- Home
- Popular IT Certifications
- How to Secure a SOHO Wireless Network and a SOHO Wired Network
How to secure a SOHO wireless network and a SOHO wired network

The SOHO wireless network is being used by many people every day. It is common to see the being used every day at some offices. So it is important that they are made secured as well. The reason is, that a network which is opened, invites the troubles to the computer itself. So making the network secured should be the first priority of everyone. If someone wants to have some strong network then he should be doing something to secure the basic infrastructure that is the foundation of this network. There is some easy way for that and it is that the network should be closed in some closet. That closet should be locked. Also, if someone makes some restriction that they others cannot gain any access to the network, then it would become so easy for someone. There can be the door with some lock or can be something digital, they all are used for the protection of the network. Sometimes, one can even use the bio metrics. Hence there would be some finger print reader which would be found at the door so that only those who have that print would get access to the network. Also, one can limit the people who can get the access to one's network.
Change default user-names and passwords:
If someone has been using some wired or some unwired network. Then there is something which one can use for the security. There one has to be too much careful while having the default credentials for the infrastructure of the devices. There are the usernames and the password that are brought from the factory. They are written on the box and mentioned outside too, sometimes. But as soon as one gets it, he should change the both of them. As long as the one has the same username and the password, there are chances that someone might have read those credentials on the box and he might steal it and can use it further. So once then person is logged into it, he gets the full control over it and he can change the things here.
Changing SSID:
SSID is basically the name of the network. When one open up the wireless networks list, one can find many of the networks and they all contain some names. These names are actually the SSID. These are the things through which one can know that what is the name of the network and hence can recognize them. The SSID of the network should not be something so common or something that can actually point towards one. Someone might like to make some smart move and remove the SSID. Then, the network would be shown but the SSID won't be shown and hence, one won't be able to get connected. Here comes the double security, one would not only have to guess the password but the username as well. Also, it can be done by disabling the access point from the broadcasting. But doing that doesn't really mean that now one has put up some restriction access to all of the networks. What is happened by disabling the SSID is that it just becomes invisible. So someone who knows that how one should be looking for the wireless networks would still be able to find it out. But it is a thing which can help one cleaning up the big list of all those networks which one can see on the wireless access.
Setting encryption:
The encryption has two types, mainly. One of them is not being used since it has some flaws. That is still available in some really old routers but using it is just a mess. It is named as the WEP. This is the most insecure type and one should totally avoid it and should not bother installing it or using it even if one's current network offers this technology. This encryption service is too much insecure. The latest and the best encryption settings contain the WPA-2. That is the best among all encryptions settings which have been introduced. Many of the modern devices have it, so if one is using some old device, then one should get switched to this one.
Disabling SSID broadcast:
SSID is the name of any network which is available. One can turn the SSID off so that no one can know that there is some network available and when they ant to get connected to it, they will find that they can't. The reason is that one would not just have to type in the password, but would have to know the username too. One might want to disable the SSID since it has the benefits mentioned above. One can do that manually.
Enable MAC filtering:
On the wired and the unwired networks, one can do something and get some access restricted to the network. This thing is done through something known as the MAC addresses or it is the Media Access Controls. This is basically the address of the hardware, the network device's address. These network devices are those which have been connected to the network that one is using. By applying some filters to the infrastructure, then one can make some limitations about those who are getting some access to the network and the place from where the network is being originated.
Antenna and access point placement:
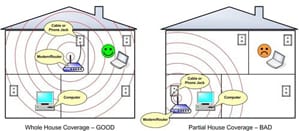
There are many types of the receivers which are used by one. There are so many antennas which can be used for receiving the signals from the access point which is located pretty far. So when someone is using the internet, one should keep in mind that at what points the signals are being travelled and how much power is being used to enable it for that. Also, one should try to place the receiving point and the access point at near distance since if they are near, the signal strength would be stronger and the internet would work better.
Radio power levels:
One should know that the radio signals have some more power than the normal signals. They are pretty fast so they can cover some good distance within the short period of time. The regularity's region can put some restriction of the maximum power that can be transferred. Also, sometimes the selection of the channels and the code used by that country can also affect the power level of the radio waves.
Assign static IP addresses:
Normally one would not do the fixed IP addresses at the homes. But in some ranges one would find them. The router get assigned a new IP itself ad one doesn't have to do anything. By this change one won't even realize any difference. The static IP doesn't change and the computer keeps it for the use for long time. The good thing is that if someone wants to have some local server, then this is good. Since the local home network would then be accessed by anyone in the world and the requests coming would be forwarded to the server machine. If there is the dynamic IP, then the server won't be able to work properly and it would be broken down. For the gaming purposes too, one would like having some static IP address. One while playing, has to forward some of the ports while playing multilayer games. Some of the routers contain some automated setup which is named as the uPNP. Hence one can play the games without any disturbance and the warnings from the network. But this can lead to some IP address conflicts as well. That is the message sometimes one can see. If the IP is set up the same, then the router would start the IP automatically. At other point, some other computer might have the same IP and hence the conflict would arise.
Change default usernames and passwords
When one gets the device, he should act fast and change the default username and the password already. When it is done, then one can have some full access to the device. Hence one would be able to set any settings he wants and it is very useful. Also, there is a website too at the internet, it has all the list of those routers and the companies which are present in market and the list of the usernames and the passwords used is given there so one can find the information from there as well.
Enable MAC filtering:
The MAC filtering helps someone getting the network more and more secured. But the MAC address is something which is too simple to spoof. There are many of the network interface card which have the ability to allow one to manually configure the MAC addresses in the computers. So, the thing which has to be done by one is the usage of the free software from internet. Also, then plug that in and observe that what are the types of the MAC address which are communicating right now. Also, when someone sees that one of those addresses have left the network, then one can use that specific MAC Address for communication. This is called the security with the help of obscurity. It is not very obvious that how one can face that problem, but it is somehow, not a good security feature. If there is the access point where the one wants to get access, there should be the offering of the MAC addresses. One can just add them to one's list and then one can create limitation of the MAC addressees which are being communicated through one's network.
Assign static IP addresses:
There is some other technique too which is being used by one. It is known as the static IP address usage. One can use this technique instead of using the automatic ID, which is known as the dynamic IP as well. One can use this technique whether one of on some wired network or on some wireless network. The IP address is pretty obvious if the encryption is not the proper one. Also, there is the security through the obscurity, if there is someone who is trying to plug in and then they are unable to get the address automatically then someone who knows that how to do the drill can manually set the addresses on one's computer. Hence he can still have the access to the network.
Disabling ports:
In some of the large environments, it can be difficult for someone to keep the tracks of the thing that who is into the network and who is getting disconnected from it. So, one might like to do the disabling of the physical ports on the routers so that one can administratively perform that specific function. But it helps one making the network become even more secured. It is something good but maintaining it might become a problem for someone. The reason is that the while getting the port enabled or disabled, one would manually have to access the router. Hence, the administrative abilities are require here. But this helps maintaining the security level of the network. So this thing surely can bring some good benefits for someone.
Physical security:
The physical security of the routers and the switches require that one should keep them in some pace where someone else cannot mess with them physically. Like, one might like that the switched is placed in some cabinet which has a lock. So when the owner wants, he can simply go and can restart it or can configure it. This way, it becomes way too easy for someone to protect the router physically.
So one can know that there are many of the ways through which the SOHO router can be saved. It can be the wired one or the wireless one, that isn't the matter since there are the cures for both of them. The security can be done in many ways like the virtual security and the physical security as well.
Site Search:






