. Linux, BSD, or Solaris) help Posix.1e ACLs, taking into account an early POSIX draft that was deserted. A considerable lot of them, for instance AIX, Freebsd, Mac OS X starting with variant 10.4 ("Tiger"), or Solaris with ZFS file system, help Nfsv4 ACLs, which are a piece of the Nfsv4 standard. In spite of the fact that it is furthermore conceivable to design Access Control Lists focused around system space names, this is for the most part a faulty thought on the grounds that individual TCP, UDP, and ICMP bundles don't contain area names. Hence, the gadget implementing the Access Control List should independently determination names to numeric locations. This introduces an extra assault surface for an aggressor who is trying to trade off security of the framework which the Access Control List is securing. Both individual servers and switches can have system ACLs. Access control records can by and large be arranged to control both inbound and outbound activity, and in this connection they are like firewalls.
At the point when making a right to gain entrance show, you characterize criteria that are connected to each one bundle that is handled by the switch; the switch chooses whether to forward or hinder every parcel on the premise of whether the parcel matches the criteria.
Average criteria you characterize in access records are bundle source addresses, parcel end of the line locations, and upper-layer command of the parcel. On the other hand, every command has it particular set of criteria that might be characterized.
For a solitary access show, you can characterize numerous criteria in various, separate access list proclamations. Each of these announcements ought to reference the same recognizing name or number, to attach the announcements to the same access list. You can have the same number of criteria explanations as you need, restricted just by the accessible memory. Obviously, the more articulations you have, the more troublesome it will be to fathom and deal with your right to gain entrance lists. Because the request of access rundown criteria proclamations is imperative, and on the grounds that you can't reorder or erase criteria explanations on your switch, Cisco proposes that you make all right to gain entrance list proclamations on a TFTP server, and afterward download the whole get to rundown to your switch.
To utilize a TFTP server, make the right to gain entrance list explanations utilizing any content manager, and spare the right to gain entrance list in ASCII organization to a TFTP server that is open by your switch. At that point, in the event that you ever need to roll out improvements to a right to gain entrance show, you can make them to the content document on the TFTP server, and duplicate the altered record to your switch as before. Or a few commands, you can apply up to two rights to gain entrance records to an interface: one inbound access rundown and one outbound access list. With different commands, you apply stand out access list which checks both inbound and outbound bundles.
In the event that the right to gain entrance rundown is inbound, when the switch gets a parcel, the Cisco IOS programming checks the right to gain entrance list's criteria explanations for a match. On the off chance that the parcel is allowed, the product keeps on preparing the bundle. In the event that the parcel is denied, the product disposes of the bundle.
In the event that the right to gain entrance rundown is outbound, in the wake of accepting and routing a bundle to the outbound interface, the product checks the right to gain entrance list's criteria articulations for a match. In the event that the bundle is allowed, the product transmits the parcel. In the event that the bundle is denied, the product disposes of the packet. CISCO gives essential activity sifting abilities with access control records (additionally alluded to as access records). Access records could be designed for all steered system commands (IP, AppleTalk, et cetera) to channel the bundles of those commands as the parcels pass through a switch. You can design access records at your switch to control access to a system: access records can keep certain activity from entering or leaving a network. Access records channel system movement by controlling whether steered parcels are sent or obstructed at the switch's interfaces. Your switch inspects every bundle to figure out if to forward or drop the parcel, on the premise of the criteria you indicated inside the right to gain entrance records. Access list criteria could be the source location of the movement, the end of the line location of the activity, the upper-layer command, or other data. Note that complex clients can off and on again effectively dodge or nitwit fundamental access records in light of the fact that no confirmation is needed.
In current SQL usage, ACL likewise oversee gatherings and legacy in a chain of command of gatherings. So "cutting edge ACLs" can express all that RBAC express, and are remarkably capable (contrasted with "old ACLs") in their capability to express get to control arrangement regarding the route in which managers view associations. For information trade, and for "abnormal state correlations", ACL information could be meant XACML.
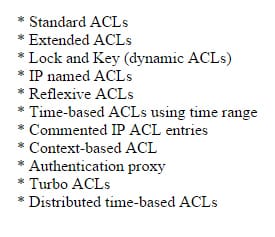
There are many types of ACL, they are;
Standard (editing and sequence numbers)
The standard ACL is the type of ACL. It is the kind in which only 1 source IP can get filtered inside a network.
Extended
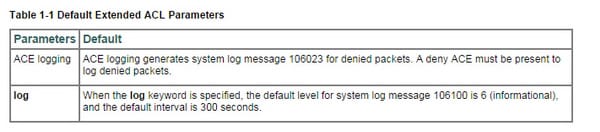
ACLs are utilized to control system access or to indicate movement for some peculiarities to follow up on. A broadened ACL is made up of one or more get to control passages (Aces). Each one ACE defines a source and end of the line for matching movement. You can recognize parameters inside the right to gain entrance rundown charge, or you can make questions or article bunches for utilization in the ACL.
An ACL is made up of one or more Aces. Each one ACE that you enter for a given ACL name is added to the end of the ACL. The request of Aces is paramount. At the point when the security machine chooses whether to forward or drop a bundle, the security apparatus tests the parcel against each one ACE in the request in which the entrances are recorded. After a match is discovered, no more Aces are checked. Case in point, in the event that you make an ACE at the start of an ACL that unequivocally allows all activity, no further explanations are ever checked.
You can impair an ACE by making it inactive. When utilizing NAT or PAT, mapped addresses and ports are no more needed in an ACL for a few gimmicks. You ought to now dependably utilize the true, untranslated addresses and ports for these gimmicks. Utilizing the true address and port implies that if the NAT arrangement transforms, you don't have to change the ACLs.
Named
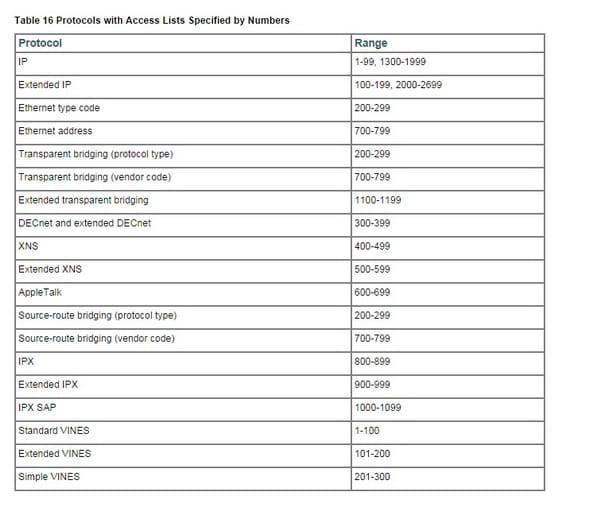
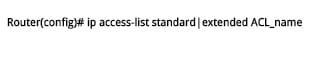
An incredible peculiarity of Cisco IOS is Named Access Control Lists. Cisco switches help Named Access Control Lists (ACLs) from IOS rendition 11.2. A real impediment of Numbered Access Control Lists (ACLs) was the quantity of aggregate numbered Access Control Lists (ACLs) you can make was restricted. Taking after table demonstrates the Access Control List (ACL) numbers you can use for Standard Access Control Lists (ACLs) and Extended Access Control Lists (ACLs).named Access Control Lists (ACLs) permits standard and stretched out ACLs to be given names rather than numbers. Not at all like in numbered Access Control Lists (ACLs), can we alter Named Access Control Lists.
To make a Named Access Control List (ACL), we can utilize the accompanying IOS summon from Global Configuration mode.
Numbered
All right to gain entrance records must be recognized by a name or a number. Named access records are more advantageous than numbered access records in light of the fact that you can determine a significant name that is less demanding to recollect and partner with an errand. You can reorder explanations in or add articulations to a named access list.
Named access records help the accompanying peculiarities that are not backed by numbered access records:
- IP choices separating
- Noncontiguous ports
- TCP banner sifting
- Erasing of passages with the no license or no denies summon.
You can apply get to inclines to the inbound or outbound interfaces of a gadget. Applying a right to gain entrance rundown to an inbound interface controls the activity that enters the interface and applying a right to gain entrance rundown to an outbound interface controls the movement that passageways the interface. At the point when programming gets a bundle at the inbound interface, the product checks the parcel against the announcements that are designed for the right to gain entrance list. Applying access records to channel approaching bundles can spare gadget assets in light of the fact that sifted parcels are tossed before entering the gadget.
You can utilize the TCP Access Control List (ACL) Splitting gimmick of the Rate-Based Satellite Control Command (RBSCP) on the outbound interface to control the kind of parcels that are liable to TCP affirmation (ACK) part on an outbound interface. You can reference a right to gain entrance list by utilizing a debug charge to cutoff the measure of debug logs. For instance, in view of the separating or matching criteria of the right to gain entrance rundown, debug logs could be constrained to source or end locations or commands. You can utilize access records to control routing upgrades, dial-on-interest (DDR), and nature of administration (QoS) characteristics.
Log option
Logging-empowered access control records (ACLs) give knowledge into movement as it crosses the system or is dropped by system gadgets. Lamentably, ACL logging could be CPU escalated and can contrarily influence different capacities of the system gadget. There are two essential components that help the CPU burden increment from ACL logging: methodology exchanging of parcels that match log-empowered access control entrances (Aces) and the era and transmission of log messages. Utilizing the arrangement charges point by point within this archive, overseers can strike a harmony between movement precision and the comparing effect on gadget CPU load.
ACL is the basic part of network. It is as important as NAT or any other part of networking is, so those who want to become network engineer must understand what ACL is and how it works.
Site Search:






